Elastic and AWS deliver on AI-driven security analytics
Amazon Bedrock and Elastic’s Attack Discovery automate security analyst workflows
.jpeg)
As cyber threats grow increasingly sophisticated, the need for highly effective security measures becomes imperative. Traditional SIEMs aren’t equipped to address threats fast enough because they rely on too many manual and labor-intensive tasks. AI-driven security analytics from Elastic’s Search AI platform solves these challenges.
The introduction of Elastic’s Attack Discovery, which includes AI-driven security analytics, empowers security teams to tackle these challenges faster and more accurately than ever before. By leveraging large language models (LLMs) and retrieval augmented generation (RAG), the Attack Discovery feature helps analysts cut through alert noise to pinpoint attack patterns efficiently — distilling a flood of alerts into a handful of actionable discoveries. Attack Discovery can be connected with Amazon Bedrock, making it much easier to connect to and utilize the latest LLMs.
"We continue to partner with Elastic on their AI and security initiatives,” said Ayan Ray, Senior Partner Solutions Architect, Data and Analytics at AWS. “Attack Discovery is an exciting addition to their existing generative AI capabilities, and we know that Amazon Bedrock users will be able to leverage this feature to help improve security analyst workflows."
Elastic Attack Discovery and Amazon Bedrock
This powerful combination equips security analysts with advanced tools to enhance their team’s defensive posture within minutes. Let’s explore how these technologies work together to fortify your security operations.
Simplifying threat detection with Attack Discovery
Attack Discovery is engineered to deconstruct the complex web of cyber threats using generative AI, leveraging LLMs to identify and understand sophisticated attack patterns. This is essential for swift and precise threat responses, ensuring your team can effectively mitigate risks.
By automating the correlation and documentation of attack sequences, Attack Discovery significantly cuts time spent on manual detection. It provides a comprehensive view of the attack chain, from inception to potential breaches, via an interactive interface that offers a detailed summary of threats complete with actionable insights. This facilitates improved internal communication and efficient response strategies.
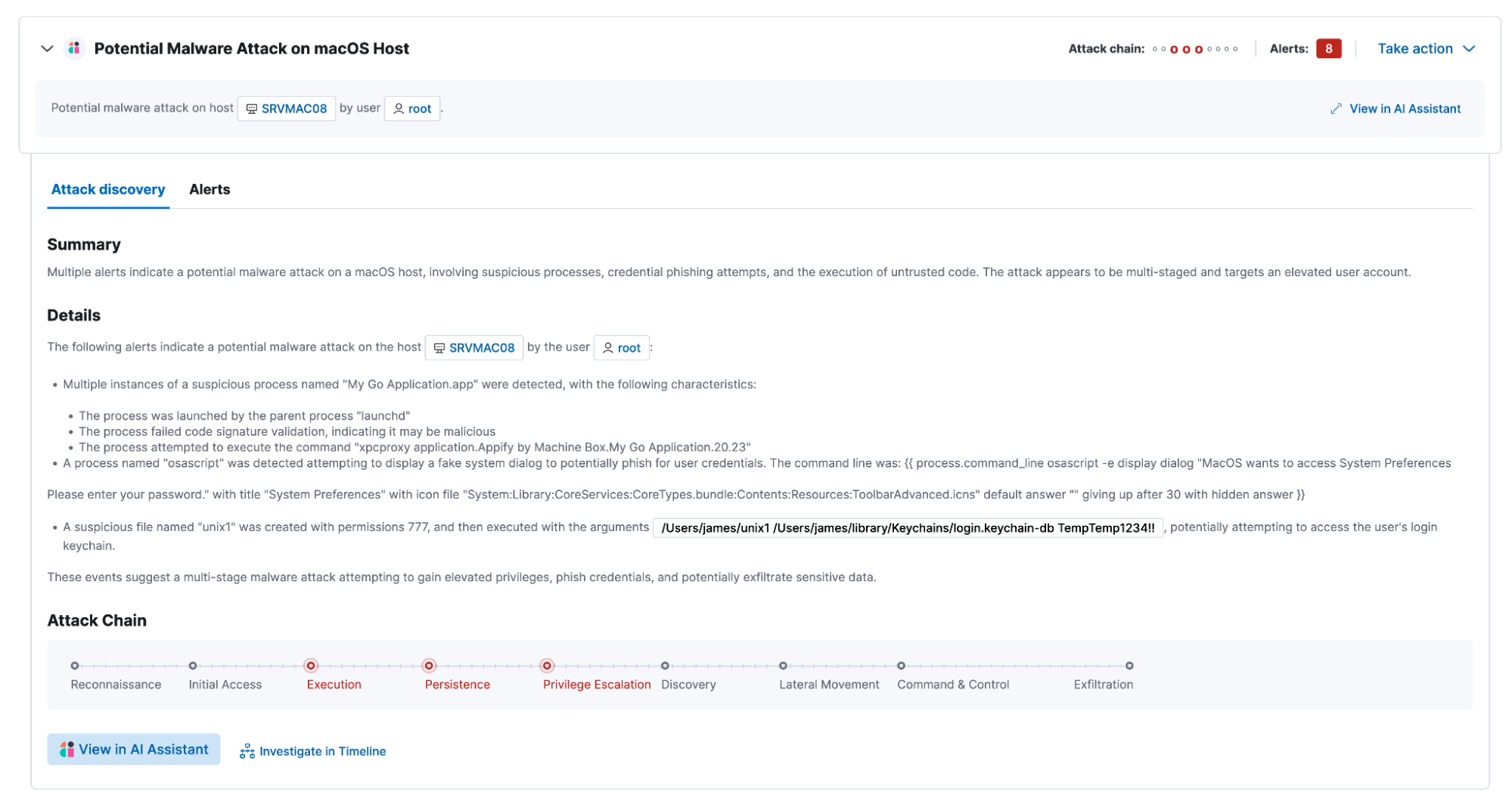
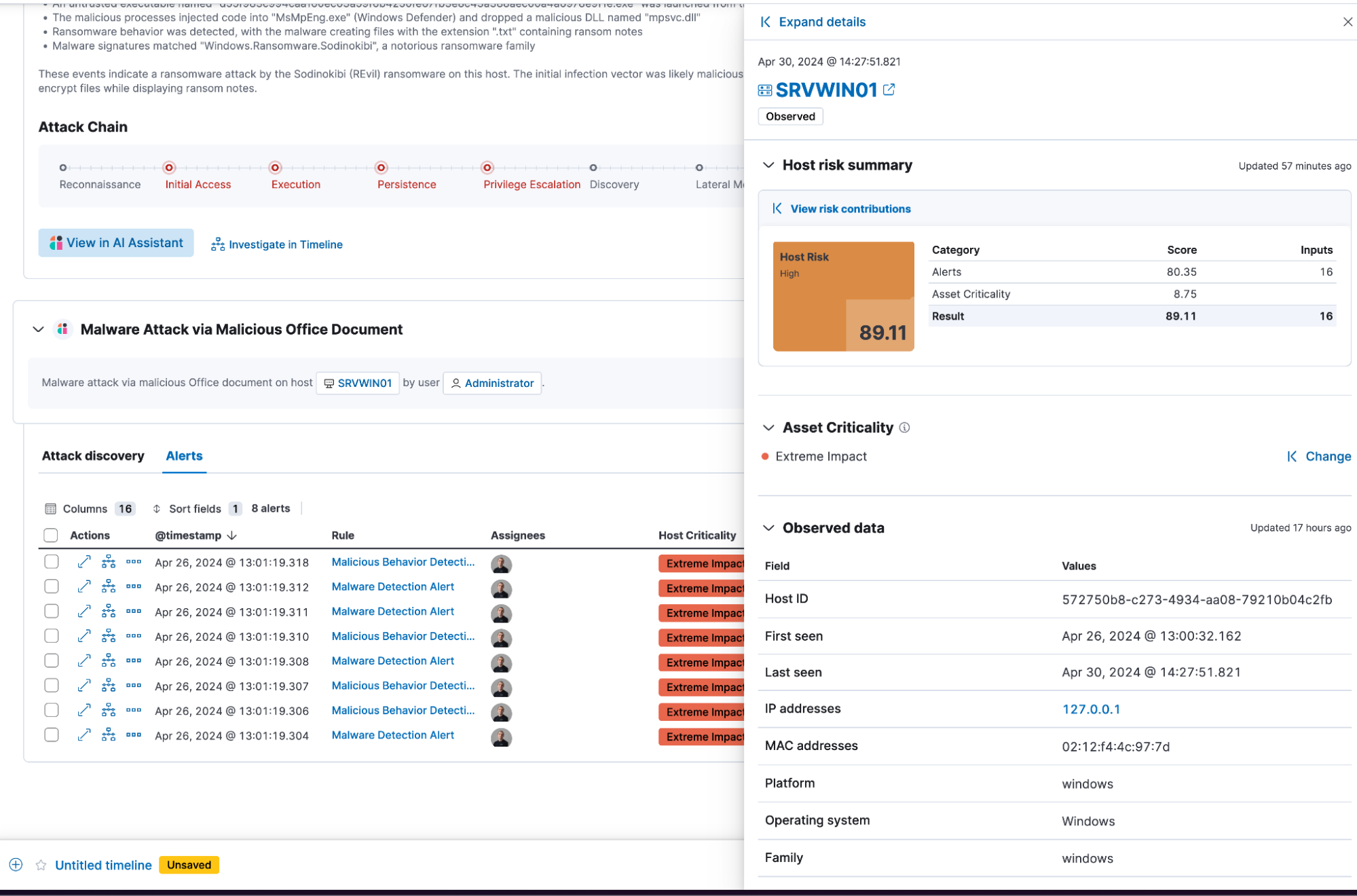
Empowering security teams
The integration of Attack Discovery within your security operations will change the focus of a security analyst to become more proactive. Rather than spending hours manually reviewing and linking related alerts, Attack Discovery uses generative AI to identify and connect components of the attack chain. This connection follows the attack from beginning to end — from initial breaches, such as phishing emails or malware downloads, to activity within the network, like lateral movement and privilege escalations — and provides deep insights into the nature of each threat. The integration within the AI-driven security analytics solution allows analysts to ask follow-up questions and get deeper insights and remediation steps within the context of the current threat. The comprehensive view provided helps analysts grasp the entire scope of an attack, enhancing strategic defenses.
Fostering collaboration and insight
Attack Discovery delivers an attack summary and interactive visualizations, both explaining the nature of the attack detected and the different tactics employed. This holistic view helps teams understand and discuss the progression of threats in real time, enhancing collaborative decision-making. The discoveries from Attack Discovery are ready to be shared in reports across departments, ensuring that all stakeholders are informed and aligned, which is critical for improving the security posture of the organization.
Integration with Amazon Bedrock
In continued partnership with AWS, Elastic extends the capabilities of Attack Discovery via Amazon Bedrock, connecting seamlessly with the Anthropic Claude 3 family of models: Haiku, Sonnet, and Opus. Amazon Bedrock’s developer-friendly platform allows for easy experimentation with a diverse array of foundational models (FMs), providing a unified API that supports rapid adaptation and minimal coding. Additionally, Elastic Security Labs recently debuted new detection rules for Amazon Bedrock.
This technology partnership between Elastic's Attack Discovery and Amazon Bedrock empowers organizations to harness the power of AI, revolutionizing their security frameworks to be more agile and resilient against evolving cyber threats.
The release and timing of any features or functionality described in this post remain at Elastic's sole discretion. Any features or functionality not currently available may not be delivered on time or at all.
In this blog post, we may have used or referred to third party generative AI tools, which are owned and operated by their respective owners. Elastic does not have any control over the third party tools and we have no responsibility or liability for their content, operation or use, nor for any loss or damage that may arise from your use of such tools. Please exercise caution when using AI tools with personal, sensitive or confidential information. Any data you submit may be used for AI training or other purposes. There is no guarantee that information you provide will be kept secure or confidential. You should familiarize yourself with the privacy practices and terms of use of any generative AI tools prior to use.
Elastic, Elasticsearch, ESRE, Elasticsearch Relevance Engine and associated marks are trademarks, logos or registered trademarks of Elasticsearch N.V. in the United States and other countries. All other company and product names are trademarks, logos or registered trademarks of their respective owners.