Blocklist
The blocklist allows you to prevent specified applications from running on hosts, extending the list of processes that Elastic Defend considers malicious. This helps ensure that known malicious processes aren’t accidentally executed by end users.
The blocklist is not intended to broadly block benign applications for non-security reasons; only use it to block potentially harmful applications. To compare the blocklist with other endpoint artifacts, refer to Optimize Elastic Defend.
- In addition to configuring specific entries on the Blocklist page, you must also ensure that the blocklist is enabled on the Elastic Defend integration policy in the Malware protection settings. This setting is enabled by default.
- You must have the Blocklist privilege or the appropriate user role to access this feature.
By default, a blocklist entry is recognized globally across all hosts running Elastic Defend. You can also assign a blocklist entry to specific Elastic Defend integration policies, which blocks the process only on hosts assigned to that policy.
Find Blocklist in the navigation menu or use the global search field.
Click Add blocklist entry. The Add blocklist flyout appears.
Fill in these fields in the Details section:
Name: Enter a name to identify the application in the blocklist.Description: Enter a description to provide more information on the blocklist entry (optional).
In the Conditions section, enter the following information about the application you want to block:
Select operating system: Select the appropriate operating system from the drop-down.Field: Select a field to identify the application being blocked:Hash: The MD5, SHA-1, or SHA-256 hash value of the application’s executable.Path: The full file path of the application’s executable.Signature: (Windows only) The name of the application’s digital signer.TipTo find the signer’s name for an application, go to Discover and query the process name of the application’s executable (for example,
process.name : "mctray.exe"for a McAfee security binary). Then, search the results for theprocess.code_signature.subject_namefield, which contains the signer’s name (for example,McAfee, Inc.).
Operator: For hash and path conditions, the operator isis one ofand can’t be modified. For signature conditions, chooseis one ofto enter multiple values orisfor one value.Value: Enter the hash value, file path, or signer name. To enter multiple values (such as a list of known malicious hash values), you can enter each value individually or paste a comma-delimited list, then press Return.NoteHash values must be valid to add them to the blocklist.
Select an option in the Assignment section to assign the blocklist entry to a specific integration policy:
Global: Assign the blocklist entry to all Elastic Defend integration policies.Per Policy: Assign the blocklist entry to one or more specific Elastic Defend integration policies. Select each policy where you want the blocklist entry to apply.NoteYou can also select the
Per Policyoption without immediately assigning a policy to the blocklist entry. For example, you could do this to create and review your blocklist configurations before putting them into action with a policy.
Click Add blocklist. The new entry is added to the Blocklist page.
When you’re done adding entries to the blocklist, ensure that the blocklist is enabled for the Elastic Defend integration policies that you just assigned:
- Go to the Policies page, then click on an integration policy.
- On the Policy settings tab, ensure that the Malware protections and Blocklist toggles are switched on. Both settings are enabled by default.
The Blocklist page displays all the blocklist entries that have been added to the Elastic Security app. To refine the list, use the search bar to search by name, description, or field value.
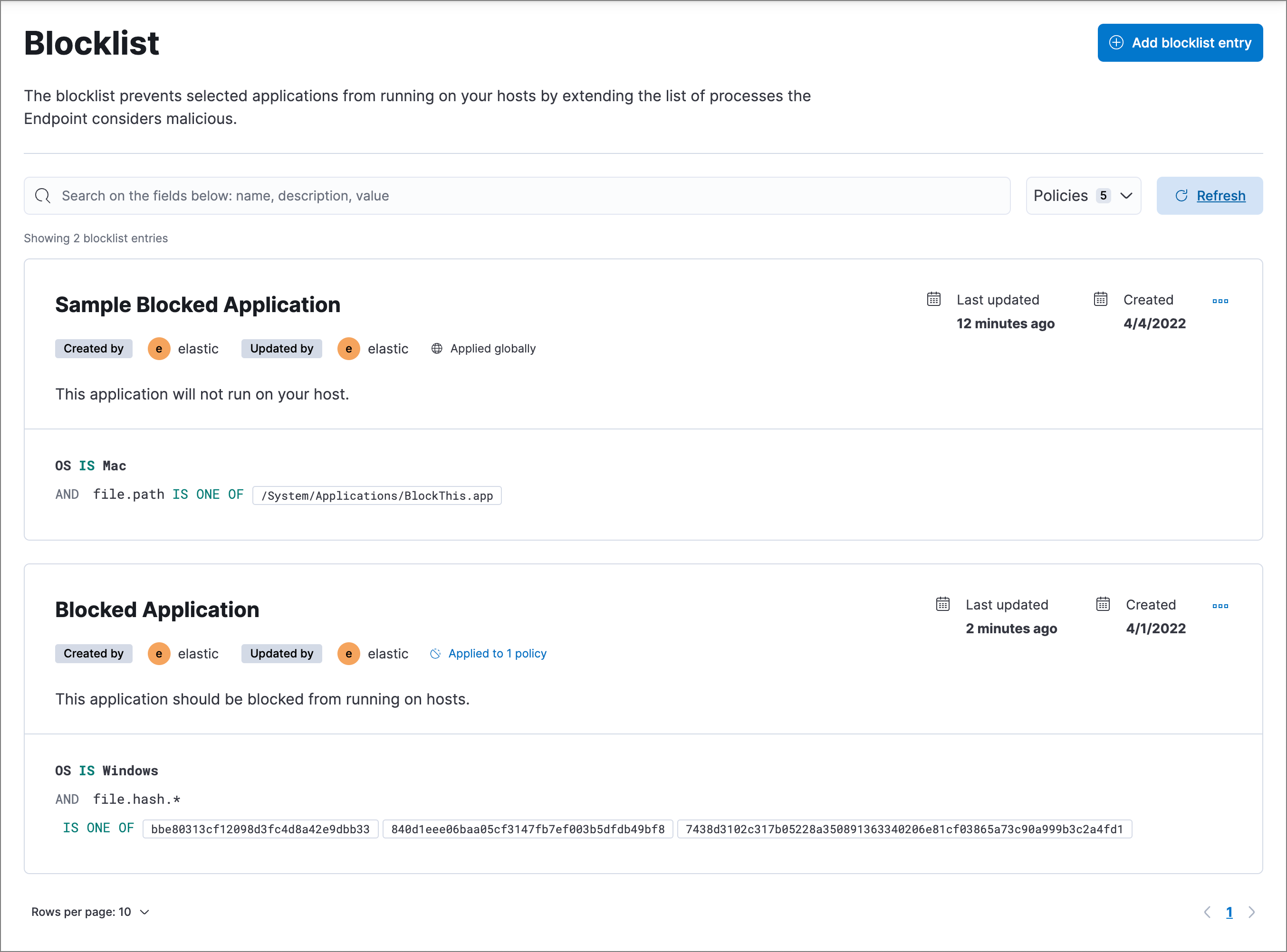
You can individually modify each blocklist entry. You can also change the policies that a blocklist entry is assigned to.
To edit a blocklist entry:
- Click the actions menu (…) for the blocklist entry you want to edit, then select Edit blocklist.
- Modify details as needed.
- Click Save.
You can delete a blocklist entry, which removes it entirely from all Elastic Defend policies. This allows end users to access the application that was previously blocked.
To delete a blocklist entry:
- Click the actions menu (…) for the blocklist entry you want to delete, then select Delete blocklist.
- On the dialog that opens, verify that you are removing the correct blocklist entry, then click Delete. A confirmation message displays.