Elastic Cloud Hosted
Elastic Cloud Hosted is the Elastic Stack, managed through Elastic Cloud deployments.
It is also formerly known as Elasticsearch Service.
Elastic Cloud Hosted allows you to manage one or more instances of the Elastic Stack through deployments. These deployments are hosted on Elastic Cloud, through the cloud provider and regions of your choice, and are tied to your organization account.
A hosted deployment helps you manage an Elasticsearch cluster and instances of other Elastic products, like Kibana or APM instances, in one place. Spin up, scale, upgrade, and delete your Elastic Stack products without having to manage each one separately. In a deployment, everything works together.
Elastic Cloud Hosted is one of the two deployment options available on Elastic Cloud. Depending on your needs, you can also run Elastic Cloud Serverless projects.
Hardware profiles to optimize deployments for your usage.
You can optimize the configuration and performance of a deployment by selecting a hardware profile that matches your usage.
Hardware profiles are presets that provide a unique blend of storage, memory and vCPU for each component of a deployment. They support a specific purpose, such as a hot-warm architecture that helps you manage your data storage retention.
You can use these presets, or start from them to get the unique configuration you need. They can vary slightly from one cloud provider or region to another to align with the available virtual hardware.
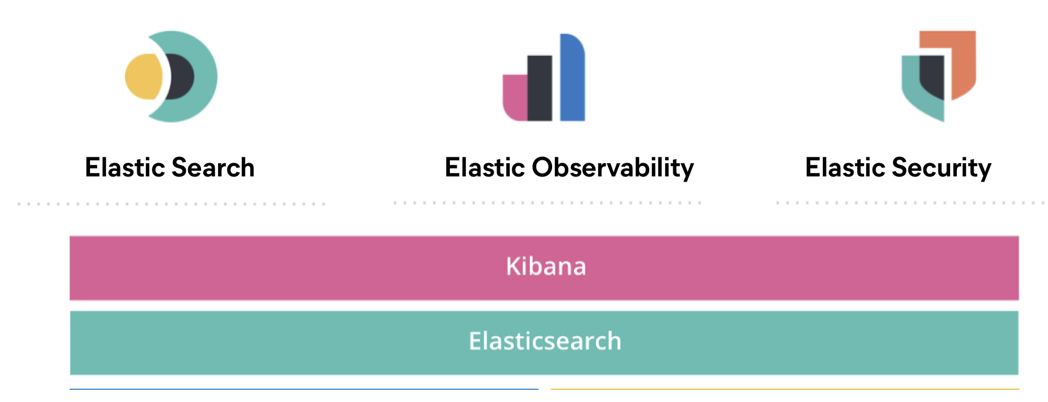
Solutions to help you make the most out of your data in each deployment.
Building a rich search experience, gaining actionable insight into your environment, or protecting your systems and endpoints? You can implement each of these major use cases, and more, with the solutions that are pre-built in each Elastic deployment.
Enterprise Search is not available in Elastic Stack 9.0+.
These solutions help you accomplish your use cases: Ingest data into the deployment and set up specific capabilities of the Elastic Stack.
Of course, you can choose to follow your own path and use Elastic components available in your deployment to ingest, visualize, and analyze your data independently from solutions.
Where to start?
Learn the basics of Elasticsearch, the Elastic Stack, and its solutions in Get started.
Sign up using your preferred method:
- Sign Up for a Trial - Sign up, check what your free trial includes and when we require a credit card.
- Sign Up from Marketplace - Consolidate billing portals by signing up through one of the available marketplaces.
Create a deployment - Get up and running very quickly. Select your desired configuration and let Elastic deploy Elasticsearch, Kibana, and the Elastic products that you need for you. In a deployment, everything works together, everything runs on hardware that is optimized for your use case.
Connect your data to your deployment - Ingest and index the data you want, from a variety of sources, and take action on it.
Adjust the capacity and capabilities of your deployments for production
There are a few things that can help you make sure that your production deployments remain available, healthy, and ready to handle your data in a scalable way over time, with the expected level of performance. Check Production guidance.
Secure your environment
Elastic Cloud has built-in security. For example, HTTPS communications between Elastic Cloud and the internet, as well as inter-node communications, are secured automatically, and cluster data is encrypted at rest.
In both Elastic Cloud Hosted and Elastic Cloud Serverless, you can augment these security features in the following ways:
- Configure IP filters to prevent unauthorized access to your deployments and projects.
- Configure private connectivity and apply VPC filtering to establish a secure connection for your deployments or projects and restrict traffic based on those private connections. Serverless supports AWS PrivateLink only; Elastic Cloud Hosted supports AWS PrivateLink, Azure Private Link, and GCP Private Service Connect.
In Elastic Cloud Hosted, you can also:
- Encrypt your deployment with a customer-managed encryption key.
- Secure your settings using Elasticsearch and Kibana keystores.
- Use the list of Elastic Cloud static IPs to allow or restrict communications in your infrastructure.
Elastic Cloud Hosted doesn't support custom SSL certificates, which means that a custom CNAME for an Elastic Cloud Hosted endpoint such as mycluster.mycompanyname.com also is not supported.
Refer to Elastic Cloud security for more details about Elastic security and privacy programs.
Refer to Security for more details.
As part of your overall security strategy, you can also do the following:
- Prevent unauthorized access with password protection and role-based access control.
- Control access to dashboards and other saved objects in your UI using Spaces. If applicable, you can also set a default CPS scope for each space.
- Connect a local cluster to a remote cluster to enable cross-cluster replication and cross-cluster search.
- Manage API keys used for programmatic access to Elastic.
Monitor your deployments and keep them healthy
Elastic Cloud Hosted provides several ways to monitor your deployments, anticipate and prevent issues, or fix them when they occur. Check Monitoring to get more details.
AutoOps is a monitoring tool that simplifies cluster management through performance recommendations, resource utilization visibility, and real-time issue detection with resolution paths. Learn more about AutoOps.
Find more information about Elastic Cloud Hosted on the following pages:
- Licenses and subscriptions
- Available stack versions
- Elastic Cloud Hosted hardware
- Elastic Cloud Hosted regions
- Service status
- Getting help
- Restrictions and known problems
Elastic Cloud Hosted FAQ
This frequently-asked-questions list helps you with common questions while you get Elastic Cloud Hosted up and running for the first time. For questions about Elastic Cloud Hosted configuration options or billing, check the Technical FAQ and the Billing FAQ.
- What is Elastic Cloud Hosted?
- Is Elastic Cloud Hosted, formerly known as Elasticsearch Service, the same as Amazon’s Elasticsearch Service?
- Can I run the full Elastic Stack in Elastic Cloud Hosted?
- Can I try Elastic Cloud Hosted for free?
- What if I need to change the size of my Elasticsearch cluster at a later time?
- Do you offer support subscriptions?
- Where are deployments hosted?
- What is the difference between Elastic Cloud Hosted and the Amazon Elasticsearch Service?
- Can I use Elastic Cloud Hosted on platforms other than AWS?
- Do you offer Elastic’s commercial products?
- Is there a limit on the number of documents or indexes I can have in my cluster?
- What is Elastic Cloud Hosted?
- Elastic Cloud Hosted is hosted and managed Elasticsearch and Kibana brought to you by the creators of Elasticsearch. Elastic Cloud Hosted is part of Elastic Cloud and ships with features that you can only get from the company behind Elasticsearch, Kibana, Beats, and Logstash. Elasticsearch is a full text search engine that suits a range of uses, from search on websites to big data analytics and more.
- Is Elastic Cloud Hosted, formerly known as Elasticsearch Service, the same as Amazon’s Elasticsearch Service?
- Elastic Cloud Hosted is not the same as the Amazon Elasticsearch service. To learn more about the differences, check our AWS Elasticsearch Service comparison.
- Can I run the full Elastic Stack in Elastic Cloud Hosted?
- Many of the products that are part of the Elastic Stack are readily available in Elastic Cloud Hosted, including Elasticsearch, Kibana, plugins, and features such as monitoring and security. Use other Elastic Stack products directly with Elastic Cloud Hosted. For example, both Logstash and Beats can send their data to Elastic Cloud Hosted. What is run is determined by the subscription level.
- Can I try Elastic Cloud Hosted for free?
- Yes, sign up for a 14-day free trial. The trial starts the moment a cluster is created. During the free trial period get access to a deployment to explore Elastic solutions for Search, Observability, Security, or the latest version of the Elastic Stack.
- What if I need to change the size of my Elasticsearch cluster at a later time?
- Scale your clusters both up and down from the user console, whenever you like. The resizing of the cluster is transparently done in the background, and highly available clusters are resized without any downtime. If you scale your cluster down, make sure that the downsized cluster can handle your Elasticsearch memory requirements. Read more about sizing and memory in Sizing Elasticsearch.
- Do you offer support?
- Yes, all subscription levels for Elastic Cloud Hosted include support, handled by email or through the Elastic Support Portal. Different subscription levels include different levels of support. For the Standard subscription level, there is no service-level agreement (SLA) on support response times. Gold and Platinum subscription levels include an SLA on response times to tickets and dedicated resources. To learn more, check Getting Help.
- Where are deployments hosted?
- We host our Elasticsearch clusters on Amazon Web Services (AWS), Google Cloud Platform (GCP), and Microsoft Azure. Check out which regions we support and what hardware we use. New data centers are added all the time.
- What is the difference between Elastic Cloud Hosted and the Amazon Elasticsearch Service?
-
Elastic Cloud Hosted is the only hosted and managed Elasticsearch service built, managed, and supported by the company behind Elasticsearch, Kibana, Beats, and Logstash. With Elastic Cloud Hosted, you always get the latest versions of the software. Our service is built on best practices and years of experience hosting and managing thousands of Elasticsearch clusters in the Cloud and on premise. For more information, check the following Amazon and Elastic Elasticsearch Service comparison page.
Note that there is no formal partnership between Elastic and Amazon Web Services (AWS), and Elastic does not provide any support on the AWS Elasticsearch Service.
- Can I use Elastic Cloud Hosted on platforms other than AWS?
- Yes, create deployments on the Google Cloud Platform and Microsoft Azure.
- Do you offer Elastic’s commercial products?
-
Yes, all Elastic Cloud Hosted customers have access to basic authentication, role-based access control, and monitoring.
Elastic Cloud Gold, Platinum and Enterprise customers get complete access to all the capabilities in X-Pack:
- Security
- Alerting
- Monitoring
- Reporting
- Graph Analysis & Visualization
Contact us to learn more.
- Is there a limit on the number of documents or indexes I can have in my cluster?
-
No. We do not enforce any artificial limit on the number of indexes or documents you can store in your cluster.
That said, there is a limit to how many indexes Elasticsearch can cope with. Every shard of every index is a separate Lucene index, which in turn comprises several files. A process cannot have an unlimited number of open files. Also, every shard has its associated control structures in memory. So, while we will let you make as many indexes as you want, there are limiting factors. Our larger plans provide your processes with more dedicated memory and CPU-shares, so they are capable of handling more indexes. The number of indexes or documents you can fit in a given plan therefore depends on their structure and use.