Leveling up Elastic Cloud security: Introduction to role-based access control

Did you know that you can assign roles to users to implement fine-grained control for your Elastic® Cloud organization and deployments?
Role-based access control (RBAC) is a cloud security best practice that is considered a standard feature in enterprise software, as it provides a structured way to manage access to cloud resources. Within an RBAC framework, roles are a vital construct for grouping, organizing, and delegating permissions to different users. These roles provide a consistent way to manage and clarify user access and minimize the risk of errors or oversights.
By assigning roles to users, organizations can ensure that each user has access only to the resources they need to perform their job, while also limiting the risk of unauthorized access to sensitive information or functionalities. Role assignment also applies to API keys, which can be considered “machine users” that enable automation via API calls.
Elastic Cloud roles and use cases
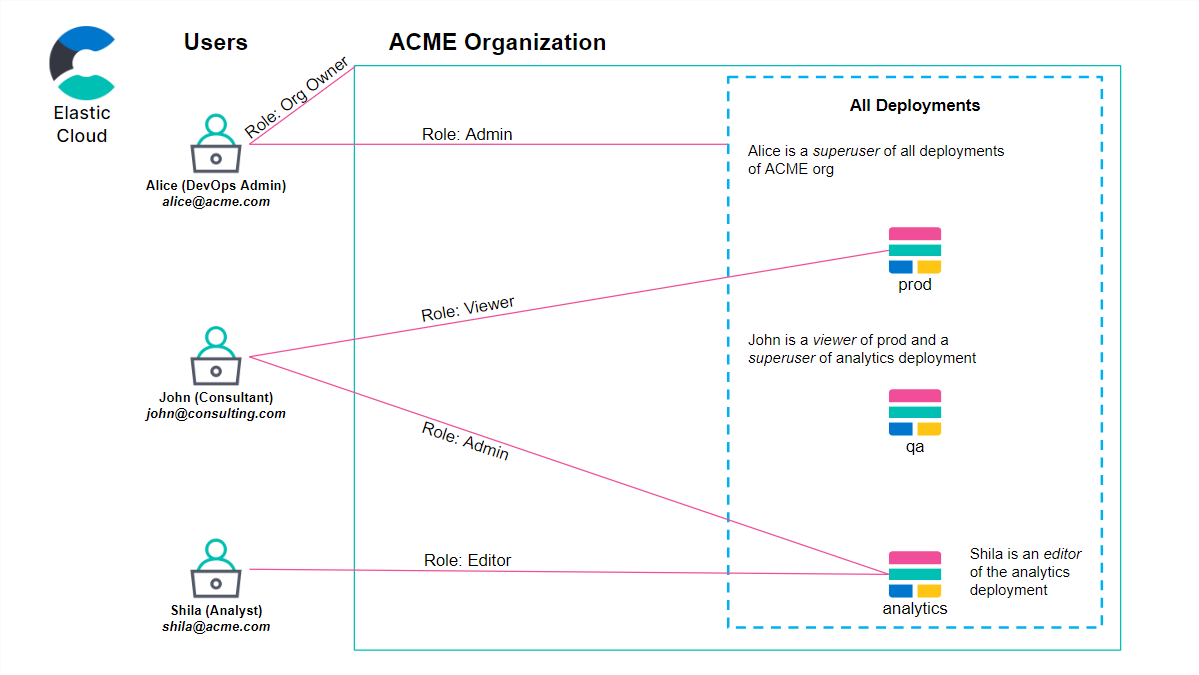
Within an Elastic Cloud organization, users and API keys can have one or more roles and each role grants specific privileges. Depending on the role type, a role can be assigned at an organization-wide level or at a deployment level. Deployment-level roles control access either to all deployments or a specific deployment.
When logging into a deployment, a user’s Elastic Cloud role dictates what permissions the user has based on an Elastic Stack role mapping. This mapping allows for centralized control over resource access for the Elastic Cloud platform and deployment applications through a single role. The following image shows some real-life examples of Elastic Cloud roles as they map to deployments inside an Organization.
The standard Elastic Cloud roles are as follows:
- Organization owner: This role is assigned by default to the person who created the organization; typically, it should be assigned to system administrators of your Elastic Cloud environment. This role provides complete control of deployments, organization-level details and properties, security privileges such as role management, as well as billing and subscription management. Organization owners log in to deployments with the superuser stack role privileges.
- Billing admin: This role allows managing an organization’s billing details such as credit card information, subscription, and invoice history. Billing admins cannot manage other organization or deployment-level details and properties or sign in to deployments. Budget holders or financial teams are the typical users associated with the Billing admin role.
- Admin: This role is reserved for Elastic Cloud deployment administrators. It grants access to all deployment details, properties, and security privileges. Like Organization owners, Admins log in to deployments with superuser stack role privileges. This role can apply to one or more deployments.
- Editor: This role has the same rights as Admin except for deployment creation and management of security privileges and is able to sign in to the deployment with the editor stack role. Editor applies to one or more deployments and is usually suited for IT professionals working with the Elastic Stack.
- Viewer: This role only allows users to view deployment details and interact with them but provides no edit access, so it can be assigned to members of your team requiring read-only access. The viewer role applies to one or more deployments.
How to manage roles in Elastic Cloud
To get started, go to your avatar in the upper right corner of the Cloud console, and choose Organization to open the Organization management page.
From the Members tab, you can manage roles for users, and you can edit the roles of API keys from the API Keys tab. Select the user/API key you want to edit, or click Edit under Actions to open the role management page:
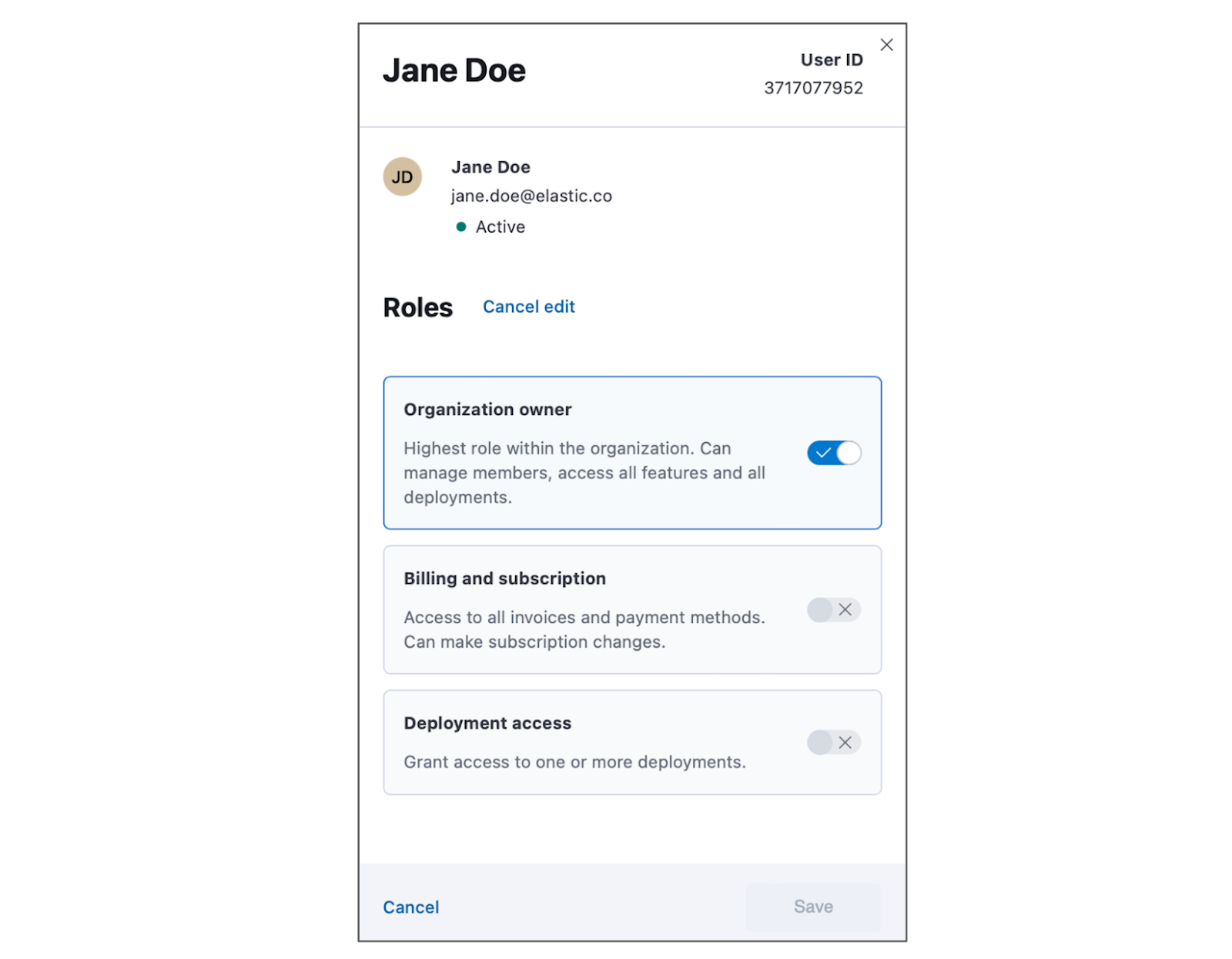
Select the appropriate roles for the user/API key and click Save. Changes will take effect immediately.
Learn more
You can learn more about Elastic Cloud RBAC in the product documentation. If you are ready to assign roles, you can log in to your Elastic deployment, navigate to the Organization page, select your users or API Keys, and manage their roles.
The release and timing of any features or functionality described in this post remain at Elastic's sole discretion. Any features or functionality not currently available may not be delivered on time or at all.