Cyber investigation and Response
Elastic Security for investigation and incident response
Empower practitioners and collaborate beyond the SOC. Accelerate investigation and response to foil unfolding attacks. Continually improve efficiency with AI-driven security analytics.
Validated by security experts
Security teams around the world investigate and respond to cyber threats with Elastic Security.
Customer spotlight

ECI responds to external attacks and insider threats with Elastic.
Customer spotlight
OmniSOC protects five university systems from advanced threats with Elastic.
Customer spotlight

PSCU investigators reduced dwell time by 99% with Elastic.
Accelerate cyber investigation and incident response
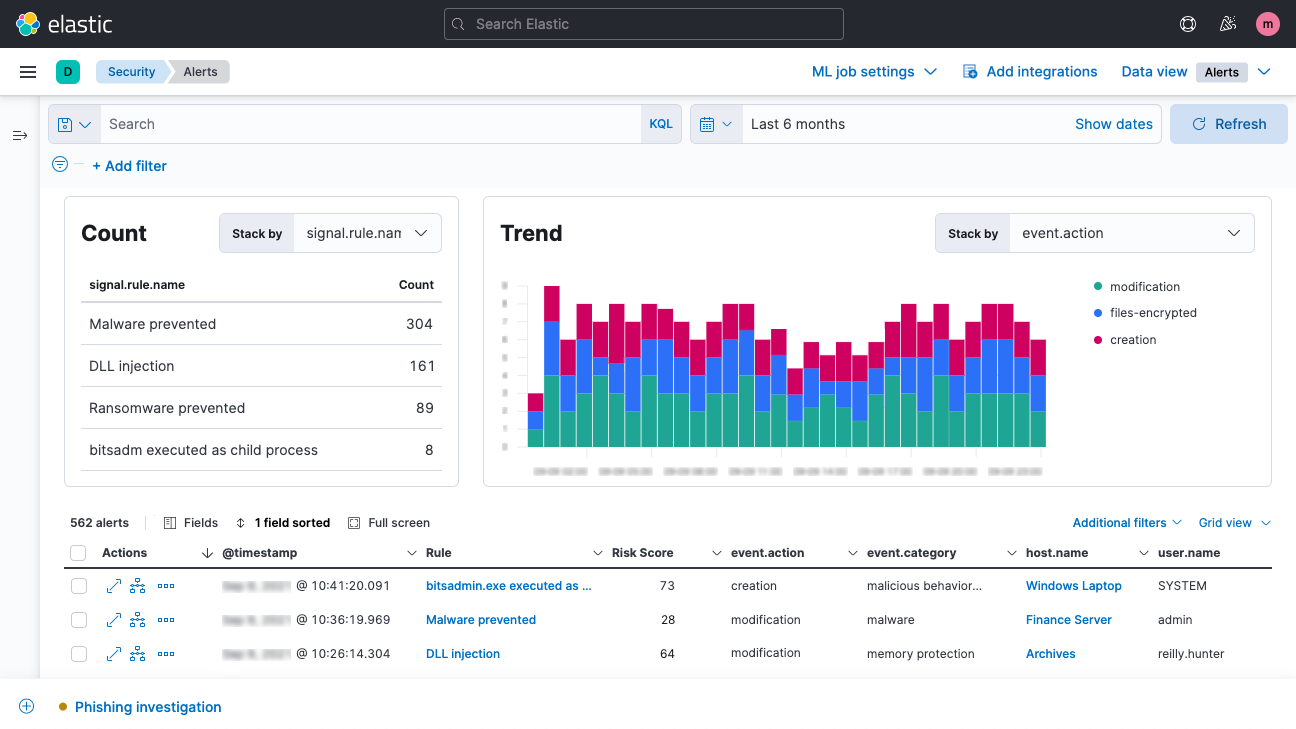
Tighten investigation and response times to neutralize threats before damage is done.
Get immediate answers
Incident investigation and response is a sprint…and a marathon. Outpace adversaries — through each investigation — by eliminating the cognitive load caused by scattered data and prolonged query times.
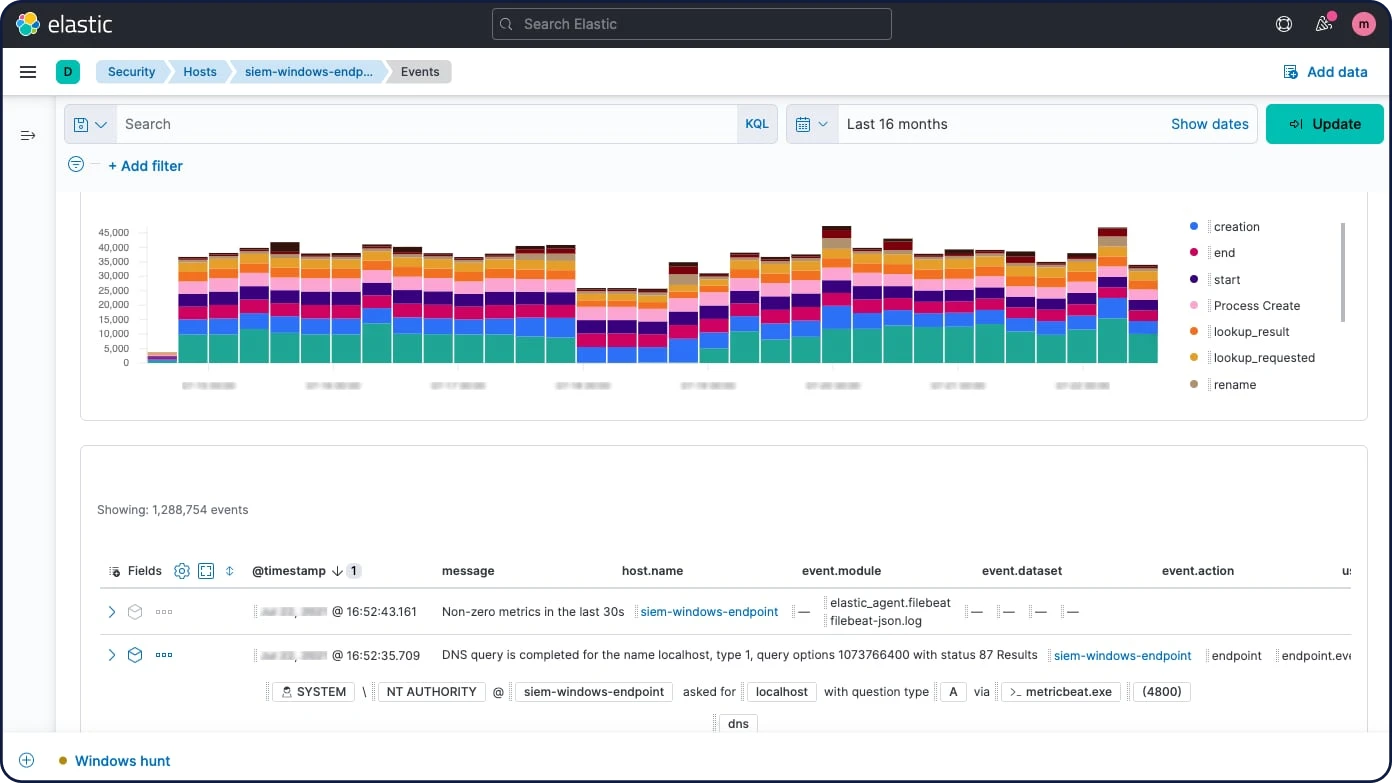
Tap into years of archives
Unleash analyst productivity with a security platform built for massive scale. Wield years of actionable archives retained in fully searchable, low-cost object stores to confidently determine incident root-cause and scope. Ensure comprehensive remediation by drilling down and pivoting anywhere the investigation takes you.
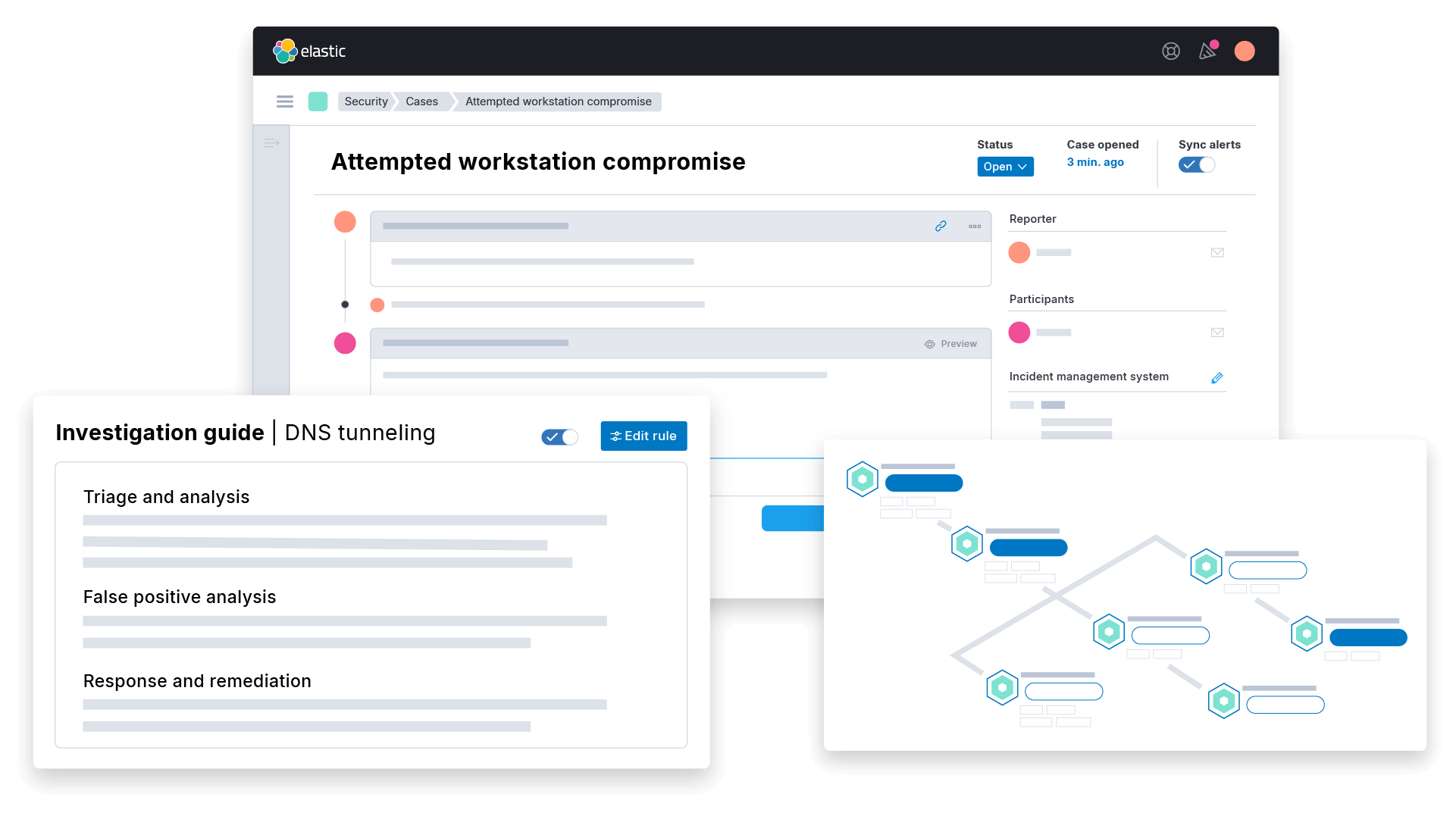
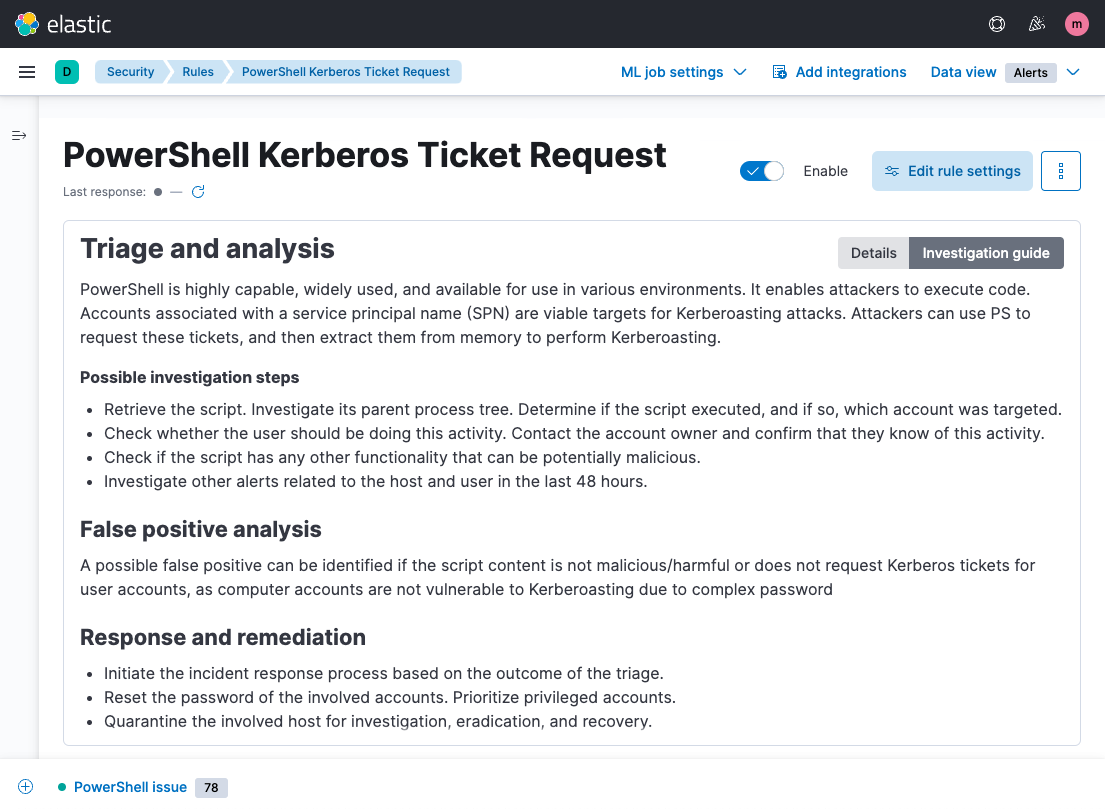
Standardize key processes
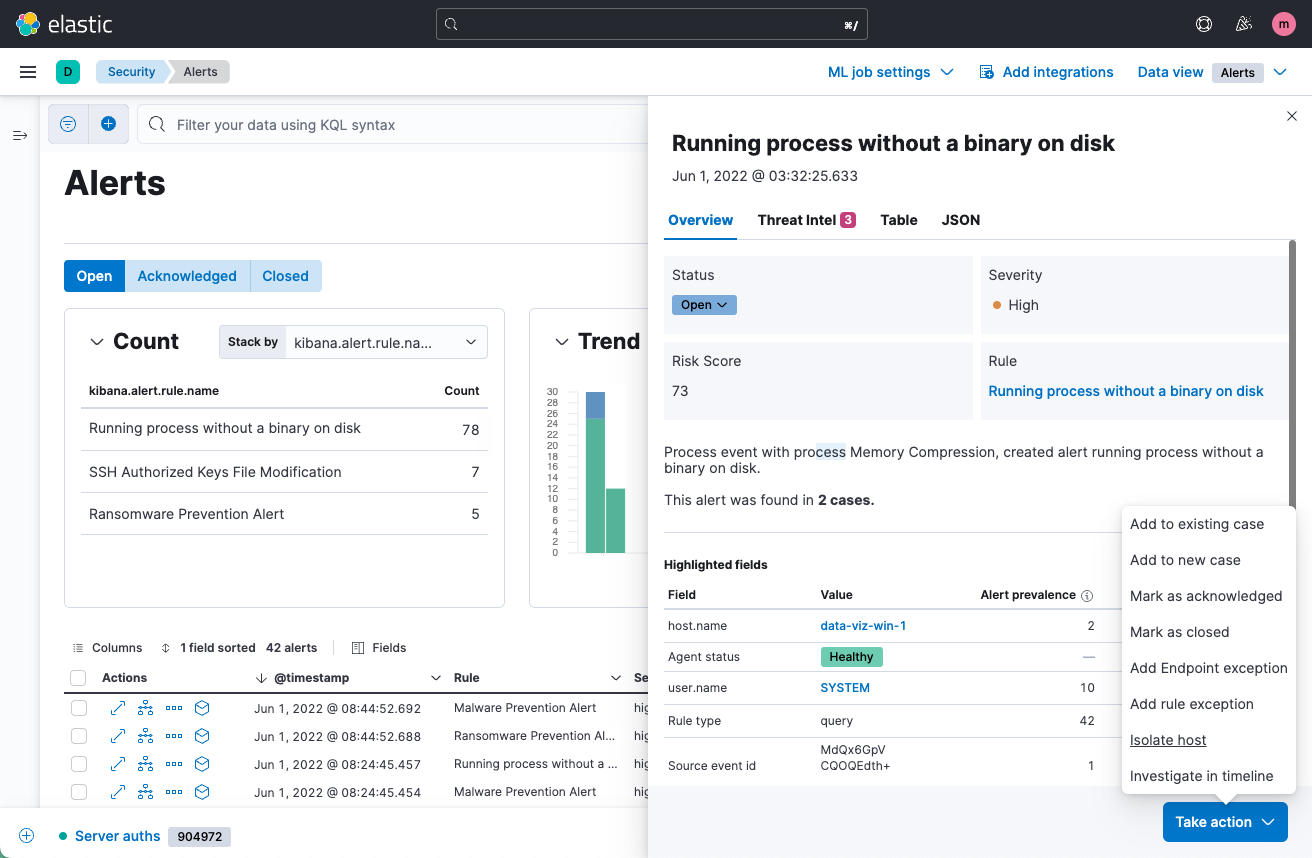
Triage, investigate, and respond to alerts with investigation guides outlining why an alert fired, how to determine whether it represents a true threat, and which steps to take next. With expert advice from Elastic Security Labs researchers, our built-in playbooks lower the learning curve for junior analysts and augment the knowledge of seasoned practitioners.
Follow your instincts
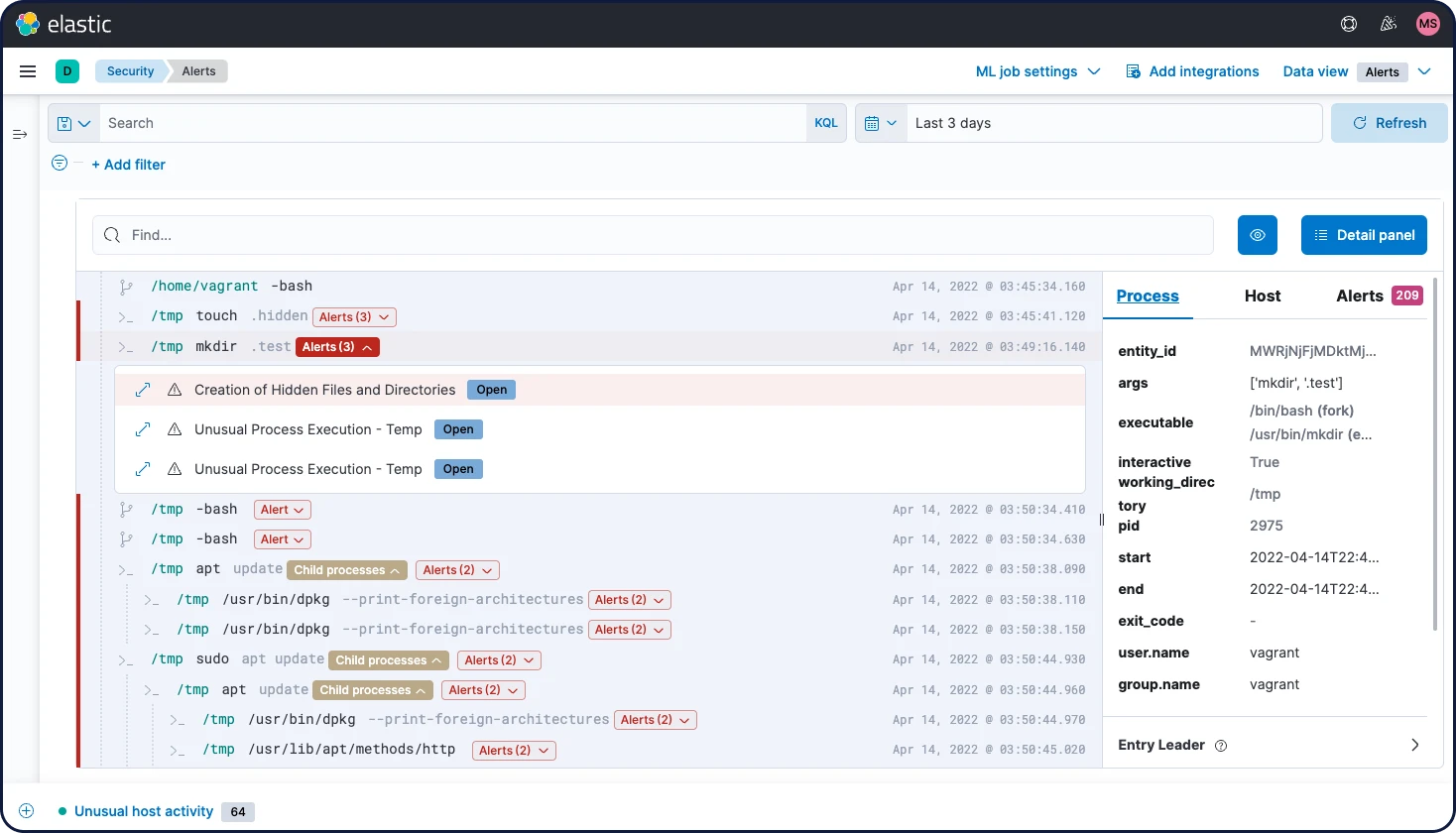
Discover connections between disparate data points on a unified investigation timeline. Scrutinize individual users and hosts, and examine a terminal-like view of the services running on key systems. Easily access internal and external context, including threat intelligence, host anomaly score, alert attribute counts, and more.
Remediate rapidly
Perform remediation across the entire enterprise using collected data and the power to invoke automated actions across distributed endpoints. Coordinate efforts with built-in case management. Collaborate across teams leveraging integrations with external security and ticketing workflow tools.
Do more with Elastic
Bring the speed, scale, relevance, and simplicity of Elastic to teams of all types.
Security
Prevent, detect, and respond to threats — quickly and at scale.
Observability
Analyze logs, metrics, and APM traces in a single stack.
Enterprise Search
Power search experiences for your workplace, website, or apps.



