What’s new in Elastic Security 8.10: Scale your defenses and outpace attackers
Richer alert contextualization, generative AI in GA, ATT&CK® coverage view, cloud security posture management (CSPM) for Google Cloud, and automated CSPM onboarding for AWS accounts

Elastic Security brings a MITRE ATT&CK®-aligned detection coverage view, richer alert contextualization, and extended cloud security posture management (CSPM) to Google Cloud Platform (GCP). Together, these capabilities help the SOC find and address gaps in detection coverage, investigate attacks faster, and proactively address cloud misconfigurations and vulnerabilities.
Elastic Security 8.10 is available now on Elastic Cloud — the only hosted Elasticsearch offering to include all of the new features in this latest release. You can also download the Elastic Stack and our cloud orchestration products, Elastic Cloud Enterprise and Elastic Cloud for Kubernetes, for a self-managed experience.
What else is new in Elastic 8.10? Check out the 8.10 announcement post to learn more >>
Investigate faster with rich alert contextualization
Elastic Security 8.10 reimagines the analyst experience, fueling faster and more effective alert investigation. Together with the alert monitoring, triage, and management improvements delivered in earlier releases, it helps practitioners quickly discard false-positives, determine the root-cause and scope of attacks, and respond before damage is done.
The solution offers analysts the information they need, when they need it — and shifts smoothly between facilitating fast alert triage and methodical investigation. Context and continuity are its hallmarks.
Opening the restyled Alert sidebar reveals an array of valuable guidance and context, accelerating exploration. The analyst can see why the alert fired and easily access rule and alert details, along with relevant MITRE ATT&CK tactics and techniques. A full investigation guide can now be viewed alongside the alert. Previews of the Analyzer and Session View visualizations are available, too.
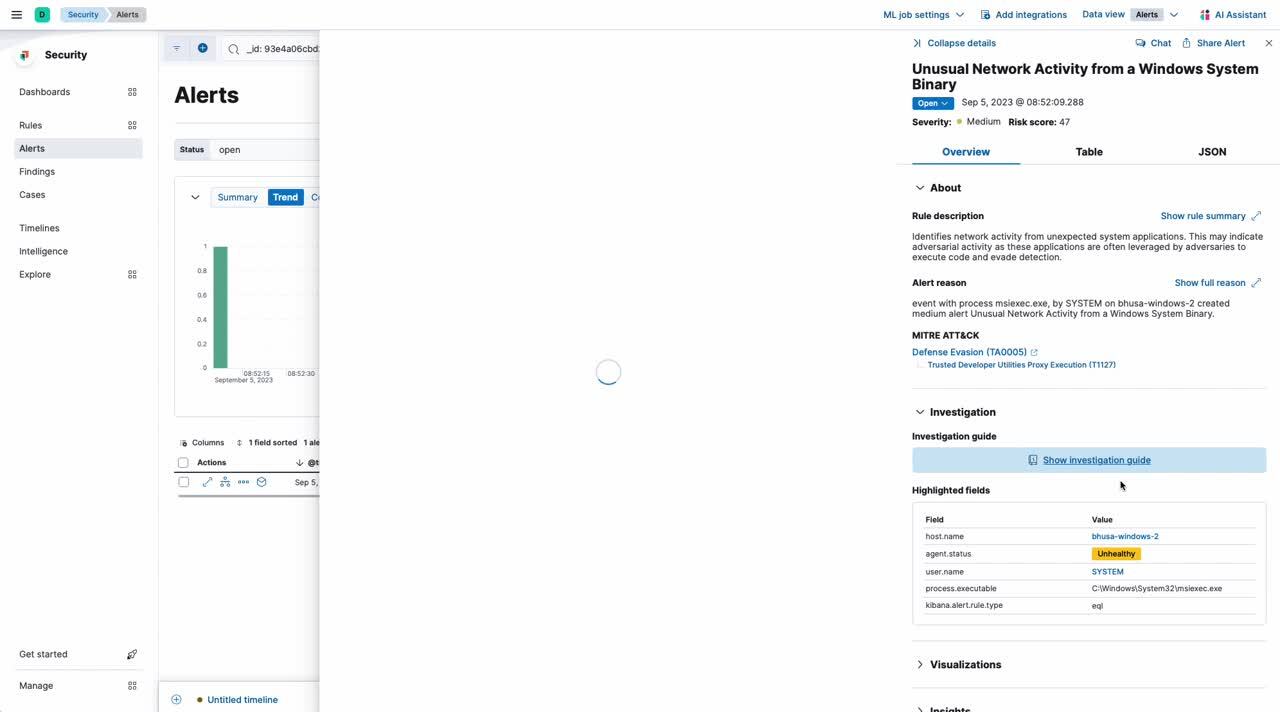
Analysts can access rich insights by expanding the Alert sidebar, including host and user risk scoring from Elastic advanced entity analytics, threat intelligence from third-party feeds, correlated cases and events, and field value prevalence. The release preserves valuable visibility into threat intelligence matches and correlations.
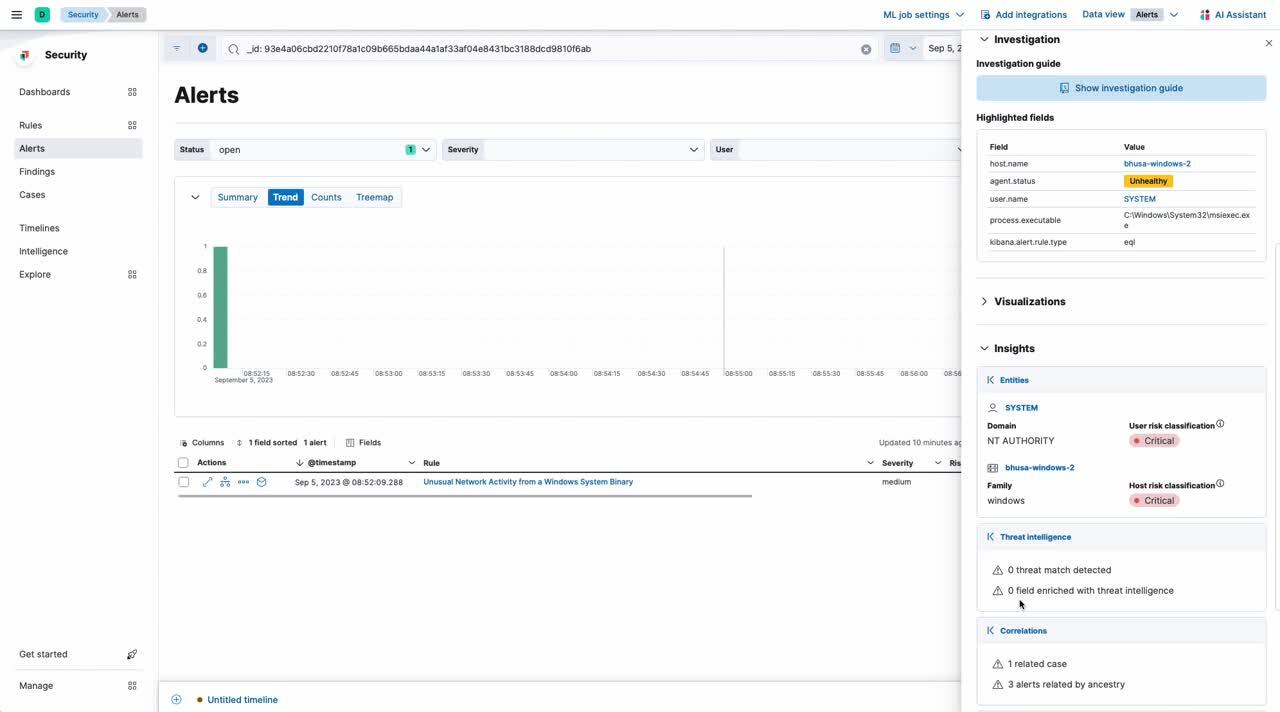
This readily accessible information powers investigation. An analyst investigating a suspected compromised user account, for example, can see all of the hosts that a specific user has accessed, right from the Entities section of the expanded Alert sidebar.
Highlighted fields guide practitioners to the data that matters most, and new in 8.10, these fields can be customized. Practitioners can see how rare or common these attributes are for the hosts and users of their organization, helping indicate whether it is innocuous or malicious. For example, if an executable is observed on every host, it’s probably less worrisome, but if it’s new to the environment, it might merit a closer look.
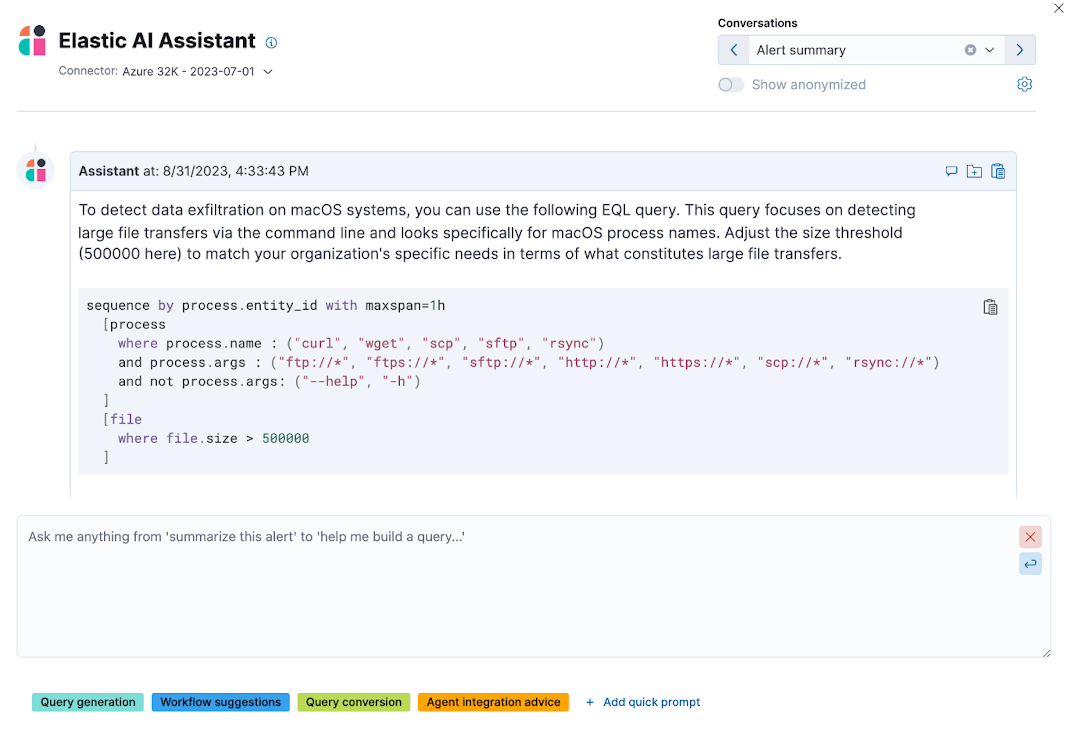
More big news: Elastic AI Assistant, our generative AI sidekick, enters general availability today. To help analysts triage and investigate suspected attacks faster and more effectively, it synthesizes alert details, suggests next steps, and explains how to accomplish tasks within Elastic.
Uncover and address detection gaps across MITRE ATT&CK®
To advance an organization’s security posture over time, the SOC must methodically monitor its detection portfolio, identify gaps, and prioritize detection development. In recent years, many enterprises have adopted MITRE ATT&CK® to track adversarial TTPs (tactics, techniques, and procedures), assess risks, and create mitigations.
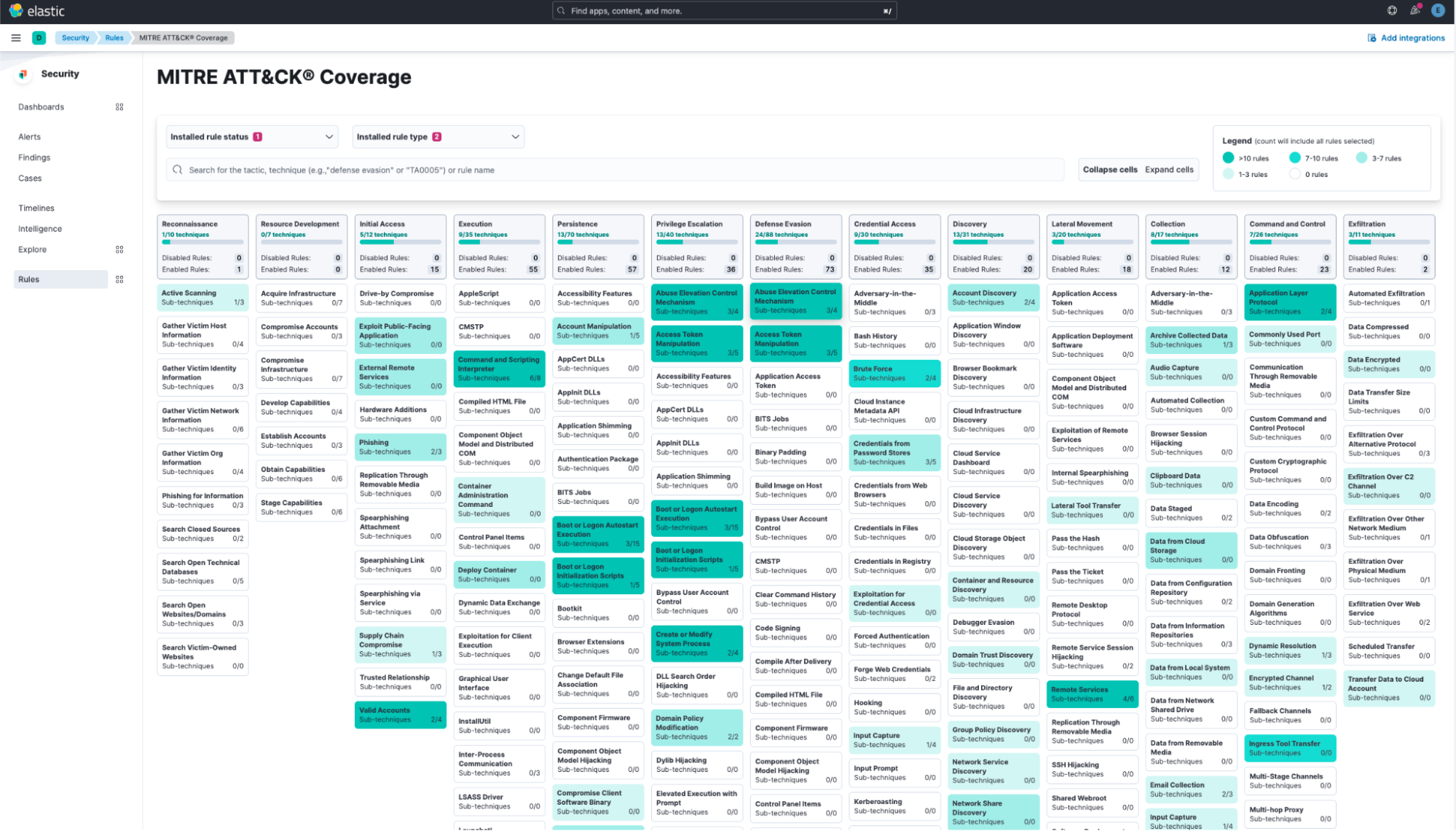
The new MITRE ATT&CK Coverage page in Elastic Security shows the coverage provided by prebuilt and custom rules across inventoried tactics and techniques, and helps practitioners address gaps using detections from Elastic Security Labs. Bringing this information into Elastic Security from GitHub makes it easier to understand and leverage.
Cloud security posture management, now for Google Cloud
Elastic Security 8.10 expands its cloud security posture management (CSPM) capabilities to cover Google Cloud. You can now assess and bolster the security posture of your GCP assets right from our platform.
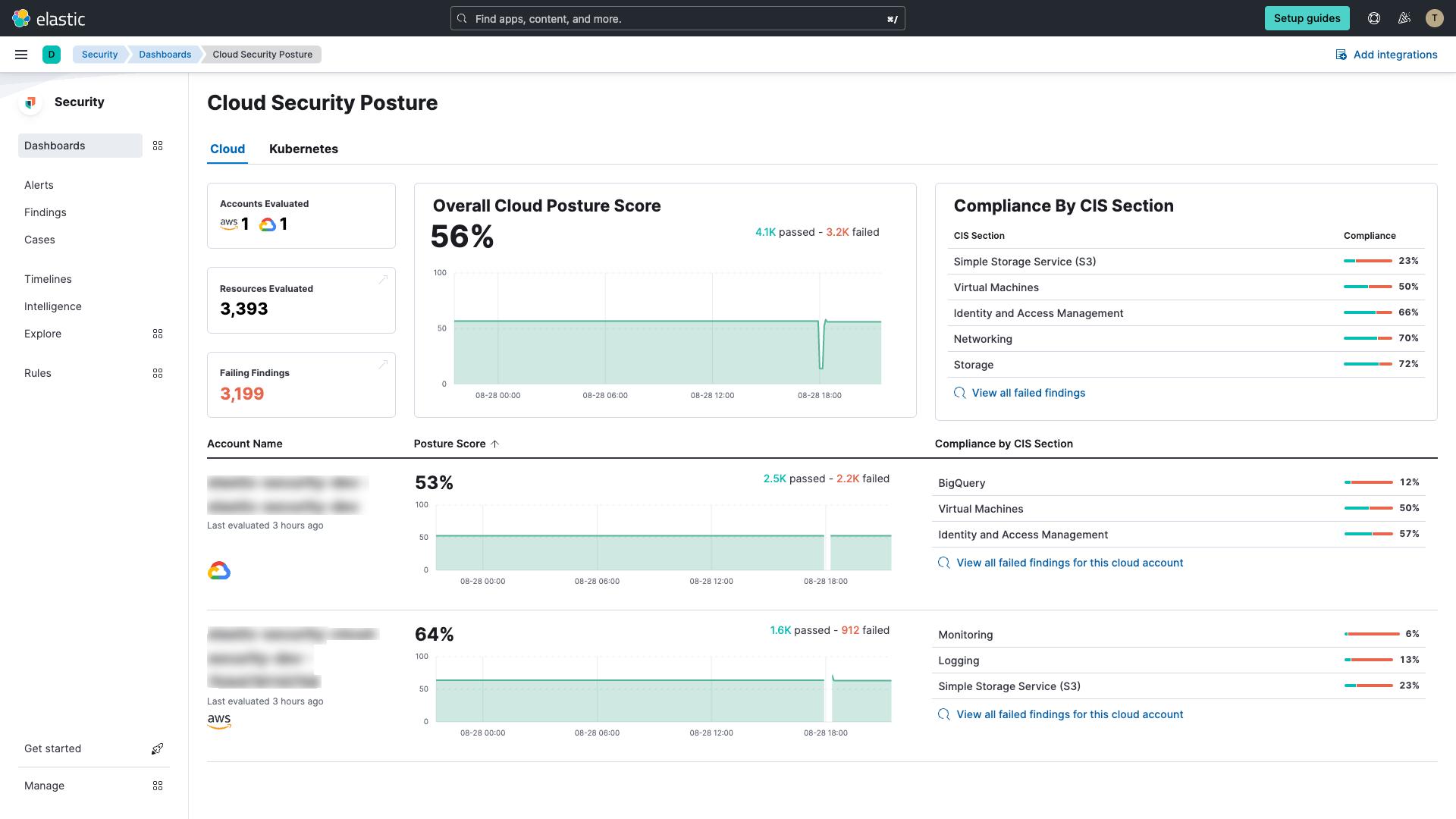
The best part? This gives you a bird's-eye view of your security posture across all of your multi-cloud environments, helping you grow and diversify your cloud strategy confidently and securely.
Automate CSPM onboarding across an AWS Organization
Elastic Security 8.10 simplifies the daunting task of managing the security posture of fast-changing cloud infrastructure. This release introduces automated onboarding into cloud security posture management (CSPM) for every account within an AWS Organization — including both longstanding accounts and new accounts added in the future. No more tedium, no more coverage gaps — just a clear, consolidated view of your entire cloud security posture.
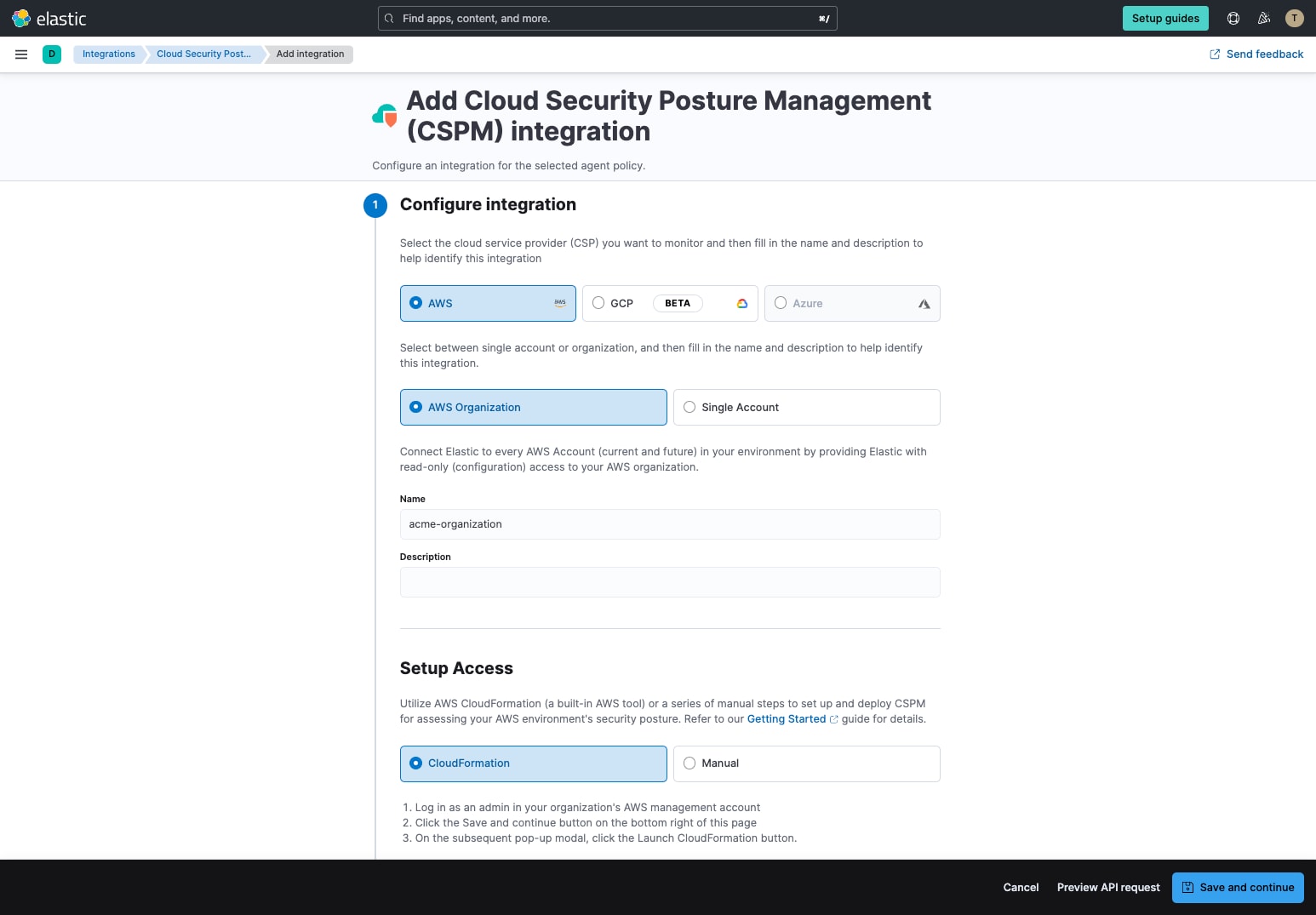
Further, a new integration with AWS CloudFormation pares a previously intricate onboarding process down to just a few clicks. With a comprehensive view of your security posture across all of your AWS accounts — both current and future — you can ensure that cloud assets are optimally configured to maintain the confidentiality, integrity, and availability of your data.
Try it out
Read about these capabilities and more in the Elastic Security release notes.
Existing Elastic Cloud customers can access many of these features directly from the Elastic Cloud console. Not leveraging Elastic on cloud? Start a free trial.
The release and timing of any features or functionality described in this post remain at Elastic's sole discretion. Any features or functionality not currently available may not be delivered on time or at all.