Get up and running
editGet up and runningedit
This functionality is in beta and is subject to change. The design and code is less mature than official GA features and is being provided as-is with no warranties. Beta features are not subject to the support SLA of official GA features.
You need:
-
An Elasticsearch cluster and Kibana (version 7.2 or later) with a basic license. See Getting started with the Elastic Stack.
You can skip installing Elasticsearch and Kibana by using our hosted Elasticsearch Service on Elastic Cloud. The Elasticsearch Service is available on both AWS and GCP. Try the Elasticsearch Service for free.
- Beats shippers (version 7.x or later) installed for each system you want to monitor
You might need to modify UI settings in Kibana to change default behaviors, such as the index pattern used to query the data. For more information, see Kibana.
Install Beats shippersedit
To populate the SIEM app with hosts and network security events, you need to install and configure Beats on the systems from which you want to ingest security events:
- Filebeat for forwarding and centralizing logs and files
- Auditbeat for collecting security events
- Winlogbeat for centralizing Windows event logs
- Packetbeat for analyzing network activity
The Elastic Common Schema (ECS) enables SIEM to work
with custom and third-party data sources in addition to
those supported by Beats. It is important to note that SIEM uses the
host.name ECS field as the primary key for identifying hosts.
You can install Beats using a Kibana-based guide or directly from the command line.
Install Beats using the Kibana-based guideedit
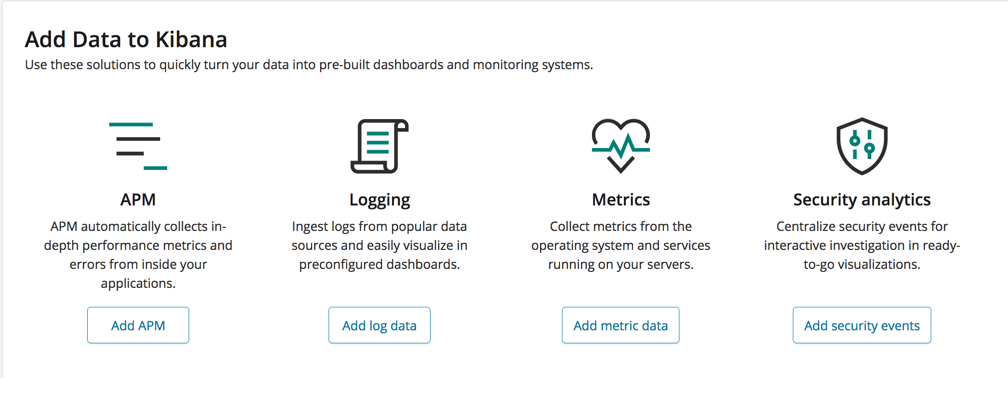
Follow the instructions in the Add Data section of the Kibana home page. Click Add log data or Add metrics, and follow the links for the types of data you want to collect.
Download and install Beats from the command lineedit
If your data source isn’t in the list, or you want to install Beats the old fashioned way:
- Filebeat and Filebeat modules. See the Filebeat modules quick start and enable modules for the events you want to collect. If there is no module for the events you want to collect, see the Filebeat getting started to learn how to configure inputs.
- Auditbeat. See Auditbeat getting started.
- Winlogbeat. See Winlogbeat getting started.
- Packetbeat. See Packetbeat getting started.
Enable modules and configuration optionsedit
For either approach, you need to enable modules in Auditbeat and Filebeat to populate the SIEM app with data.
To populate Hosts data, enable these Auditbeat modules:
To populate Network data, enable the relevant Packetbeat protocols and Filebeat modules: