On-demand webinar
Finding Bad Guys Using Math and Statistics
Hosted by:

Jared McQueen
Principal Systems Engineer
McQueen Solutions
Overview
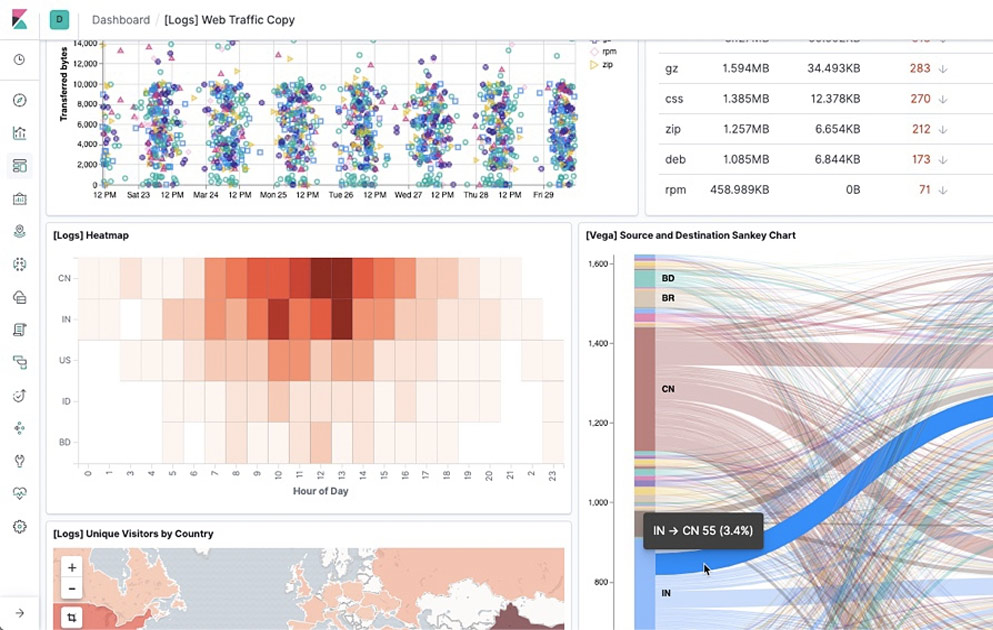
Using enrichment to turn low-value events into high-value events. Enrichment techniques are geoip, tld extraction, length, and entropy. I then demonstrate how to find anomalous stuff like: drive-by malware / malicious web browsing Command and Control (C2) Communications DNS tunneling Data Exfiltration

View next


Upcoming webinar
How WP Engine brings AI innovation to websites with Elastic and Google Cloud

Upcoming webinar
What we got wrong about AI in the public sector: A fireside chat with IDC