KI-Agenten sind nur so gut wie die Oberflächen, die sie zurückgeben. Ein textbasiertes Tool-Ergebnis reduziert alles, was von Natur aus visuell oder interaktiv ist: ein Dashboard, eine Alert-Liste, ein Untersuchungsgraph, ein verteilter Trace. Das Gespräch wird zu einem Ort, an dem man Fragen stellt und der Agent antwortet, aber sobald die Arbeit intensiver wird, wechselt man zu einem anderen Tab, einem anderen Produkt, einer anderen Authentifizierungsgrenze.
MCP-Apps verändern die Form dieser Antwort. Ein Tool kann nun eine interaktive Benutzeroberfläche zusammen mit seiner Textzusammenfassung zurückgeben, und der Host (Claude Desktop, Claude.ai, VS Code Copilot, Cursor) rendert sie inline im Gespräch. Das Modell behält den kompakten Text für das Reasoning bei. Der Mensch erhält eine anklickbare Live-Schnittstelle direkt neben dem Chat.
Drei Eigenschaften unterscheiden diese Art der Integration von „einem Webhook, der eine URL zurückgibt“:
- Erhaltung des Kontexts. Die Benutzeroberfläche ist Teil des Gesprächs – kein Tabwechsel, keine Übergaben.
- Bidirektionaler Datenfluss. Die Benutzeroberfläche kann für frische Daten Tools auf dem MCP-Server aufrufen, und der Host kann neue Ergebnisse vom Agenten zurück in die Benutzeroberfläche senden. Keine separate API-Schicht oder Authentifizierungsleitung.
- Sandbox-Vertrauensgrenze. MCP-Apps laufen in einem vom Host gesteuerten iFrame. Sie können weder auf die übergeordnete Seite zugreifen, noch Cookies lesen oder ihren Container verlassen.
Sicherheitsoperationen basieren auf Triage, Untersuchungsgraphen und Attack Discovery, bei der ein KI-Agent Hunderte von Alerts in eine Handvoll Angriffsketten korreliert. Observability bedeutet verteilte Traces und detaillierte Zeitreihenanalysen. Das Erstellen in Kibana bedeutet ein Dashboard-Raster. Wenn man irgendetwas davon auf Text reduziert, geht das verloren, was es nützlich macht. Wir haben MCP-Apps für alle drei entwickelt und stellen sie gemeinsam als Open Source zur Verfügung, sodass dasselbe Gespräch von einer Triage-Warteschlange über einen Abhängigkeitsgraphen bis hin zu einem Live-Dashboard geführt werden kann, ohne dass der Chat verlassen werden muss.
Jede der drei Referenz-Apps ist ein MCP-Server, der viele interaktive Ansichten anbietet, nicht ein Bündel separater Produkte. Allein die Sicherheits-App zeigt sechs Dashboards an, die dieselbe Server-Shell, dasselbe Modell für die Sichtbarkeit von Tools und dieselbe Host-Bridge verwenden. Das Muster ist klein; die Oberfläche ist der Bereich, an dem sich der Wert zusammensetzt.
Elastic Security MCP App
Warum es für den SOC wichtig ist
Wenn ein Agent einem SOC-Analysten sagt „Es gibt 47 Alarme auf Host-314, hier ist eine Zusammenfassung“, dann hat er keine Arbeit verrichtet.. Er hat lediglich an den Ort gedeutet, an dem die Arbeit beginnt. Die eigentliche Arbeit findet in der Alarmliste, dem Prozessbaum, dem Untersuchungsgraphen und der Ticketdatei statt. Das geht nicht anhand eines Textabsatzes.
Die Sicherheits-MCP-App gibt den Workflow selbst zurück. Der Analyst erteilt dem Agenten Anweisungen, und der Agent antwortet mit einem interaktiven Dashboard im Chat, auf dem der Analyst Alerts detailliert analysieren, Bedrohungsanalysen ausführen, Angriffsketten korrelieren und Tickets eröffnen kann, ohne dabei den Gesprächsfaden zu verlieren. Und da die Ergebnisse, Anfragen und Tickets alle wieder in Elasticsearch landen, wartet dieselbe Untersuchung in Kibana, wo der Analyst nach Abschluss des Gesprächs wieder anknüpfen kann.
Sechs interaktive Dashboards
Die Elastic Security MCP-App liefert sechs interaktive Elemente, eines pro Haupt-SOC-Workflow. Jedes dieser Elemente ist eine React-Benutzeroberfläche, die inline gerendert wird, wenn der Agent das entsprechende Tool aufruft:
| Tool | Was es tut | Interaktive Benutzeroberfläche |
|---|---|---|
| Alert-Triage | Abrufen, Filtern und Klassifizieren von Sicherheits-Alerts | Schweregradgruppierung, KI-Urteilskarten, Prozessbaum, Netzwerkereignisse |
| Angriffserkennung | KI-korrelierte Angriffskettenanalyse mit On-Demand-Generierung | Narrativkarten zu Angriffen mit Konfidenzbewertung, Entitätsrisiko und MITRE-Mapping |
| Case Management | Erstellen, Suchen und Verwalten von Untersuchungstickets | Ticketliste mit Warnungen, Beobachtungen, Kommentar-Tabs und KI-Aktionen |
| Erkennungsregeln | Durchsuchen, Optimieren und Verwalten von Erkennungsregeln | Regelbrowser mit KQL-Suche, Abfragevalidierung, Analyse rauschbehafteter Regeln |
| Threat Hunt | ES|QL-Workbench mit Entitätsanalyse | Abfrageeditor, anklickbare Entitäten und Untersuchungsgraph |
| Beispieldaten | Generieren von ECS-Sicherheitsereignissen für gängige Angriffsszenarien | Szenario-Picker mit vier vorgefertigten Angriffsketten |
Jedes Tool liefert eine kompakte Textzusammenfassung, die das Modell für das Reasoning zurate ziehen kann, zusammen mit der interaktiven Benutzeroberfläche, auf der der Analyst agiert. Die Benutzeroberfläche kann auch frische Daten im Hintergrund über die MCP-Host-Bridge abrufen. Das vollständige Tool-Modell und die Bridge-API befinden sich im Architekturdokument des Repo.
Die App wird auch mit Claude Desktop-Skills ausgeliefert, SKILL.md -Dateien, die dem Agenten beibringen, wann und wie jedes Tool verwendet werden soll. Laden Sie vorgefertigte Skill-Zip-Dateien aus der neuesten Version herunter.
Vom Alert zum Ticket
Vier Skills decken den Kern des SOC-Kreislaufs ab. Jeder greift einen Prompt auf, ruft ein Tool auf und gibt ein interaktives Dashboard zusammen mit einer Textzusammenfassung zurück, über die das Modell nachdenkt. Der Tag eines Analysten beginnt normalerweise mit einer Alert-Warteschlange.
Triage-Alerts. Bitten Sie den Agenten, eine Triage nach Host, Regel, Nutzer oder Zeitfenster durchzuführen. Der Skill „Alert Triage“ liefert ein Dashboard mit KI-Urteilen oberhalb der ursprünglichen Alert-Liste. Jedes Urteil pro Erkennungsregel klassifiziert die Aktivität dieser Regel als gutartig, verdächtig oder bösartig und enthält eine Konfidenzbewertung sowie eine empfohlene Vorgehensweise. Klicken Sie auf eine Warnung, um eine detaillierte Ansicht mit einem Prozessbaum, Netzwerkereignissen, verwandten Warnungen und MITRE ATT&CK-Tags zu öffnen. Sie müssen nicht zwischen dem KI-Gespräch und Ihrem Benachrichtigungs-Dashboard in Kibana wechseln, alles findet in Echtzeit innerhalb Ihres Gesprächs statt.

Jagen Sie Bedrohungen. Bitten Sie den Agenten, Ihre Indizes zu durchsuchen. Der Skill „Threat Hunt“ gibt eine ES|QL-Workbench zurück, in der die Abfrage vorausgefüllt und automatisch ausgeführt wird. Jede Entität in den Ergebnissen ist anklickbar, um Details aufzurufen. Das Modell schreibt eine kurze Zusammenfassung unter die Tabelle – was ungewöhnlich ist, was verbunden ist, was einen genaueren Blick wert ist. Es bietet dann den nächsten Schritt an: Entweder tiefer in die Bedrohungssuche einzutauchen oder eine neue Fähigkeit innerhalb der MCP-App zu starten, die die bisher geleistete Arbeit ergänzt. Eine hervorragende Ergänzung dazu ist die Durchführung einer „Attack Discovery“, um mehr Kontext zu den Alerts zu sammeln, mit denen Sie sich eingehend beschäftigt haben, und zu den Bedrohungen, die Sie bisher gejagt haben.

Attack Discovery ausführen. Der Skill „Attack Discovery“ löst die Attack Discovery-API aus und gibt eine Rangliste der Ergebnisse zurück. Jedes Ergebnis besteht aus einer Reihe von zusammenhängenden Warnungen, die zu einer Angriffskette zusammengefügt werden. Dabei werden die MITRE-Taktik, eine Risikobewertung, eine Konfidenzbewertung sowie die betroffenen Hosts und Nutzer im Voraus angezeigt. Die Zusammenfassung des Agenten befindet sich unterhalb der Ergebnisse in der gleichen Rangordnung, und die Konversation enthält nun alles, was zum Handeln benötigt wird: Abfragen bei der Bedrohungsjagd, Triage-Entscheidungen, korrelierte Ketten, alles bereit für den nächsten Schritt.

Öffnen Sie Tickets, ohne den Chat zu verlassen. Genehmigen Sie die Ergebnisse gesammelt oder bitten Sie den Agenten, Tickets für bestimmte Alerts zu eröffnen. Der Skill „Case Management“ erstellt für jedes genehmigte Ergebnis ein Ticket (mit angehängtem Quell-Alert und übernommenen MITRE-Taktiken aus der Angriffskette) und zeigt die aktuelle Ticket-Liste direkt an. Klicken Sie auf ein Ticket, um die Detailansicht aufzurufen, die eine Reihe von KI-Aktionsschaltflächen enthält: Ticket zusammenfassen, Nächste Schritte vorschlagen, IOCs extrahieren und Zeitleiste generieren. Jede einzelne sendet einen strukturierten Prompt zurück an den Chat, sodass der Agent den Kontext des Tickets aufnimmt, ohne dass eine erneute Einführung erforderlich ist. Die Zusammenfassung des Agenten befindet sich unterhalb der Ticketliste und umfasst die gesamte IR-Warteschlange, einschließlich der gerade eröffneten Tickets und früherer Ergebnisse, die noch eines benötigen.

Jeder Schritt in diesem Walkthrough läuft in derselben Schleife: Ein Prompt kommt herein, der Skill nimmt ihn auf, das Tool gibt eine kompakte Textzusammenfassung zurück, die das Modell analysieren kann, zusammen mit einer interaktiven Benutzeroberfläche, auf der der Analyst arbeitet. Verkettet man die Skills miteinander, bilden sie einen durchgängigen SOC-Ablauf – suchen, priorisieren, korrelieren, Tickets öffnen und den nächsten Wechsel einleiten –, wobei das Modell den Sitzungskontext bei jedem Schritt berücksichtigt. Wenn Sie einen beliebigen einzeln aufrufen, erhalten Sie immer noch das vollständige Dashboard, das auf den von Ihnen benannten Datenausschnitt verweist. So oder so sammelt sich die Arbeit innerhalb des Gesprächs an: kein Wechseln zwischen Tabs, kein Kopieren und Einfügen, keine Übergaben.
Zwei weitere Skills vervollständigen die App: ein Browser für Erkennungsregeln zum Optimieren rauschbehafteter Regeln und ein Generator für Beispieldaten zum Erzeugen realistischer ECS-Ereignisse in einem neuen Cluster. In einem Folgebeitrag werden wir auf alle sechs näher eingehen: Untersuchungsgraph, Angriffsablauf-Canvas und vollständiger Walkthrough.
„Die MCP-App für Elastic Security schließt die Lücke zwischen automatisierter Erkennung und manueller Suche. Indem wir unsere Sicherheitsdaten direkt in eine einzige Schnittstelle innerhalb von Claude Desktop integriert haben, konnten wir „stille“ Bedrohungen in weniger als einer Stunde aufdecken – Risiken, die keine Standard-Alerts auslösten, aber sofortiges Handeln erforderten. Dies verstärkt die Leistungsfähigkeit unserer Analysten enorm.“ Mandy Andress: Chief Information Security Officer (CISO), Elastic.
So funktionierts
Jede MCP-App ist ein kleiner Node.js-Server, dessen Tools sowohl eine kompakte Textzusammenfassung für das Modell als auch eine React-Benutzeroberfläche zurückgeben, die der Host inline rendert. Da sie auf der offenen MCP App-Spezifikation basiert, läuft derselbe Server auf jedem kompatiblen Host – siehe die Architektur-Dokumentation des Repositorys für das vollständige Design.
Ausprobieren
Erfordert Elasticsearch 9.x mit aktivierter Security, plus Kibana für Tickets, Regeln und Angriffserkennung. Der schnellste Weg ist das Ein-Klick-.mcpb -Bundle aus der neuesten Version – wählen Sie es mit einem Doppelklick in Claude Desktop aus, und Sie werden nach Ihrer Elasticsearch-URL und Ihrem API-Schlüssel gefragt. Einrichtungsanleitungen für Cursor, VS Code, Claude Code, Claude.ai und zum Kompilieren aus dem Quellcode finden Sie im Repository.
Elastic Search MCP-App: Aus Gesprächen erstellte Dashboards
Jeder Kibana-Nutzer kennt den Umweg über das Dashboard: Man unterbricht seine aktuelle Arbeit, öffnet Kibana, wählt einen Index, Felder und eine Visualisierung aus, passt alles an und speichert. Das sind fünf Kontextwechsel, bevor überhaupt ein einziges Diagramm auf dem Bildschirm erscheint.
Die neue example-mcp-dashbuilder-Referenz-App fasst dies in einem Prompt zusammen. Bitten Sie den Agenten, „Erstelle mir ein Dashboard mit Umsatzkennzahlen, Bestelltrends und Kategorieaufschlüsselungen“, erscheint das Dashboard im Gespräch, ohne dass ein Wechseln des Tabs erforderlich ist.

Hinter diesem Prompt untersucht der Agent Ihre Elasticsearch-Daten über ES|QL und wählt Diagrammtypen aus, die zu den Daten passen: Balken für Vergleiche, Linien für Trends, metrische Karten für KPIs und Heatmaps für zweidimensionale Muster. Es ordnet Panels auf dem 48-spaltigen Raster von Kibana unter Verwendung des Borealis-Themes der Elastic-Benutzeroberfläche an, und das Ergebnis ist vollständig interaktiv: Sie können Panels direkt im Chat verschieben, ihre Größe ändern und sie in ausklappbare Abschnitte gruppieren. Wenn das Dashboard korrekt aussieht, exportiert ein einziger Tool-Aufruf es zu Kibana, wobei ES|QL-Abfragen und benutzerdefinierte Farben erhalten bleiben. Sie können ebenfalls bestehende Kibana-Dashboards zur KI-gestützten Bearbeitung wieder in den Chat importieren.
Das Prinzip ist dasselbe wie bei der Security-App: Wenn das Artefakt das Produkt ist, schließt die Rückgabe innerhalb des Gesprächs den Kreis zwischen der Beschreibung dessen, was man will, und der Anzeige des Produkts.
Unter der Haube folgt es demselben MCP-App-Muster. Ein Node.js-Server registriert ein view_dashboard modellorientiertes Tool zusammen mit einer Reihe von App-spezifischen Tools, die die Benutzeroberfläche direkt aufruft (Datenabruf, Layout-Persistenz, Zeitfelderkennung, Export/Import). Die Dashboard-Ansicht selbst ist eine einzelne, eigenständige HTML-Datei, die mit vite-plugin-singlefile geliefert wird und als MCP-App-Ressource dient. Entwickler, die das Repo forken, erhalten die gleiche Server-Shell und den gleichen Host-Bridge, die sie in der Security-App sehen, jedoch auf einen anderen Job ausgerichtet. Die example-mcp-dashbuilder README enthält die vollständige MCP-Architektur und Diagrammtyp-Referenz.
Elastic Observability MCP-App
Die dritte Referenz-App, die Elastic Observability MCP-App, behandelt die SRE-Version desselben Formproblems. Wenn etwas in der Produktion ausfällt, ist die Antwort, die der diensthabende Ingenieur benötigt, keine Grafik, sondern eine Diagnose, die aus K8s-Metriken, APM-Topologie, ML-Anomalien und Risikobewertung zusammengesetzt ist. Die Form der Antwort ist eine kausale Geschichte: Was ist gescheitert und warum, was hängt davon ab und was ist als Nächstes zu tun.
Sechs Tools zur Unterstützung des Workflows bei der Untersuchung der Beobachtbarkeit
| Tool | Abhängigkeit | Was es tut |
|---|---|---|
| observe | Universal | Transiente ES|QL- und ML-Anomalie-Zugriffsprimitive – eine Abfrage einmal ausführen, eine Metrik live erfassen oder blockieren, bis ein Schwellenwert oder eine Anomalie ausgelöst wird. |
| manage-alerts | Universal | Kibana-Regeln für schwellenwertbasiertes Alerting erstellen, auflisten, abrufen und löschen. Lassen Sie die Kibana-URL weg, um im Nur-Lese-Modus auszuführen. |
| ml-anomalies | ML-Jobs | ML-Anomalieeinträge abfragen und eine Inline-Anomalie-Erkläransicht öffnen. |
| apm-health-summary | Elastic APM | Cluster-Level-Health-Rollup aus APM-Telemetrie; Layer im K8s- und ML-Kontext, wenn verfügbar. |
| apm-service-dependencies | Elastic APM | Serviceabhängigkeitsgraph – Upstream/Downstream, Protokolle, Aufrufvolumen. |
| k8s-blast-radius | Kubernetes-Metriken | Auswirkungen von Node-Ausfällen – vollständiger Ausfall, degradiert, unbeeinträchtigt, Machbarkeit der Neuplanung. |
Cluster-Health-Rollup
Fragen Sie „Was ist defekt?“ oder „Gib mir einen Statusbericht“ und erhalten Sie eine Übersicht auf einen Blick: allgemeiner Zustand, beeinträchtigte Dienste mit Begründungen, die größten Pod-Speicher-Verbraucher, Aufschlüsselung des Schweregrads der Anomalien und der Service-Durchsatz – alles in einer einzigen Ansicht. Das ist der Ausgangspunkt, wenn sich etwas komisch anfühlt, Sie aber nicht wissen, wo Sie suchen sollen. Die Ansicht passt sich an die Gegebenheiten Ihres Deployments an. APM liefert Ihnen Service-Health-Informationen. Kubernetes-Metriken fügen Pod- und Node-Kontext hinzu. ML-Jobs integrieren Anomalien.

Dienstabhängigkeitsgraph
Fragen Sie „Was ruft die Kasse auf?“ oder „Zeig mir die Topologie“ und Sie erhalten einen geschichteten Abhängigkeitsgraphen – vorgelagerte Aufrufer, nachgelagerte Abhängigkeiten, Protokolle, Anrufvolumen und Latenz pro Kante. Bitten wir Claude, uns die Serviceabhängigkeiten des Frontends zu zeigen („Zeig mir die Serviceabhängigkeiten des Frontends“):

Zoomen Sie, schwenken Sie und bewegen Sie den Mauszeiger, um alle Details zu sehen, die Sie zum Verständnis der komplexen Servicebeziehungen benötigen:

Risiko mit einem Schadensradius bewerten
Fragen Sie „Was passiert, wenn mein k8s-Node ausfällt?“ und erhalten Sie ein radiales Auswirkungsdiagramm: Die Ziel-Node in der Mitte, vollständige Deployments in Rot, beeinträchtigte in Gelb und unbeeinflusste in Grau. Eine schwebende Übersichtskarte zeigt gefährdete Pods und die Machbarkeit der Neuplanung an. Single-Replikat-Deployments werden als Single Point of Failure markiert.

Observe
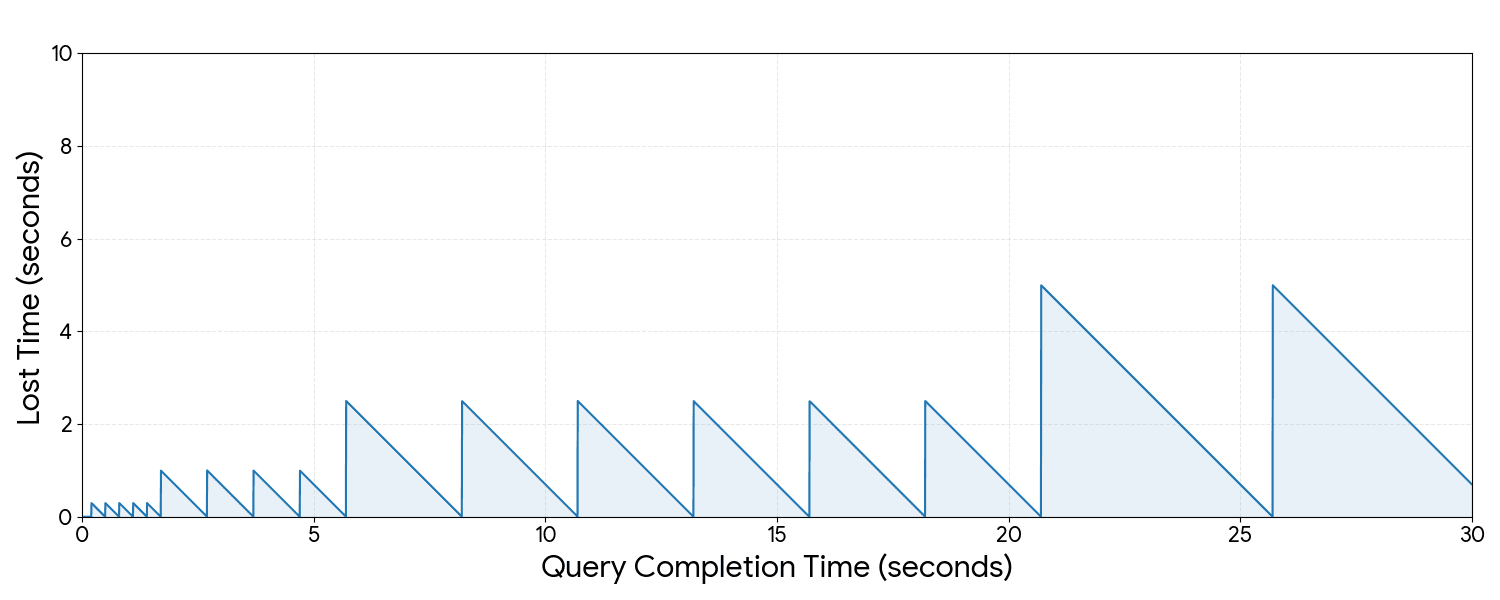
Das primäre Zugriffsprimitiv des Agenten für Elastic – ein Tool, drei Modi für drei verschiedene Bedürfnisse. Fragt man „Was macht die CPU gerade?“, führt es einmal eine ES|QL-Abfrage aus und gibt eine Tabelle zurück. Sagt man „Zeige mir die Frontend-Latenz für die nächsten 60 Sekunden“, erfasst es die Metrik live und aktualisiert das Diagramm an Ort und Stelle. Sagt man „Sag mir, wenn der Speicher unter 80 MB fällt“ oder „Achte auf alles Ungewöhnliche für die nächsten 10 Minuten“, blockiert es, bis die Bedingung erfüllt ist oder das Zeitfenster abläuft. Die Ansicht passt sich an den jeweiligen Modus an: eine Ergebnistabelle für einmalige Abfragen, ein Live-Trenddiagramm mit aktuellen, Spitzen- und Basisstatistiken für Stichproben- und Schwellenwertbedingungen, und eine Triggerkarte mit Schweregradbewertung für den Anomalienmodus.
So funktionierts
Dasselbe MCP-App-Muster wie die Security- und Search-Apps: ein Node.js-Server, sechs modellorientierte Tools, die auf sechs Einzeldatei-Ansichtsressourcen verdrahtet sind. Die Tools sind nach Deployment-Backend gruppiert (Universal, APM-abhängig, K8s-abhängig, ML-abhängig), sodass sowohl der Agent als auch der Nutzer im Voraus wissen, welche Tools für eine bestimmte Deployment relevant sind, anstatt beim Aufruf Fähigkeitslücken zu entdecken. Die MCP-App enthält auch einen beispielhaften Agent Builder-Workflow: k8s-crashloop-investigation-otel, der bei einem Kubernetes-Alert ausgelöst werden kann und eine strukturierte Ursachenzusammenfassung zurückgibt, bevor Sie ein einziges Dashboard geöffnet haben.
Der Agentic Stack, interaktiv
Drei Eigenschaften dieses Musters sind es wert, direkt erwähnt zu werden. Erstens ist das Ergebnis des Tools nicht mehr das Ende der Arbeit, sondern ihr Anfang: Das Gespräch liefert eine Schnittstelle, auf der Sie handeln können, keine Zusammenfassung, auf deren Grundlage Sie handeln müssen. Zweitens können derselbe Agent, derselbe Modellkontext und derselbe Gesprächsverlauf nun zwischen den Oberflächen von Security, Search und Observability wechseln, ohne das Gespräch zu verlassen. Drittens funktioniert das nur, weil Elasticsearch und Kibana die APIs bereits bereitstellen. Die MCP-App ist eine schlanke interaktive Schicht über den bereits mitgelieferten Produktfunktionen.
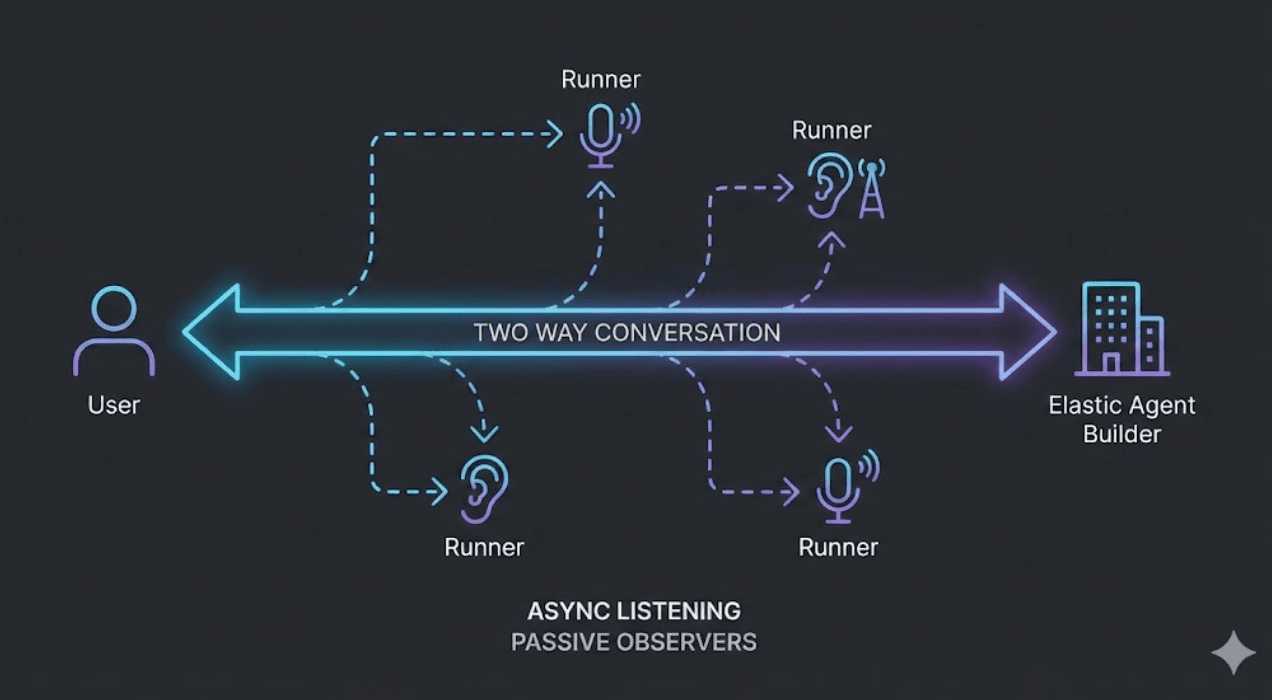
Attack Discovery unterstützt bereits die Ansicht der korrelierten Ergebnisse in dieser App. Innerhalb des Stacks geht das gleiche agentische Muster noch weiter: Elastic Workflows automatisieren die deterministischen Schritte (Entitäten anreichern, Tickets erstellen, Hosts isolieren), während Agent Builder die Daten analysiert und diese Workflows als Werkzeuge aufruft. Die MCP-App bringt diese Sicherheitsebene auch in die externe Kommunikation ein; Workflows und der Agent Builder vertiefen sie innerhalb des Stacks. Verschiedene Einstiegspunkte, dieselben Elastic-APIs darunter.
Probieren Sie es aus:
- Sicherheit: example-mcp-app-security
- Suchen und Dashboards: example-mcp-dashbuilder
- Beobachtbarkeit: example-mcp-observability
Sie haben noch keinen Elasticsearch-Cluster? Starten Sie eine kostenlose Elastic Cloud-Testversion. Weitere Informationen zu den Bausteinen der Sicherheits-App finden Sie in den zugehörigen Security Labs-Beiträgen zu Elastic Workflows und Agent Builder, Agent Skills und Attack Discovery.