Author
Samir Bousseaden
Articles

Copy Fail and DirtyFrag: Linux Page Cache Bugs in the Wild
This research analyzes the Linux kernel privilege escalation vulnerabilities Copy Fail and DirtyFrag, which exploit subtle page cache corruption bugs to create reliable paths to root access. Additionally, Elastic Security Labs is releasing detection logic for these vulnerabilities.

Phantom in the vault: Obsidian abused to deliver PhantomPulse RAT
Elastic Security Labs uncovers a novel social engineering campaign that abuses the popular note-taking application, Obsidian's legitimate community plugin ecosystem. The campaign, which we track as REF6598, targets individuals in the financial and cryptocurrency sectors through elaborate social engineering on LinkedIn and Telegram.

Prioritizing Alerts Triage with Higher-Order Detection Rules
Scaling SOC efficiency through multi-signal correlation and higher-order detection patterns.

Inside the Axios supply chain compromise - one RAT to rule them all
Elastic Security Labs analyzes a supply chain compromise of the axios npm package delivering a unified cross-platform RAT

Elastic releases detections for the Axios supply chain compromise
Hunting and detection rules for the Elastic-discovered Axios supply chain compromise.
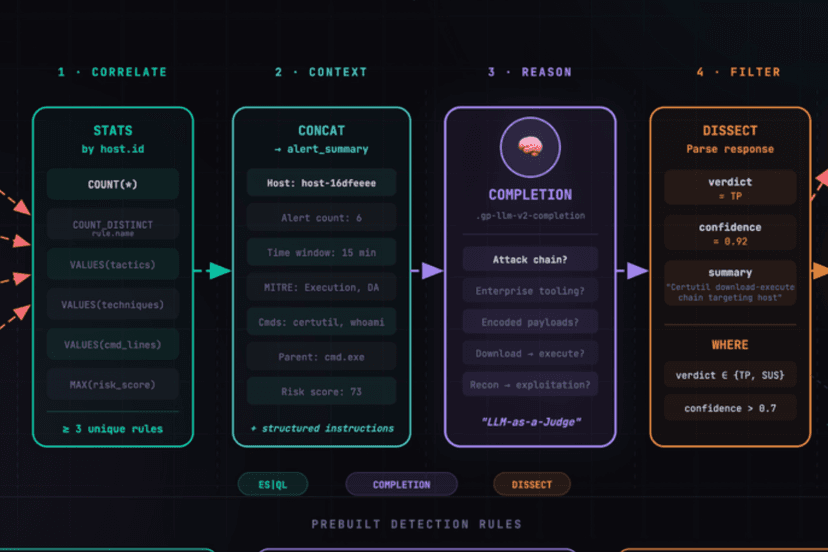
Beyond Behaviors: AI-Augmented Detection Engineering with ES|QL COMPLETION
Learn how Elastic's ES|QL COMPLETION command brings LLM reasoning directly into detection rules, enabling detection engineers to build intelligent alert triage without external orchestration.

Taking SHELLTER: a commercial evasion framework abused in-the-wild
Elastic Security Labs detected the recent emergence of infostealers using an illicitly acquired version of the commercial evasion framework, SHELLTER, to deploy post-exploitation payloads.

Announcing the Elastic Bounty Program for Behavior Rule Protections
Elastic is launching an expansion of its security bounty program, inviting researchers to test its SIEM and EDR rules for evasion and bypass techniques, starting with Windows endpoints. This initiative strengthens collaboration with the security community, ensuring Elastic’s defenses remain robust against evolving threats.
Detonating Beacons to Illuminate Detection Gaps
Learn how Elastic Security leveraged open-source BOFs to achieve detection engineering goals during our most recent ON week.

Katz and Mouse Game: MaaS Infostealers Adapt to Patched Chrome Defenses
Elastic Security Labs breaks down bypass implementations from the infostealer ecosystem’s reaction to Chrome 127's Application-Bound Encryption scheme.

Elevate Your Threat Hunting with Elastic
Elastic is releasing a threat hunting package designed to aid defenders with proactive detection queries to identify actor-agnostic intrusions.

Elastic releases the Detection Engineering Behavior Maturity Model
Using this maturity model, security teams can make structured, measurable, and iteritive improvements to their detection engineering teams..

GrimResource - Microsoft Management Console for initial access and evasion
Elastic researchers uncovered a new technique, GrimResource, which allows full code execution via specially crafted MSC files. It underscores a trend of well-resourced attackers favoring innovative initial access methods to evade defenses.

Globally distributed stealers
This article describes our analysis of the top malware stealer families, unveiling their operation methodologies, recent updates, and configurations. By understanding the modus operandi of each family, we better comprehend the magnitude of their impact and can fortify our defences accordingly.

Invisible miners: unveiling GHOSTENGINE’s crypto mining operations
Elastic Security Labs has identified REF4578, an intrusion set incorporating several malicious modules and leveraging vulnerable drivers to disable known security solutions (EDRs) for crypto mining.

Spring Cleaning with LATRODECTUS: A Potential Replacement for ICEDID
Elastic Security Labs has observed an uptick in a recent emerging loader known as LATRODECTUS. This lightweight loader packs a big punch with ties to ICEDID and may turn into a possible replacement to fill the gap in the loader market.

Dissecting REMCOS RAT: An in-depth analysis of a widespread 2024 malware, Part Four
In previous articles in this multipart series, malware researchers on the Elastic Security Labs team decomposed the REMCOS configuration structure and gave details about its C2 commands. In this final part, you’ll learn more about detecting and hunting REMCOS using Elastic technologies.

Dissecting REMCOS RAT: An in-depth analysis of a widespread 2024 malware, Part Three
In previous articles in this multipart series, malware researchers on the Elastic Security Labs team dove into the REMCOS execution flow. In this article, you’ll learn more about REMCOS configuration structure and its C2 commands.

Dissecting REMCOS RAT: An in-depth analysis of a widespread 2024 malware, Part Two
In the previous article in this series on the REMCOS implant, we shared information about execution, persistence, and defense evasion mechanisms. Continuing this series we’ll cover the second half of its execution flow and you’ll learn more about REMCOS recording capabilities and communication with its C2.

Dissecting REMCOS RAT: An in-depth analysis of a widespread 2024 malware, Part One
This malware research article describes the REMCOS implant at a high level, and provides background for future articles in this multipart series.

500ms to midnight: XZ A.K.A. liblzma backdoor
Elastic Security Labs is releasing an initial analysis of the XZ Utility backdoor, including YARA rules, osquery, and KQL searches to identify potential compromises.

In-the-Wild Windows LPE 0-days: Insights & Detection Strategies
This article will evaluate detection methods for Windows local privilege escalation techniques based on dynamic behaviors analysis using Elastic Defend features.

Unveiling malware behavior trends
An analysis of a diverse dataset of Windows malware extracted from more than 100,000 samples revealing insights into the most prevalent tactics, techniques, and procedures.
Doubling Down: Detecting In-Memory Threats with Kernel ETW Call Stacks
With Elastic Security 8.11, we added further kernel telemetry call stack-based detections to increase efficacy against in-memory threats.

Peeling back the curtain with call stacks
In this article, we'll show you how we contextualize rules and events, and how you can leverage call stacks to better understand any alerts you encounter in your environment.

Upping the Ante: Detecting In-Memory Threats with Kernel Call Stacks
We aim to out-innovate adversaries and maintain protections against the cutting edge of attacker tradecraft. With Elastic Security 8.8, we added new kernel call stack based detections which provide us with improved efficacy against in-memory threats.
Exploring Windows UAC Bypasses: Techniques and Detection Strategies
In this research article, we will take a look at a collection of UAC bypasses, investigate some of the key primitives they depend on, and explore detection opportunities.
Elastic users protected from SUDDENICON’s supply chain attack
Elastic Security Labs is releasing a triage analysis to assist 3CX customers in the initial detection of SUDDENICON, a potential supply-chain compromise affecting 3CX VOIP softphone users.

Hunting for Suspicious Windows Libraries for Execution and Defense Evasion
Learn more about discovering threats by hunting through DLL load events, one way to reveal the presence of known and unknown malware in noisy process event data.

Detect Credential Access with Elastic Security
Elastic Endpoint Security provides events that enable defenders with visibility on techniques and procedures which are commonly leveraged to access sensitive files and registry objects.

Hunting for Lateral Movement using Event Query Language
Elastic Event Query Language (EQL) correlation capabilities enable practitioners to capture complex behavior for adversary Lateral Movement techniques. Learn how to detect a variety of such techniques in this blog post.

SiestaGraph: New implant uncovered in ASEAN member foreign ministry
Elastic Security Labs is tracking likely multiple on-net threat actors leveraging Exchange exploits, web shells, and the newly discovered SiestaGraph implant to achieve and maintain access, escalate privilege, and exfiltrate targeted data.
Detecting Exploitation of CVE-2021-44228 (Log4j2) with Elastic Security
This blog post provides a summary of CVE-2021-44228 and provides Elastic Security users with detections to find active exploitation of the vulnerability in their environment. Further updates will be provided to this post as we learn more.

Detecting and responding to Dirty Pipe with Elastic
Elastic Security is releasing detection logic for the Dirty Pipe exploit.

Elastic Security uncovers BLISTER malware campaign
Elastic Security has identified active intrusions leveraging the newly identified BLISTER malware loader utilizing valid code-signing certificates to evade detection. We are providing detection guidance for security teams to protect themselves.

A close look at the advanced techniques used in a Malaysian-focused APT campaign
Our Elastic Security research team has focused on advanced techniques used in a Malaysian-focused APT campaign. Learn who’s behind it, how the attack works, observed MITRE attack® techniques, and indicators of compromise.

Practical security engineering: Stateful detection
By formalizing stateful detection in your rules, as well as your engineering process, you increase your detection coverage over future and past matches. In this blog post, learn why stateful detection is an important concept to implement.