The endpoint tax is over: Elastic Security XDR

We are ending per-endpoint pricing. While AI-driven adversaries attack in minutes, choosing which assets to protect based on a price list is a liability. For years, the industry has forced security leaders to negotiate against themselves: You protect the laptops and servers you can afford and leave the rest vulnerable to stay within budget.
That compromise is no longer sustainable. At Elastic, we believe you should build your security strategy around your risk, not your license count. By eliminating the "endpoint tax,” our agentic security operations platform is enabling organizations to achieve total visibility and world-class prevention across their entire environment.
Prevention matters more than ever
Detection alone doesn’t cut it anymore. If you’re not stopping threats at the edge, you’re chasing them after the damage is done. AI has compressed the attack lifecycle, allowing adversaries to move laterally in minutes. Because these advanced attackers operate "below the surface" where user-mode tools can't reach, you need visibility and enforcement at the same level they operate.
To stop them, you have to meet them where they live: the kernel. Elastic Defend, Elastic’s native endpoint protection, provides the necessary kernel-level visibility. By working at the root of the operating system, we can detect and block threats like rootkits, direct kernel manipulation, and advanced persistence techniques before the first line of malicious code ever executes.
This isn’t about collecting more data. It’s about having the right vantage point to prevent attacks at their source.
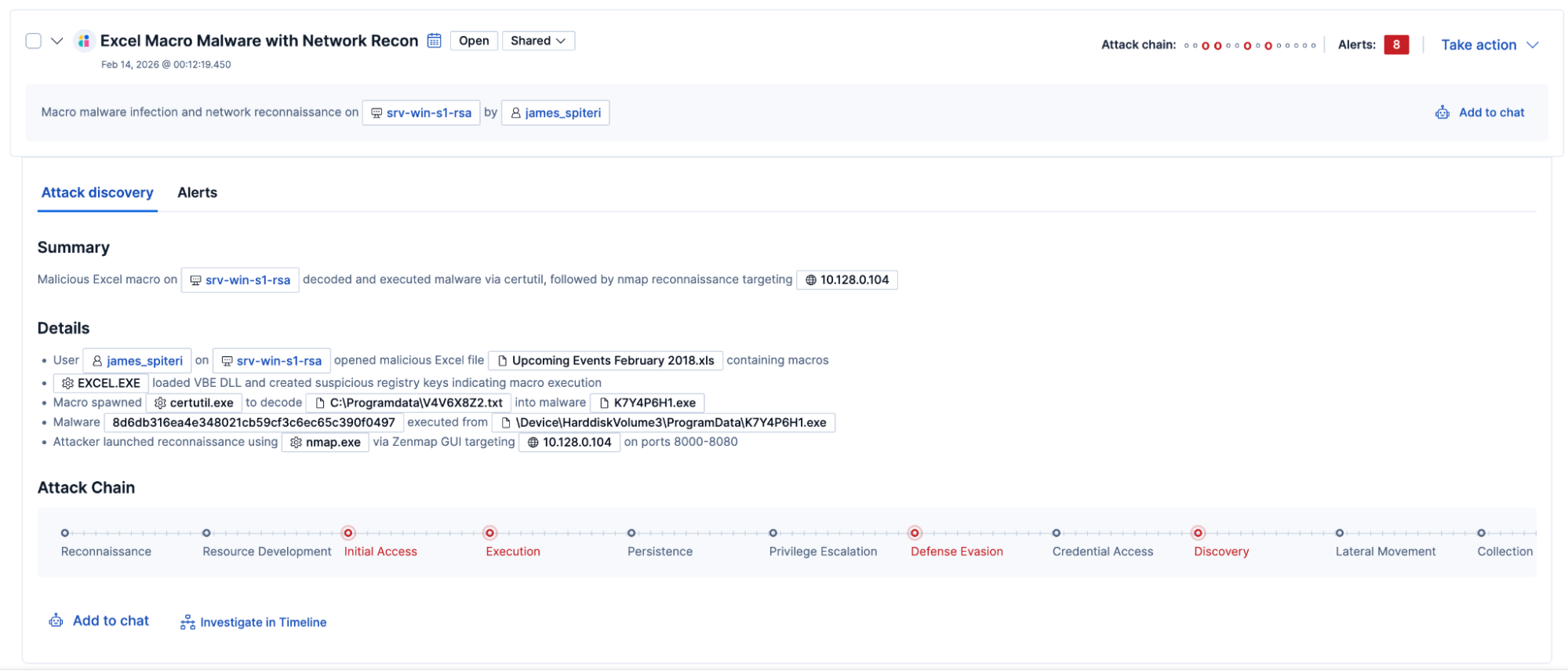
Context is what finds real attacks
Stopping attacks at the edge is only part of the story. To really catch advanced threats, you need context. But context requires scale, and most endpoint products are choking on the volume of data required for modern XDR. They lock your telemetry in a separate box, forcing your analysts to "swivel-chair" between consoles to manually stitch a story together.
Elastic is a data company with deep security DNA driven by AI. We don't just handle scale; we are built for it. We automatically correlate endpoint behavior with identity shifts, network traffic, and cloud logs. When an alert fires, the full narrative is already there. You get answers, not just more logs to sift through.
We eliminated the per-endpoint tax
Most EDR vendors still force a trade-off between coverage and cost. You protect the servers you can afford and leave the rest defenseless. That's not a security strategy; it's a liability.
Elastic Security XDR has no per-endpoint fees. You protect everything you need to protect. Security decisions get made on risk, not on what's left in a license budget.

Migrating our EDR to Elastic Defend was a 'flick of a button' experience. Since we already had Elastic Agent deployed, we activated our new security capabilities instantly through a Fleet policy. No pain, no complex rollout — just immediate protection.
Ben Collier, Security Engineering Lead, THG Ingenuity
Coverage that fits how you're actually built
Whether you need complete endpoint coverage across the enterprise, support for multiple endpoint agents, or a layered approach that extends your existing vendor, Elastic Security XDR works as the unified layer. All of it operates from a single console — no pivoting between platforms or manually stitching context across tools. And because endpoint telemetry flows directly into your SIEM, you also reduce the storage costs you're currently paying your existing endpoint vendor.
For unprotected assets, you can deploy Elastic Defend to instantly close coverage gaps with kernel-level prevention. But we also recognize that many enterprises run multiple tools. We don’t just ingest alerts from CrowdStrike, SentinelOne, or Microsoft Defender; we pull in their raw telemetry to provide the critical context that endpoint silos miss. This allows you to operationalize all your third-party data directly within Elastic. Whether it’s running advanced analytics or triggering remote responses like isolating hosts or killing processes, you can do it all without ever leaving the Elastic console.
Crucially, this protection isn't restricted by your infrastructure. Elastic can be deployed across cloud, hybrid, and on-premises environments (including fully air-gapped enclaves). We provide the same world-class protection for your most sensitive assets without forcing you into a cloud-native architecture.
Industry-validated endpoint efficacy
Our prevention-first approach isn’t just a claim; it’s independently validated. In 2025, Elastic was the only vendor to maintain a consistent 100% protection rate in AV-Comparatives' Real-World and Malware Tests for the entire year.
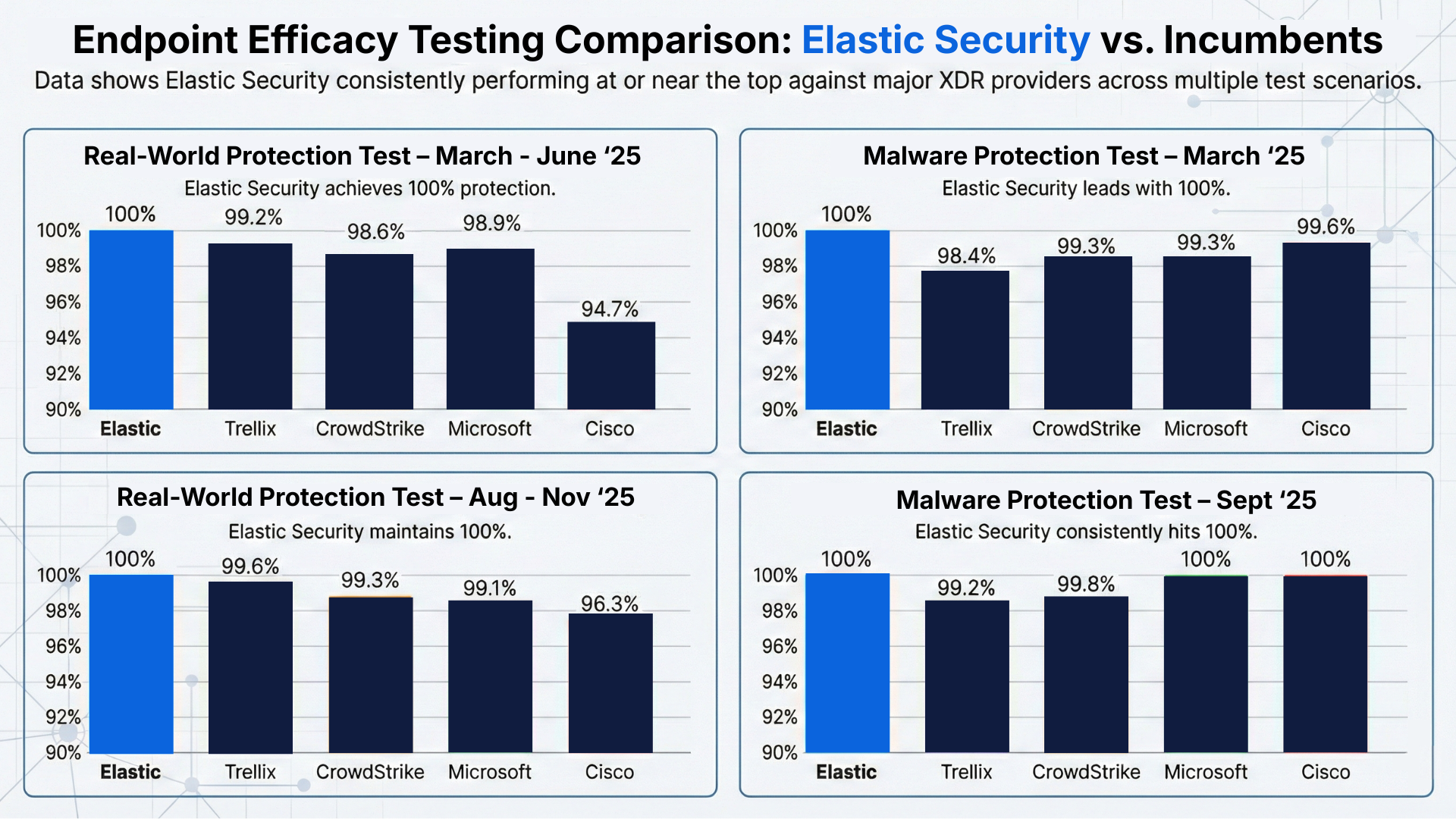
We followed this with a strong performance in the 2025 AV-Comparatives EPR Test, stopping 50 out of 50 advanced attack scenarios with zero workflow delays. This performance, combined with our unified licensing, is why IDC named Elastic a Leader in the IDC MarketScape: Worldwide Extended Detection and Response Software 2025 Vendor Assessment.
Native, agentic automation
We’ve integrated agentic AI and Elastic Workflows directly into the platform to move from alert to action in seconds. This isn't a separate SOAR tool; it is a native automation with direct access to endpoint telemetry and response actions. AI agents can autonomously reason through investigations and execute actions like querying reputation services, isolating hosts, or killing processes directly on the endpoint. By keeping the AI where the data lives, you eliminate the latency and credential overhead of third-party tools.
The bottom line
With Elastic, you can see everything, stop threats fast, and investigate incidents with confidence without paying per endpoint.
Our agentic security operations platform gives you kernel-level prevention, full endpoint visibility, and context across your environment. Alerts are correlated in real time, so your analysts spend less time pivoting between tools and more time stopping attacks. With Elastic, your security strategy is driven by risk, not license limits, letting you protect your entire environment without compromise.
What it costs
The quickest way to get started is with Elastic Cloud Serverless, a fully managed deployment priced on the volume of data you ingest and your retention period. You can use our pricing calculator for estimated costs.
If you need more control, you can deploy on Elastic Cloud Hosted (resource-based pricing) or self-managed infrastructure (node-based pricing).
Getting started
To get started, sign up for a free trial for Elastic Security, learn how to use Elastic Defend through our get-started video, or visit Oh My Malware to get hands-on with real malware samples.
The release and timing of any features or functionality described in this post remain at Elastic's sole discretion. Any features or functionality not currently available may not be delivered on time or at all.
In this blog post, we may have used or referred to third party generative AI tools, which are owned and operated by their respective owners. Elastic does not have any control over the third party tools and we have no responsibility or liability for their content, operation or use, nor for any loss or damage that may arise from your use of such tools. Please exercise caution when using AI tools with personal, sensitive or confidential information. Any data you submit may be used for AI training or other purposes. There is no guarantee that information you provide will be kept secure or confidential. You should familiarize yourself with the privacy practices and terms of use of any generative AI tools prior to use.
Elastic, Elasticsearch, and associated marks are trademarks, logos or registered trademarks of Elasticsearch B.V. in the United States and other countries. All other company and product names are trademarks, logos or registered trademarks of their respective owners.