Secure your deployments on Elastic Cloud with Azure Private Link
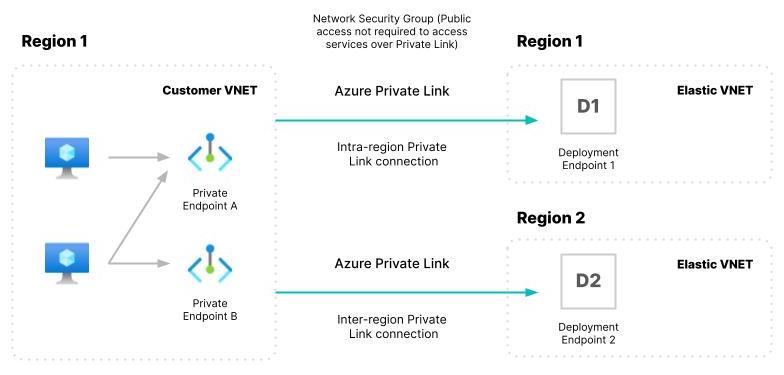
We are pleased to announce the general availability of the Azure Private Link integration with Elastic Cloud. Azure Private Link provides private connectivity between your VNET (Virtual Network) and other Azure resources. Private Link simplifies your cloud network architecture and eliminates data exposure to the public internet by routing your data to private Azure service endpoints.
The use of Azure Private Link with Elastic Cloud provides an additional layer of security to help you meet your security policy and compliance requirements. You can take advantage of Azure Private Link across all subscription tiers on Elastic Cloud. In this blog we’ll show you how easy it is to get started. We’ll walk you through the steps to configure Private Link access between your VNET and Elastic Cloud deployment.
Step 1: Create a Private Link endpoint using the Elastic Cloud service alias
First you’ll need to create a Private Link endpoint using the Azure portal or command line interface (CLI). The Private Link endpoint is assigned a private IP address from your VNET.
Create a private endpoint in your VNet using the service alias for your region. Follow the Azure instructions for details on creating a private endpoint to an endpoint service. Use the service aliases for the region in which your Elastic Cloud deployment is hosted. The IP address of the private endpoint is used to create a DNS A record, this will be done in the next step.
For example, here is what creating an endpoint for the region East US 2 looks like using the Azure Private Link Service Alias for that region: eastus2-prod-002-privatelink-service.64359fdd-7893-4215-9929-ece3287e1371.eastus2.azure.privatelinkservice.
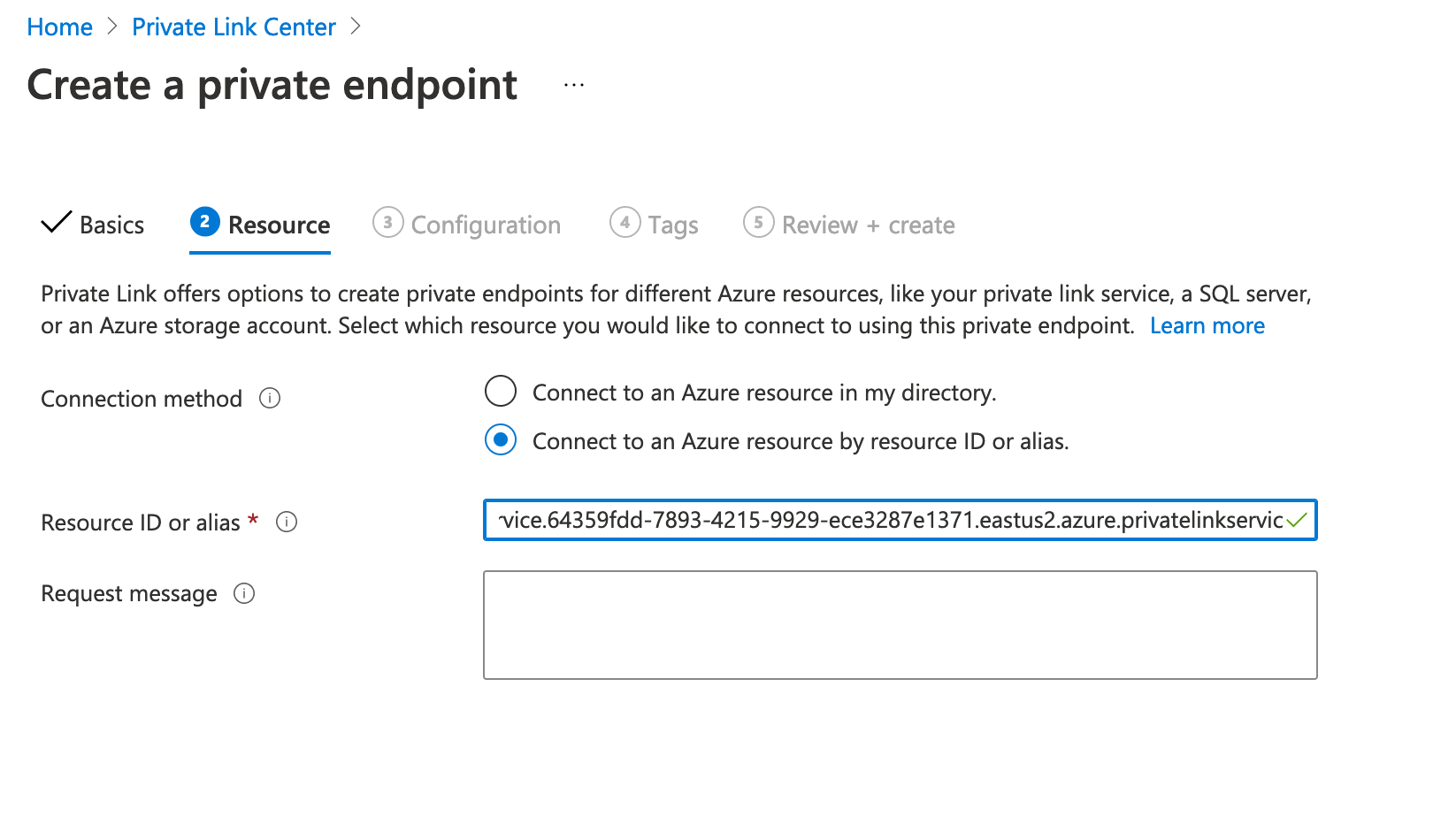
Your endpoint has a private IP address and you can find this through the network interface for the endpoint.
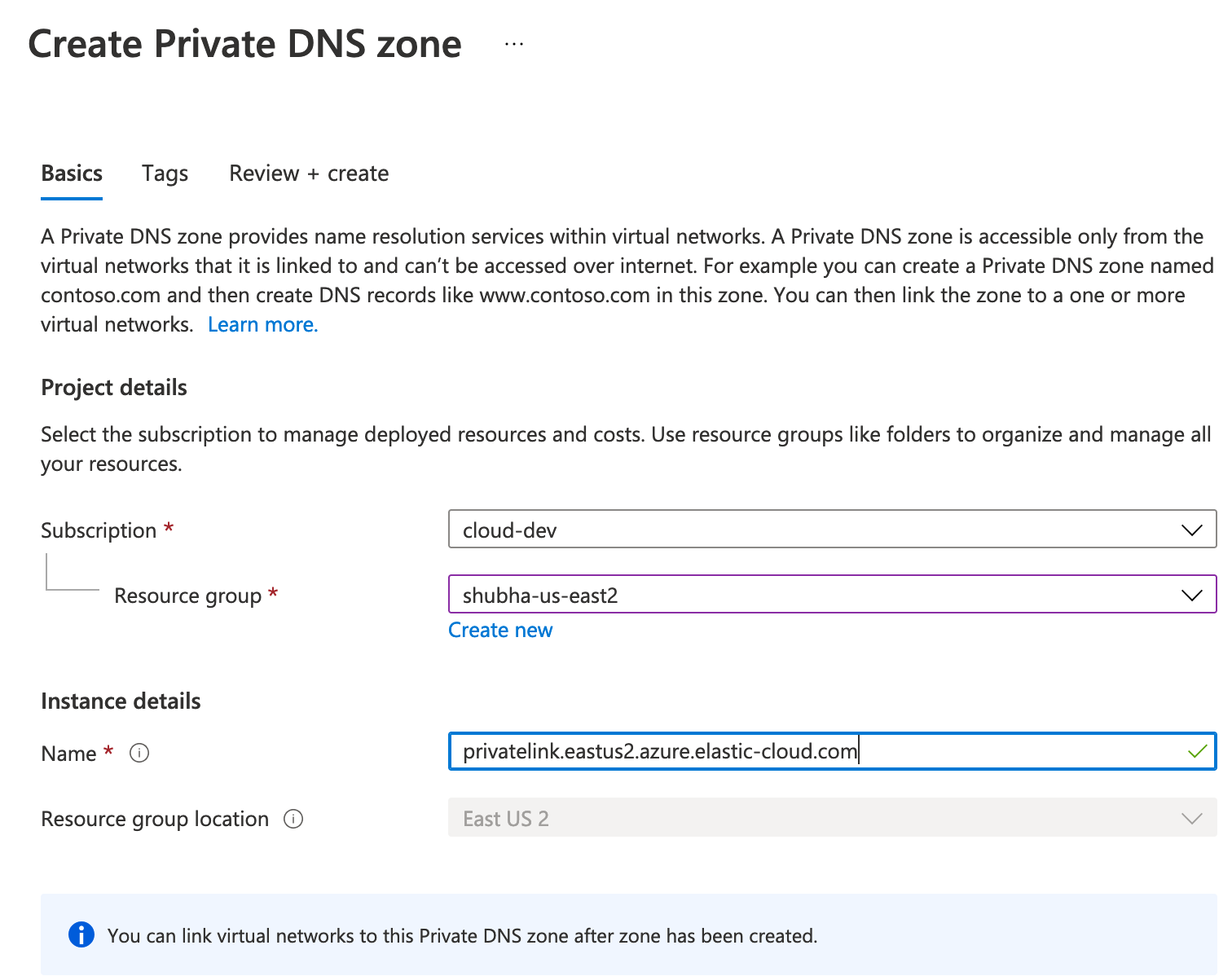
Step 2: Create a DNS record for the Private Link endpoint
Create a DNS record for your private endpoint and associate it with the VNet your Private Link endpoint resides in (learn more at Azure Private Endpoint DNS Configuration).
- Create a Private DNS zone using the Private Hosted Zone domain name listed in our documentation for your region.
- Associate the VNET your private endpoint resides in.
- Create a DNS A record pointing to the IP address of the private endpoint.
To see detailed instructions refer to our documentation. Below is an example of using privatelink.eastus2.azure.elastic-cloud.com as the Private Hosted Zone DNS.
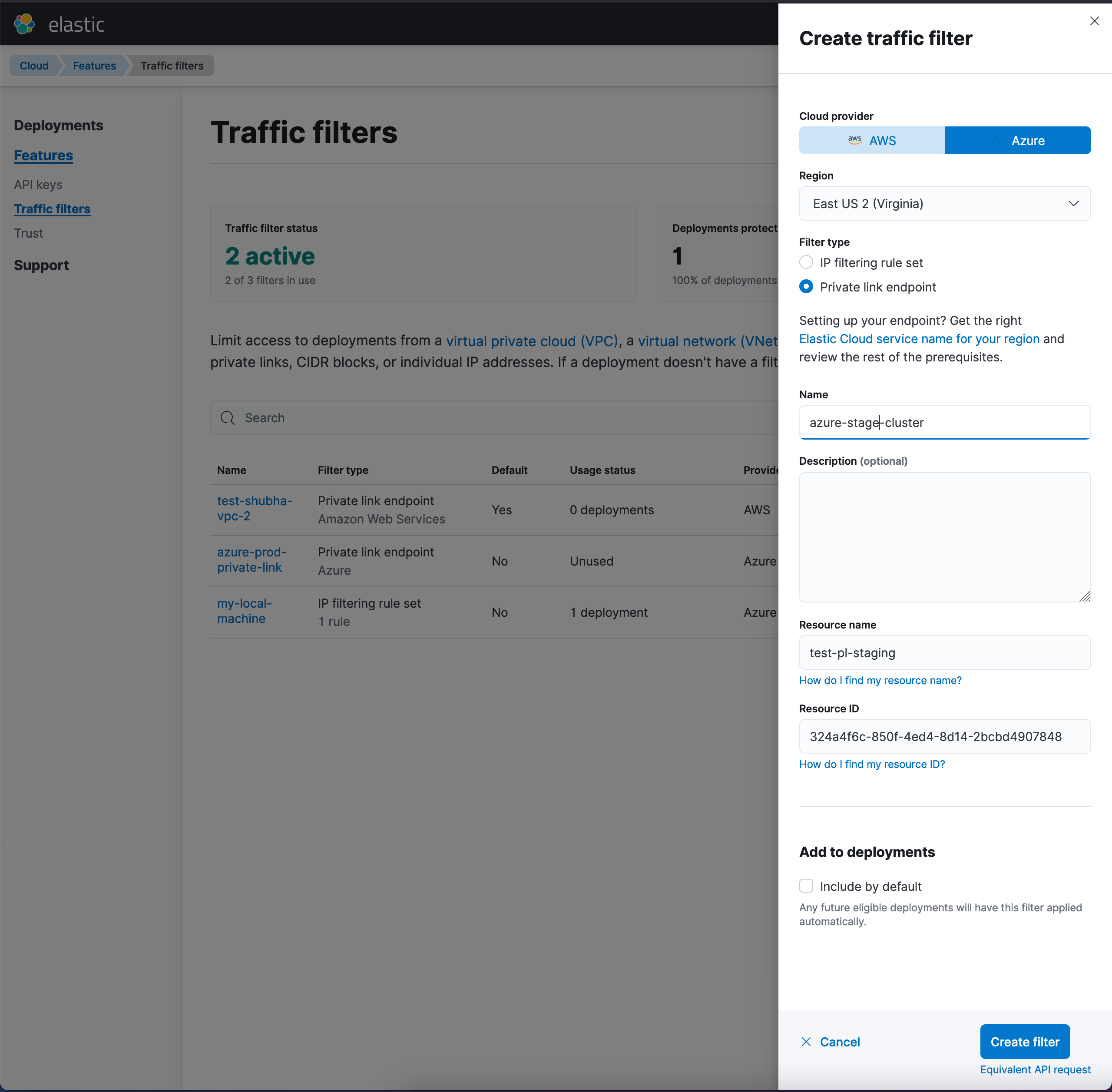
Step 3: Create a traffic filter for the Private Link endpoint on the Elastic Cloud portal
Create a traffic filter and select the filter type “Private Link endpoint” on the Elastic Cloud portal and in the next step associate it with one or more deployments. This is when Elastic approves your Private Link endpoint. Once you associate a Private Link endpoint traffic filter with a deployment, only clients connecting through the endpoint using the Private Link route will be able to reach all the endpoints (e.g., Elasticsearch, Kibana, APM Server, etc.) in your deployment.
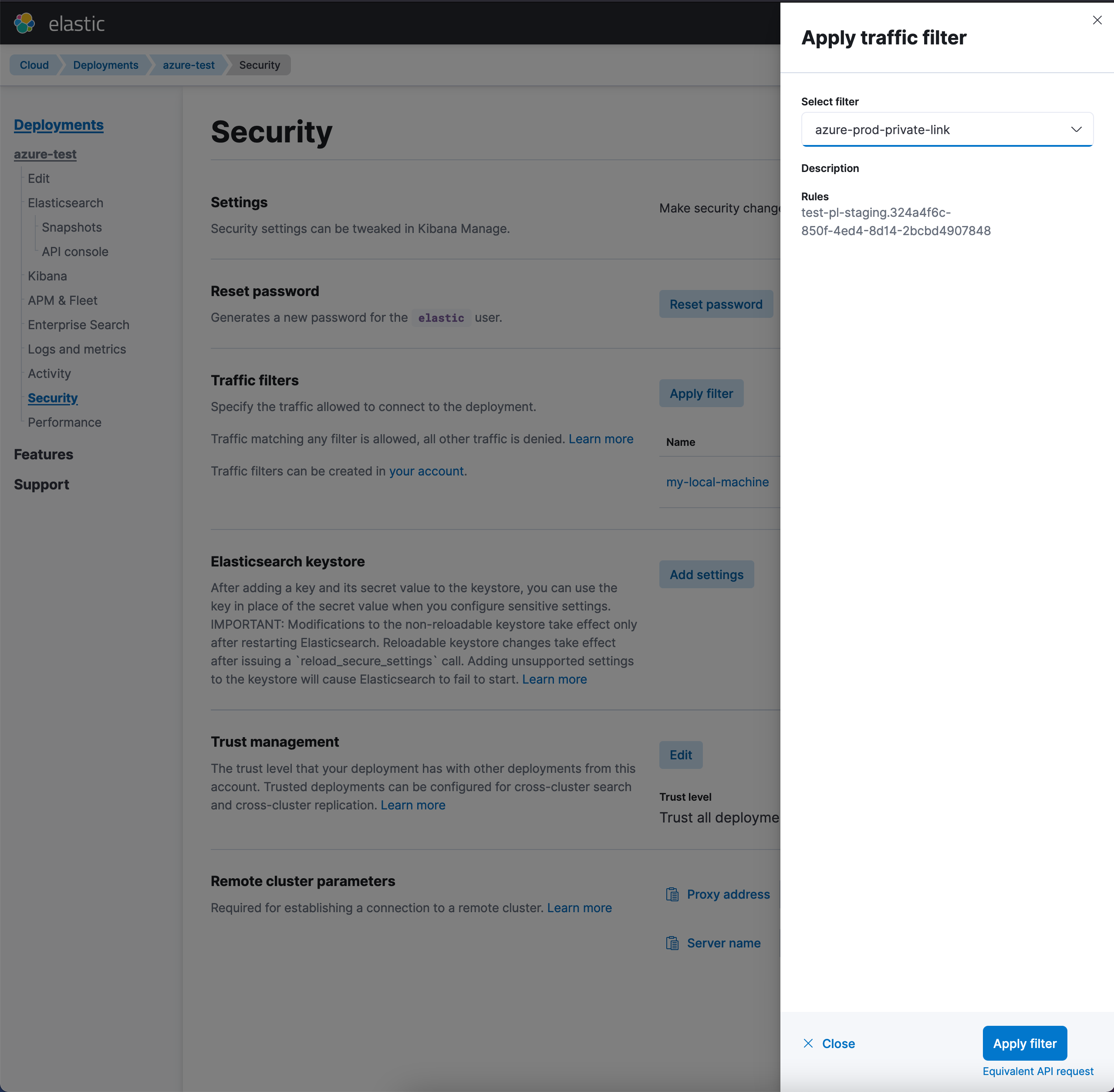
Step 4: Associate the traffic filter to one or more deployments
Apply the newly created traffic filter to all relevant deployments through the Elastic Cloud console. Once you associate a filter, your deployment will only be accessible from IP addresses and VNETs you specify in your configuration. The deployment endpoints for accessing your Elasticsearch cluster from a VNET for instance is https://<elasticsearch-cluster-id>.privatelink.eastus2.azure.elastic-cloud.com:9243.