How we use Elastic at Square Enix to develop videogames securely
Editor’s Note — August 19, 2020: The Elastic SIEM solution mentioned in this post is now referred to as Elastic Security. The broader Elastic Security solution delivers SIEM, endpoint security, threat hunting, cloud monitoring, and more. If you're looking for more specific information on Elastic Security for SIEM use cases, visit our SIEM solution page.
I’ve participated in many security projects at multiple workplaces throughout my career and, amongst many other responsibilities, I am now leading the design and engineering effort for a custom security analytics platform at my current employer, Japanese videogame maker Square Enix.
For security analytics at Square Enix, and at other workplaces, I’ve chosen Elastic. At Square Enix, our previous managed security operations service had been supplied by an external third party. It wasn’t cost effective, adding new data sources was slow, and it simply wasn’t as scalable as Elastic. Many of our data sources are also bespoke or have non-standard formats, so being able to parse and manipulate these in detail, using Elastic components such as Logstash, was an additional advantage.
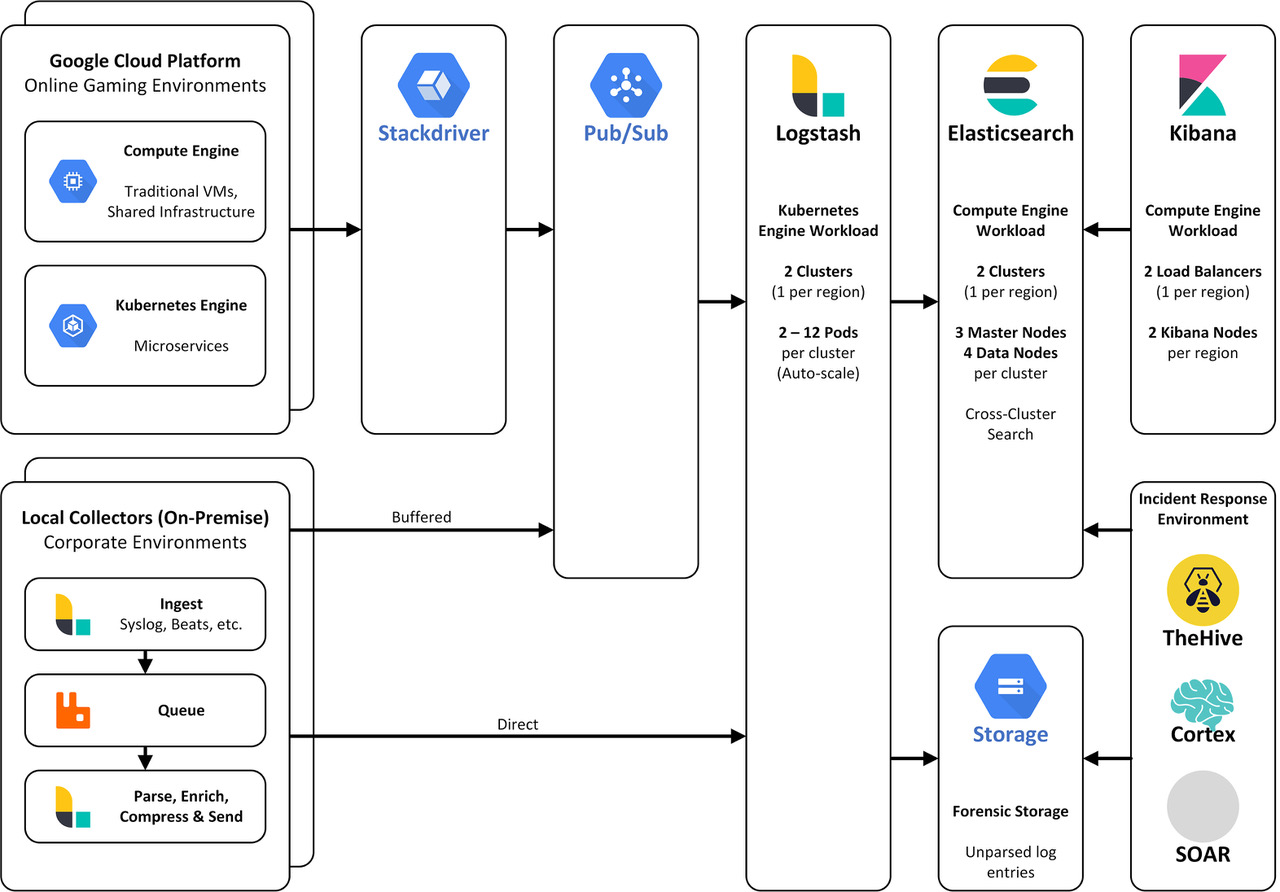
We have used Elastic for over a year now, helping to protect both our corporate and online gaming environments. With Elastic, I can add a new data source to be logged within hours or days. With our old solution this process took weeks, meaning our corporate and online gaming environments had visibility gaps that could not be plugged as fast as we can now fill them with Elastic.
This is a big deal. The more sources you log, the more visibility you have and the more secure you become. And with Elastic, we’re charged based on the resources we use, not on how much data we log. Our teams love the fact that we can log more for less with Elastic.
Our hybrid approach to Elastic SIEM
In the competitive videogame market, we develop our games discreetly, and must be confident that the only people testing our games are our developers, quality assurance staff and others that we’ve authorised. It would be difficult, if not impossible, to develop without this level of discretion to protect our intellectual property from thieves and leakers.
And when it comes to security analytics surrounding our corporate and online gaming environments, we’ve built a ton of Kibana dashboards visualising multiple data sources like firewalls, endpoint data using Beats, Cloud service data and so on.
For both our corporate and online gaming environments, we intend to start using Elastic SIEM, which debuted a year ago, as part of a hybrid approach to security analytics. Our security analysts will be able to continue using our bespoke Kibana dashboards that relate closely to our security logs. But we’ll also be adding new log sources and transitioning old log sources to the Elastic Common Schema in order to support greater use of Elastic SIEM. We plan on taking full advantage of Elastic SIEM features, such as the detection engine, and embracing new features as they’re added.
Preventing “gaming the system” with telemetry
If Elastic detects an unauthorised user or computer attempting to access one of our games in development, we’ll be investigating them and blocking them in their tracks. But there’s more to securing our games than just making sure that we develop them securely, or protecting our servers, endpoints and networks.
We’ll also be using security analytics powered by Elastic to combat cheating within our games.
We’re capturing telemetry data coming from the games themselves. So if somebody is on Level 1 of a game, and then seconds later they’ve upleveled a dozen times, something that’s impossible within the confines of the game dynamics, we know something is awry. That is not normal game play, and we’ll respond accordingly.
So thanks to Elastic, it’s game over for both cheaters and leakers.
Ben Trethowan — Information Security Manager at Square Enix