After the alert: Rethinking how we investigate financial crime
Learn how Elastic helps financial institutions optimize investigation workflows, surface hidden patterns, and reduce time of investigation.

Summary
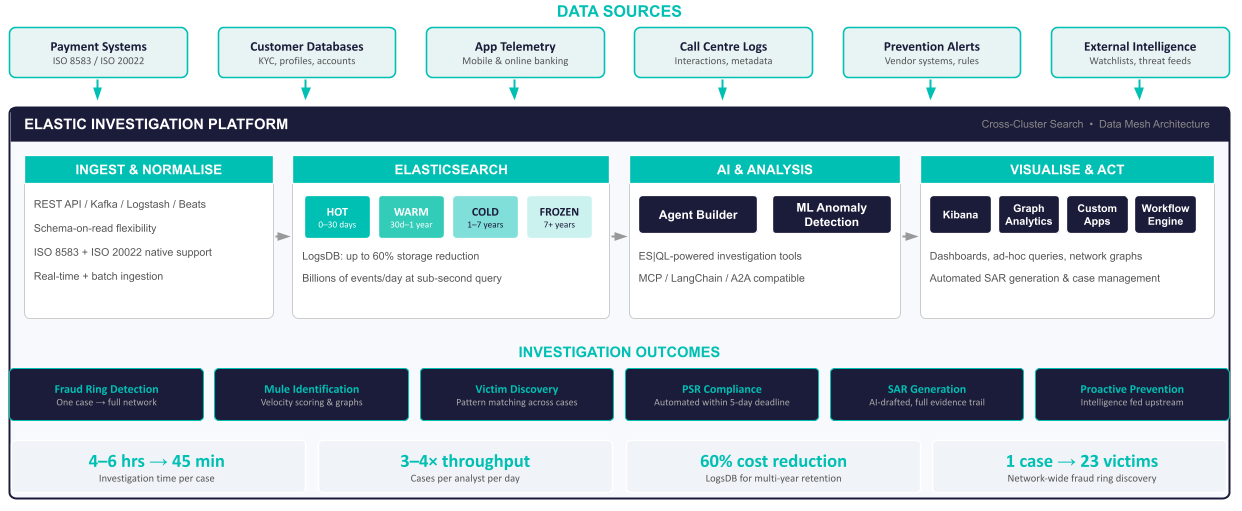
- Elastic provides AI-assisted fraud investigation that reduces case triage time for financial institutions.
- Cross-cluster search unifies transaction, telemetry, and customer data across teams without moving data.
- ES|QL and AI agents automate mule scoring, velocity analysis, and suspicious activity report generation.
- Elasticsearch logsdb index mode cuts storage costs by up to 60% for multi-year regulatory retention.
Financial services has invested heavily in fraud prevention. The industry stops the majority of attempted fraud before it reaches customers by leveraging real-time transaction monitoring, behavioral scoring, and device fingerprinting. In the UK alone, the industry prevented £870 million of attempted fraud in the first half of 2025, blocking 70 pence of every pound criminals tried to steal — but £629 million still got through.
That figure, drawn from UK Finance’s Half Year Fraud Report 2025,1 represents 2.1 million confirmed cases requiring investigation, triage, or reporting — a 17% increase year over year. The global picture is even starker; the Global Anti-Scam Alliance2 estimates worldwide scam losses at over $1 trillion annually.
Prevention systems are doing their job. The question facing fraud teams today is not how to build better walls, but what happens once someone gets over them? The investigation layer — the work that turns an alert into an outcome — is where the bottleneck sits.
And the cost of that bottleneck is rising. The UK’s Payment Systems Regulator now requires banks to reimburse Authorised Push Payment (APP) fraud victims within five working days, splitting liability 50/50 between sending and receiving institutions.3 With APP fraud reaching £257.5 million in H1 2025 alone, investigation speed now translates directly to balance sheet impact.
Closing the gap with Elastic
Elastic’s focus in the fraud space is on investigation and analytics — the work that happens after an alert fires, a customer reports a loss, or a suspicious pattern emerges. It operates as a system of intelligence alongside your systems of record, complementing existing prevention tools with the analytical depth needed to turn alerts into outcomes.
Several leading fraud prevention vendors already use Elasticsearch as part of their own infrastructure. For financial institutions already running Elastic for security, observability, or search, fraud investigation capabilities can be added to existing deployments or connected via cross-cluster search (CCS).
Making the investigation scalable with AI
With over two million cases4 in a single half-year and growing, investigation teams cannot scale through headcount alone. AI-assisted triage changes this equation. When an analyst receives a case, an AI agent can have already assessed the transaction against the customer’s behavioral baseline, scored the receiving account for suspicious characteristics, and surfaced similar cases. The analyst’s role shifts from data gathering to judgement, which is where human expertise adds the most value.
Elastic Agent Builder enables the creation of purpose-built investigation agents using Elasticsearch Query Language (ES|QL) queries packaged as tools like mule scoring, velocity analysis, layering detection, and Confirmation of Payee checks. Agents decide which tools to invoke based on case context and integrate with any large language model (LLM) through open standards, including vLLM, MCP, and agent-to-agent (A2A) protocols.
Bring the full data picture into the investigation
Fraud investigators need far more than transaction records; customer profiles, application telemetry, device metadata, call center logs, and external intelligence all carry investigative value. A payment that looks unremarkable in isolation might tell a very different story when combined with login behavior, device changes, or a pattern of recent customer service calls. In practice, much of this data sits unused, not because it lacks value but because different teams own different data sources — each behind its own access policies and technology constraints.
Elastic’s cross-cluster search capability addresses this directly: Transaction data stays in the banking cluster, application telemetry stays in the observability cluster, and investigators search across both in a single request with full role-based access controls (RBAC) and audit trails. Login patterns, device changes, session telemetry, and customer service interactions all become discoverable alongside payment records.
Query flexibly with ES|QL
ES|QL gives investigators the ability to explore data in ways that predefined dashboards cannot support. In real time, it can:
Filter transactions by velocity thresholds
Group by receiving account
Correlate payment timing with login behavior
Aggregate across millions of records to surface outliers
When combined with AI agents, ES|QL queries become the tools that power automated investigation while remaining available for ad-hoc, analyst-driven exploration in dashboards.
Automate compliance and reporting
Workflow automation orchestrates end-to-end processes from alert through case creation to suspicious activity report generation. AI agents can draft SARs with full narrative and evidence trails. Case management provides the unified audit trail required for Payment Systems Regulator (PSR) mandatory reimbursement within the five-day deadline.
Scale affordably
Elasticsearch logsdb index mode reduces storage costs by up to 60% for transaction data, making multi-year regulatory retention economically viable. Tiered storage from online to searchable archive automatically manages data lifecycles across seven years or more. Elastic handles billions of events and petabytes of data daily for security use cases worldwide; fraud investigation data volumes are well within its operating envelope.
The bottom line
The organizations that will manage fraud most effectively are not necessarily the ones with the best prevention walls. They are the ones with the fastest, most connected investigation capability behind those walls. The faster you can understand what happened, find related cases, and act on the findings, the better the outcome for victims, compliance, and the bottom line.
Elastic gives fraud teams the unified data platform and AI assistance to investigate at the speed the threat demands.
What’s next?
In part two of this blog series, we will walk through the technical architecture: the data model, ES|QL queries, and cross-cluster search configuration that power the platform. Part three will cover the AI agents and workflow automation in detail, illustrated with a worked investigation scenario.
Ready to explore Elastic for fraud investigation? Talk to our financial services team about a proof of concept with your data, an architecture review of your current fraud stack, or a strategic discussion on how Elastic fits your fraud roadmap.
Sources
1. UK Finance, Half Year Fraud Report 2025
2. Global Anti-Scam Alliance, Global State of Scams 2025 Report
3. UK Payment Systems Regulator, APP Fraud Reimbursement Policy (October 2024)
4. Following the Fraud: The Role of Money Mules
The release and timing of any features or functionality described in this post remain at Elastic's sole discretion. Any features or functionality not currently available may not be delivered on time or at all.