AI made attacks faster. Your SIEM platform needs to catch up.
The stack managing them was built for a different threat environment. Every vendor-imposed barrier that was inefficient before adversarial AI is now a gap attackers use.
You're in good company
Customer spotlight
 Airtel improves cyber posture with Elastic’s AI capabilities, boosting SOC efficiency by 40% and accelerating investigations by 30%.
Airtel improves cyber posture with Elastic’s AI capabilities, boosting SOC efficiency by 40% and accelerating investigations by 30%.Customer spotlight

California EDD reduced mean time to response by 99%, using Attack Discovery to prioritize alerts across 80,000 monthly events and surface the most critical threats.
Customer spotlight
Mimecast centralizes visibility, drives investigations, and cuts critical incidents by 95%, transforming global SecOps.
DETECT. INVESTIGATE. RESPOND.
The SIEM built for the agentic SOC
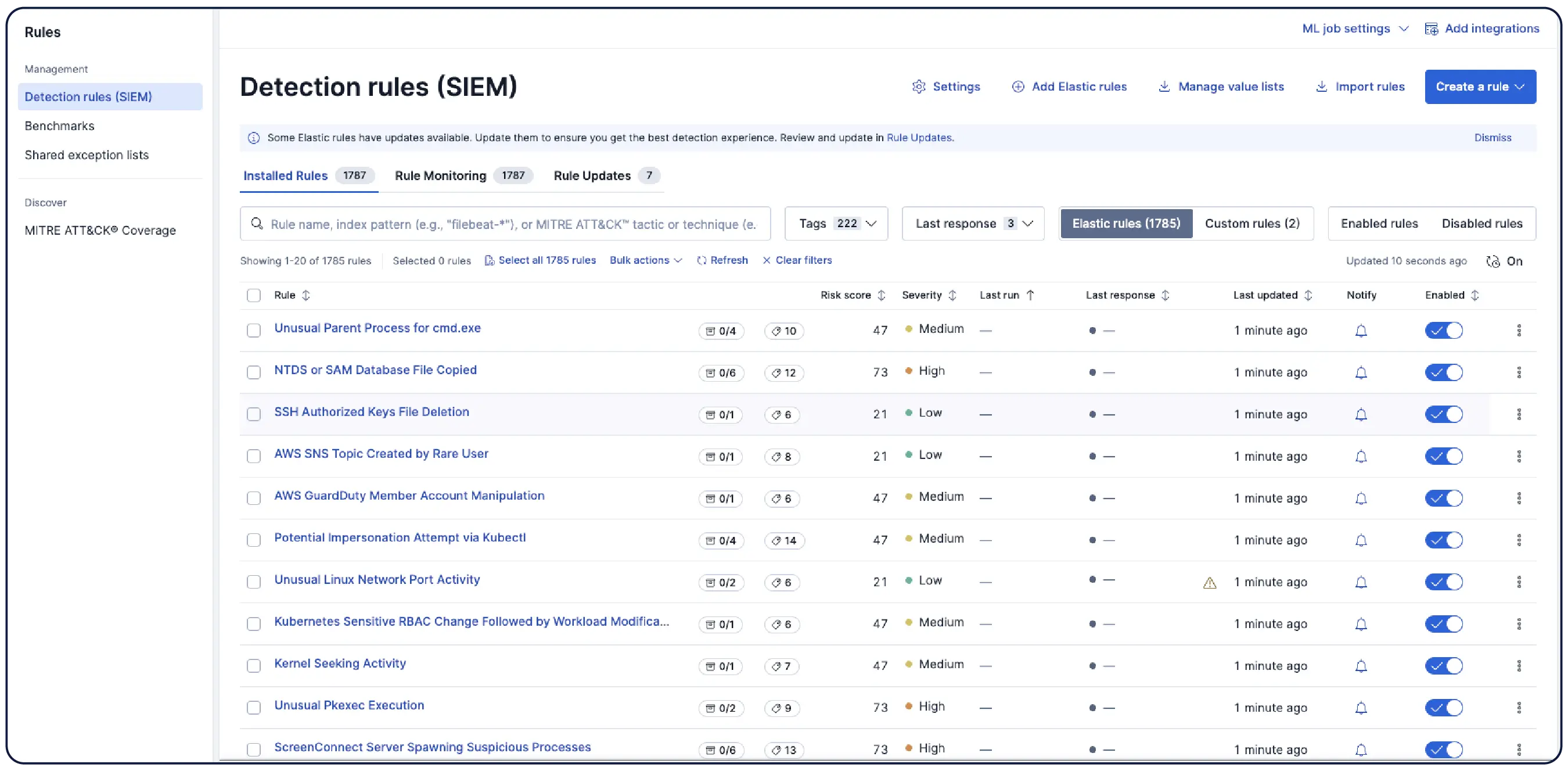
Detection to response, all in one platform. Autonomous agents run the full lifecycle. Your analysts handle judgment, verification, and approval.
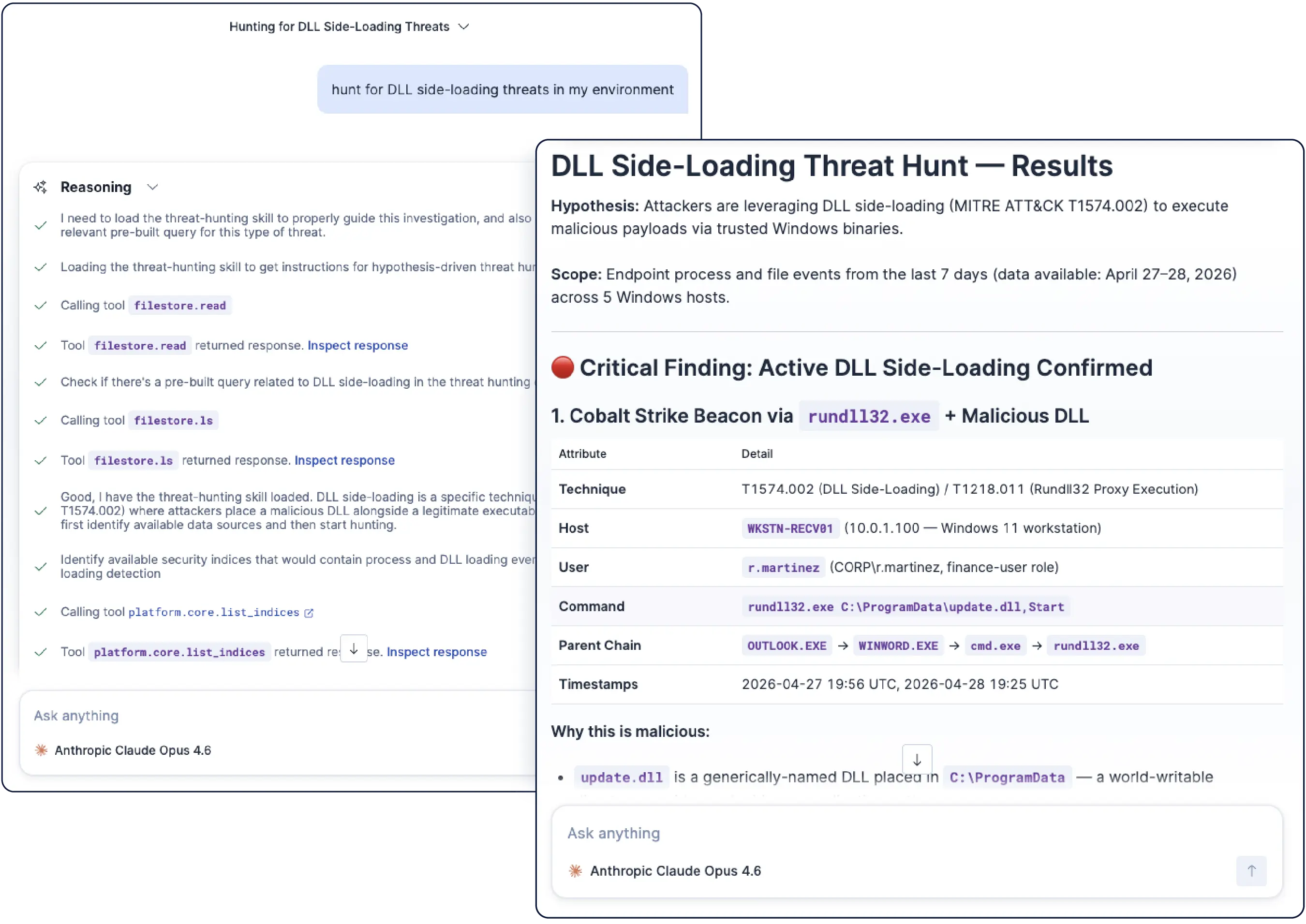
Find threats before they surface as alerts. The Threat Hunt skill executes hypothesis-driven hunts from threat intel, runs ES|QL queries against live data, and maps findings to MITRE ATT&CK automatically. For on-demand hunts, describe the threat in plain language and get a validated query built by Elastic Security Labs researchers.
Security where you work
The same composable AI skills, across every surface security analysts use
Chat-first, wherever you work
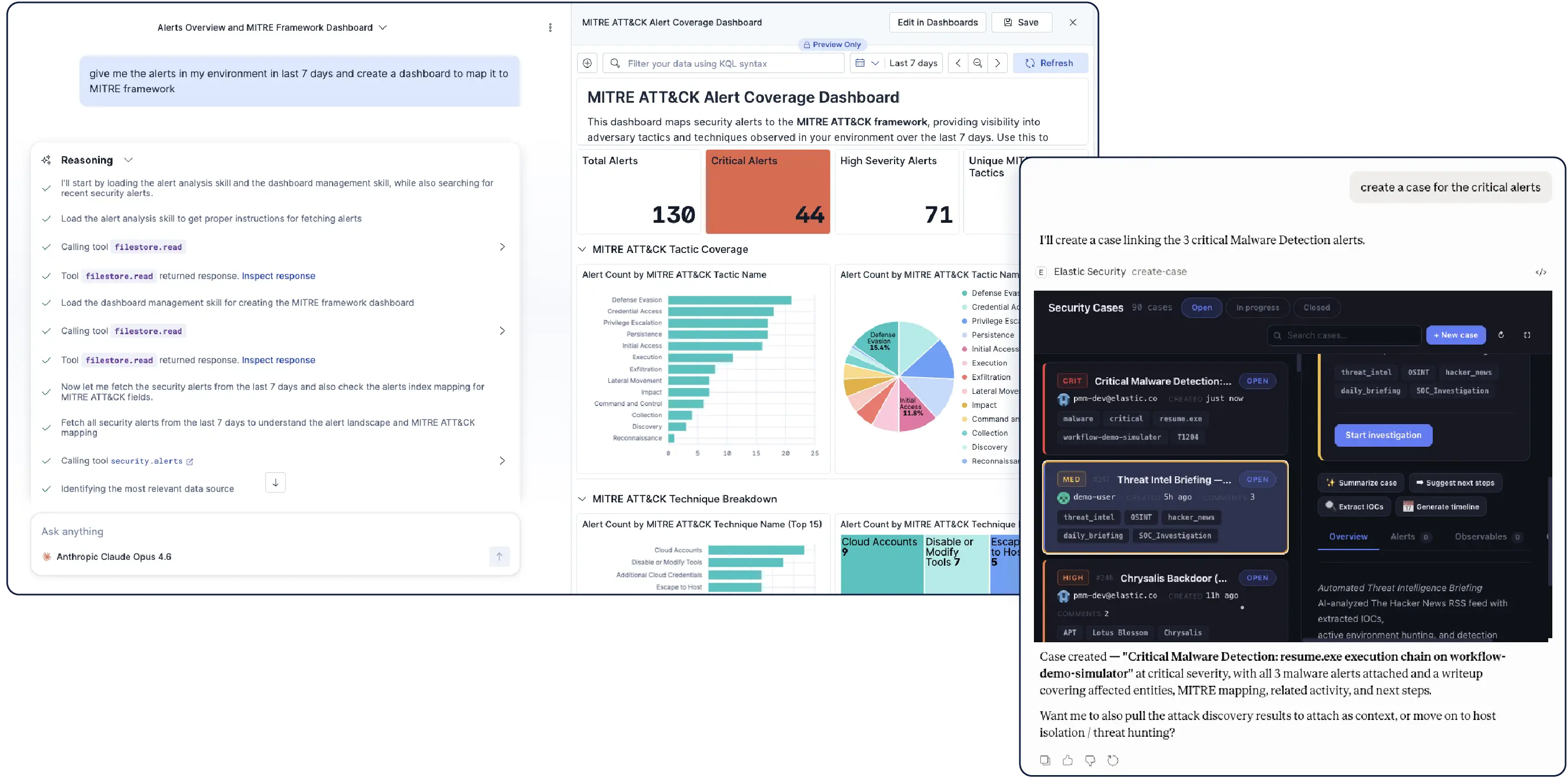
Ask questions and get interactive triage dashboards, investigation graphs, editable detection rules, attack chains, and case actions — from inside Elastic Security or directly from Claude, VS Code, Cursor, and any MCP-compatible AI tool.
Purpose-built product views
Implement structured workflows for the full SOC lifecycle. Triage queues, incident response with approval gates, case management, detection engineering, and AI skill monitoring all happen in one platform, no console switching.
Join the chat
Connect to Elastic Security's global community — from open conversations and collaboration to hardening our product.
Frequently asked questions
What is a SIEM?
What is a SIEM?
A SIEM — security information and event management — is the platform at the center of security operations. It collects and correlates data across an environment, detects threats, and gives analysts the visibility to investigate and respond. Modern SIEMs have evolved into agentic security operations platforms — incorporating AI-driven detection, automated investigation, and native response capabilities across the full SOC lifecycle, where autonomous agents handle the work and analysts handle the judgment.
How does Elastic SIEM support agentic security operations?
How does Elastic SIEM support agentic security operations?
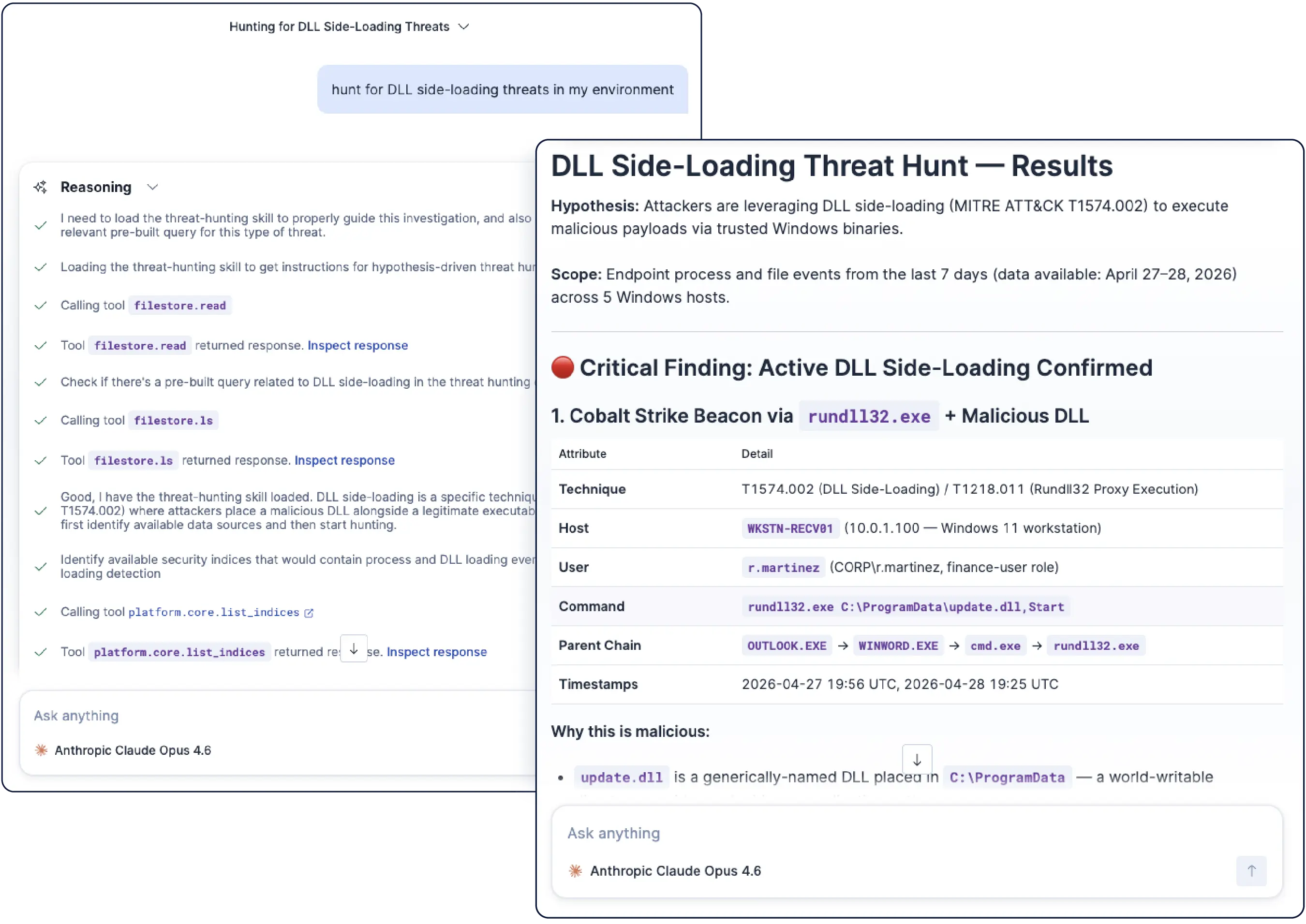
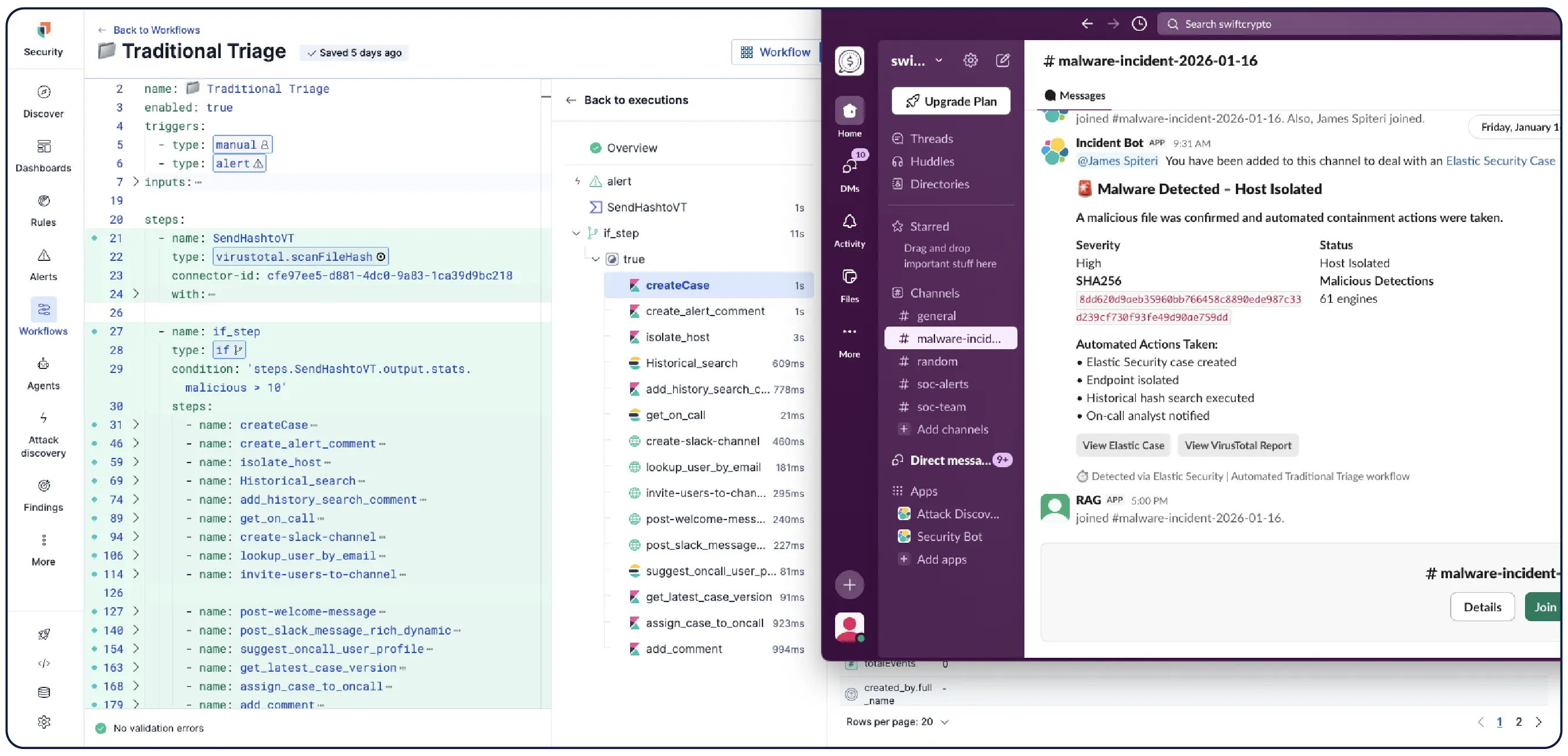
Elastic is the agentic security operations platform that already includes unified SIEM and XDR. Autonomous agents handle the full lifecycle from ingestion through response — correlating alerts, investigating entities, and staging response plans. Native automation through Elastic Workflows executes the response: scripted playbooks for defined tasks, agentic reasoning for complex investigations. The Elastic AI Agent ships with purpose-built skills for every SOC stage out of the box. Analysts handle judgment, verification, and approval.
What are AI skills in security operations?
What are AI skills in security operations?
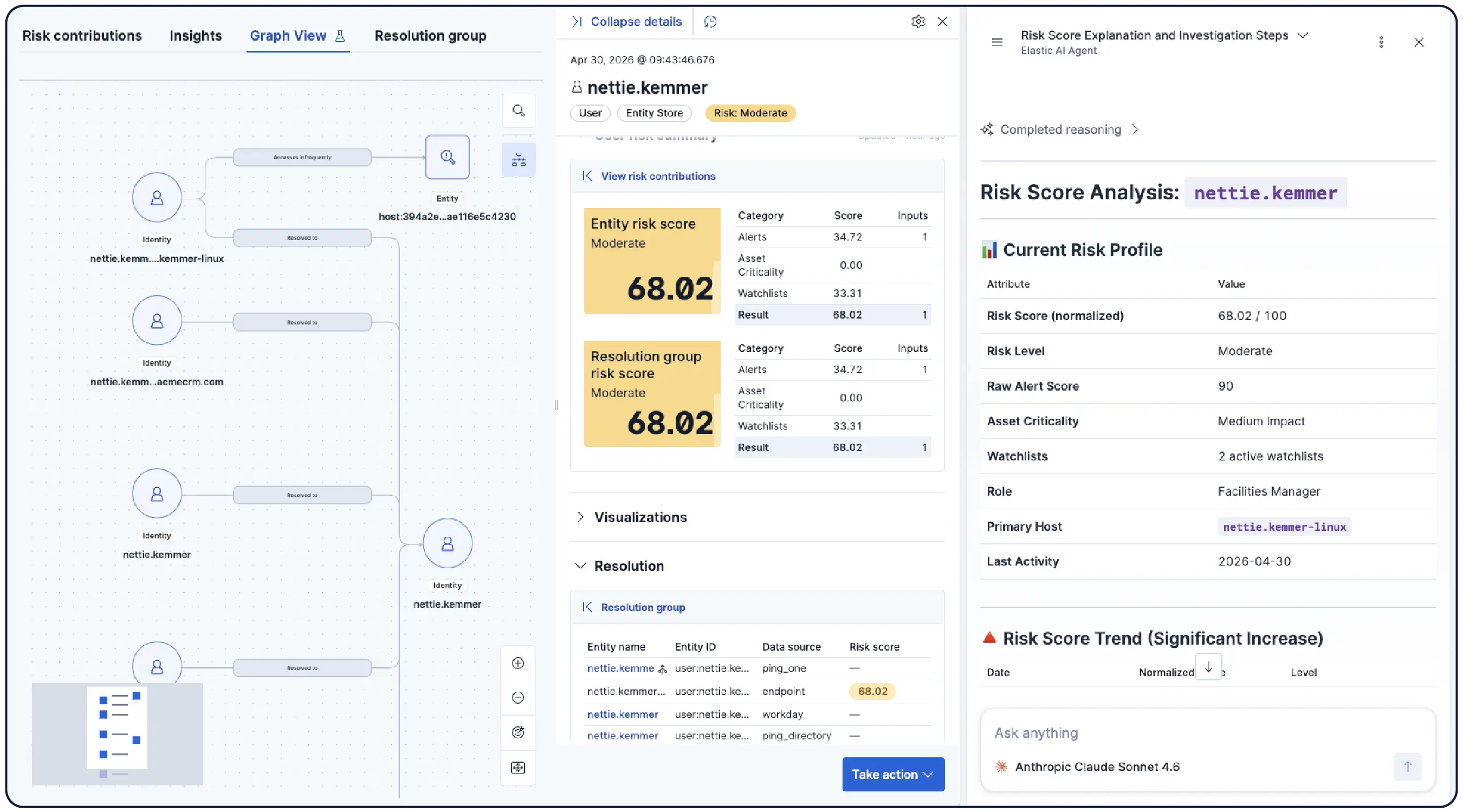
AI skills are purpose-built capabilities that teach an AI agent how to perform a specific security task — threat hunting, alert analysis, detection engineering, entity analytics, and more. Unlike general-purpose AI, skills are designed for the exact workflows SOC analysts run every day. Each skill packages specialized instructions and tools for a single job, loading only when needed — keeping the agent lightweight and accurate rather than overloaded with a bloated system prompt. Skills also work together — Alert Analysis hands off to Entity Analytics, and Threat Hunting feeds the detection pipeline — without the analyst managing each handoff. One agent, the right skill, every time.
How do AI skills run in Elastic Security?
How do AI skills run in Elastic Security?
Elastic ships security skills out of the box with the Elastic AI Agent — no configuration required. Out-of-the-box security skills cover threat hunting, alert analysis, detection engineering, entity analytics, and anomaly investigation. Platform skills for dashboard creation, workflow authoring, and graph creation are also available, letting analysts build dashboards, write automation, and visualize attack paths through conversation. Skills invoke each other automatically and run via Workflows or on-demand through Agent Builder. Teams can also build custom skills tailored to their environment. Skills are accessible inside Elastic Security or from any MCP-compatible AI tool including Claude, Cursor, and VS Code. Every reasoning step is visible and auditable.
How does Elastic SIEM work with AI tools like Claude and Cursor?
How does Elastic SIEM work with AI tools like Claude and Cursor?
Elastic Security is accessible from any MCP-compatible AI tool — including Claude, Cursor, VS Code, and GitHub Copilot. Through the Elastic Security MCP App, analysts can triage alerts, run threat hunts, manage cases, and interact with detection rules without leaving the AI tool they're already working in. The same skills available inside Elastic Security are available externally. Security work happens wherever the analyst is, not just inside a dedicated console.
Does Elastic SIEM include SOAR?
Does Elastic SIEM include SOAR?
Yes. Elastic Workflows brings native automation directly into Elastic Security — where your security data already lives in the SIEM. It automates triage, enrichment, response, notification, and case management across every alert and investigation. Workflows combines scripted automation for defined tasks and agentic reasoning for complex investigations enabling AI agents to act on their findings. No separate SOAR to buy, integrate, or maintain. No integration that breaks during an active incident.
What makes Elastic SIEM different from legacy SIEM platforms?
What makes Elastic SIEM different from legacy SIEM platforms?
Elastic is the agentic security operations platform that unifies SIEM, XDR, and native automation. Detection rules are developed by Elastic Security Labs, validated by the community, and open for review. The platform deploys on-premises, in the cloud, or in air-gapped environments without moving data. Where legacy SIEMs impose structural taxes — on endpoints, automation, AI, and data access — Elastic is built to remove them.
What are the hidden taxes in legacy SIEM platforms?
What are the hidden taxes in legacy SIEM platforms?
Legacy security platforms impose four structural taxes on SOC teams — costs and barriers that were inefficient before adversarial AI and are now a liability.
- The endpoint tax: Per-device pricing that forces coverage tradeoffs. Teams leave endpoints unmonitored because the cost of full coverage is prohibitive. Elastic includes XDR and endpoint telemetry with no per-device fee — every endpoint covered, no coverage decisions driven by a pricing model.
- The automation tax: A separate SOAR license required to make the SIEM take action. Elastic Workflows is native to the platform. No separate product to buy, integrate, or maintain.
- The AI black-box tax: Proprietary AI that hides its reasoning, leaving teams unable to validate decisions made on their behalf. Elastic's AI is transparent — see the prompts, queries, and reasoning behind every decision. Any LLM, including on-premises models for air-gapped environments.
- The data tax: Rehydration delays and ingestion caps that put historical data out of reach during active investigations. Elastic queries data where it lives — years of historical data searchable in the same query as live data, no rehydration wait, no penalty.
Together these four taxes — endpoint, automation, AI black-box, and data — represent structural barriers that fragment security operations and create gaps adversaries exploit. Elastic is designed to remove all four.
Can Elastic SIEM run in air-gapped or on-premises environments?
Can Elastic SIEM run in air-gapped or on-premises environments?
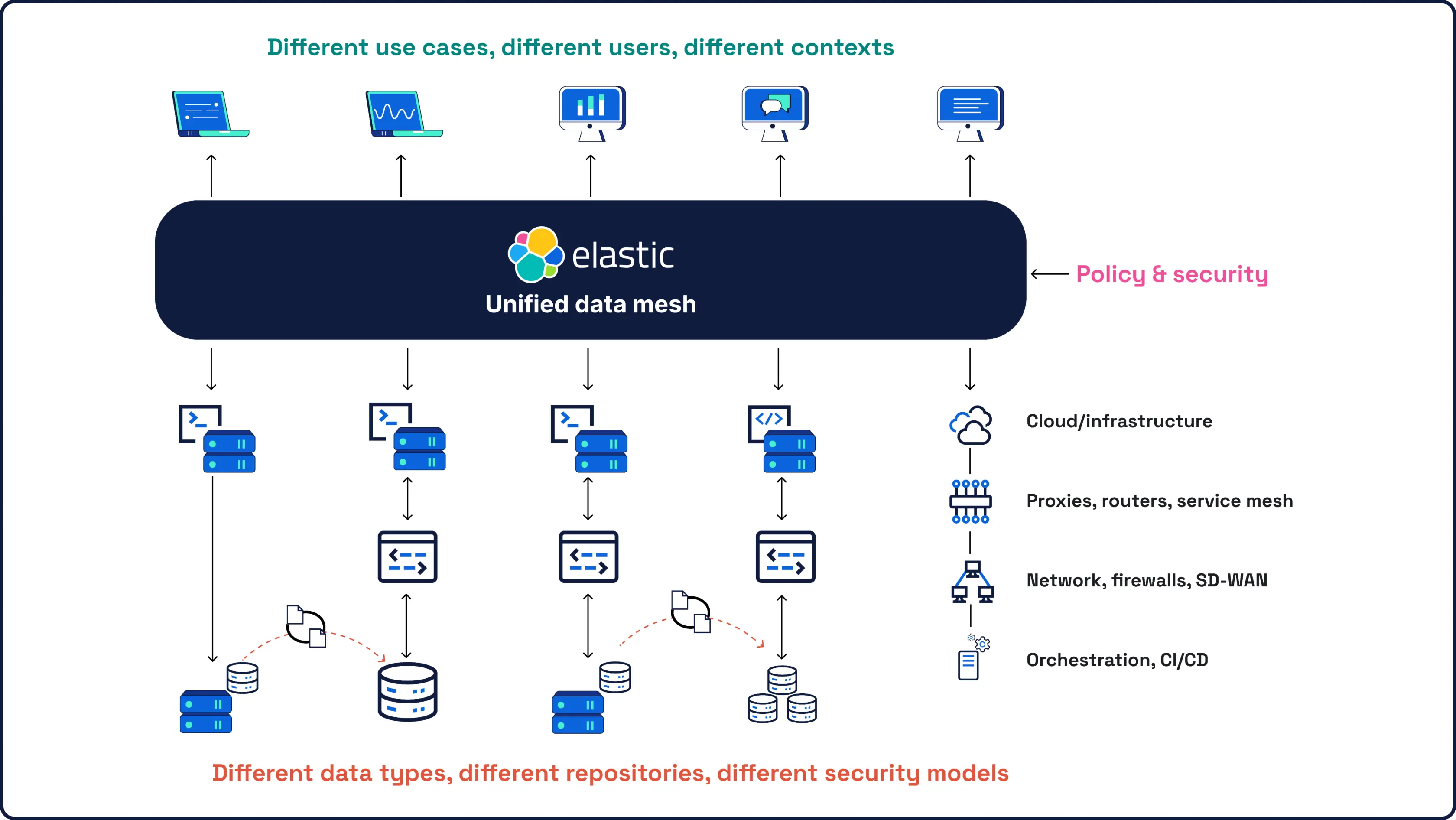
Yes. Elastic deploys on-premises, in the cloud, or in air-gapped environments with no data movement required. Federated search runs queries across distributed deployments without centralizing data. AI reasoning supports on-premises LLMs for air-gapped environments — no dependency on a vendor's cloud model. Elastic Cloud holds certifications including PCI DSS, HIPAA, FedRAMP, GDPR, and TISAX, with full documentation available in our Trust Center. This makes Elastic the platform of choice for defense, government, and regulated industries with strict data residency and compliance requirements.
What data sources does Elastic SIEM support?
What data sources does Elastic SIEM support?
Elastic supports 400+ prebuilt integrations and up to 1,000 total security and data source integrations. When a new source connects, the platform identifies the data type, maps the schema automatically, and recommends detection rules — no pipeline engineering required. Universal schema support across ECS and OCSF means a detection written once works across sources. Data shipped via OpenTelemetry is supported natively.











.jpg)
