Designing an observability solution for public cloud and on-prem implementation

In my previous article, I talked about the importance of how a unified observability approach can augment the security posture of an organization.
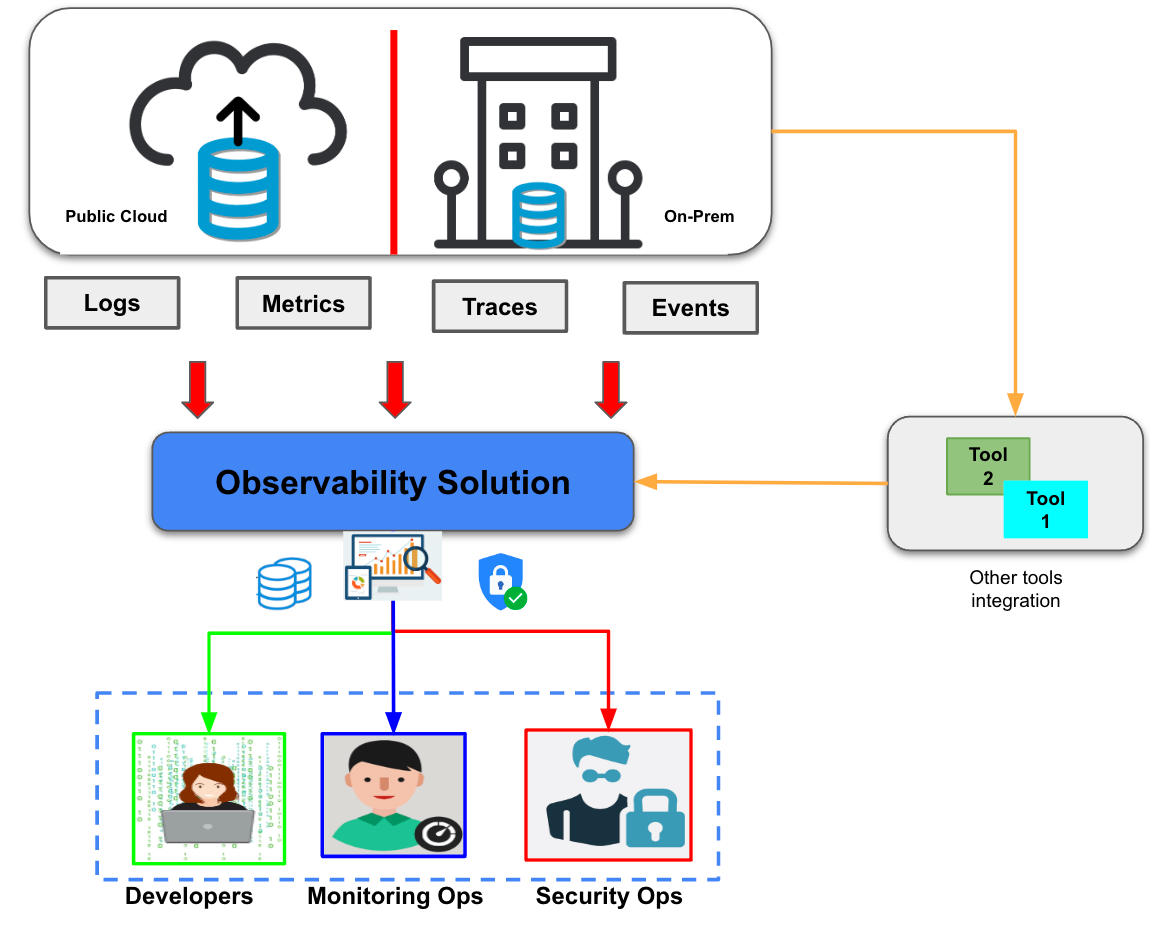
In this article, I’ll discuss the different components architects should consider when designing an observability solution for public cloud and on-premise implementations.
Having a sound observability solution on both cloud and on-prem is essential. This is especially true due to the rise of microservices architecture adoption, which makes visibility, traceability, and correlation of different components a necessity to be at the forefront of what is happening in your environment via almost real-time insights.
These recommendations are based on many considerations and a number of factors to ensure that the solution provides effective monitoring, troubleshooting, and analysis capabilities.
Data types
First and foremost, consider the types of data that you need to collect to get a complete picture of the system.
- Metrics — help you track the performance over time
- Logs and events — provide detailed information about systems events
- Traces — provide you with end-to-end visibility into requests
You’ll also want to think about including other advanced data types, like:
- Synthetic testing — provides data via simulated traffic to test the performance and behavior of an application
- Systems profiling — provides information about systems or applications performance based on the collected data across a certain period of time
- User experience/feedback — data collected by analytics tools to provide insights into user behavior, preferences, and issues
Data collection methodology
The next step is to determine how the data will be collected from different sources. There are multiple potential sources to consider, such as APIs or other methods. The collection process should be efficient and scalable to avoid data loss by overwhelming the system.
Storage and retention strategy
Another consideration is deciding on your storage and retention strategy. You need to decide where to store the collected data and for how long. Depending on the organization requirements, data can be stored in a centralized repository or distributed across multiple locations. It is essential to define retention policies that optimize cost, compliance, and query-ability. Storage considerations are critical when designing an observability solution. Here are some things to keep in mind:
- Data retention: The observability solution should store enough data to provide a historical perspective on system performance, security, and health. However, long-term storage can be costly, so it's important to determine the appropriate retention period based on business and compliance requirements.
- Storage location: The storage location should be determined based on data access requirements, security, and cost. Depending on the data sensitivity level, data can be stored on-premises or in the public cloud, while considering data sovereignty and compliance with regulations.
- Scalability: The observability solution should be designed to scale and handle large volumes of data as system complexity and traffic grow. This includes horizontal scaling through sharding and vertical scaling by adding resources.
Alert generation and notification
Alerting is another important consideration to think about. You need to have a strategy for establishing criteria for alert generation and notification. Alerts can be triggered based on predefined thresholds, anomalies, or changes in system behavior. Effective alerting is essential to provide fast responses to issues and reduce mean time to resolution (MTTR).
Data security
Consider security measures to protect the data being collected and stored. This includes encrypting data in transit and at rest, implementing access controls, and monitoring for suspicious activity. Things to consider in the design are:
- Access controls: Access controls should be implemented to ensure that only authorized users can access the observability data.
- Encryption: All data should be encrypted in transit and at rest to prevent unauthorized access to the observability data. This includes transport encryption via TLS/SSL and data-at-rest encryption using encryption mechanisms like AES-256.
- Network security: Measures to ensure network security should be considered to prevent unauthorized access to the observability solution using firewall, intrusion detection and prevention mechanisms, and other network security controls.
- Compliance: The solution should be designed to meet regulatory requirements such as GDPR, HIPAA, and PCI-DSS.
Data visualization
The next thing to determine is how the data will be presented to users. Visualization tools can help users to understand trends, identify patterns, and troubleshoot issues more effectively.
Integration
The ability to integrate with other tools and systems is an important design consideration. The solution should be able to integrate with the existing incident management, collaboration, and automation tools. This will help streamline workflows and enhance overall system efficiency.
Scalability and performance
Finally, think about the scalability and performance of your observability solution. You need to ensure that it can scale to handle growth in data volume, complexity, and workload. This includes optimizing resource allocation, network bandwidth, and data processing capabilities.
Your next challenge
Observability design should meet the needs of your public cloud and on-premise implementation so that you can ensure the proper visibility, traceability, and overall health of both your systems and applications deployed anywhere in your environment.
But most importantly, having a properly implemented observability solution should enhance your security implementation both on public cloud and on-premise implementation while maintaining the confidentiality, integrity, and availability of your organization's most important services and applications.
Learn why observability is key to solving business and operational challenges.