Continuous Monitoring
Elastic Security for continuous monitoring
Fuse data from across your attack surface to eliminate blind spots, empower practitioners, and reduce risk. All with continuous monitoring across your on-premises and cloud-based infrastructure.
Validated by security experts
Security teams around the world establish holistic visibility with continuous monitoring on Elastic Security.
Customer spotlight

Randstad ingests 73 million events per hour from dozens of sources.
Customer spotlight
Postbank stops fraud and secures retail banking sites with Elastic.
Customer spotlight

MISI boosts cyber resilience by achieving rich visibility with Elastic.
Eliminate blind spots and data silos
You can't stop what you can't see, so bring your data together in Elastic Security.
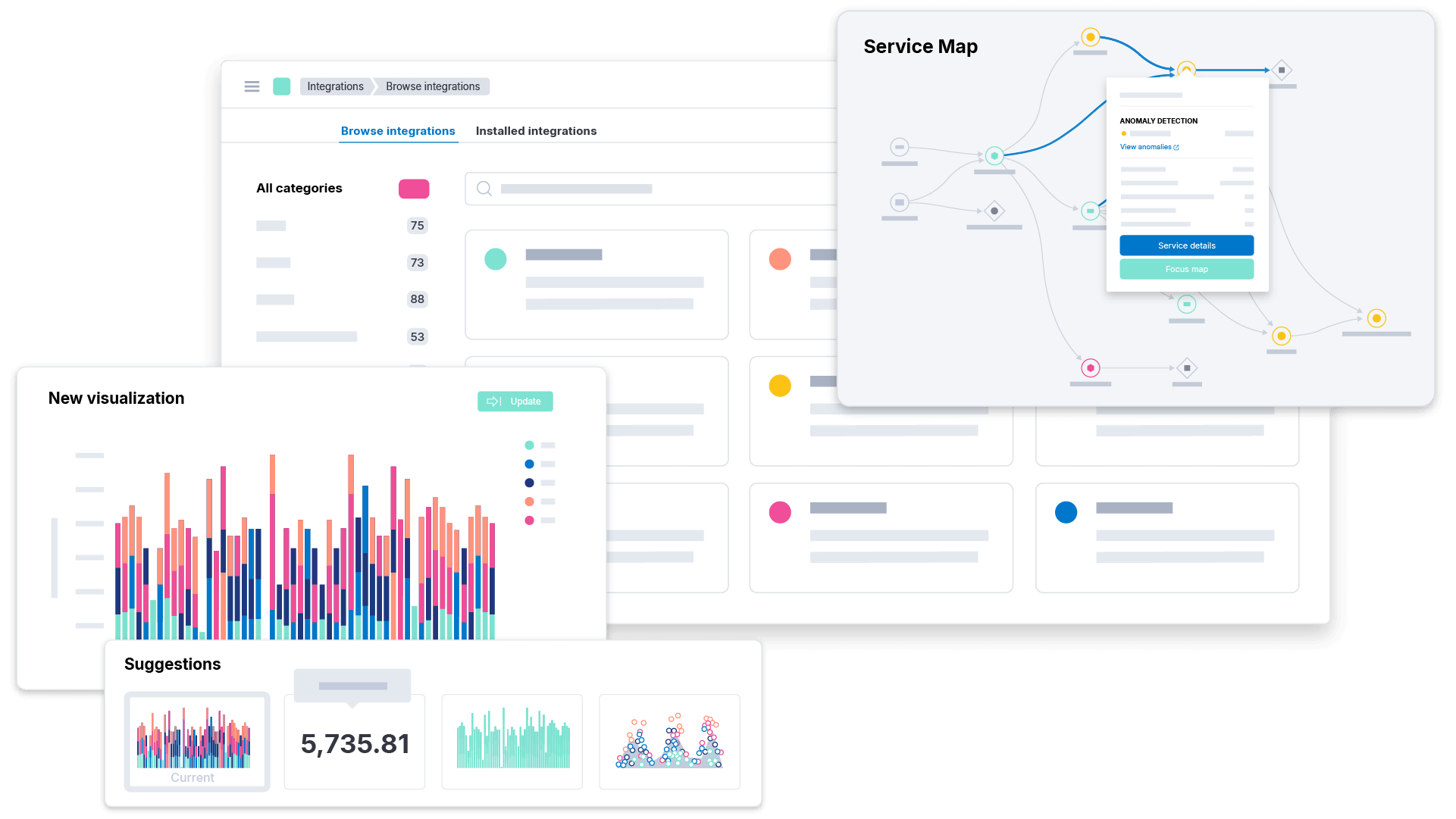
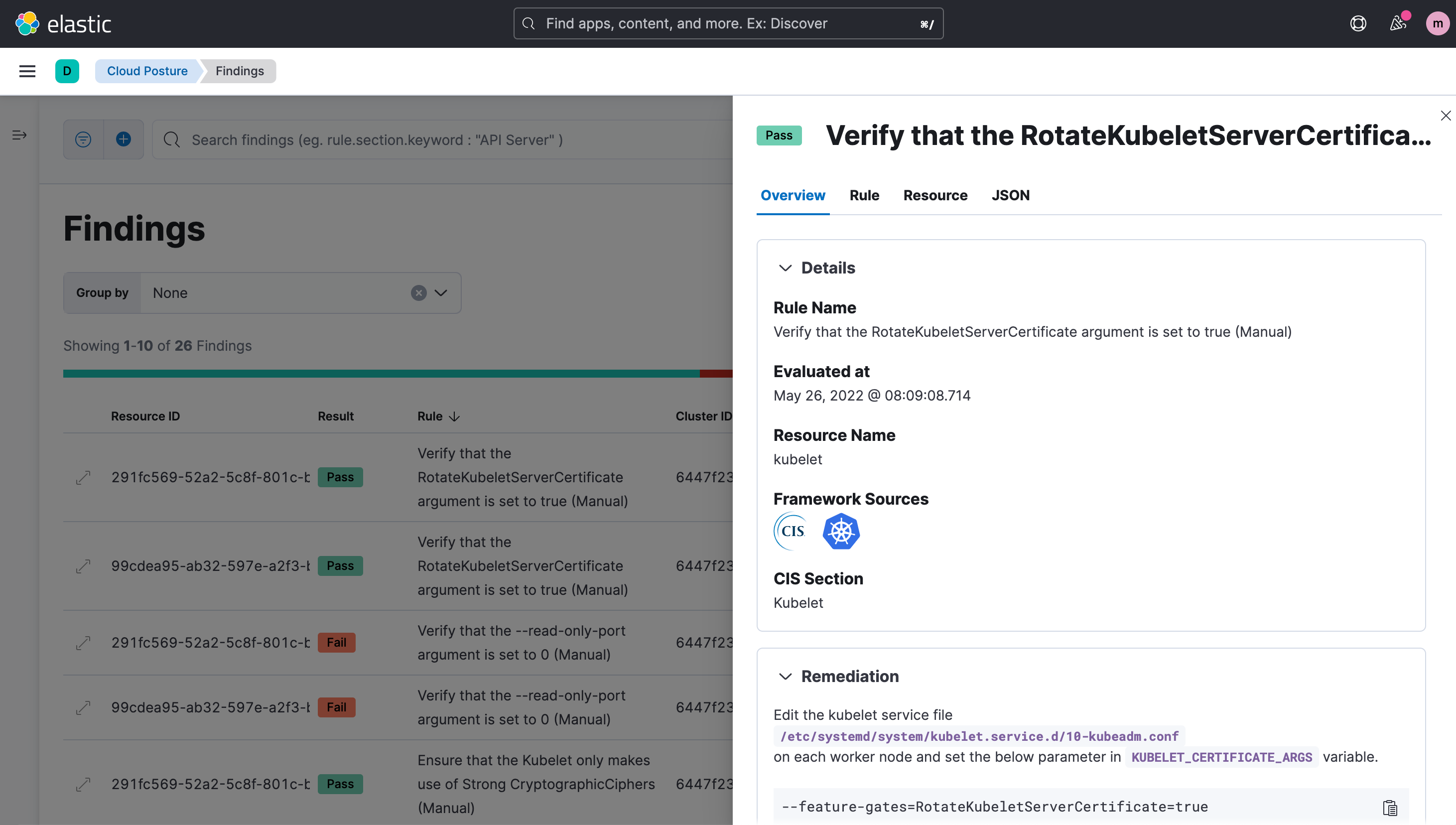
Cloud and application monitoring
Protect platforms like AWS, GCP, and Azure from data theft, resource hijacking, and sabotage. Observe container security and health. Safeguard distributed workplaces by tracking IT and security applications from Azure AD to Zoom.
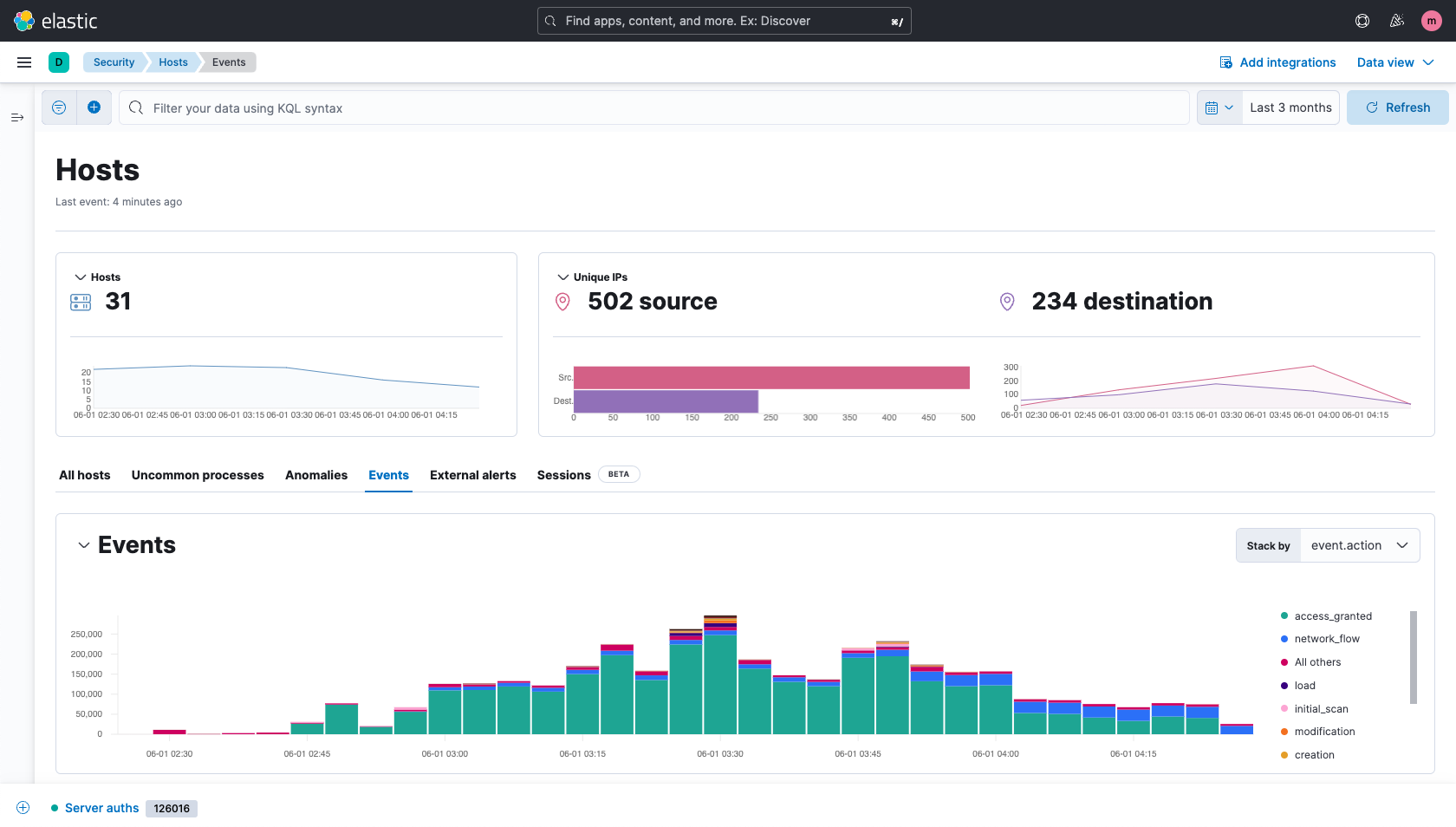
Infrastructure and host monitoring
Monitor mission-critical environments in the cloud, data center, and beyond. Deepen visibility with kernel-level data collection from Windows, macOS, and Linux systems. Consolidate alerts from endpoint security technologies and other third-party tools.
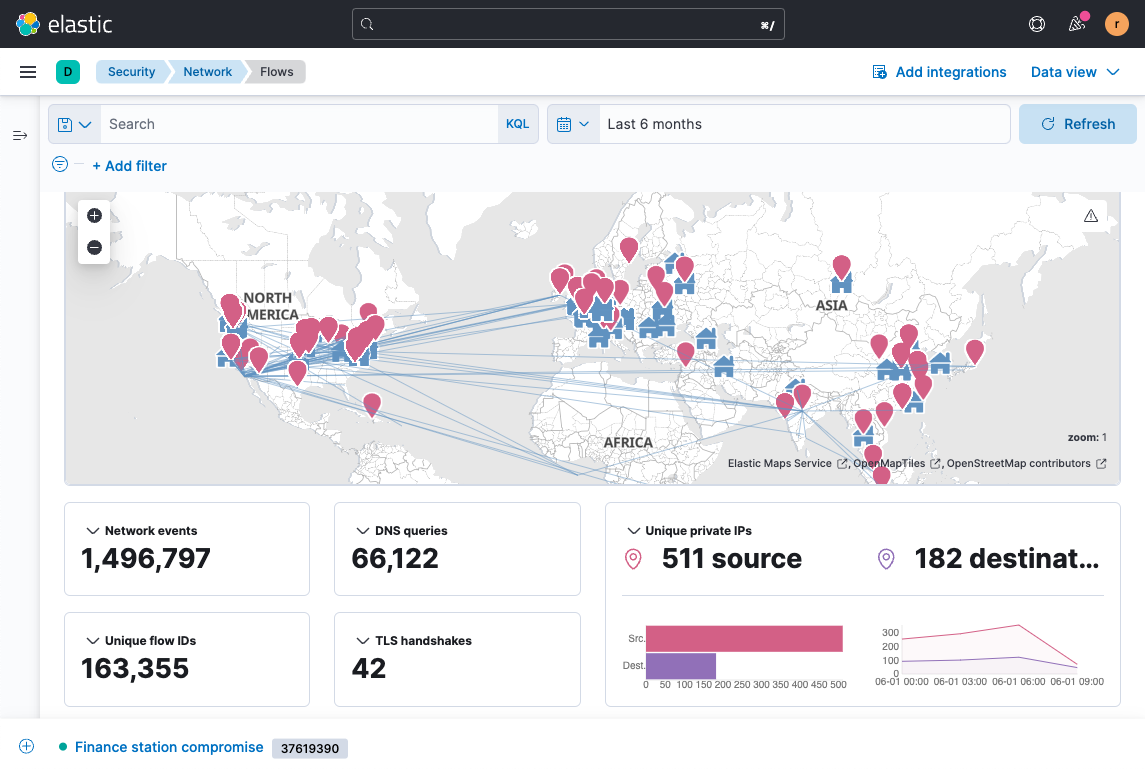
Network activity monitoring
Monitor network data to establish broad environmental visibility, uncover suspicious activity, and inform investigations. Rapidly integrate commercial IT and security products — plus protocols like DNS, HTTP, NetFlow, TLS, and SMTP. See even deeper by capturing network packets with Elastic Agent.
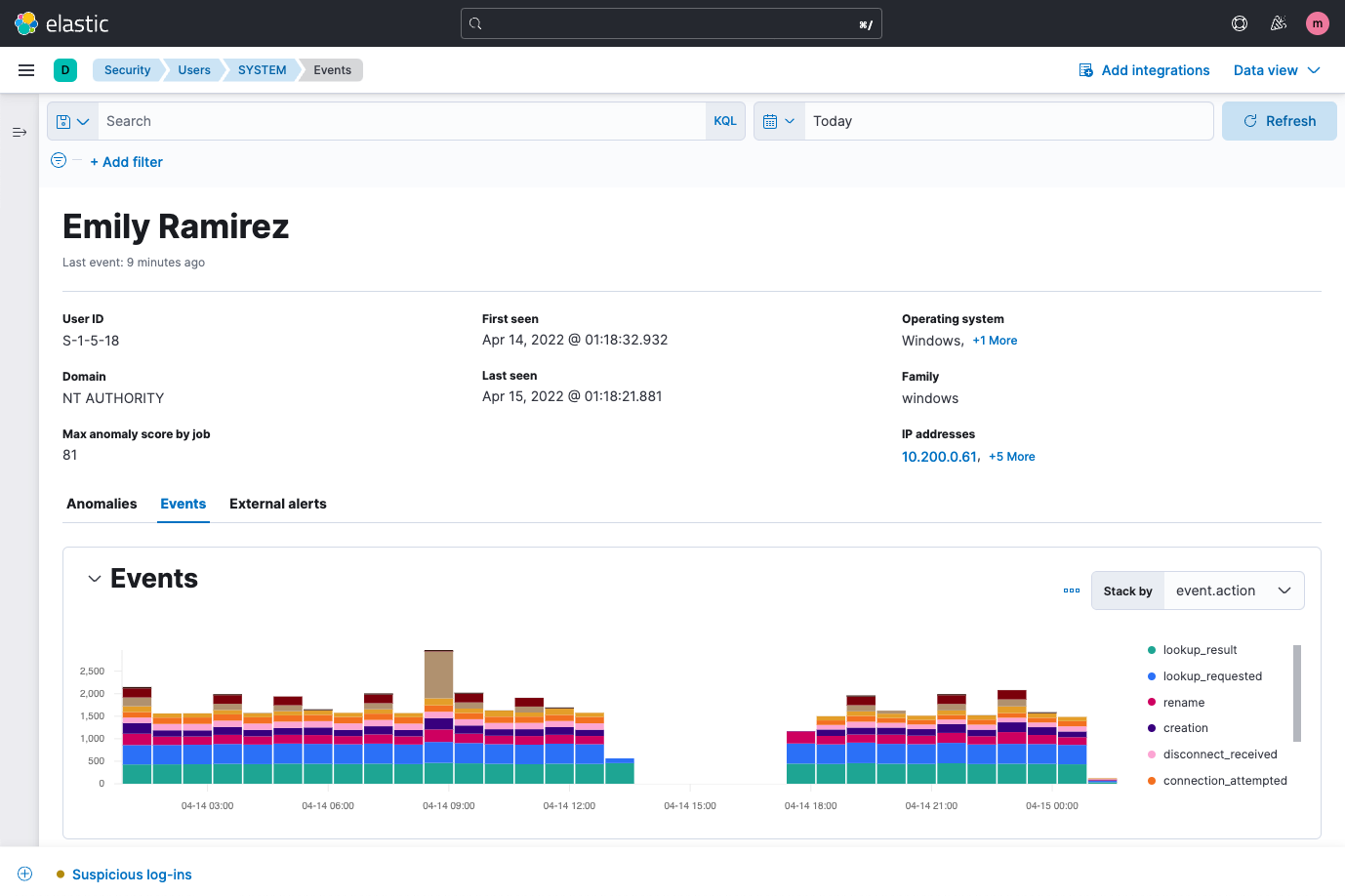
User activity monitoring
Safeguard your organization from theft and sabotage by monitoring user activity and context for signs of insider threats, compromised accounts, and privilege abuse. Focus on an individual user to see key attributes, observed activity, and associated anomalies and alerts.
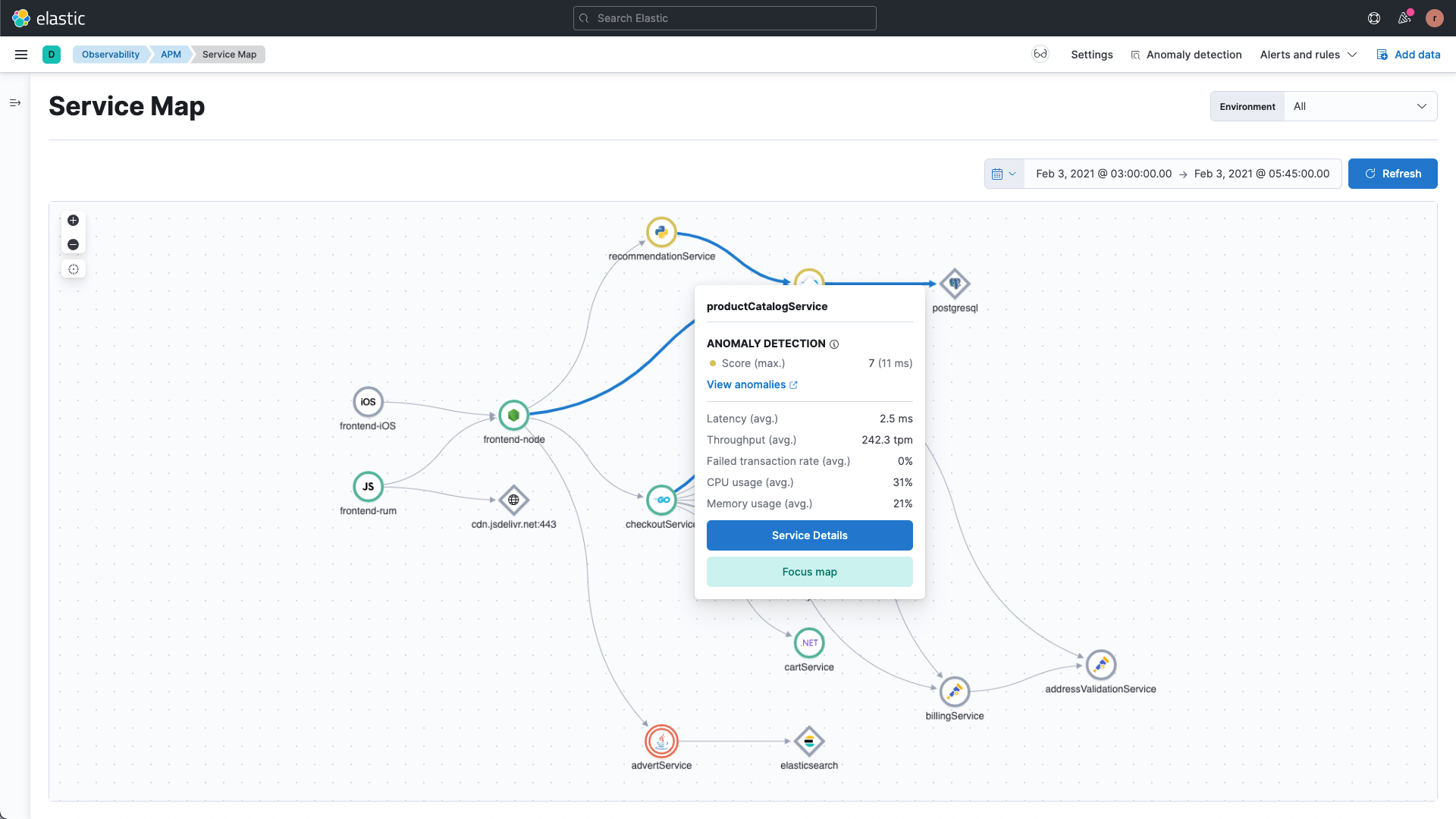
Custom security monitoring
Visualize non-traditional data sources — APM traces, metrics, business analytics, and others — to glean novel insights. Track organizational security posture and team performance. Monitor and share top-level findings on bespoke dashboards.
Do more with Elastic
Bring the speed, scale, relevance, and simplicity of Elastic to teams of all types.
Security
Prevent, detect, and respond to threats — quickly and at scale.
Observability
Analyze logs, metrics, and APM traces in a single stack.
Enterprise Search
Power search experiences for your workplace, website, or apps.



