Limitless XDR defined: Ingest, retain, and analyze security data freely
Elastic Security's newest features define the potential of XDR for cybersecurity teams. Our single platform brings together SIEM and endpoint security, allowing users to ingest and retain large volumes of data from diverse sources, store and search data for longer, and augment threat hunting with detections and machine learning.
Security vendors are using the term “XDR” with increasing frequency, applying varied definitions to suit their respective technologies. The term began as an evolution of EDR (endpoint detection and response), and tried to encapsulate the need for varied data sources in the investigative process by using “X” for “eXtended.” Through all the varying definitions, the core concepts remain:
- Visibility: The exponential growth of data makes a security practitioner’s job increasingly difficult. They need a central place to conduct analysis, root-cause identification, and remediation planning.
- Analytics: This central collection of data cannot be a data swamp. It must give users a flexible framework to compose, enable, and monitor new analytics use cases at scale. It should also seamlessly integrate with analyst workflows to prioritize and build the attack narrative.
- Response: This central solution must be responsive. Users need a way to remediate attacks — preventing them before they even start is all the better. Ransomware “detection” does not help an organization. Native endpoint security allows for reducing mean time to remediate (MTTR) to zero.
Ultimately, at Elastic we define XDR in this way:
XDR modernizes security operations, enabling analytics across all data and automating key processes to bring prevention and remediation capabilities to every host.
Many users of Elastic see the term XDR and think “I am doing this already in my security program.” In fact, the concept of collecting multiple data sources, analyzing them at scale, detecting threats in the information, building a response plan, and then conducting remediation can be viewed as the doctrine of a SOC (security operations center). What XDR is promising to do is encapsulate much of this work into a unified solution and provide help where possible to accelerate the analyst workflow of triage, investigation, escalation, and response — ultimately bringing this capability to more users. Adversaries target anyone, not just those with SOCs, and XDR promises to help not just enterprise organizations, but also those that have not yet built out robust security programs to battle against these unrelenting attacks.
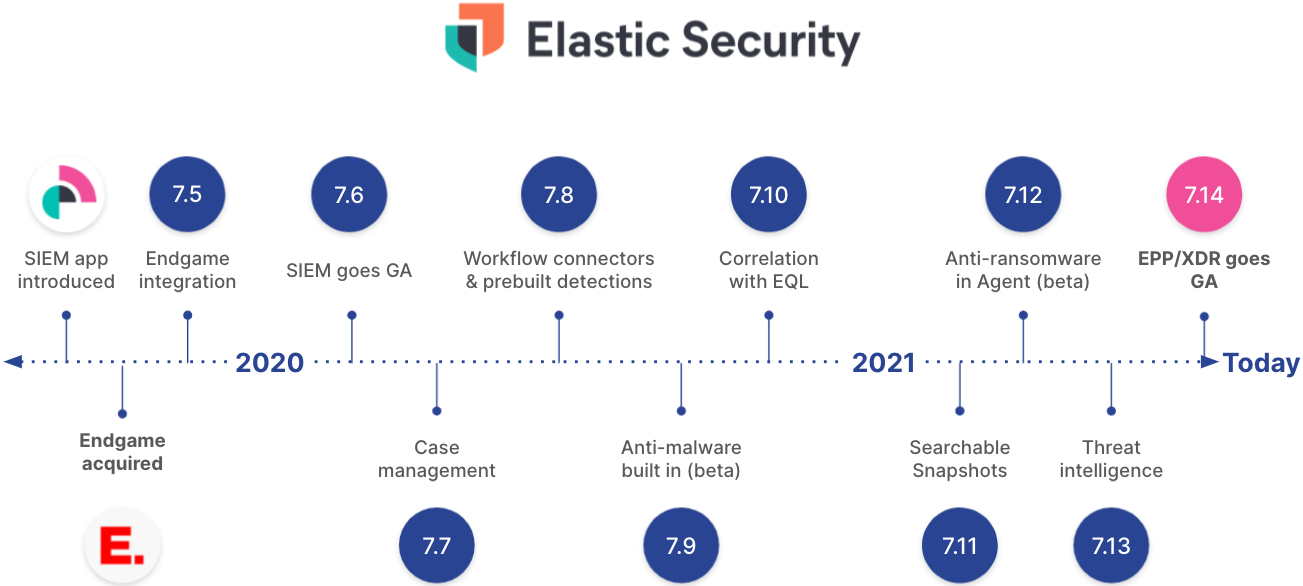
When Elastic joined forces with Endgame, an EPP vendor, Shay shared our vision of unifying SIEM and endpoint security for every user. This democratization of security allows anyone — not just large enterprises — to prevent, detect, and respond to advanced threats. Since then, our journey has led us to this moment where we have launched our generally available endpoint security capabilities in the same user experience as our security analytic/SIEM capabilities. This merging of SIEM and endpoint security solutions is XDR.
What makes Elastic unique in the emerging market of XDR is that our solution is limitless.
X is for eXtended
Limitless visibility
XDR solutions that evolved from endpoint security products are generally unable to scale to ingest and retain the volume and diversity of data sources in your enterprise. Elastic is years ahead of other solutions in solving the data problem, utilizing our free and open architecture to ingest any data source. We map the data of hundreds of prebuilt integrations to the Elastic Common Schema (ECS), and our user community continually adds new extensions continually. Plus, Logstash enables custom data collection of any kind. Elastic Agent is a single installer that supports hundreds of integrations, offering new use cases in one click.
Limitless data
Attacker dwell times far exceed the current retention of most SIEM and XDR systems. And even if those systems retain the data, they typically slow analysis to a crawl. Elastic can take action on frozen data in object storage, such as Amazon S3, for years of search, threat intelligence, dashboards, reports, and more. Simply change the time range from 2 weeks to 2 years, and in minutes the results are at your analysts’ fingertips.
D is for Detection
Limitless analysis
Threats evolve constantly. Detecting and stopping them requires defense in depth. At Elastic, numerous detection layers are available across all your data — from correlation across any number of data sources to threat intelligence applied to years of information and machine learning models detecting anomalies. Our team delivers hundreds of MITRE ATT&CK®-mapped detections and machine learning jobs to ensure you are achieving value on day one.
We’ve opened up our development of our detections, allowing you to connect directly to the team and share the wisdom of the Elastic community. Our hierarchical detection engine architecture allows new detection rules to analyze previous detections, looking for advanced attack progressions. Many organizations collect data in different geographic areas, cloud providers, and regions. Backhauling information is costly and inefficient. Using Cross Cluster Search, Elastic can bring your search to the data, empowering all these analytics in your multi-cloud environment without the need to transfer data across regions or providers
R is for Response
Finally, issues that are detected will need to be promptly addressed. Modern remediation requires an ability to take action across the Enterprise — not only by killing a process, but also disabling a user, removing an email from the server, or blocking a bad domain at the firewall. Analysts need a simple, intuitive way to collaborate on an investigation, build a remediation plan, launch it, and report on its success.
Elastic includes free and open case management — users leverage the cases feature to communicate and collaborate with their team. Cases have expanded to seamlessly integrate with key remediation vendors like ServiceNow ITSM, ServiceNow SecOps, IBM Resilient, JIRA, and Swimlane, fitting into the existing remediation workflow of businesses of any scale. In addition, our API-first development and webhooks capability allows for integration into any other productivity tool.
And of course, Elastic Agent provides a centralized way to coordinate data collection and policy enforcement like automatically quarantining malicious files and stopping ransomware. During remediation, Osquery management on every OS (Windows, macOS, and Linux) allows our users to gather any additional information required in the incident process. And when an attack is identified, a simple one-click host isolation capability on Windows and macOS will stop the adversary from stealing or destroying data while you build the response plan. This response is below the user-mode firewall, implementing the control at the kernel level to prevent adversary tampering.
A (the hidden letter) is for Automation
With all this additional visibility, XDR solutions must also help to automate the analyst process to ensure efficiency across disparate data sources. Many capabilities work to take the analyst workflow and apply it at scale:
- One-click data ingestion: Security teams are constantly being asked to monitor new sources of data from the business, such as cloud infrastructure, SaaS authentication providers, and point security products. Analysts need to spend their time finding value in the data, not building ingest pipelines. Elastic Agent provides a fast and easy way to ingest, normalize, and apply the data, including dashboards, models, rules, and more.
- Scaling detections across all data sources: Beyond the power of the types of detections, users need to ensure they are also being supplied with a constant supply of quality detections, kept up to date against tomorrow’s threats. The team at Elastic, working with the actively engaged and amazing community, keep this open detection rules repo up to date.
- Accelerating analyst decisions: With growing data sources and growing detections across those sources, analyst workload is bound to increase. First, your XDR solution needs to not only alert, but also tell you what alert (or collection of alerts) should be investigated first. Using the context of all the data sources, Elastic scores the risk of hosts in the environment to prioritize detections based on the highest risk to the business. Second, by enriching alerts with knowledge from previous detections, cases and threat intelligence, analysts can more easily determine if something needs to be escalated. Third, analysts need to be guided through the next steps to the fastest time to resolution. Elastic provides investigation guides for detections to help an analyst understand the most useful next steps.
XDR is free, open, and unmatched at Elastic
Limitless usage
Resource-based pricing allows you to take control with flexible licensing. Don’t let rigid licensing interfere with your mission. With Elastic, no matter your use case, data volume, or endpoint count, you’ll pay only for the server resources you use. The result is predictable pricing and the flexibility to adapt based on your needs.
Our mission at Elastic Security is to protect the world’s data from attack. We are constantly innovating in the protection space to ensure our users across the world are protected from tomorrow’s attacks. The solution delivers free and open capabilities of SIEM, Endpoint Security, and XDR on a single platform built for limitless analysis, enabling organizations to prevent, detect, and respond before damage is done.
If you’re new to Elastic Security, you can experience our latest version on Elasticsearch Service on Elastic Cloud for free.