Elastic SIEM 7.3.0 released
Editor’s Note — August 19, 2020: The Elastic SIEM solution mentioned in this post is now referred to as Elastic Security. The broader Elastic Security solution delivers SIEM, endpoint security, threat hunting, cloud monitoring, and more. If you're looking for more specific information on Elastic Security for SIEM use cases, visit our SIEM solution page.
We introduced Elastic SIEM as a beta in version 7.2, and we are already seeing strong adoption and receiving positive feedback from our community. Five weeks later, we’re here with version 7.3, and we have even more to share.
If you’d like to give Elastic SIEM a try, the 7.3 version is available on our Elasticsearch Service on Elastic Cloud, and for download in the default distribution of the Elastic Stack.
Improve detection with integrated machine learning
For 7.3, we’ve integrated machine learning anomaly detection jobs into the SIEM app, streamlining security operations workflows and taking a meaningful step toward integrating detection rules into Elastic SIEM.
Anomaly detection is vital for effective threat detection and threat hunting because it addresses gaps left by traditional correlation-based alerting. In 7.3, users can easily enable and run a set of machine learning anomaly detection jobs to detect specific attack-related behaviors — right from the SIEM app. Users looking to extend their coverage beyond these prebuilt jobs can easily add custom anomaly detection jobs using the Machine Learning app.
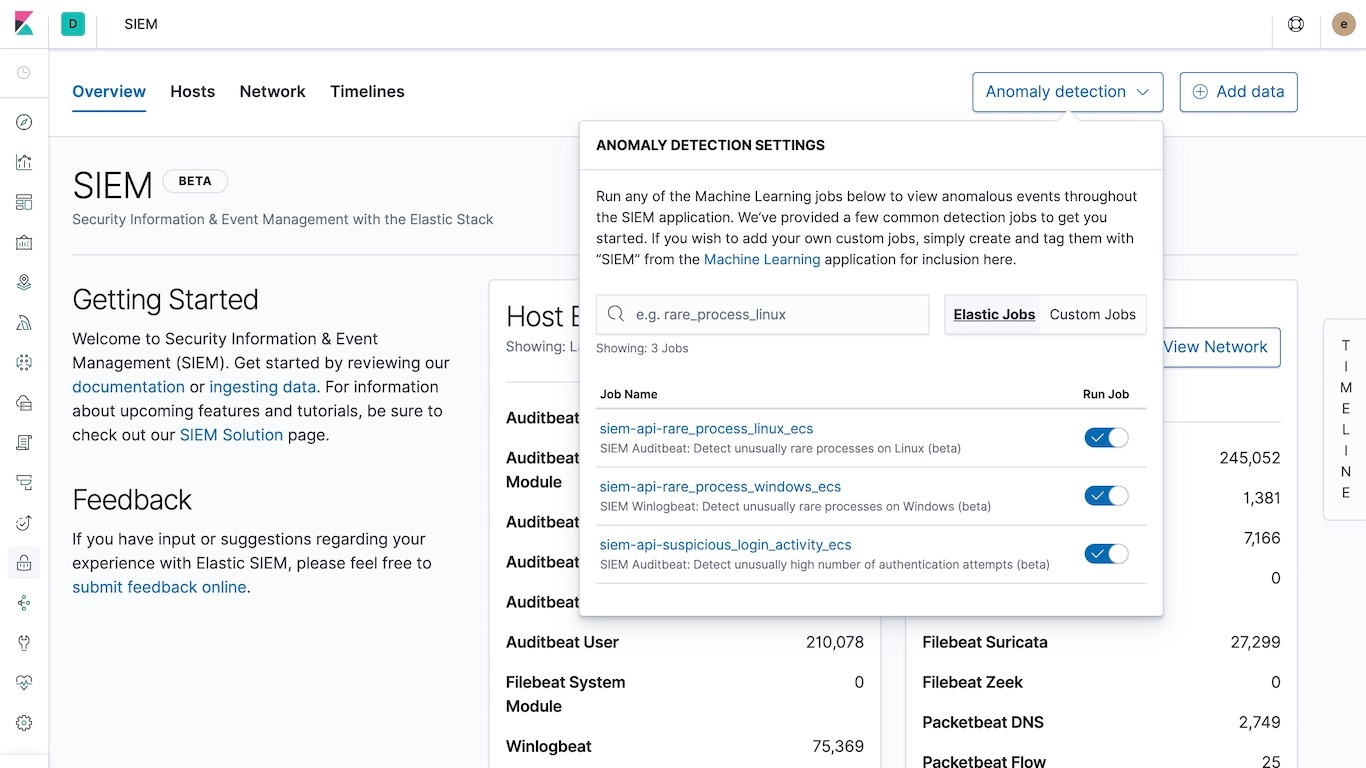
Detected anomalies are displayed on the Hosts and Network views in the SIEM app and specific details are available in the Host Details and IP Details pages.
View underlying queries
Analysts can now examine the queries that drive most of the chart and table widgets in the SIEM app. It’s as simple as accessing the Inspect button located in the top-right corner of these visualizations. This is our first step toward empowering practitioners to customize the SIEM app to support organizational workflows.
Ingest GCP VPC flow logs
We’ve also introduced a Filebeat module that ingests Virtual Private Cloud (VPC) flow logs from Google Cloud. It ships data in Elastic Common Schema (ECS) format, of course, so events are available for immediate analysis in the SIEM app (or with Maps, on a Canvas workpad...you name it).
Get started today
Haven’t tried Elastic SIEM yet? Spin up a cluster on our Elasticsearch Service or install the latest version of the Elastic Stack. Already have ECS data in Elasticsearch? Just upgrade your clusters to 7.3 and give Elastic SIEM a try.
To simplify your getting started journey, we have some great material to get you started:
- Elastic SIEM solutions page: https://www.elastic.co/solutions/siem
- Elastic SIEM documentation: https://www.elastic.co/guide/en/siem/guide/current/index.html
- Elastic SIEM webinar recording: https://www.elastic.co/webinars/introducing-elastic-siem