Auditbeat
Lightweight shipper for audit data
Collect your Linux audit framework data and monitor the integrity of your files. Auditbeat ships these events in real time to the rest of the Elastic Stack for further analysis.
Keep an eye on your Linux systems
Monitor user activity and processes, and analyze your event data in the Elastic Stack without touching auditd. Auditbeat communicates directly with the Linux audit framework, collects the same data as auditd, and sends the events to the Elastic Stack in real time. If you’re feeling nostalgic, you can run auditd alongside Auditbeat (in newer kernels).
Don’t rewrite what works. Use your existing audit rules to ingest data painlessly. Who was the actor? What action did they perform and when? Auditbeat retains all of the original syscall data and the associated paths so you have the context you need.
Get the right message(s)
Avoid getting caught in the cross-hairs of split messages, duplicate events, and meaningless ID numbers. Unlike auditd, Auditbeat groups related messages into a single event. It also handles the parsing and normalizing of the messages, delivering structured data to Elasticsearch — like converting numeric IDs to names. And with the processors that are a part of every Beat, you can filter and amend data easily.
File integrity monitoring
Auditbeat allows you to carefully watch lists of directories for any funny business on Linux, macOS, and Windows. File changes are sent in real time to Elasticsearch, each message containing metadata and cryptographic hashes of the file contents for further analysis.
Simply specify the paths to the directories you want Auditbeat to watch and take a congratulatory sip of coffee.
It doesn't miss a beat
Spool your Linux system events to disk so your pipeline doesn’t skip a data point — even when interruptions such as network issues occur. Auditbeat holds onto incoming data and then ships it all to Elasticsearch or Logstash when things are back online.
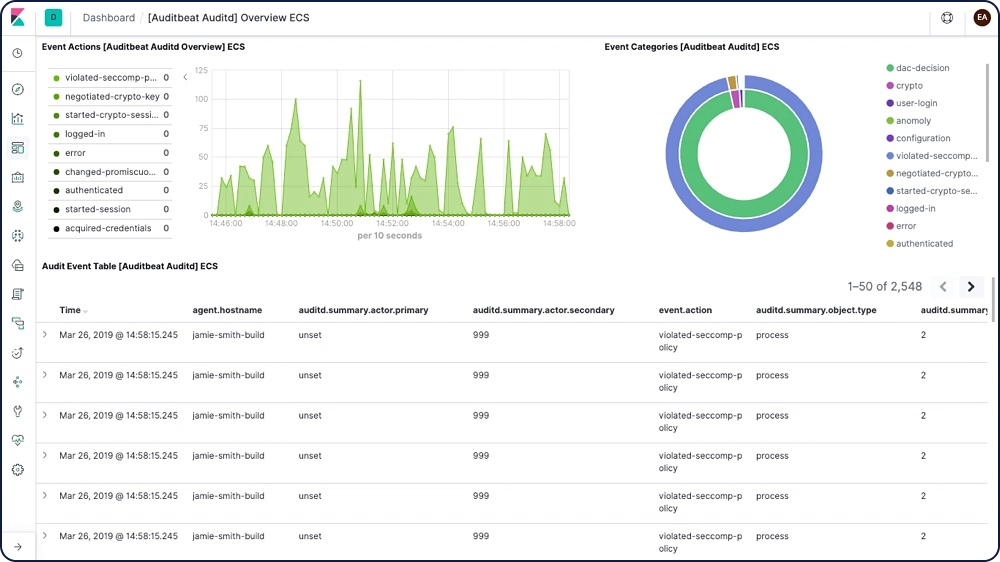
Ship to Elasticsearch. Visualize in Kibana.
Auditbeat is part of the Elastic Stack, meaning it works seamlessly with Logstash, Elasticsearch, and Kibana. Whether you want to transform or enrich your metrics with Logstash, fiddle with some analytics in Elasticsearch, or build and share dashboards in Kibana, Auditbeat makes it easy to ship your data to where it matters most.