On-demand webinar
Spotting Security Anomalies with the new Elasticsearch Maps and Uptime features in the Elastic (ELK) Stack
Hosted by:

James Spiteri
Director of Product Management, Elastic Security
Elastic

Nic Palmer
Principle Solutions Architect, EMEA
Elastic
Overview
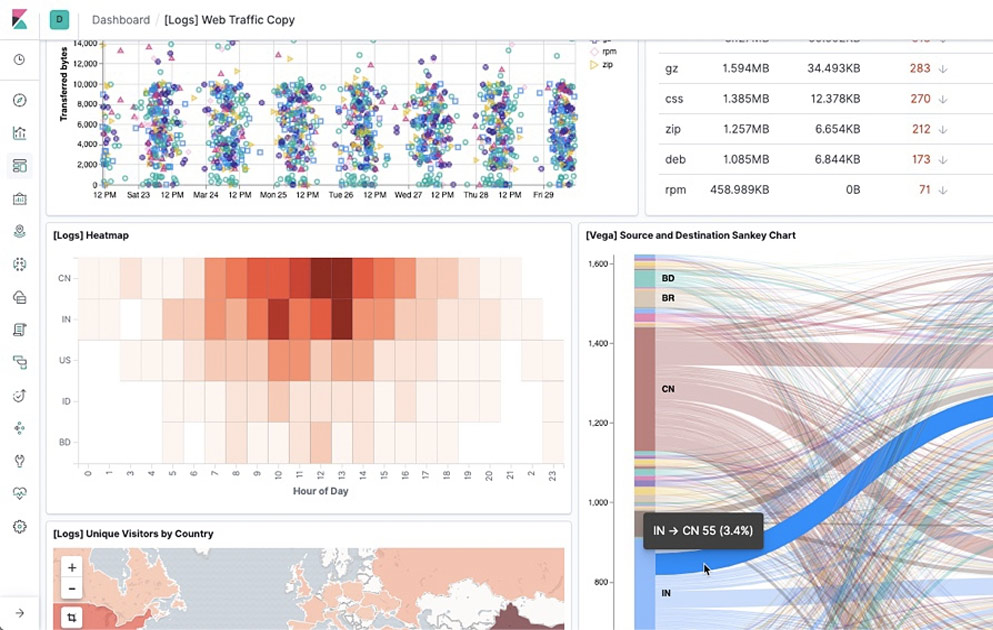
With the launch of "Maps" and "Uptime", we’ve given users of the Elastic Stack even more ways of analysing data sets and spotting issues within their environments. The use of these features may be fairly obvious in a network operations, business analytics or operational analytics context - but what about security operations?
Elastic’s lightweight heartbeat agent can periodically monitor several network services such as http(s), TCP and ICMP endpoints. Within seconds, the data finds its way into Elasticsearch and is immediately viewable in the new curated uptime UI. We have other beats such as Filebeat and Packetbeat, as well as logstash plugins, which can gather data sources with IP addresses and enrich them with geo location information. Now, with a dedicated UI for maps, we can layer several different data sources which contain geo points, aggregate them, correlate against other metrics, and more.
In this webinar, James Spiteri, Elastic Solutions Architect, Cyber Security Specialist, and Nicholas Palmer, Elastic Solutions Architect, show you how one can use the Maps and Uptime features to spot anomalies in security data sets.
This demo will show:
- How to use heartbeat and uptime to spot potential security anomalies (WAF failures, TLS certificate expiry, irregular latency etc).
- Using maps to layer several different security data sources with geo points
- Create machine learning jobs and alerts based on the heartbeat datasets
Additional Resources:

View next


Upcoming webinar
How WP Engine brings AI innovation to websites with Elastic and Google Cloud

Upcoming webinar
What we got wrong about AI in the public sector: A fireside chat with IDC