Author
Articles by Craig Chamberlain
Head of Detection Science, Elastic
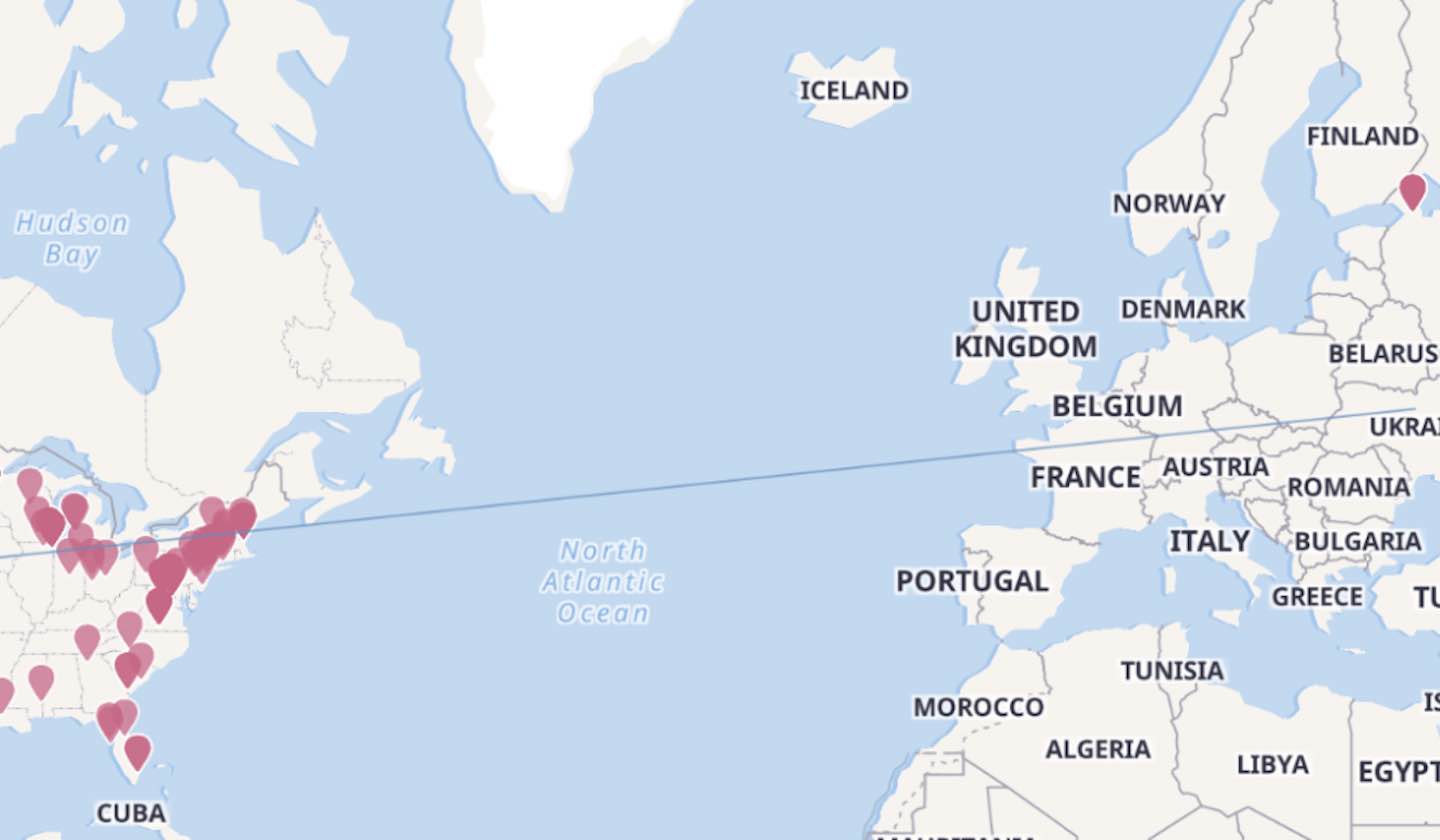
46 days vs. 16 minutes: Detecting emerging threats and reducing dwell time with machine learning
Using ML-based anomaly detection, such as the unsupervised ML jobs in the Elastic stack, we can shrink the dwell time for this malware persistence mechanism from 46 days to less than one day, a decrease by a factor of 1100!

ProblemChild: Generate alerts to detect living-off-the-land attacks
In this blog post, we walk through our release of a fully trained detection model, anomaly detection configurations, and detection rules that you can use to get your ProblemChild framework up and running in your environment in minutes.
Generating MITRE ATT&CK® signals in Elastic SIEM: Sysmon data
In this post, we outline a straightforward approach to detecting threats with Elastic SIEM that doesn't require any specific programming, or analytical knowledge — it's perfect for helping just about any security practitioner stay ahead of attacks.
Sign up for Elastic Cloud free trial
Spin up a fully loaded deployment on the cloud provider you choose. As the company behind Elasticsearch, we bring our features and support to your Elastic clusters in the cloud.