Configure and install the Endpoint Security integration
editConfigure and install the Endpoint Security integration
editLike other Elastic integrations, Endpoint Security can be integrated into the Elastic Agent through Fleet. Upon configuration, the integration allows the Elastic Agent to monitor for events on your host and send data to the Elastic Security app.
To configure the Endpoint integration on the Elastic Agent, you must have permission to use Fleet in Kibana. You must also have admin permissions in Kibana to access the Endpoints page in the Elastic Security app.
Before you begin
editDepending on the macOS version you’re using, macOS may require you to grant full disk access to different kernels, system extensions, or files. See Enable Full Disk Access for more information.
Add the Endpoint Security integration
edit-
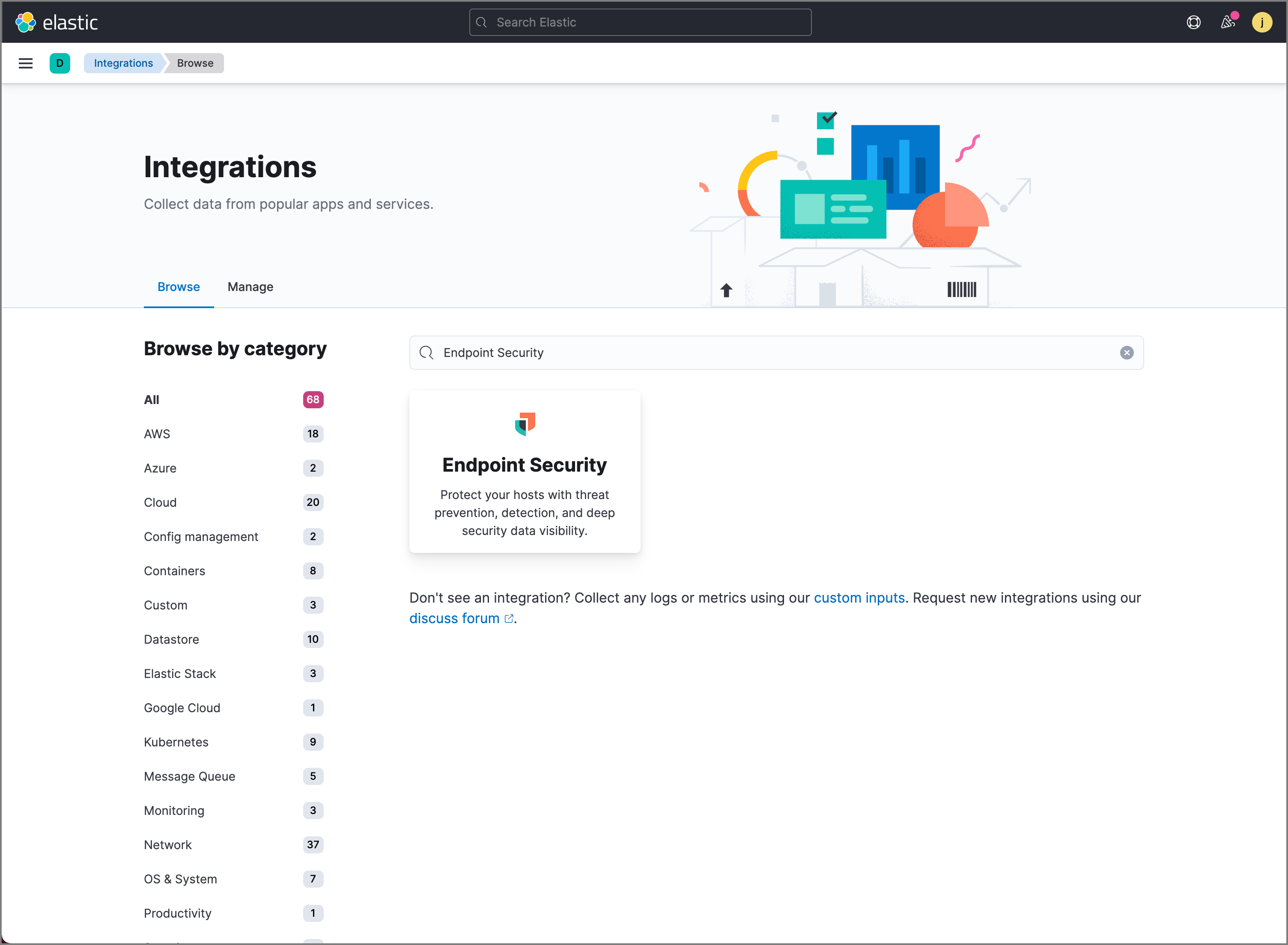
In Kibana, select Security → Endpoints. If this is not your first time using Elastic Security, select Management → Integrations and search for "Endpoint Security."
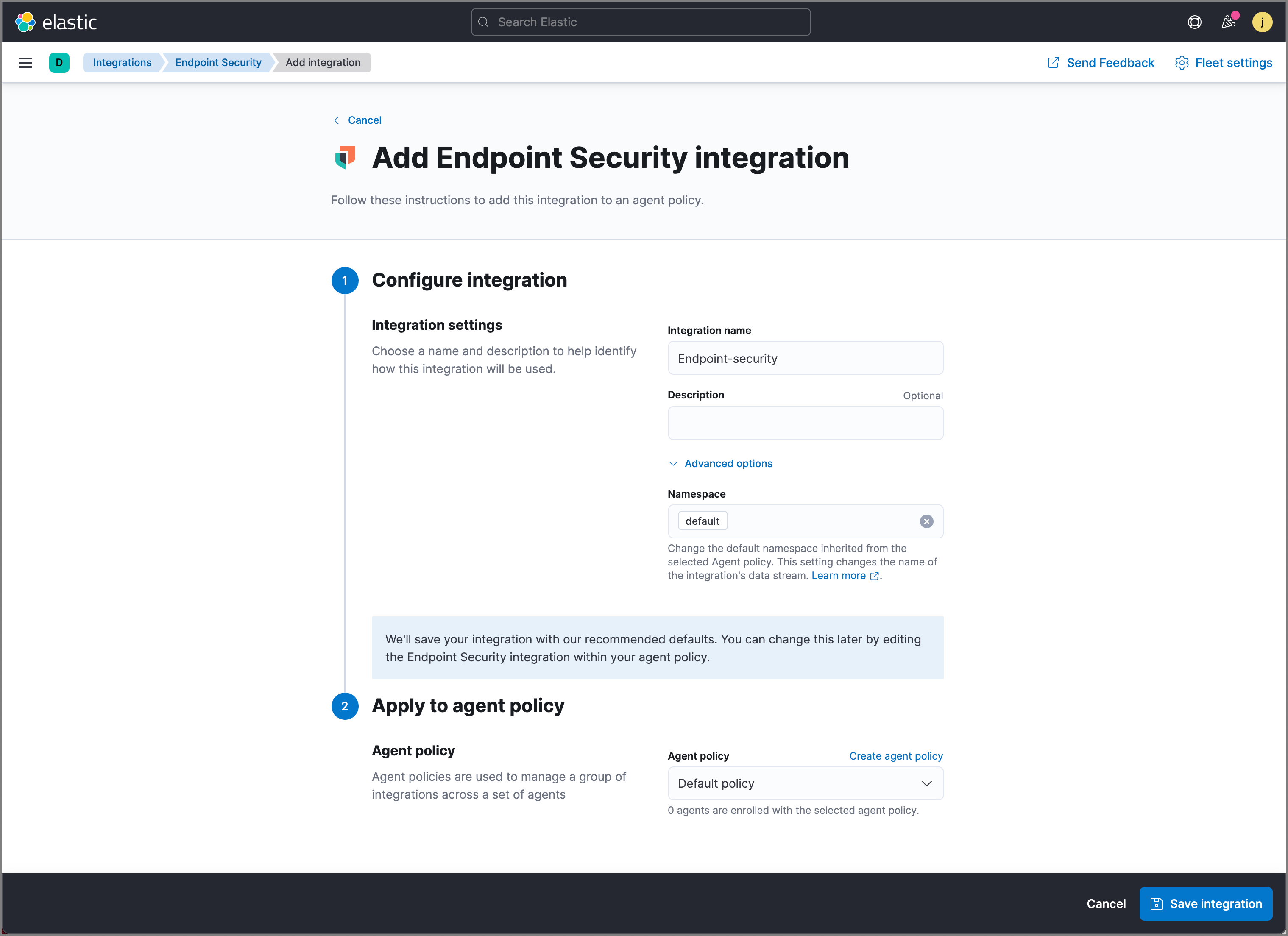
- On the Endpoints page of the Elastic Security app or the Endpoint Security integration page (Management → Integrations), select Add Endpoint Security. The integration configuration page appears.
- Select an agent policy for the Elastic Agent. You can select one of the two default policy options, an existing policy, or select Create agent policy to create a new one. For more details on Elastic Agent configuration settings, see Configuration settings.
-
Configure the Endpoint Security integration with a name and optional description. When the configuration is complete, click Save integration in the lower right corner.
Configure and enroll the Elastic Agent
editTo configure the Elastic Agent, Endpoint Security requires enrollment through Fleet to enable the integration.
Before you add an Elastic Agent, a Fleet Server must be running. See Add a Fleet Server.
Important information about the new Fleet Server
editIf you are running an Elastic Stack version earlier than 7.13.0, you can skip this section.
If you have upgraded to an Elastic Stack version that includes the new Fleet Server (>=7.13.0), you will need to redeploy your agents. Review the following scenarios to ensure you take the appropriate steps.
- If you redeploy the Elastic Agent to the same machine through the Fleet application after you upgrade, a new agent will appear.
- If you want to remove the Elastic Agent entirely without transitioning to the Fleet Server, then you will need to manually uninstall the agent on the machine. This will also uninstall the endpoint. See Uninstall Elastic Agent.
- In the rare event that the Elastic Agent fails to uninstall, you might need to manually uninstall the endpoint. See Uninstall an endpoint at the end of this topic.
Endpoint Security cannot be integrated with an Elastic Agent in Standalone mode.
-
Go to Fleet → Agents → Add agent.
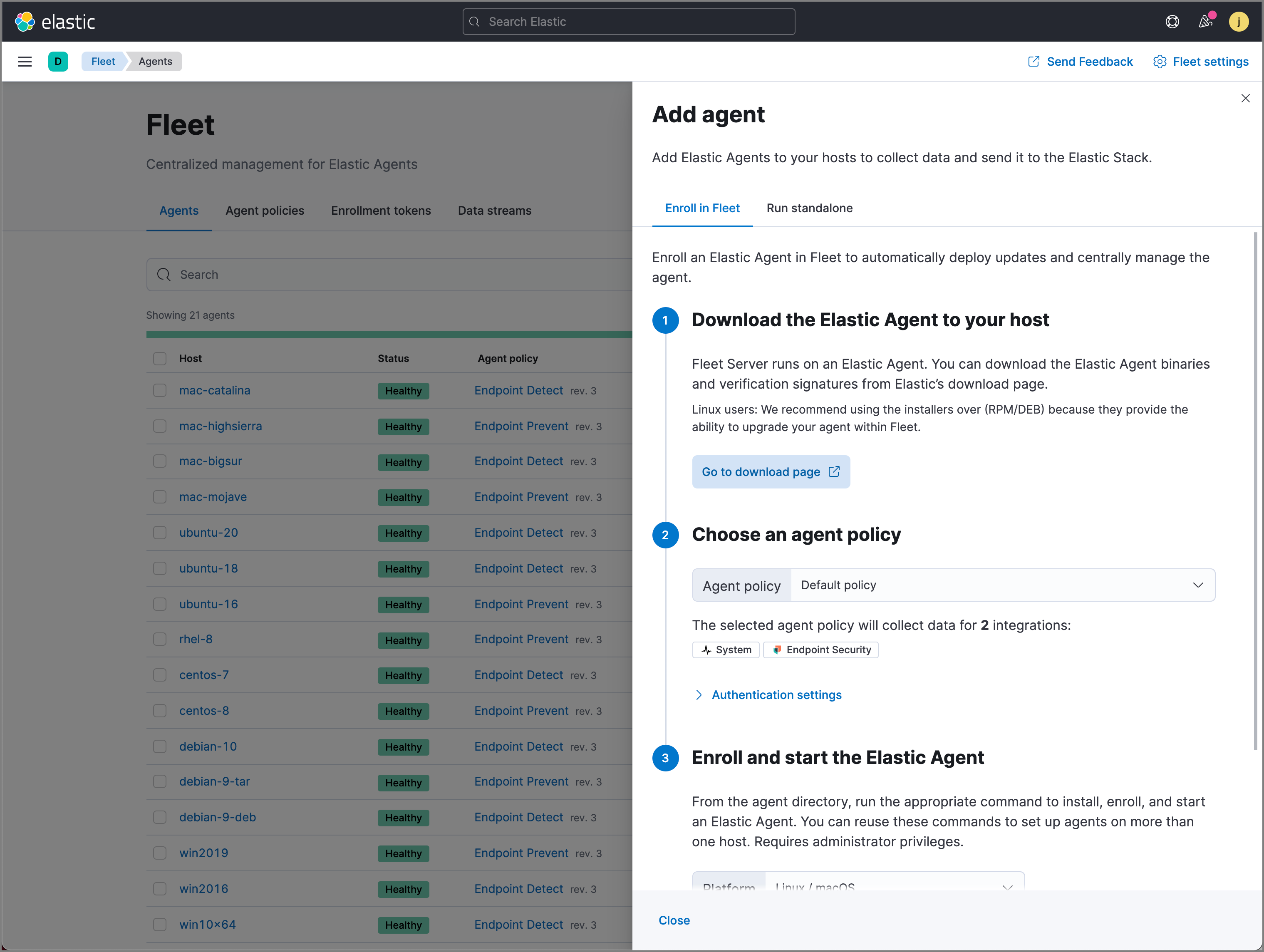
- In the Add agent pane, download the Elastic Agent on your host’s machine.
-
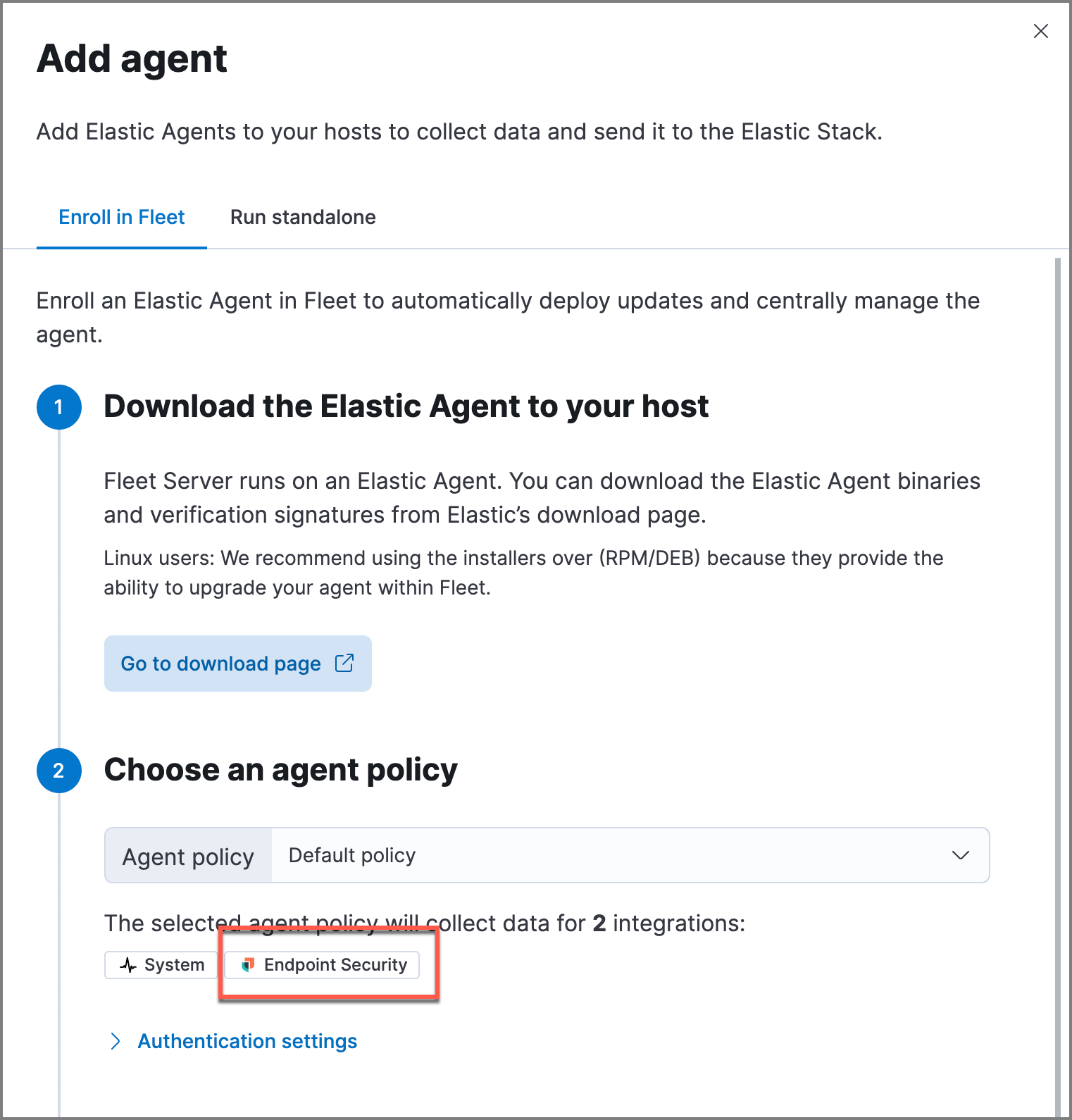
After the download is complete, select the Endpoint Security integration.
- After the Elastic Agent is installed on your host machine, open a command line interface and navigate to the directory where the agent is located. Copy the commands from Fleet for your OS to enroll and run the agent.
- After you have enrolled the Elastic Agent on your host, select Continue. The host now appears on the Endpoints page in the Elastic Security app.
Enable Elastic Endpoint kernel
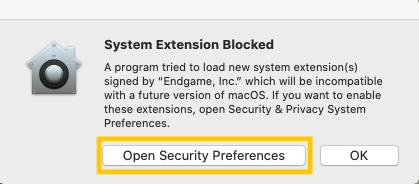
editIf you are running the Elastic Agent with the Elastic Endpoint integrated on macOS 10.13, 10.14 and 10.15, you will be prompted to approve a kernel extension from "Endgame, Inc". To approve the extension:
-
Select Open Security Preferences. The Security and Privacy pane opens.
-
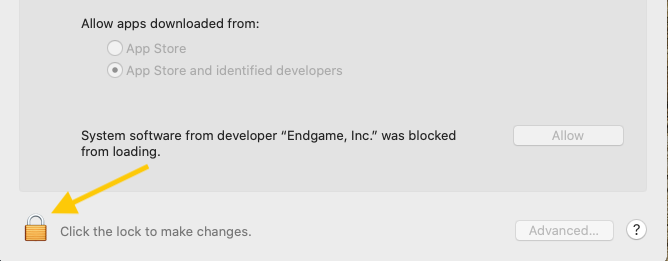
Select the Lock icon at the bottom left of the window to make changes to your security settings.
-
Allow "Endgame, Inc" by clicking the Allow button.
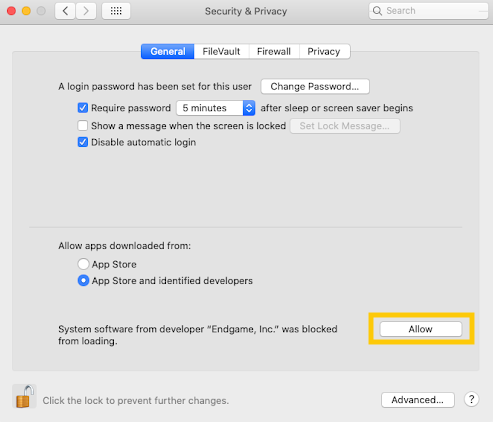
Endgame Sensor users can approve the kernel the same way for the Elastic Endgame app.
If the prompt does not appear because you’re using a version earlier than macOS Big Sur (11.0), enable the extension by doing the following:
- Open a Terminal application.
-
Enter
kextload /Library/Extension/kendpoint.kext. Prepend the command withsudoif necessary. -
To confirm the kernel extension has loaded, enter
kextstat | grep co.elastic.kendpoint. -
You should receive an output similar to
149 0 0xffffff7f82e7b000 0x21000 0x21000 co.elastic.kendpoint (7.11.0) BD152A57-ABD3-370A-BBE8-D15A0FCBD19A <6 5 2 1>. If you receive this output, the kernel extension is enabled.
Configure an Integration policy (optional)
editAfter the Elastic Agent is installed successfully, malware prevention and ransomware prevention (a Platinum+ license feature) are automatically enabled on protected hosts. If needed, you can update the Integration policy to configure malware protection, ransomware protection, event collection, and antivirus settings to meet your company’s security needs.
To access the Integration policy:
- In the Elastic Security app, go to Manage → Endpoints to view the Endpoints list. Remember that you must have admin permissions in Kibana to access this page.
- From the Integration Policy column, select the policy you want to configure. The Integration policy Configuration page appears.
- Review the policy settings below and configure as appropriate.
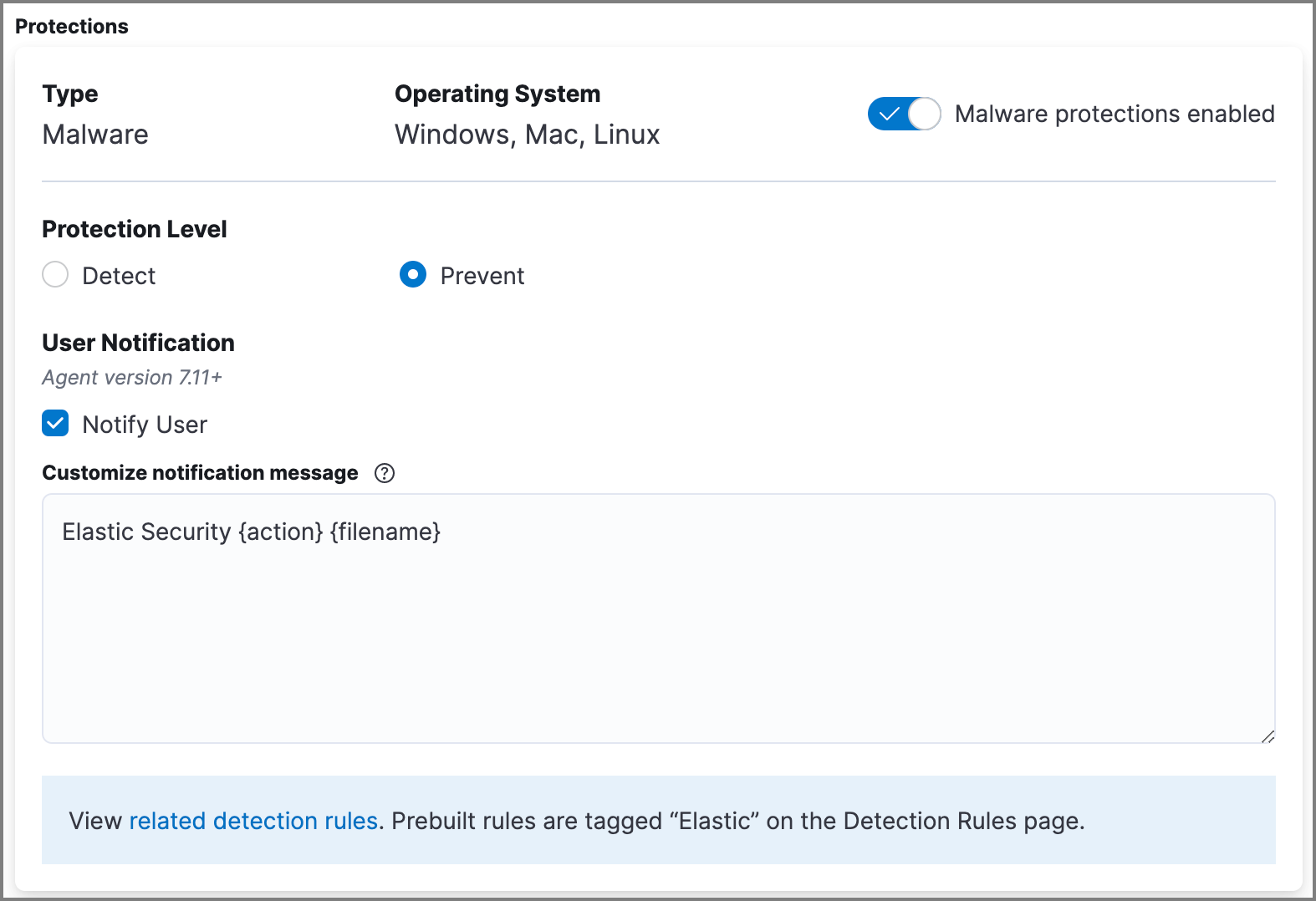
Malware protection
editMalware prevention on the Elastic Agent detects and stops malicious attacks by using a machine learning model that looks for static attributes to determine if a file is malicious or benign.
By default, malware protection is enabled on Windows, macOS, and Linux hosts. To disable malware protection, switch the Malware protections enabled toggle off. Malware protection levels are as follows:
- Detect: Detects malware on the host and generates an alert. The agent will not block malware. You must pay attention to and analyze any malware alerts that are generated. Notifications do not appear by default. Select the Notify User option to enable them.
-
Prevent (Default): Detects malware on the host, blocks it from executing, and generates an alert. Notifications appear by default. Deselect the Notify User option to disable them.
Platinum and Enterprise customers can customize these notifications using the
Elastic Security {action} {filename}syntax.
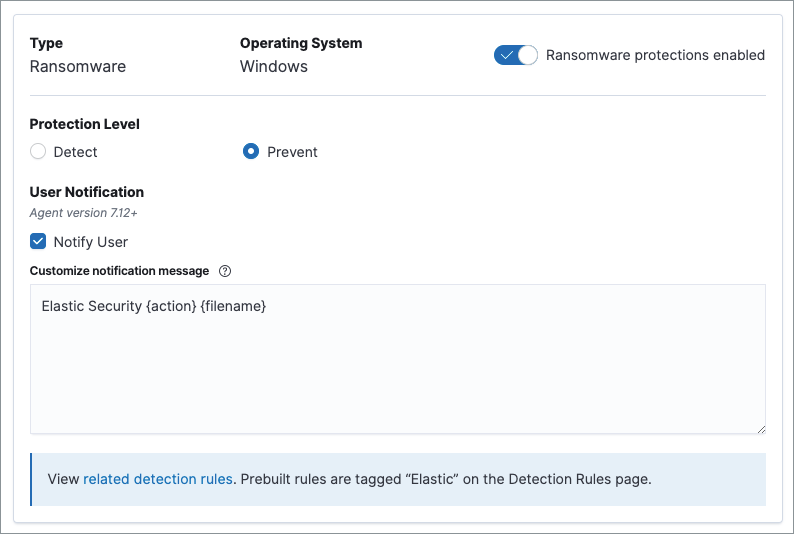
Ransomware protection
editBehavioral ransomware prevention detects and stops ransomware attacks on Windows systems by analyzing data from low-level system processes. It is effective across an array of widespread ransomware families — including those targeting the system’s master boot record.
Ransomware protection is a paid feature and is enabled by default if you have a Platinum or Enterprise license. If you upgrade to a Platinum+ license from Basic or Gold, ransomware protection will be disabled by default.
Ransomware protection levels are as follows:
- Detect: Detects ransomware on the host and generates an alert. The Elastic Agent will not block malware. Select the Notify User option to enable user notifications.
-
Prevent (Default): Detects ransomware on the host, blocks it from executing, and generates an alert. User notifications are enabled by default. Deselect the Notify User option to disable them.
Platinum and Enterprise customers can customize these notifications using the
Elastic Security {action} {filename}syntax.
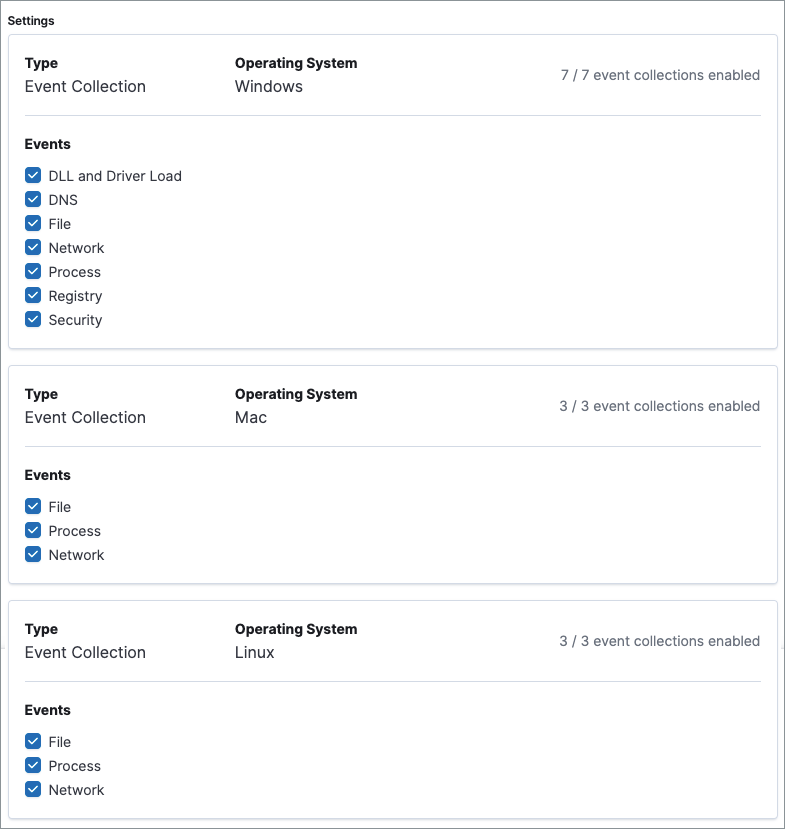
Event collection
editIn the Settings section, review the events that collect data on each operating system. By default, all event data is collected. If you no longer want a specific event to collect data, deselect it.
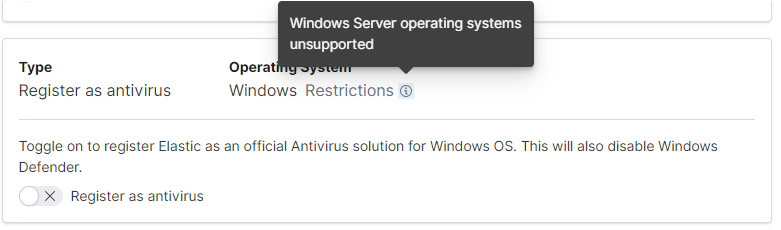
Register Elastic Security as antivirus (optional)
editIf you download the Elastic Agent version 7.10 or later on Windows 7 or above, you can configure Elastic Security as your antivirus software switching the Register as antivirus toggle on.
Advanced policy settings (optional)
editUsers with unique configuration and security requirements can select Show Advanced Settings to configure the policy to support advanced use cases. Hover over each setting to view its description.
Advanced settings are not recommended for most users.
Save the integration
edit- After you have configured the policy, click Save.
- On the dialog that appears, click Save and Deploy changes. If successful, a "Success" confirmation appears in the lower right corner.
Uninstall an endpoint
editUse these commands to uninstall an endpoint ONLY if uninstalling an Elastic Agent is unsuccessful.
Windows
cd %TEMP% copy "c:\Program Files\Elastic\Endpoint\elastic-endpoint.exe" elastic-endpoint.exe .\elastic-endpoint.exe uninstall del .\elastic-endpoint.exe
macOS
cd /tmp cp /Library/Elastic/Endpoint/elastic-endpoint elastic-endpoint sudo ./elastic-endpoint uninstall rm elastic-endpoint
Linux
cd /tmp cp /opt/Elastic/Endpoint/elastic-endpoint elastic-endpoint sudo ./elastic-endpoint uninstall rm elastic-endpoint