What’s next: Black Hat 2023 takeaways
.png)
AI-driven guidance
Generative AI was a major topic of discussion throughout Black Hat. The event’s opening keynote highlighted the “potential benefits and risks associated with the democratization” of AI and announced DARPA’s AI Cyber Challenge, a two-year competition to develop AI-powered security tools. In discussion, vendors highlighted how AI, generative AI, and large language models would soon change the everyday work of security practitioners, and attendees dug into how close vendors were to making these visions reality.
Visitors to the Elastic booth experienced a glimpse of the AI future in the product of today. We recently introduced Elastic AI Assistant, our pioneering generative AI sidekick, heralding its promise to “democratize cybersecurity and enable users of every skill level.” The swift advancement of generative AI — and Elastic’s open roots and rapid innovation — have propelled this capability forward. The tool breaks new ground, according to a recent report by IDC, and customers have provided substantial positive feedback.
Elastic AI Assistant accelerates triage and investigation workflows by summarizing alerts and helping analysts consider which steps to take next. It also provides step-by-step guides for accomplishing tasks within Elastic and eases migration from legacy data platforms by streamlining the conversion of existing data pipes and queries. Elastic AI Assistant harnesses AI with Elastic’s text search and is made possible by an open integration framework that today connects Open AI and Microsoft Azure OpenAI.
Advanced entity analytics
The threat landscape remains remarkably dynamic, per ongoing research from Elastic Security Labs. Recent industry reports reveal that traditional ransomware has declined in popularity, while identity-based attacks and data extortion (particularly via the MOVEit exploit) have surged. Several Black Hat sessions and vendor announcements addressed how organizations are applying behavioral analytics to fight back.
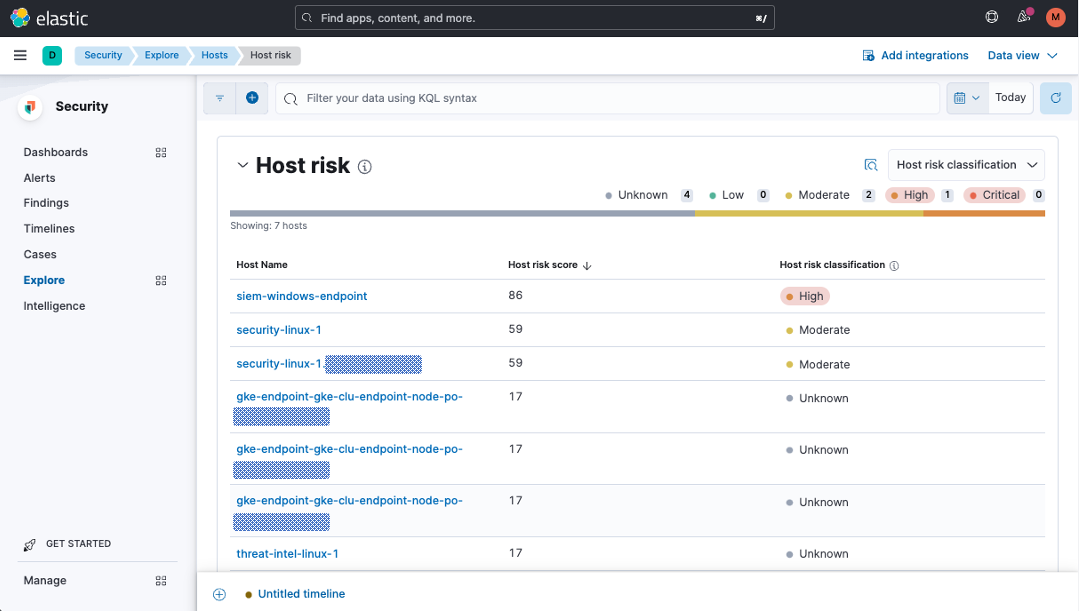
The top attack vector for data breaches continues to be insider threats originating from stolen or misused credentials for employees, contractors, or vendors. As such, we’re focused on advanced entity analytics, including generative AI, entity-centric risk scoring, and spotting anomalies with machine learning.
Researchers and engineers from Elastic Security Labs participated at Black Hat and DEFCON and shared new analytics content — including an update to our advanced analytics package for lateral movement. Detecting malicious lateral movement with traditional detection rules can be difficult because attackers use sophisticated methods and tools to move under the security radar. With the addition of prebuilt ML jobs that detect malicious activity from Windows RDP events, these analytics are now generally available. Dig in at our open detection rules repo.
Years of data, ready when you need it
Thwarting long-lurking threats — including APTs like those that cracked log4j and SolarWinds — requires months or years of data. As such, the SOC must be able to collect a large amount of data, retain it for a long period of time, and search it quickly. Unfortunately, the volume of Black Hat presentations discussing how to overcome the data management shortcomings of most analytics platforms suggests that SOCs may be inured to these limitations.
Elastic makes compromising your access to data unnecessary, rendering data lakes obsolete. It optimizes speed, scalability, and cost efficiency by indexing data only once (when it’s ingested) rather than every time it’s read. Customers can store and analyze data on commodity object stores like Amazon S3, Google Cloud Storage, and Azure Cloud Storage, or on-prem options like MinIO. Historical snapshots are searchable at unprecedented speed, without rehydrating the entire data set. Using cross-cluster search, our federated search capability, analysts can simultaneously search multiple deployments, even across multiple hyperscale clouds and on-prem systems. The result? Years of data, searchable in seconds, within your existing budget.
Open for integration
The global security community is embracing open data standards because normalizing data makes it easier to query, correlate, visualize, and harness for machine learning. In the lead-up to Black Hat, two major data schema projects shared meaningful progress. Building on our contribution of Elastic Common Schema (ECS) to OpenTelemetry (OTel), new vendors are joining forces, supporting the convergence of security and observability data within the Cloud Native Computing Foundation (CNCF). Likewise, the Open Cybersecurity Schema Framework (OCSF), a complimentary taxonomy, announced general availability.
Beyond streamlining analysis of diverse data, open data standards reduce the grip of certain outsized vendors pushing to lock customers into closed tool portfolios. Proprietary approaches benefit dinosaurs, but nobody else: not the builders of modern solutions, and certainly not the SOC teams stuck with hamstrung technologies. Open security, for the win.
Looking ahead
Elastic Security community members have a lot of company — but the conversations at Black Hat 2023 showed that we’re still ahead of the curve. With generative AI, advanced entity analytics, years of context from across your enterprise, and an open approach, the solution equips security teams to modernize SecOps.
Want to learn more? View our webinar about harnessing AI with Elastic Security.