Elastic Security: Building the future of Limitless XDR

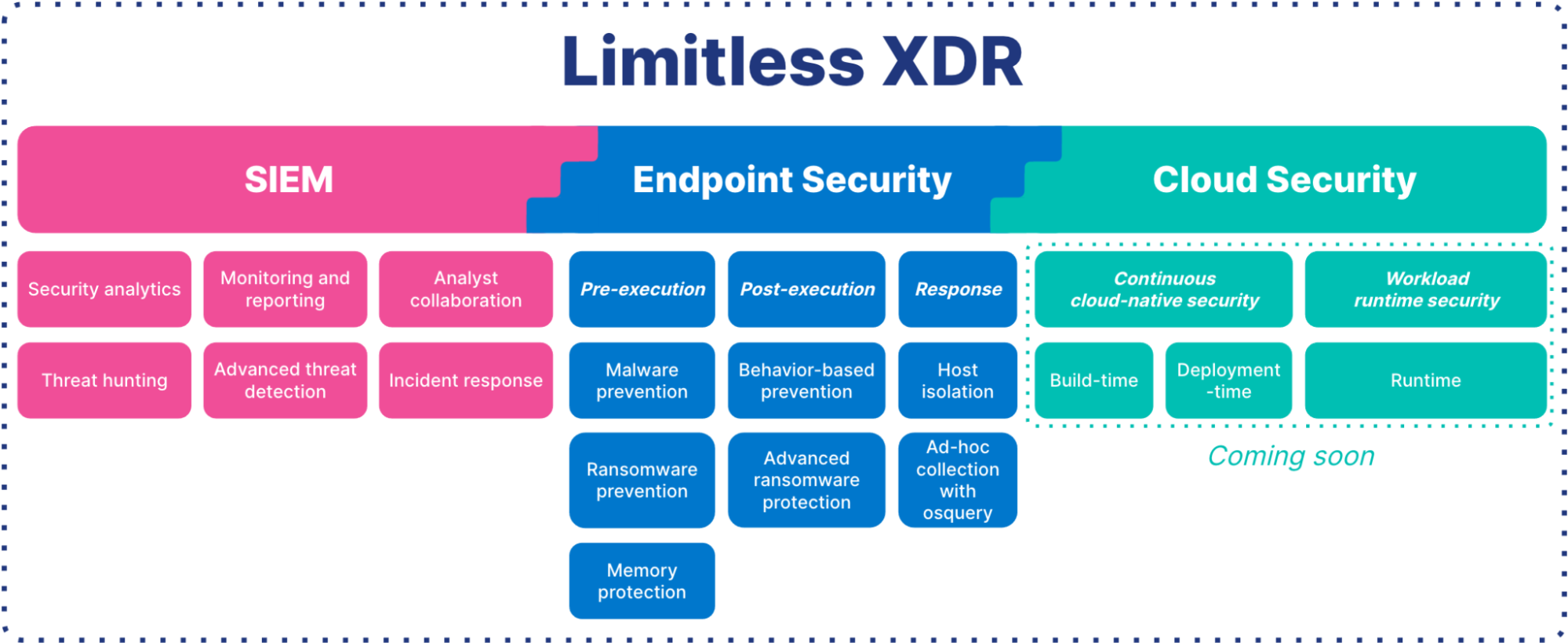
At ElasticON Global 2021, the team behind Elastic Security shared how we’re building the future of Limitless XDR (Extended Detection & Response) by unifying the capabilities of SIEM, endpoint security, and cloud security.
With Limitless XDR, practitioners can prevent, detect, and respond to the threats of today and tomorrow. It helps organizations advance security maturity by enabling proactive threat hunting and continuous detection across the attack surface, streamlining response with automation and access to years of historical data, and stopping threats right at the endpoint.
Let’s explore the top themes addressed at our ElasticON Global Security keynote.
Defense in depth, with SIEM and security analytics
SIEM is the backbone of our Limitless XDR solution, enabling detection and response across your attack surface. Our keynote explored how Elastic Security accelerates security operations, with real-world scenarios demonstrating advanced threat detection, proactive threat hunting, comprehensive monitoring and reporting, and collaborative incident response — all with an intuitive and lightning-fast analyst UI.
Powering security analytics — at scale, on any dataset — is core to what differentiates Elastic Security. In a snap, analysts can analyze hundreds of terabytes of data retained on inexpensive object stores (e.g., Amazon S3, Microsoft Azure Storage, Google Cloud Storage, and even on-prem with technologies like MinIO) — removing economic and technical barriers. See it in action in the keynote.
We’re rapidly extending the capabilities of our SIEM solution, and we have a huge vision — with advancements in machine learning (ML)-powered analyst insights, entity analytics, and advanced attack detection use cases all on the horizon.
Prevent, collect, and respond on every endpoint
No XDR solution is complete without the ability to prevent, detect, and respond to threats at the endpoint. Elastic extends endpoint security with prevention and detection in depth, universal data collection for cross-environment analysis, remote host inspection, and distributed response.
Endpoint prevention: With pre-execution ransomware prevention, malware prevention, memory protection, and multiple layers of run-time prevention against advanced threats, Elastic Security stops attacks right at the endpoint.
Endpoint detection and response: Elastic Security delivers prebuilt, MITRE ATT&CK®-aligned behavior protections to spot attackers who’ve made it past the perimeter. An integration with osquery collects rich host data to accelerate triage, and users can invoke remote response actions like host isolation on any OS to streamline response.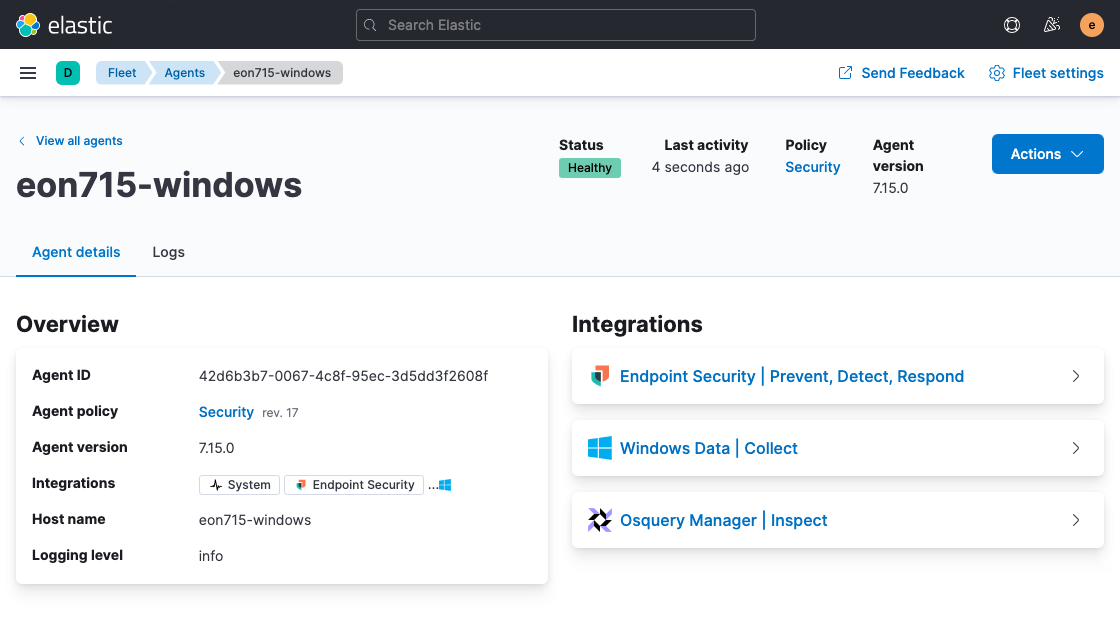
And there's even more to come for endpoint security. We intend to deliver Kernel-level endpoint visibility — not just for desktops, laptops, and servers of every operating system, but also for common infrastructure and cloud workloads, containerized workloads, and serverless workloads.
We’ll also further advance our extended prevention and detection, developing new ways to stop advanced attacks and techniques like novel ransomware, in-memory attacks, and credential theft. Finally, we’re extending endpoint response with automated rollback, plus capabilities across file, process, and registry operations.
Shifting cloud security left never felt so right
To protect organizations everywhere they operate, we have joined forces with two strong teams focused on cloud security. The advanced capabilities that they are building into Elastic Security will help users mature their cloud security protections from build-time, to deployment-time, to runtime.
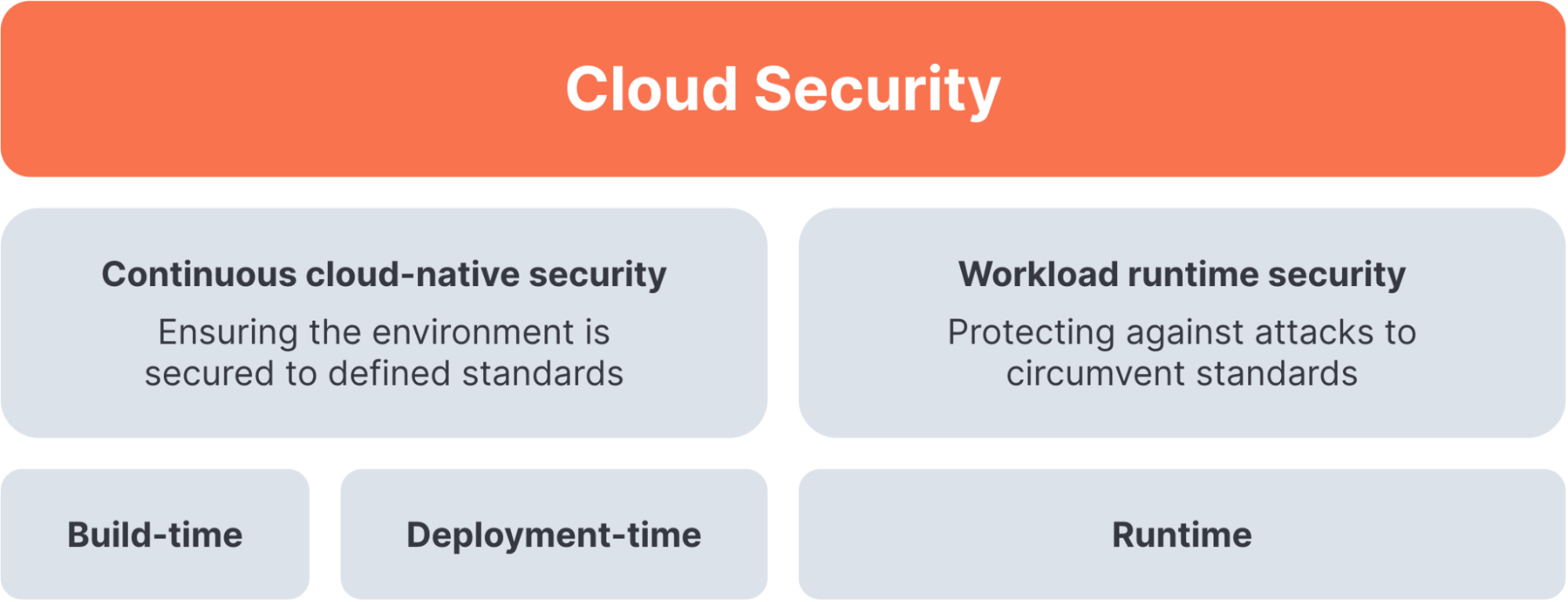
Adding the cloud security posture management (CSPM) capabilities of build.security into Elastic Security will enable organizations to monitor and analyze the development and deployment of cloud applications, elevating security and ensuring compliance with organizational policies.
We’re also accelerating our efforts in cloud workload protection platform (CWPP) through our acquisition of Cmd. Once a part of Elastic Security, these capabilities will enable organizations to detect, prevent, and respond to attacks against cloud workloads. The Cmd product embraces a developer-first approach, delivering experiences that all practitioners — from developers to operations, DevOps, site reliability engineers, and security experts — can embrace.
With these cloud security technologies integrated into Elastic Security, organizations will be able to protect their cloud-native workloads with the solution they’re already using to tackle their top security operations use cases. Check out the keynote to hear from Amit Kanfer of build.security and Jake King of Cmd.
The journey continues
Elastic Security is more than the sum of its parts.
It's not just what we at Elastic are doing — our amazing ecosystem of partners and users are building with us by adding integrations to support data collection and context gathering, continuous detection, automated response, and more.
The power and expertise of our community helps propel our solution and makes it more readily available to a wider range of users. Ultimately, the more accessible our solution is to security practitioners the world over, the more we all benefit from a better-secured global ecosystem. That’s why we make Elastic Security free and open, so that it’s readily available to analysts everywhere.
Limitless XDR is Elastic Security’s answer to the data problem that is the crux of today’s effective cybersecurity practice. To learn more about our vision for Elastic Security, watch our keynote and other Security sessions from ElasticON Global.
The release and timing of any features or functionality described in this post remain at Elastic's sole discretion. Any features or functionality not currently available may not be delivered on time or at all.