Banks are leveraging modern cloud security tools to mitigate human error

The efficiency, security, and scalability of cloud operations are driving financial institutions’ adoption of the technology faster than ever before. The ability to meet customers where they want to transact, personalize solutions, and leverage new data and analytics solutions (including AI) on-demand is driving this growth. In fact, according to Accenture, the banking industry's workloads in the cloud more than doubled from 2021 to 2022.
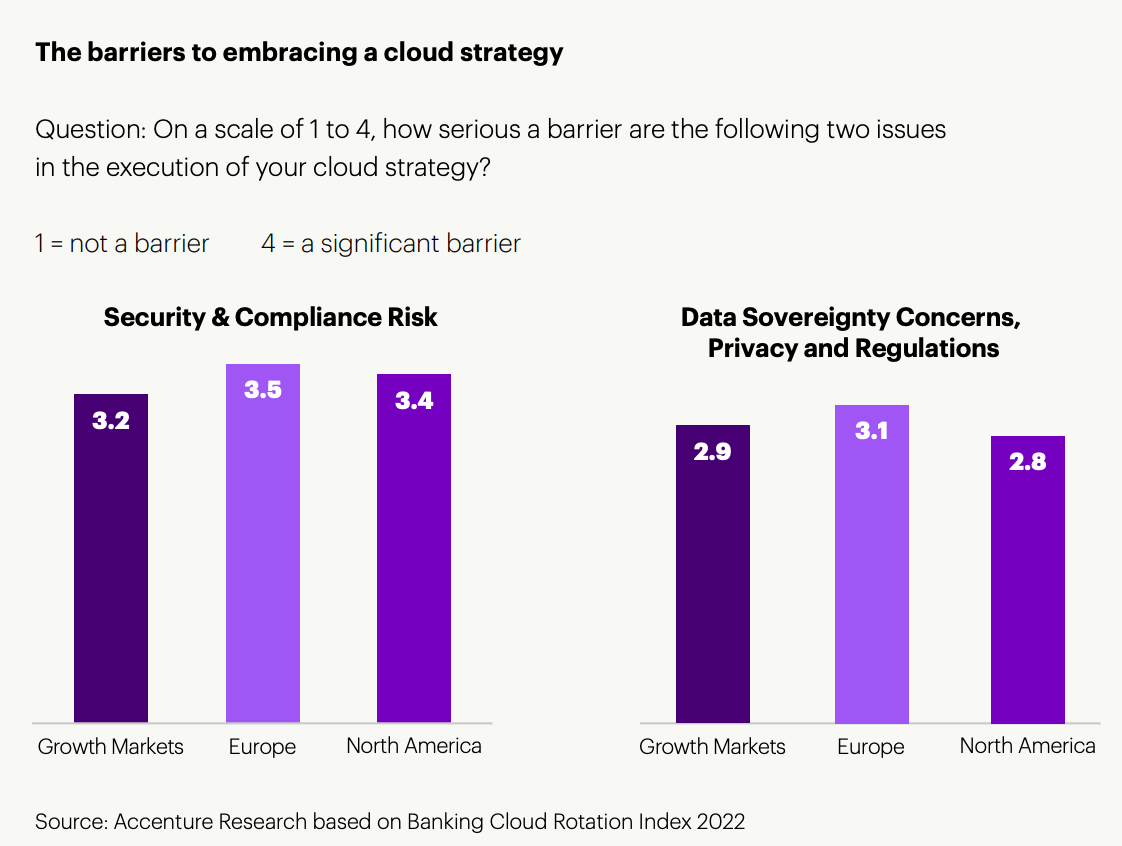
However, despite the rapid pace of change, more than 85% of banking workloads still remain on-prem. Part of the apprehension to send more workloads to the cloud has to do with underlying cloud security concerns. Even with rapid security advancements made by cloud providers over the past decade, the risk of a data breach or failure to meet regulations is still a major concern for financial institutions.
Where the rubber meets the cloud
The argument that cloud providers offer financial institutions a more secure environment than that of deploying on-prem is a fair one. Cloud providers have an army of subject-matter experts and top tier talent, and they are investing heavily in security innovation. The technology they offer is built on modern architecture, with updates and patches managed by the provider. Compliance and regulations are closely monitored, with all major cloud providers working closely with local jurisdictions to obtain the proper certifications in financial services (e.g., PCI DSS, GDPR, SOX).
However, even with all of these protection mechanisms in place, errors on the client side can still lead to massive disruptions. Cloud providers look at security as a shared responsibility with their customers. The challenge is that setting up and running workloads in the cloud is still a relatively new task for most financial institutions. It can be easy to misallocate resources, set the wrong permissions, or get lost in the complexity of new services — especially if developers and users are not appropriately trained in this capacity.
Gartner states that 99% of cloud failures will be the customer’s fault due to mistakes like cloud misconfigurations. Research from Elastic Security Labs also found that nearly 1 in 3 (33%) attacks in the cloud leverage credential access, indicating that users often overestimate the security of their cloud environments and consequently fail to configure and protect them adequately.
Cloud Native Application Protection Platforms as (not) a separate tool
The category of Cloud Native Application Protection Platforms (CNAPPs) offers security capabilities to help customers with their “security in the cloud” responsibilities. This is meant to enhance their security posture as they perform continuous compliance checks and identify risks associated with workloads being developed. CNAPPs can help users automatically identify and remediate misconfigurations, maintain compliance, and provide greater visibility and analysis into multi-cloud environments. This can greatly reduce the risk of breaches and potential reputational harm for financial institutions.
While the advantages of CNAPP tools are clear, it's critical that FSIs are not adding yet another tool to the complex mix of vendors they use for cyber and information security. To support this objective, Elastic now delivers the only leading security analytics solution that includes CNAPP for AWS, and it’s coming soon for Google Cloud and Microsoft Azure. This is part of the holistic, single-platform Elastic Security solution, which enables financial institutions to manage the security of their environment across on-prem, hybrid, and multi-cloud environments. By combining traditional security tools into one, teams can protect, investigate, and respond to threats quickly and at scale without pivoting across technologies. The solution enables security teams to protect their cloud environments and:
- Gain deep visibility into cloud runtime workloads to accelerate remediation with Cloud Workload Protection
- Minimize exposed attack surfaces that result from misconfiguration by using Cloud Security Posture Management to align deployments with industry benchmarks with one-click, out-of-the-box integrations
- Know what’s happening inside a container and detect malicious behavior within runtime workloads with the expanded Container Workload Protection
- Provide efficient end-to-end triage workflows with risk and runtime context by continuously identifying and reporting known vulnerabilities with Cloud Vulnerability Management at minimal resource utilization