Elastic Security 7.10 equips the SOC to automate the detection and prioritization of complex threats across premises and cloud
Security teams need a growing amount of data, and to be able to analyze and perform automated detection across all of it, quickly and accurately. Modern threats require instant correlation across not only traditional security data, but also cloud infrastructure and application data, and years of historical data — for investigative work, hunting, threat profiling, and more. Security teams need to contextualize findings with threat and business context, pinpoint which issues are of the highest priority, and quickly find the best path to resolution.
 Elastic Security 7.10 delivers key new capabilities that drive greater SIEM value into the detection engine, enabling security teams to more easily detect complex threat behavior and move faster in addressing the most critical issues. With the release, security teams also gain out-of-the-box protection for multi-cloud hybrid IT environments, the ability to investigate and hunt across greater time spans, and enhancements to visibility and usability.
Elastic Security 7.10 delivers key new capabilities that drive greater SIEM value into the detection engine, enabling security teams to more easily detect complex threat behavior and move faster in addressing the most critical issues. With the release, security teams also gain out-of-the-box protection for multi-cloud hybrid IT environments, the ability to investigate and hunt across greater time spans, and enhancements to visibility and usability.
Lower MTTD and reduce alert fatigue with EQL Correlation and Indicator Match Rules
Correlation rules for high-fidelity, prioritized alerts
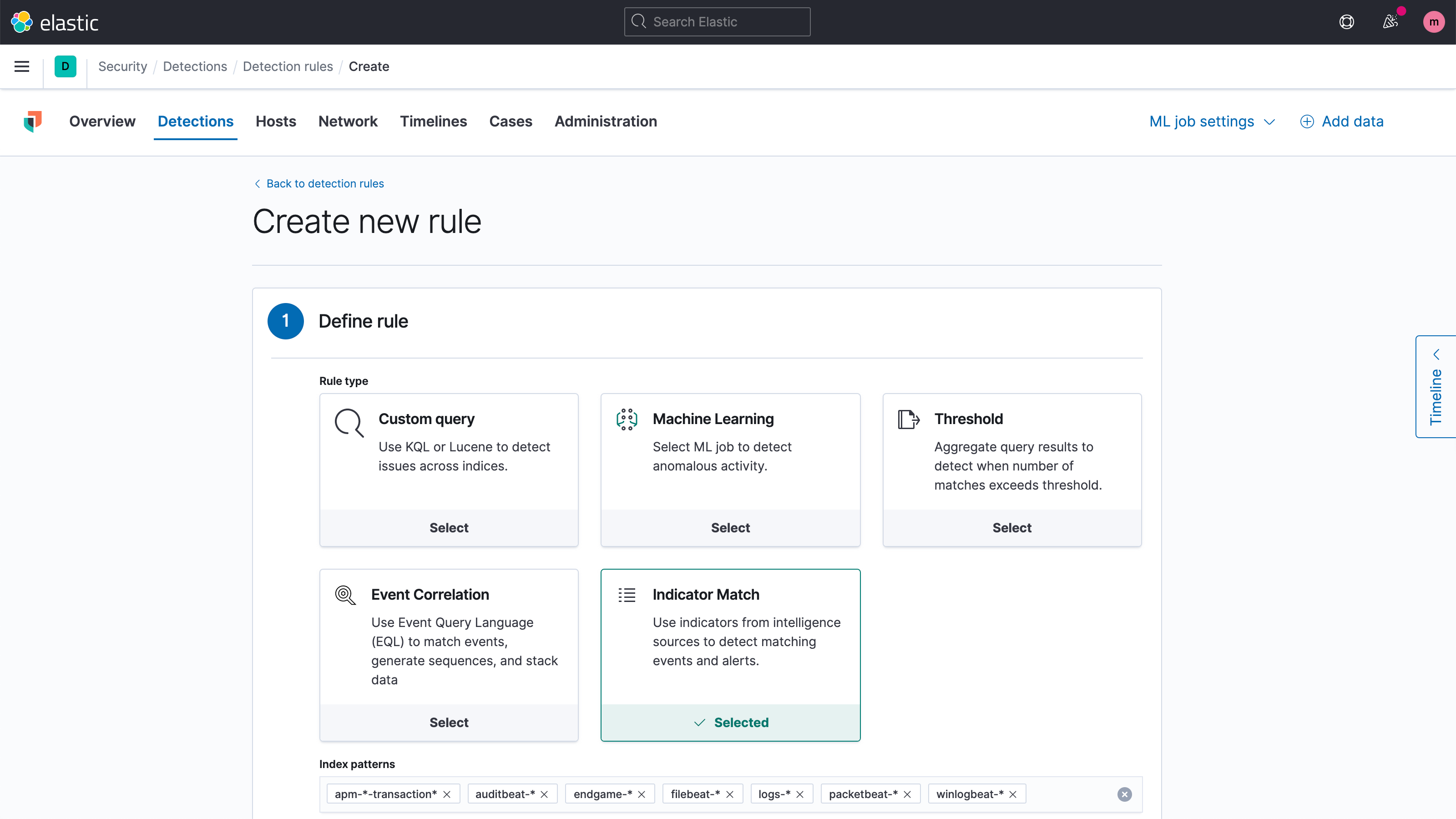
Automate detection of multi-stage attacks with the new “Event Correlation” rule type for the Elastic Security detection engine, which performs sequence-based analysis across multiple Elasticsearch indices. The result? More specific and sophisticated alerts, improving fidelity and providing vital context for analysts to identify and investigate attacks quickly. Correlation rules leverage Event Query Language (EQL), which enables security researchers and detection engineers to craft resilient rules that better identify attack behaviors, tactics, and techniques.
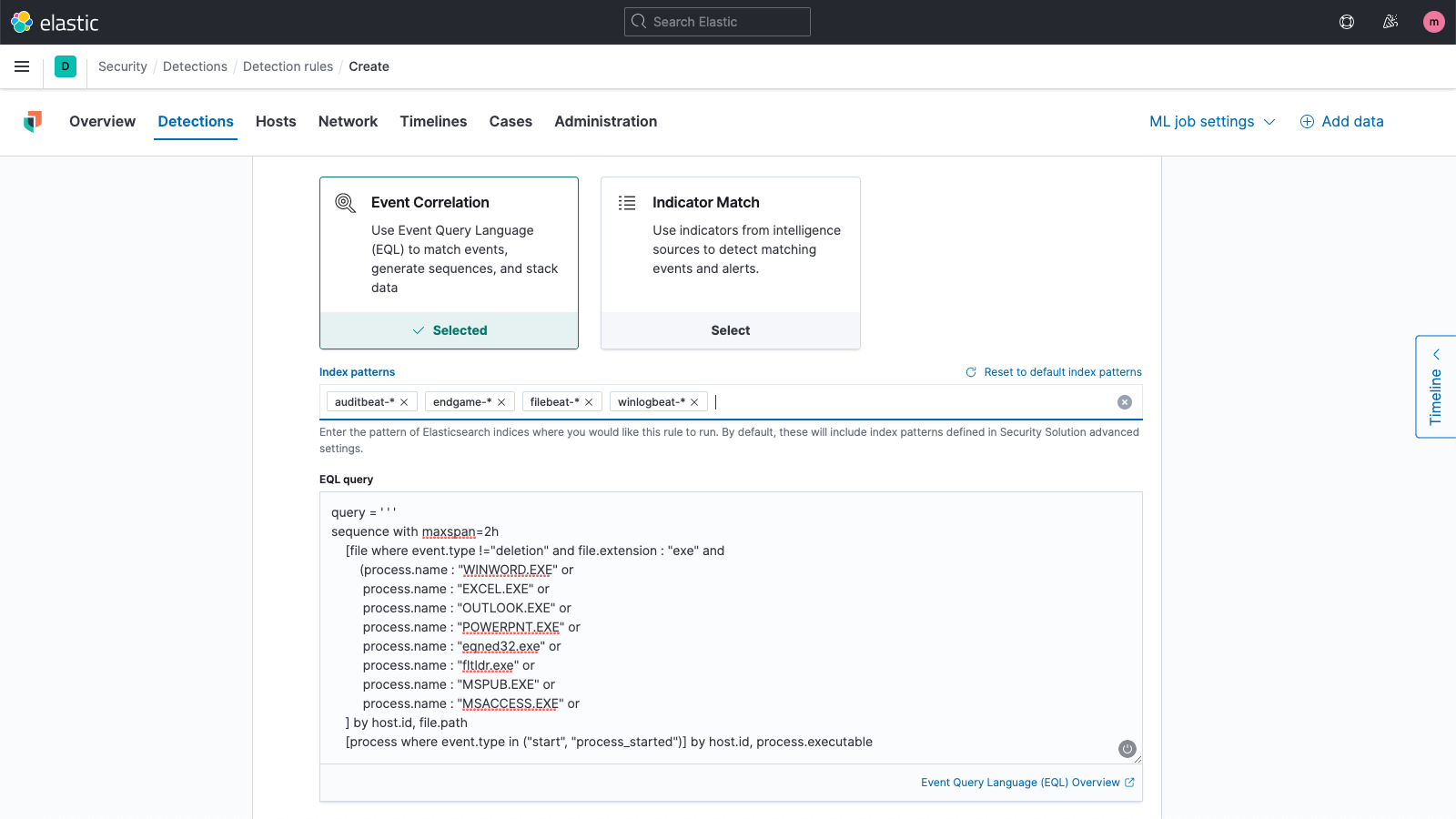
Context-aware detection rules
Generate alerts with rich context by automatically comparing events (streaming and stored) with threat indicators, high-value user accounts, asset management data, or any other dataset. Perform retrospective and real-time analysis against user-defined lists to gain critical security context, enhancing prioritization and accelerating response. This new rule type applies conditional logic to compare values in multiple indices, generating an alert upon finding a match. The severity and risk score of these generated alerts can be adjusted based on resulting indicator matches. Through correlation with alerts from indicator match rules, events involving critical assets, or high-risk users, and other sources of context, can be prioritized even higher.
Protect your infrastructure and users with prebuilt detections for Azure, Google Cloud, and Zoom
Azure and GCP detections
Our new release introduces prebuilt detection rules and machine learning jobs for Azure and GCP, supporting the detection of attack behavior categories like persistence, credential access, and discovery. Alongside the AWS detections packaged in our previous release, Elastic Security now delivers prebuilt detections for the world’s three largest cloud providers.
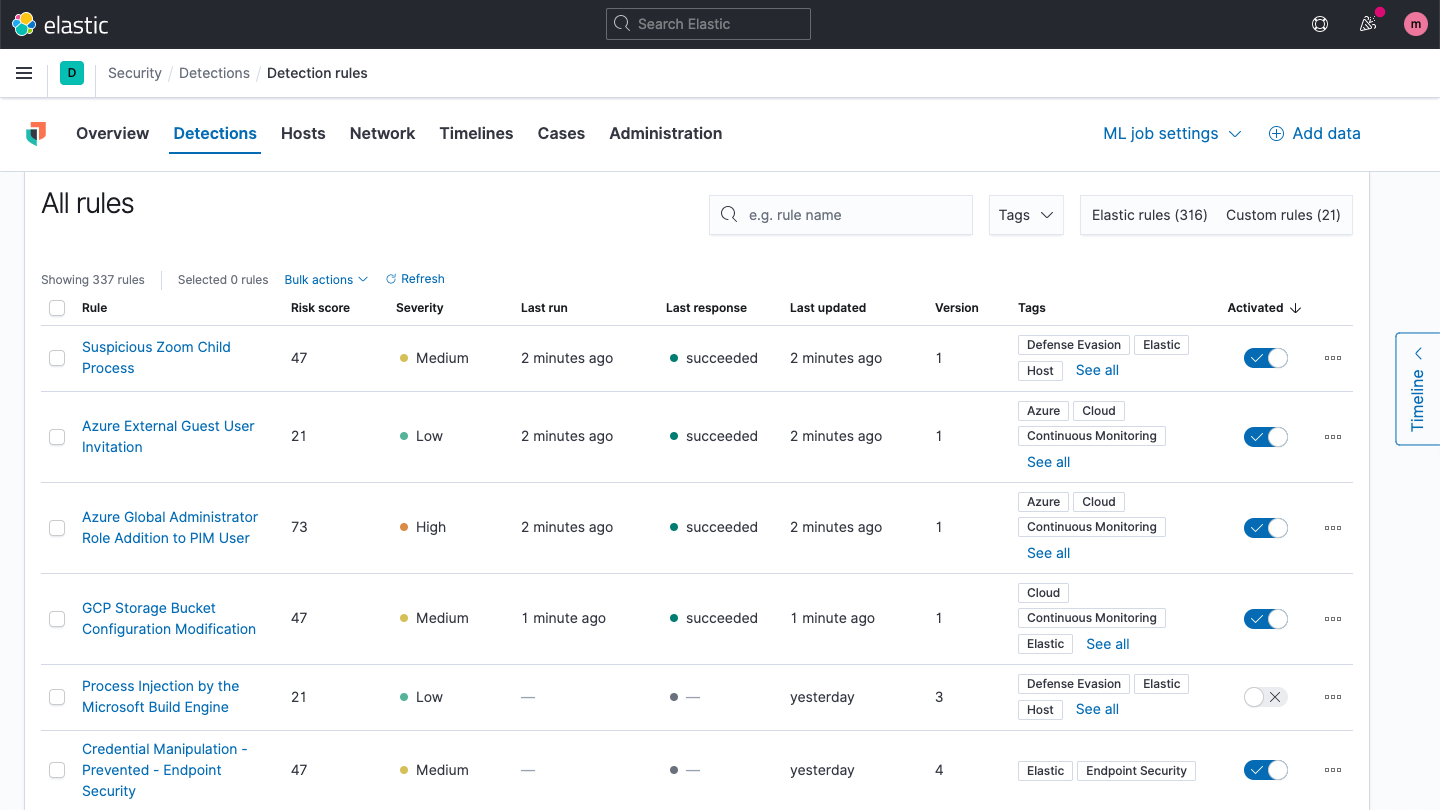
Zoom detections
Version 7.10 provides new detection rules to spot Zoom meetings configured without a passcode and detect child processes spawned by Zoom. This new content helps protect remote workers from opportunistic threat actors pursuing new vectors of attack.
Community-driven content development
Thank you to the members of the Elastic Security user community who help shape the development of the prebuilt detection rules through engagement on our public rules detection repo and ongoing discussions with our security researchers and content engineers. In addition to GitHub, you can find us on Slack.
Easily access years of security data on object stores like S3, with searchable snapshots
Collect and retain high-volume security-relevant data and apply it to any number of security tasks — hunting, investigation, forensic analysis, threat profiling, and adversary emulation. With searchable snapshots and new storage options that reduce costs while preserving searchability, data sources such as IDS, NetFlow, DNS, PCAP, and endpoint data can be kept operationally ready at greater scale. Cold tier options made possible by object stores like Amazon S3 enable organizations to implement their own long-term data retention strategies, improving cost efficiency and enabling continued analysis for threat hunting and security analytics.
Extend visibility across your attack surface with new data integrations
Cisco Umbrella integration
Elastic Security now ingests events from Cisco Umbrella, providing visibility into user activity and attempts to access potentially malicious domains. This new integration supports Umbrella proxy, cloud firewall, IP, and DNS logs, supporting use cases that are of particular importance to organizations experiencing increased remote work demands.
Microsoft 365 Defender integration
Elastic now collects incidents and supporting information flagged by M365 Defender from devices, email accounts and users. This information can be correlated with additional environmental data when threat hunting in Elastic Security. This M365 support expands our coverage of the M365 Security ecosystem, with support for Microsoft Defender for Endpoint (previously called Microsoft Defender Advanced Threat Protection) added in our previous release.
Session initiation protocol (SIP) integration
A new Packetbeat module supports the collection of session initiation protocol data. SIP data provides visibility into IP connections commonly used by video conferencing and voice calling services. Security teams collect SIP data to address various use cases, such as collecting call metadata to support the investigation of social engineering calls and monitoring for phone calls from numbers associated with malicious activity.
Zoom integration
Elastic Security now collects Zoom events, providing insight into how meetings are configured. For example, meetings with no passwords provide opportunities for Zoombombing, the unwanted, disruptive intrusion, generally by Internet trolls and hackers, into a video conference call. Further, Elastic Security 7.10 also provides new detection rules to spot nefarious activity.
Juniper SRX integration
This new integration provides insight into system, traffic, and security events generated by SRX-series firewalls. In our 7.9 release, Elastic Security introduced support for Junos OS-based devices.
Another new set of data sources for Elastic Agent
Elastic Agent now collects several data sources that previously required Filebeat or Winlogbeat: Palo Alto, Office 365, Okta, Suricata, Zeek, Windows Security Events, PowerShell, Sysmon, and more. This expanded data source support brings Elastic Agent closer to enabling organizations to perform collection and prevent malware with a single agent.
Experimental data integrations
Elastic Security 7.10 introduces several new experimental integrations, available as both Filebeat modules and Elastic Agent packages. As experimental modules, these integrations will likely evolve, so breaking changes may occur. Trying them out and have feedback? Tell us what you think on Slack or in our discussion forums.
| Source | Description | |------------------------------------|--------------------------| | Barracuda Spam Firewall | Firewall | | Cisco Meraki | Managed LAN | | Citrix Netscaler | Application delivery | | CyberArk | Privileged access management | | F5 BIG-IP Access Policy Manager | Access control | | Fortinet FortiMail | Email security | | Fortinet FortiManager | Network management | | Juniper NetScreen | Network security | | Proofpoint Email Security | Email security | | Snort IDS | Intrusion detection system | | Sophos UTM | Unified threat management | | Symantec Endpoint Protection | Endpoint protection |
ECS 1.6 support
All security integrations have been updated to use Elastic Common Schema 1.6, which adds support for several new data fields.
Respond faster with continued refinements to Elastic Security
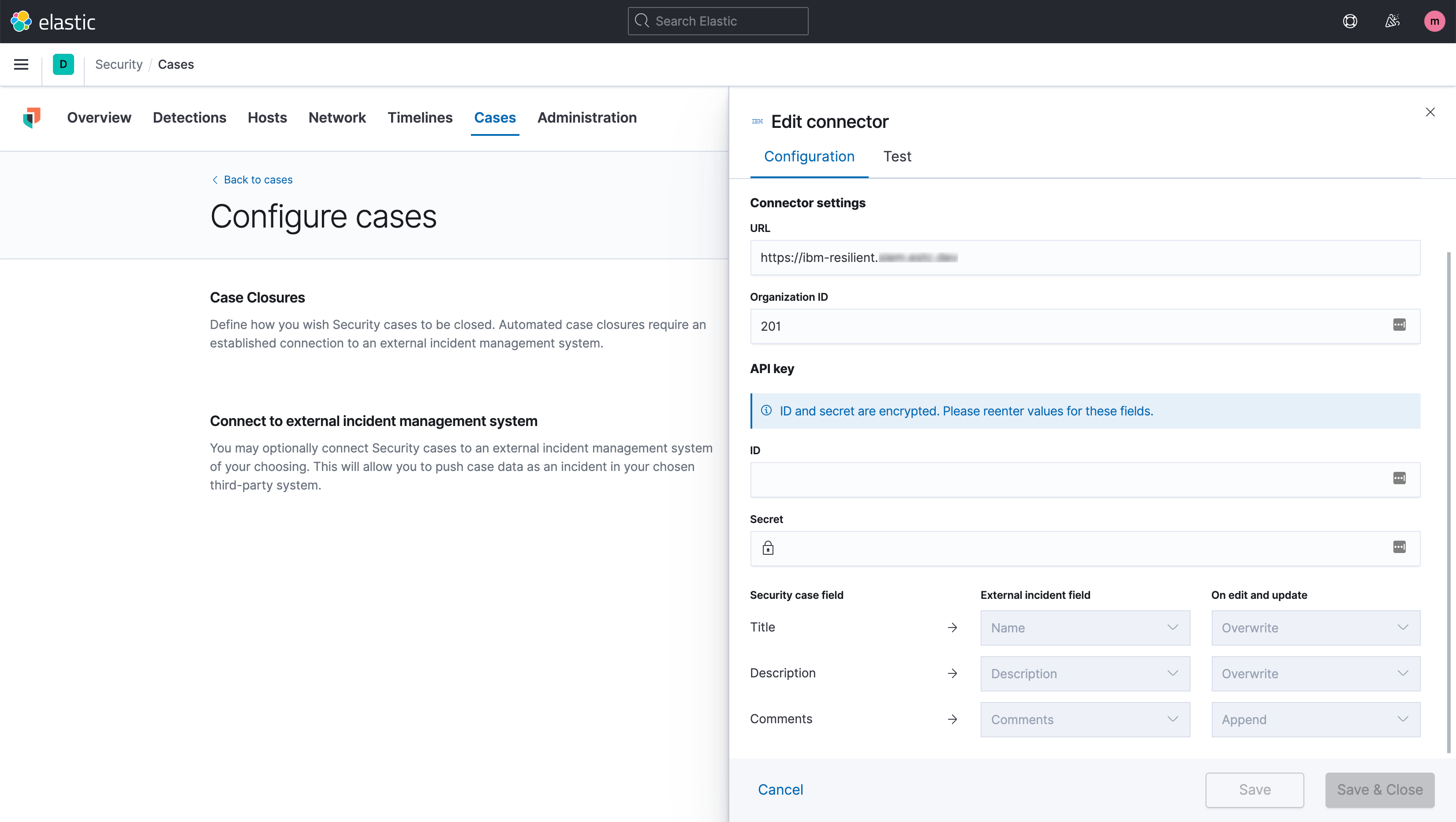
Deeper case workflow integrations
Improve handoff to third-party ticketing and SOAR tools by configuring how Elastic Security case information is forwarded. Elastic Security automatically queries the third-party system for available fields, streamlining updates.
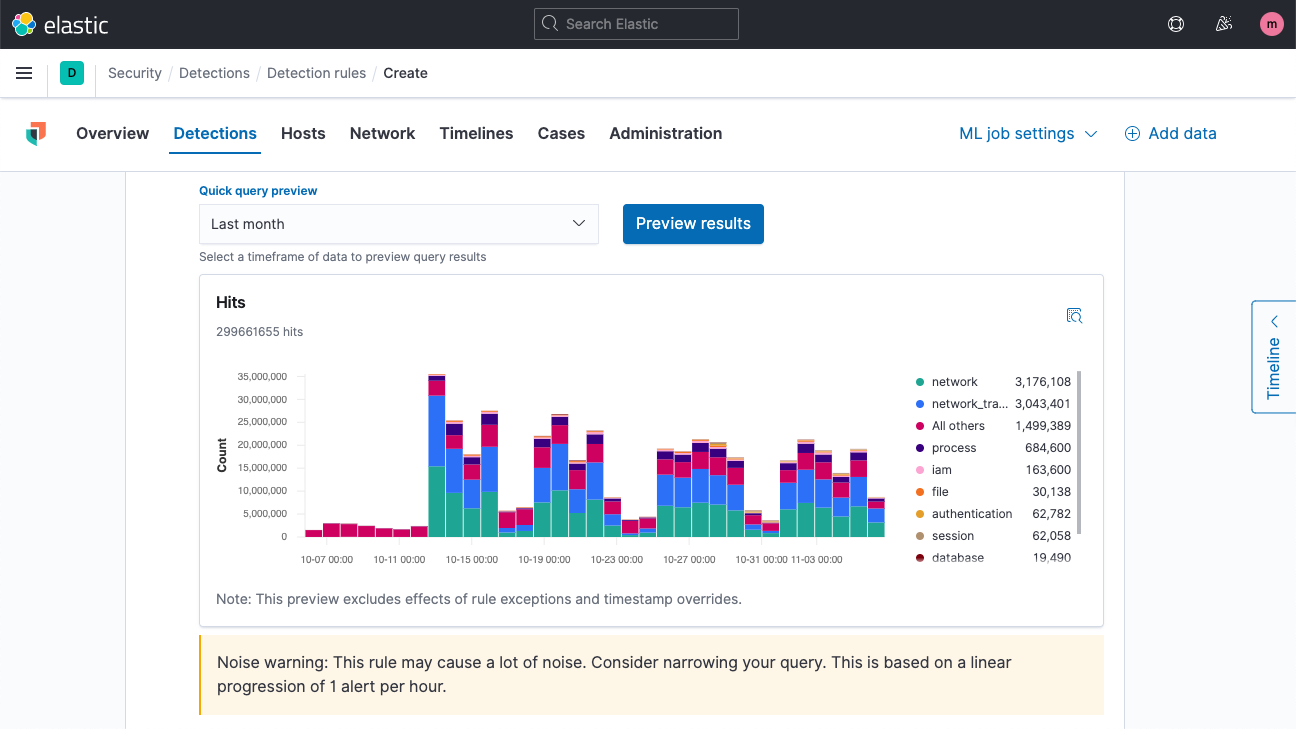
Quick rule query preview
Honing a query for a detection rule is faster than ever with a simple new way to perform backtesting on a new rule, showing how many alerts it would have generated over a preceding period. This new feature streamlines the creation of effective rules by making it easy for analysts to see when they’re on track with Custom query, Threshold, and Event correlation rules — no more rules that generate zero results...or millions.
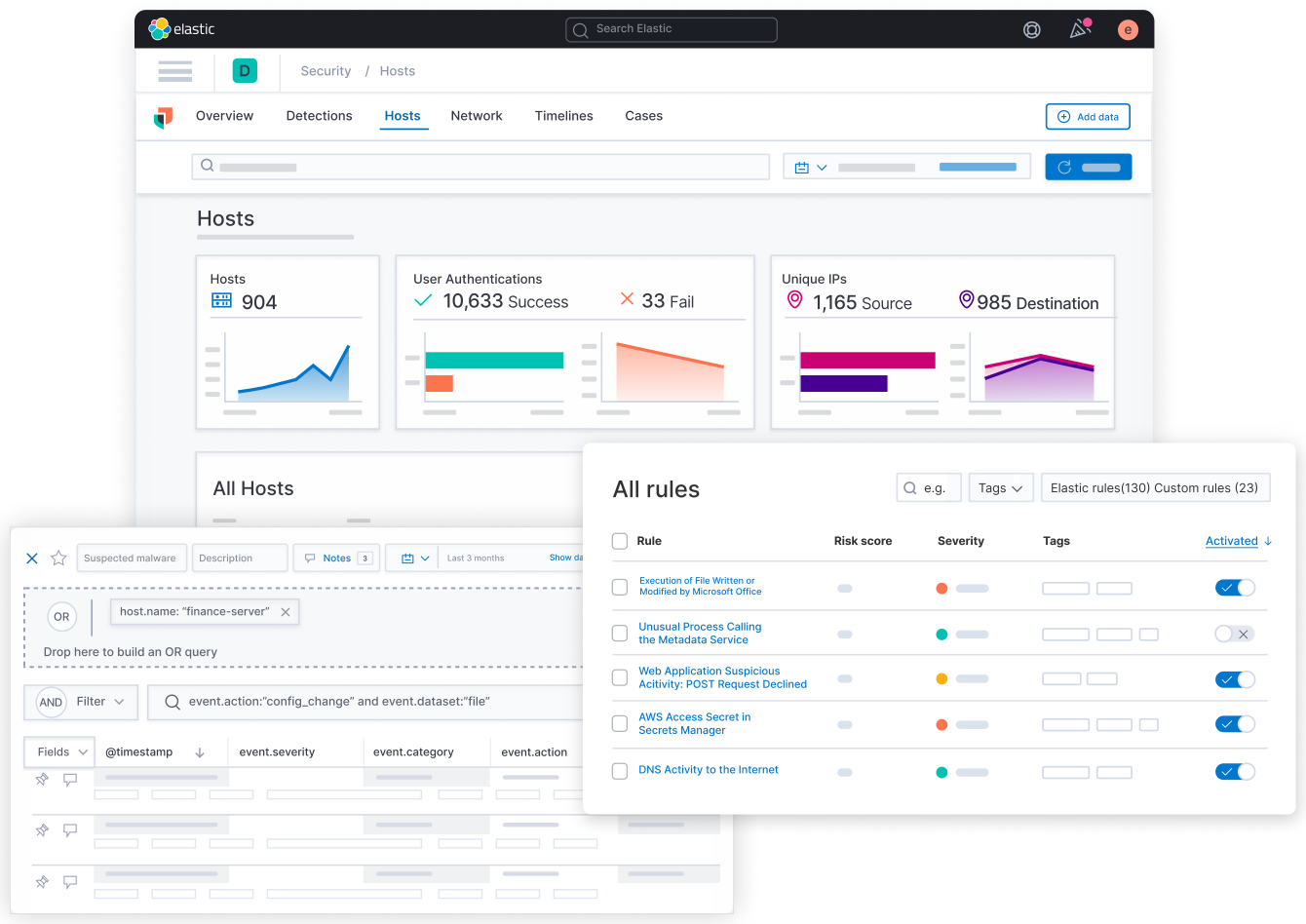
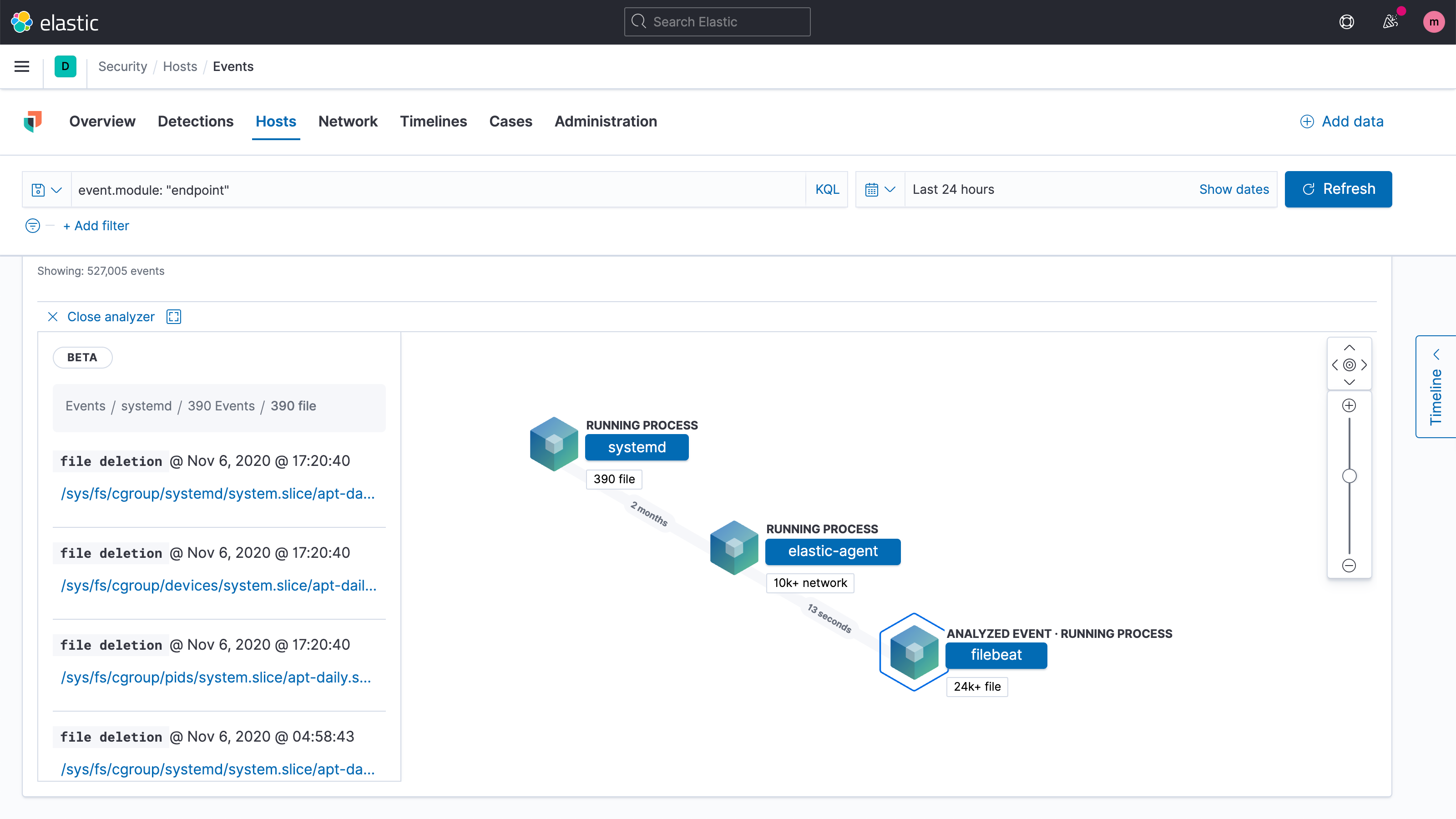
Enhanced host investigation UI
Enhancements to the interactive process tree visualization in the Analyze event view provides an enhanced understanding of process events, streamlining event triage workflows and shortening MTTR.
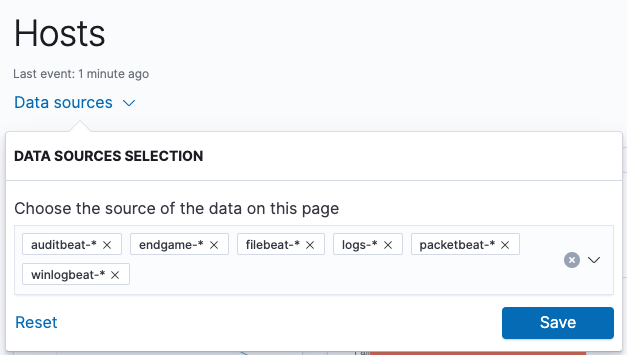
Index pattern-based data filtering
In many of the places where Elastic Security presents data, analysts now have the ability to customize the indices from which data is retrieved, enabling faster pivoting and drill-down, particularly for analysts working in large environments.
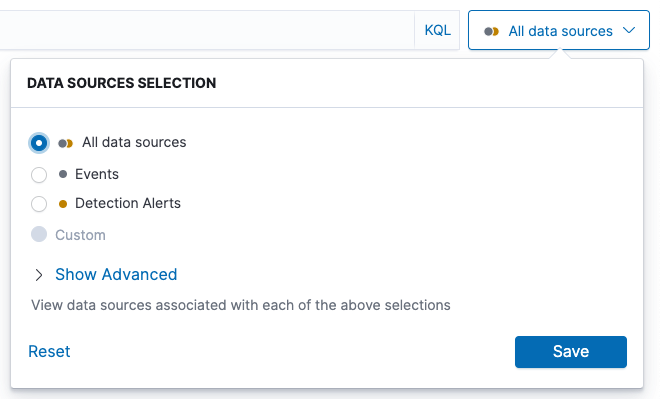
The same flexibility described above is provided in Timeline, which now allows users to choose certain index patterns for display.
Simplify malware prevention
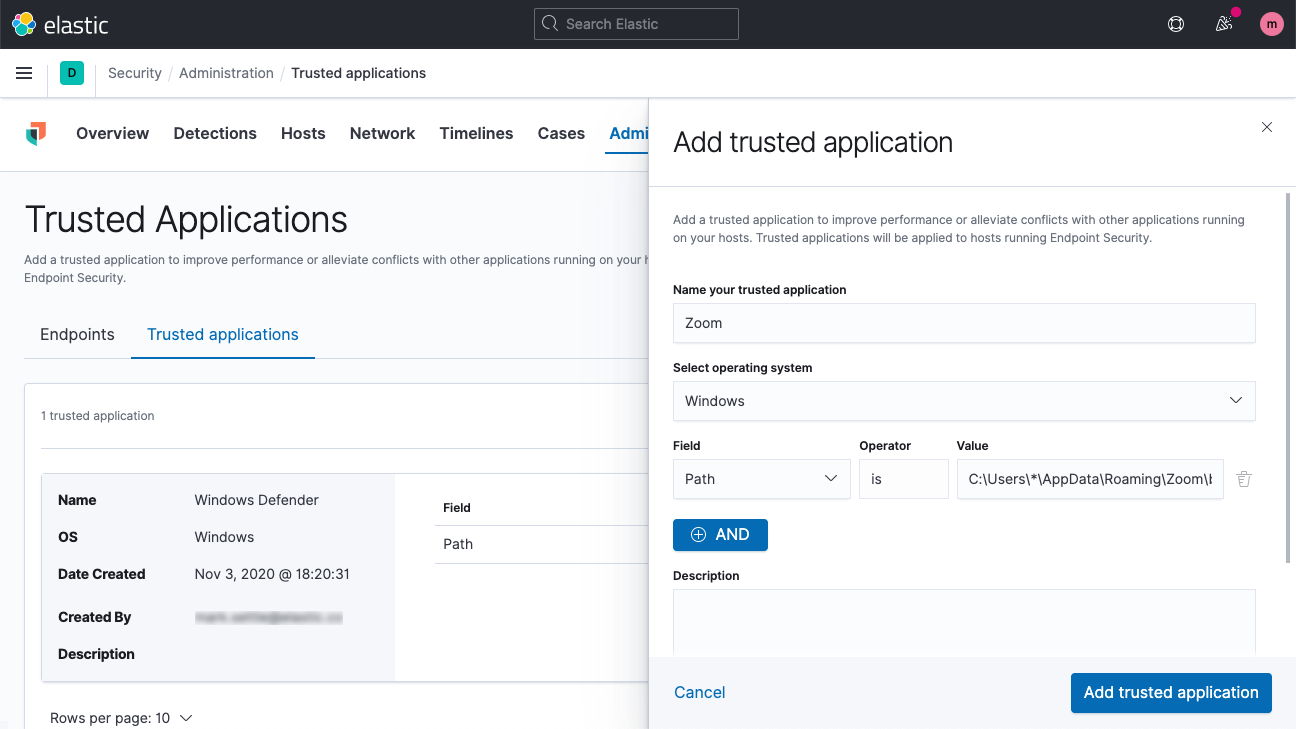
Trusted applications
Malware prevention on Elastic Agent now provides users the flexibility to mark certain applications as “trusted.” Applying this designation stops Elastic Security from tracking or blocking actions by specified applications, eliminating compatibility issues and increasing scalability.
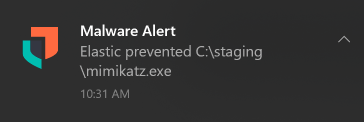
Malware prevention notifications for end users
The endpoint security package for Elastic Agent now notifies users when malware is blocked on Windows and macOS hosts.
Further endpoint enhancements
- Richer endpoint data available for forensic analysis, with new ECS 1.6 fields
- Faster fleet management, with new ways to filter and sort your hosts list
- Streamlined agent installation, enrollment, malware prevention rollout
Give Elastic Security 7.10 a spin
Want to give Elastic Security a spin? Experience all that 7.10 has to offer on Elastic Cloud, or check out an Elastic Security demo. Already have ECS-formatted data in Elasticsearch? Just upgrade to 7.10 of the Elastic Stack to start detecting and responding.
Want to see it in action? Watch the best sessions from our recent ElasticON Security virtual event.