Deep dive on the BLISTER loader
Yesterday, the Elastic Security Research Team released a detailed report outlining technical details regarding the BLISTER launcher, a sophisticated campaign that we uncovered in December 2021.
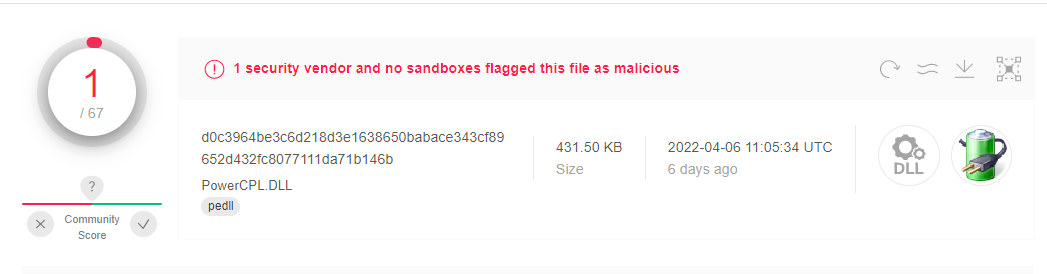
This latest release continues on research we’ve developed while observing the campaign over the last few months — specifically pertaining to the technical details of how the group behind this payload is able to stay under the radar and evade detection for many new samples identified.
Alongside this Loader research, the Elastic Security Research Team has provided a configuration extractor to allow threat researchers to continue work to discover further developments within this campaign, and expand detection capabilities for our community.
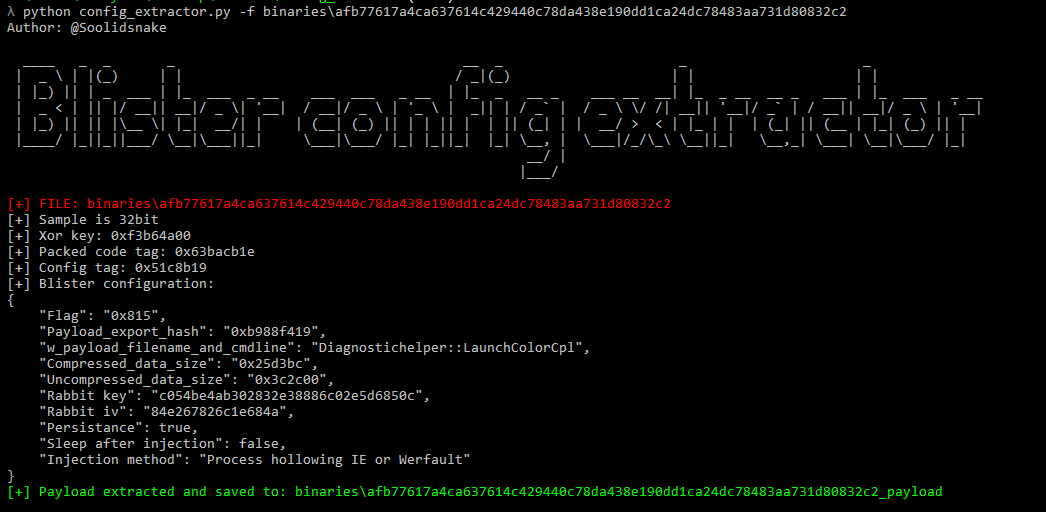
While complex, the loader research covers details around the execution flow for the campaign, and provides detailed information regarding each phase of the Loaders’ execution. The report continues to discuss nuances, signatures, and further YARA signatures for detecting this threat within any potentially impacted environment.
As Elastic Security continues to observe this threat actor group, we will provide updates to our tooling and further detailed reports regarding our findings. We wish to extend thanks to the security community for extending upon our initial findings in previous posts, and ensuring users are safe from threats such as these.
Users leveraging Elastic Security are currently protected against the known threats and vectors discussed in this post. Get started with a free 14-day trial of Elastic Cloud today.