Elastic 및 AWS Serverless Application Repository(SAR): Amazon S3에서 원활한 로그 수집을 통해 실행 가능한 인사이트 확보 시간 단축

기업이 Amazon Web Services(AWS) 클라우드 플랫폼과 서비스를 활용하여 운영 효율성을 높이고 제품을 시장에 출시할 때 로그는 Amazon Simple Storage Service(S3)에 저장된 후 외부 모니터링 및 분석 솔루션으로 보내지는 경우가 많습니다. 이제 AWS 사용자는 AWS Lambda 애플리케이션인 새로운 Elastic 서버리스 포워더를 사용하여 Amazon S3에 저장된 로그를 신속하게 수집하고, 다른 로그 및 메트릭과 함께 Elastic Stack에서 확인하여 중앙 집중식 분석을 수행할 수 있습니다.
AWS에서 Elastic으로 직접 데이터를 수집함으로써 VM 프로비저닝이나 데이터 수집기 설치와 같이 시간이 오래 걸리는 프로세스를 건너뛰고 관리 오버헤드를 줄입니다.
이 블로그에서는 AWS Serverless Application Repository(SAR)에 게시된 Elastic 서버리스 포워더 를 사용하여 아키텍처를 간소화하고 로그를 Elastic으로 전송하는 방법을 소개합니다. 이를 활용하면 멀티 클라우드와 온프레미스 환경을 모니터링하고 보호하실 수 있습니다.
AWS 환경의 상태와 성능 모니터링
Enterprise Management Associates(EMA) 그룹의 조사에 따르면, 하이브리드 및 멀티 클라우드 에코시스템의 복잡성이 증가하는 것을 고려할 때 통합 가시성이 중요한 비즈니스 이니셔티브이자 DevOps 팀의 최우선 당면 과제가 되고 있는 것은 놀라운 일이 아닙니다. 많은 조직이 제품의 시장 출시를 앞당기고 오버헤드를 줄이기 위해 컨테이너부터 서버리스 컴퓨팅까지 다양한 기술을 선택하므로 모든 아키텍처를 포괄하는 통합 가시성 솔루션이 필요하다는 점을 인식해야 합니다. EMA 연구에 따르면 포괄적인 통합 가시성 솔루션을 구현하는 팀은 개발 시간을 70% 단축하고 향상된 제품 속도를 유지관리하면서 4배 더 많은 기능을 제공할 수 있다고 합니다.
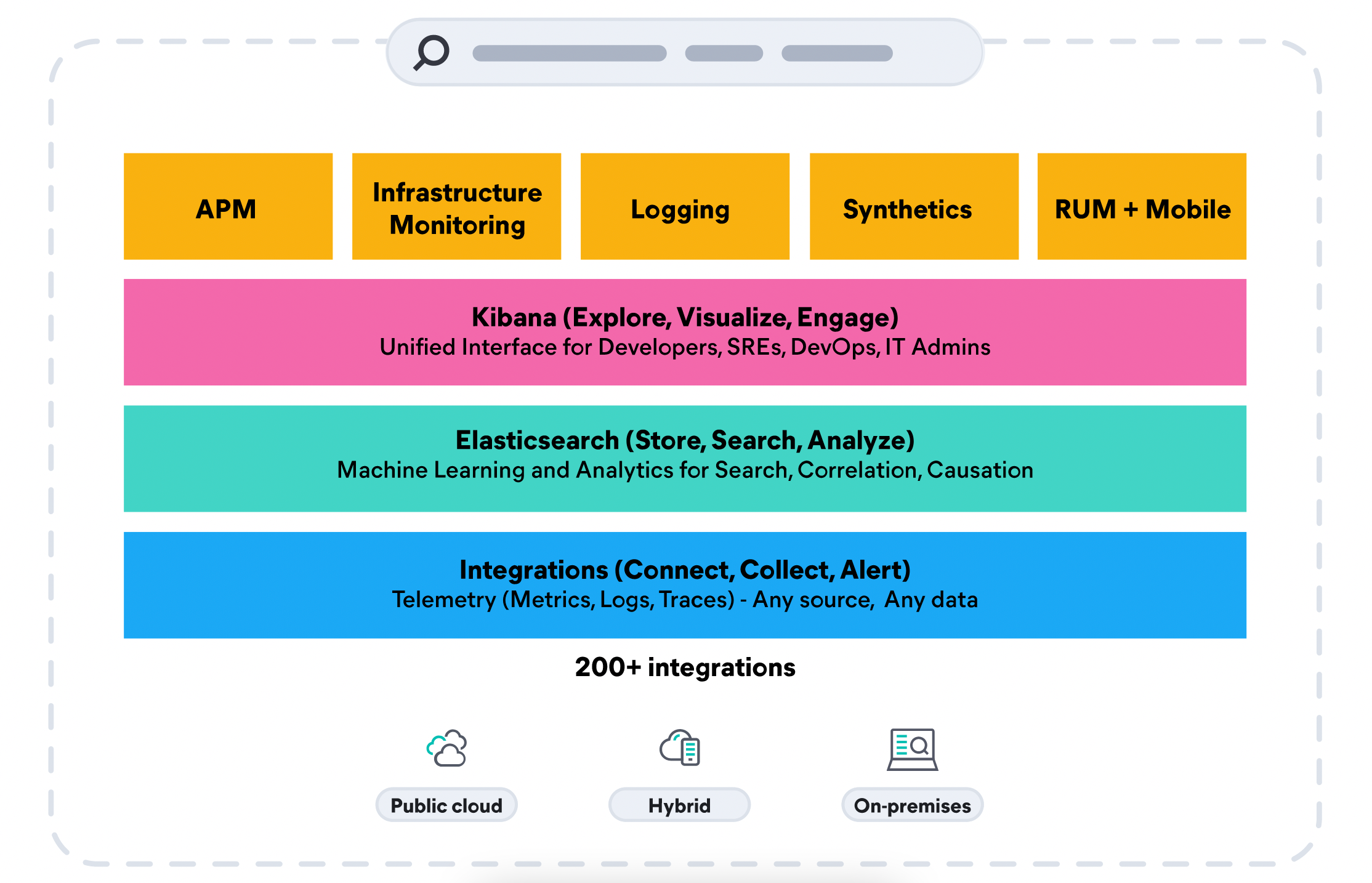
Elastic Observability는 온프레미스 데이터 세트와 함께 하이브리드 AWS 환경 전반에 걸쳐 단일 스택에서 대규모로 로그, 메트릭, APM 추적을 통합하여 전체 상황별 보기를 제공합니다. AWS Lambda, Amazon Elastic Compute Cloud(Amazon EC2), Amazon Elastic Container Service(Amazon ECS), Amazon Elastic Kubernetes Service(Amazon EKS), Amazon S3 등을 포함하여 광범위한 AWS 서비스 전반에 걸쳐 성능을 추적하고 모니터링합니다.
보안 팀이 클라우드 규모로 위협을 신속하게 차단할 수 있도록 지원
의뢰를 받아 실시된 Forrester 연구에 따르면, 고객은 Elastic Security와 Observability 솔루션을 함께 사용하여 최대 75%의 비용 절감을 달성했으며 기존 솔루션보다 10배 빠른 것으로 나타났습니다. Elastic Common Schema와 단일 리포지토리 아키텍처를 제공하므로 Amazon S3 및 기타 데이터 세트의 동일한 통합 가시성 데이터를 확장 탐지 및 대응(XDR)에 사용하여 평균 탐지 시간을 0에 가깝게 단축할 수 있습니다. Elastic Security는 SIEM과 엔드포인트 보안을 통합하여 조직이 다양한 소스에서 대량의 데이터를 수집 및 유지하고, 데이터를 보다 장기간 저장 및 검색하며, 탐지 및 머신 러닝을 통해 위협 헌팅을 강화할 수 있도록 합니다. 데이터 사일로를 제거하고, 경보 피로도를 줄이고, 조직이 환경 전반에서 위협을 신속하게 차단하도록 지원해 보세요.
빠른 검색과 향후 분석을 위해 비용 효율적으로 데이터 저장
비용 효율성을 위해 Amazon S3를 활용하는 또 다른 방법이 있습니다. Elastic은 S3에 저장된 로그를 Elastic으로 수집하는 것 외에도 조직이 Amazon S3 같은 저렴한 객체 저장 공간에 대량의 과거 데이터를 보관하는 동시에 완전히 활성화되고 검색 가능한 상태로 유지되도록 지원합니다. 원하는 기간 동안 원하는 세분화 수준으로 AWS 및 온프레미스 데이터를 유지하고 데이터가 증가함에 따라 확장해 보세요. 조직의 데이터 성능, 복원력, 보존 요구 사항을 기반으로 인덱스 수명 주기 관리와 자동 크기 조정 기능을 통해 데이터 관리 및 계층화가 자동화됩니다.
데이터 수집 간소화
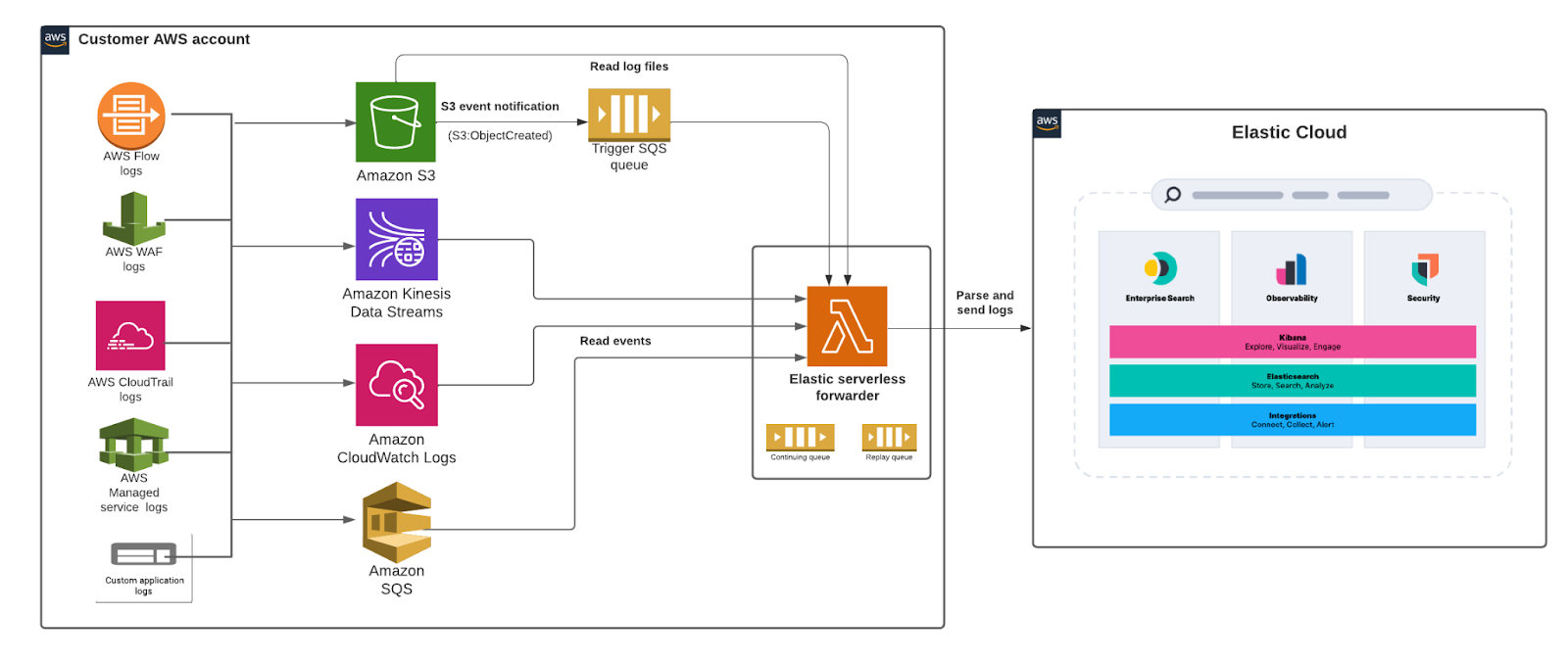
Elastic 서버리스 포워더 Lambda 애플리케이션은 Amazon S3 버킷에 포함된 로그 수집을 지원하고 이를 Elastic으로 보냅니다. Amazon S3의 SQS 대기열 이벤트 알림은 Lambda 함수의 트리거 역할을 합니다. 새 로그 파일이 Amazon S3 버킷에 기록되고 기준을 충족하면 Lambda 함수를 트리거하는 알림이 생성됩니다.
사용자는 S3 버킷에 SQS 함수 트리거를 설정하고 Elastic 연결 정보를 제공하여 로그 흐름을 허용하고 Kibana의 미리 빌드된 대시보드와 전체 분석 기능을 사용하여 로그 데이터를 활용할 수 있습니다.
아키텍처 다이어그램:
그럼 시작해볼까요
이 섹션에서는 Elastic 서버리스 포워더를 시작하여 Elastic Stack에서 Amazon Virtual Private Cloud(VPC) 흐름 로그를 분석하는 방법에 대한 단계별 튜토리얼을 살펴보겠습니다.
자세한 지침은 Elastic 서버리스 포워더 설명서를 참조하세요.
Amazon VPC 흐름 로그를 Elastic으로 수집하면 Amazon VPC 내의 네트워크 트래픽을 모니터링 및 분석하고 다음을 통해 정보에 입각한 결정을 내릴 수 있습니다.
- 로그를 빠르게 검색하고, 보고, 필터링하는 기능으로 Kibana에서 흐름 로그 데이터 분석
- 보안 그룹 규칙 평가 및 보안 격차 파악
- 특정 트래픽 유형이 탐지될 때 알려주는 경보 설정
- 일관된 성능을 보장하기 위한 지연 시간 문제 파악 및 기준 설정
시작하기 전에
- 아직 Elastic을 사용하고 있지 않다면 Elastic Cloud에서 호스팅되는 Elasticsearch Service를 사용하여 배포를 생성하세요. 배포에는 데이터 저장 및 검색을 위한 Elasticsearch 클러스터와 데이터 시각화 및 관리를 위한 Kibana가 포함됩니다. 자세한 내용은 Elastic Stack 구동하기를 참조하세요.
- S3 버킷으로 전송되도록 AWS VPC 흐름 로그를 활성화합니다. 해당 설정이 없는 경우, 손쉽게 S3 버킷을 생성하고 해당 버킷으로 VPC 흐름 로그를 전송할 수 있습니다. 기본적으로 단계는 다음과 같습니다.
- S3 버킷 생성(예: vpc-flow-logs)
- EC2 콘솔에서 특정 네트워크 인터페이스를 선택하고 작업 메뉴에서 ‘흐름 로그 생성’을 선택합니다. 이전 단계에서 생성한 S3 버킷을 대상으로 선택합니다. 자세한 내용은 AWS 설명서를 참조하세요.
- 이제 SQS 대기열(예: flow-logs-queue)을 생성하고 S3의 S3 이벤트 알림이 대기열로 전송되도록 적절한 액세스 정책을 설정하겠습니다. S3 버킷(vpc-flow-logs)에서 모든 객체 ‘이벤트 생성’에 대한 이벤트 알림이 SQS 대기열(flow-logs-queue)로 전송되도록 구성합니다. 자세한 내용은 AWS 설명서를 참조하세요.
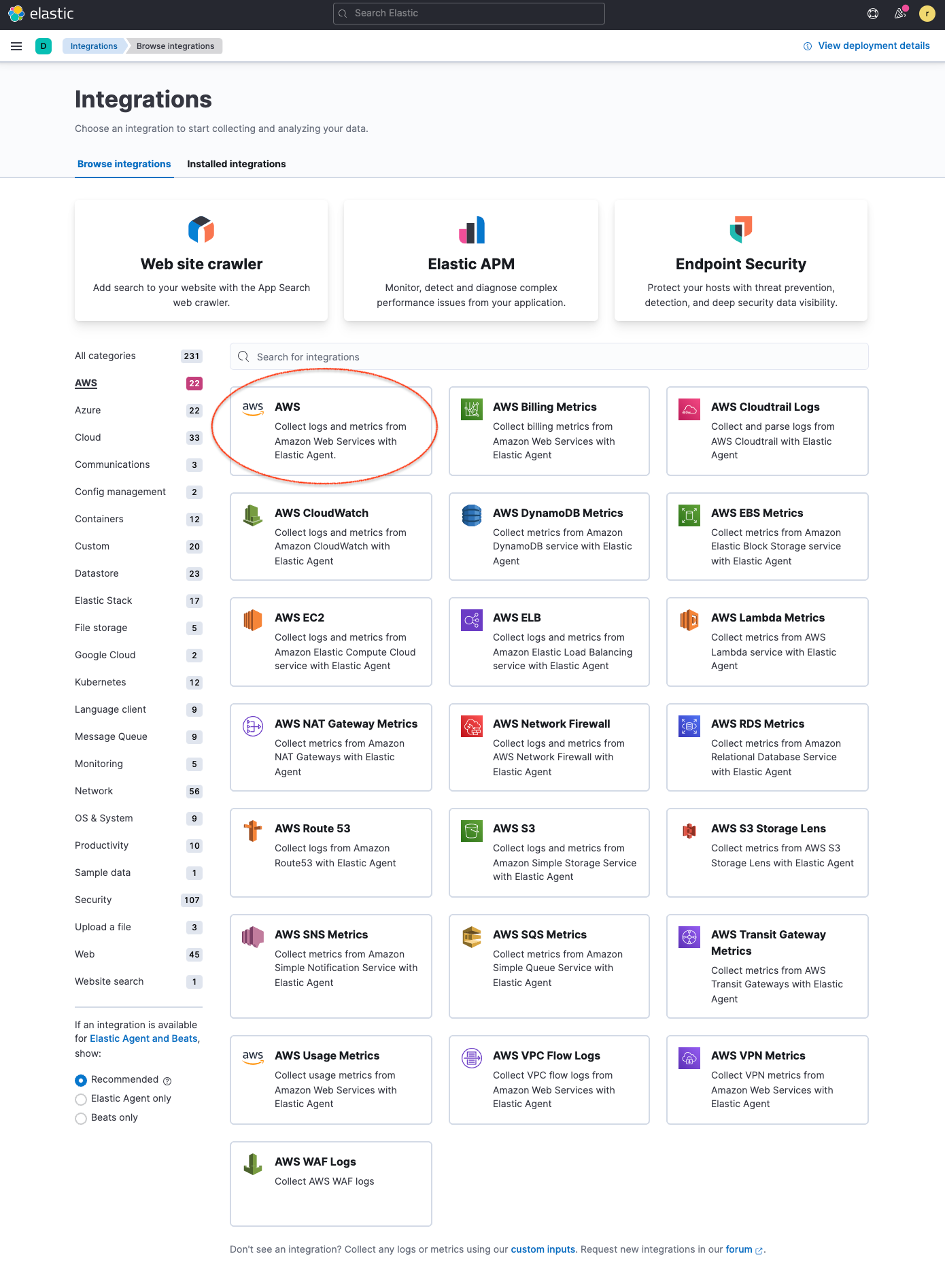
- 그런 다음 Kibana 웹 UI에서 Elastic AWS 통합을 설치합니다. 여기에는 미리 빌드된 대시보드, 수집 노드 구성, 사용자가 수집하는 로그를 최대한 활용할 수 있는 기타 자산이 포함되어 있습니다. Kibana의 통합으로 이동하여 AWS를 검색합니다. 자세한 내용을 보려면 AWS 통합을 클릭하고, 모든 AWS 통합 자산을 설치하려면 설정을 선택한 다음 AWS 자산 설치를 클릭합니다.
5. 다음으로, elastic-serverless-forwarder가 입력 소스와 대상 정보에 대한 Elastic 연결을 파악하는 데 사용할 새 S3 버킷 및 구성 파일을 생성해 보겠습니다.
.png)
다음은 샘플 구성 파일입니다.
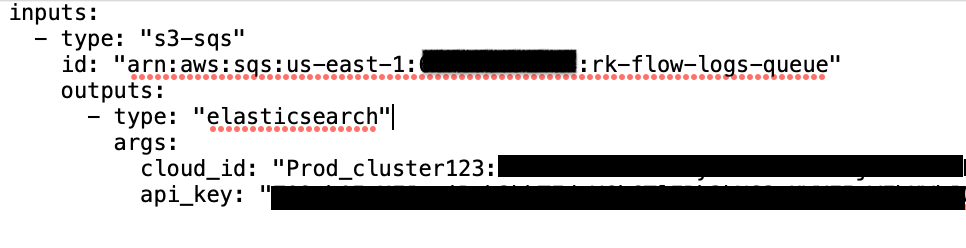
Elastic Cloud로 이동하고 Elastic Cloud 콘솔에서 Cloud ID를 복사하여 ‘cloud_id’ 파라미터에 명시합니다. Kibana로 이동하여 인증을 위해 Base64로 인코딩된 API 키를 생성하고 ‘api_key’ 파라미터에 명시합니다. 민감한 값은 AWS Secrets Manager에 저장하고 구성 파일에서 이를 참조해야 합니다.
6. AWS SAR에서 elastic-serverless-forwarder를 배포하고, Lambda 함수가 VPC 흐름 로그를 Elastic으로 수집하기 시작하도록 적절한 구성을 제공합니다.
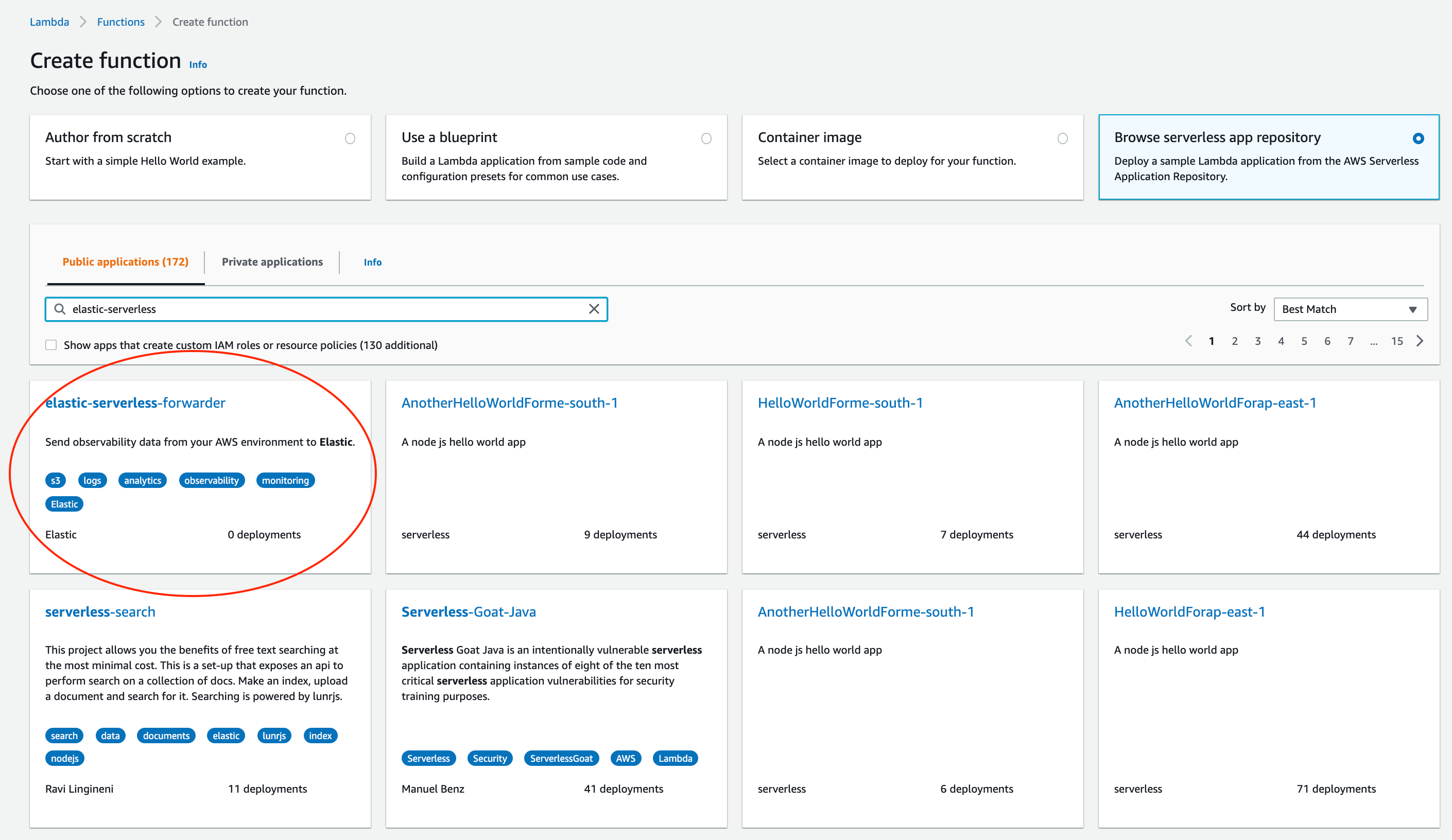
Lambda 콘솔에서 함수->함수 생성을 선택하고, 서버리스 앱 리포지토리 탐색을 선택하고, elastic-serverless-forwarder를 검색하고 해당 애플리케이션을 선택합니다.
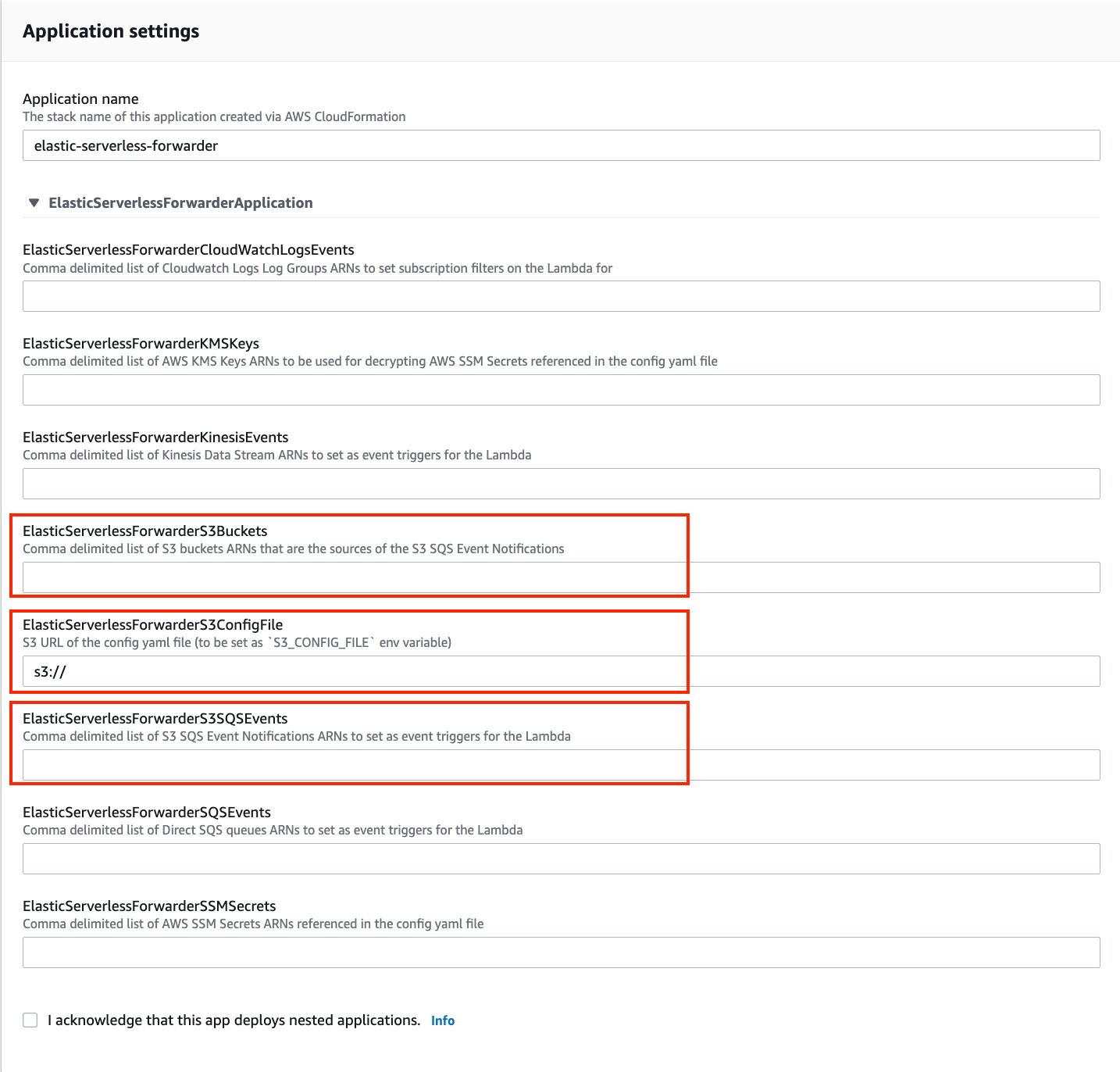
애플리케이션의 검토, 구성 및 배포 페이지에서 다음 필드를 작성합니다.
- VPC 흐름 로그가 전송되는 ElasticServerlessForwarderS3Buckets에서 S3 버킷을 지정합니다. 값은 2단계에서 생성한 S3 버킷의 ARN입니다.
- ElasticServerlessForwarderS3ConfigFile에서 구성 파일 경로를 지정합니다. 값은 5단계에서 생성한 구성 파일(sarconfig.yaml)을 가리키는 ‘s3://bucket-name/config-file-name’ 형식의 S3 URL입니다.
- ElasticServerlessForwarderS3SQSEvents에서 Lambda 함수의 트리거로 사용되는 S3 SQS 알림 대기열을 지정합니다. 값은 3단계에서 생성한 SQS 대기열의 ARN입니다.
위 값은 Lambda 배포에서 최소한의 IAM 정책을 생성하고 Lambda 함수가 적절하게 실행되도록 환경 변수를 설정하는 데 사용됩니다.
배포된 Lambda는 S3 버킷에 기록되는 VPC 흐름 로그 파일을 읽고 이를 Elastic으로 보냅니다.
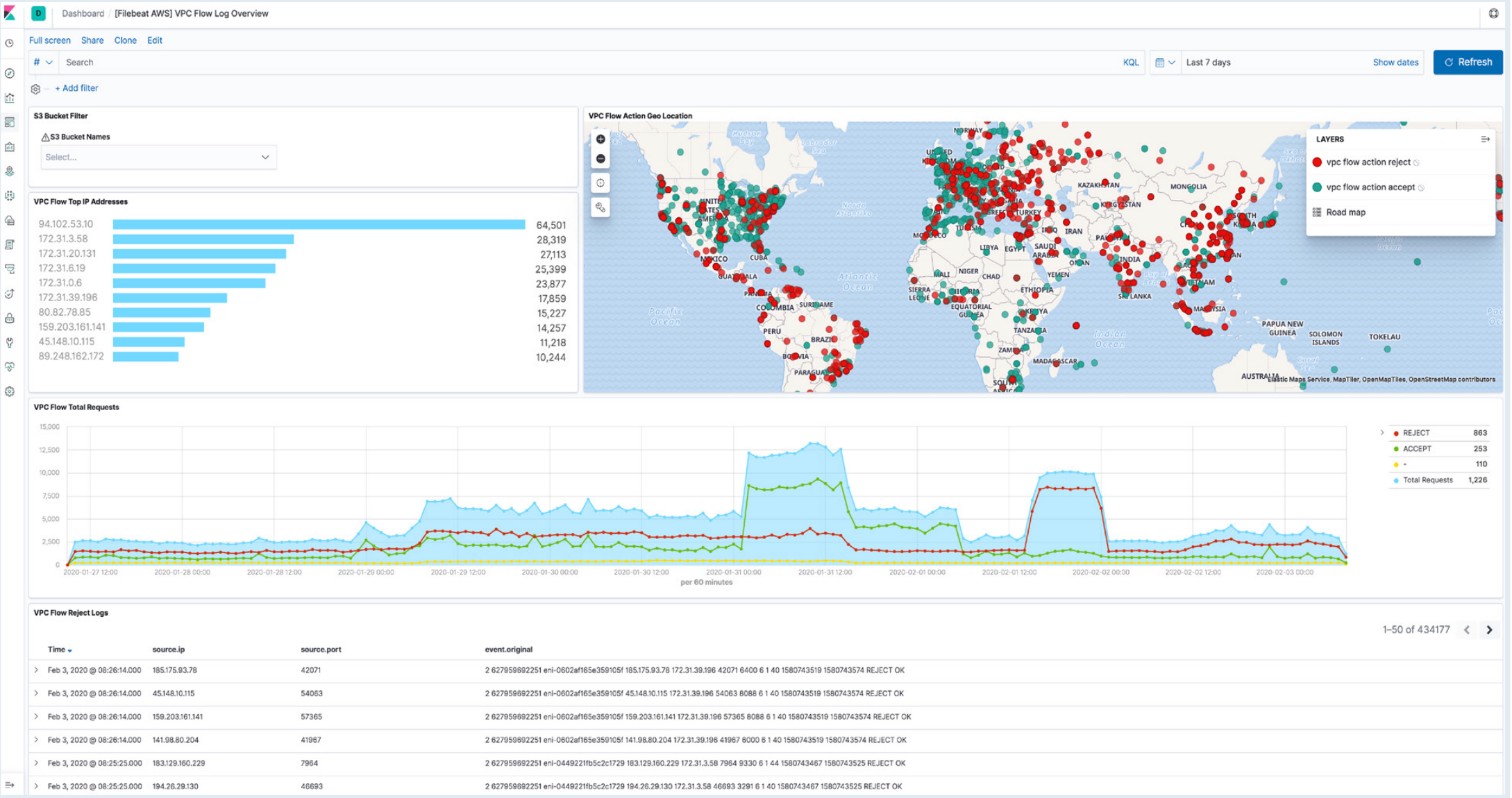
7. Kibana로 이동하여 로그가 [Logs AWS] VPC 흐름 로그 개요 대시보드에서 구문 분석되고 시각화되었는지 확인합니다.
결론
Elastic은 언제 어디서나 액세스할 수 있도록 원활한 고객 경험을 지속적으로 제공하고 있으며, AWS와의 간소화된 통합이 이러한 노력을 보여주는 최신 사례입니다. 자세히 알아보려면 elastic-serverless-forwarder 설명서로 이동하거나 AWS를 위한 Elastic Observability 가이드를 다운로드하세요.
지금 무료 체험판 시작
AWS Marketplace를 통해 가입하여 나만의 7일 무료 체험판을 시작하고, 전 세계 AWS의 Elastic Cloud 리전 어디에서나 몇 분 만에 배포를 빠르게 시작해 보세요. AWS Marketplace에서 Elastic을 구매하신 경우, 월별 통합 청구 내역서에 포함되며 AWS에 대한 약정 지출에서 반영되어 차감됩니다.
이 게시물에 설명된 기능의 릴리즈 및 시기는 Elastic의 단독 재량에 따릅니다. 현재 이용할 수 없는 기능은 정시에 또는 전혀 제공되지 않을 수 있습니다.