WARNING: Version 5.4 of the Elastic Stack has passed its EOL date.
This documentation is no longer being maintained and may be removed. If you are running this version, we strongly advise you to upgrade. For the latest information, see the current release documentation.
Kibana and Security
editKibana and Security
editKibana users have to log in when X-Pack security is enabled on your cluster. You configure X-Pack security roles for your Kibana users to control what data those users can access. You also need to configure credentials for the Kibana server so the requests it submits to Elasticsearch on the user’s behalf can be authenticated.
To prevent user passwords from being sent in the clear, you must configure Kibana to encrypt communications between the browser and the Kibana server. If are encrypting traffic to and from the nodes in your Elasticsearch cluster, you must also configure Kibana to connect to Elasticsearch via HTTPS.
With X-Pack security enabled, if you load a Kibana dashboard that accesses data in an index that you are not authorized to view, you get an error that indicates the index does not exist. X-Pack security do not currently provide a way to control which users can load which dashboards.
Support for tribe nodes in Kibana was added in v5.2.
To use Kibana with X-Pack security:
-
Configure the password for the built-in
kibanauser. The Kibana server submits requests as this user to access the cluster monitoring APIs and the.kibanaindex. The server does not need access to user indices.By default, the
kibanauser password is set tochangeme. Change this password through the reset password API:PUT /_xpack/security/user/kibana/_password { "password" : "s0m3th1ngs3cr3t" }Once you change the password, you need to specify it with the
elasticsearch.passwordproperty inkibana.yml:elasticsearch.password: "s0m3th1ngs3cr3t"
-
Assign the
kibana_userrole to grant Kibana users the privileges they need to use Kibana.You also need to grant Kibana users access to the indices that they will be working with in Kibana.
-
If you’re using the
nativerealm, you can assign roles using the User Management API. For example, the following creates a user namedjacknichand assigns it thekibana_userrole:POST /_xpack/security/user/jacknich { "password" : "t0pS3cr3t", "roles" : [ "kibana_user" ] } -
If you are using an LDAP or Active Directory realm, you can either assign roles on a per user basis, or assign roles to groups of users. By default, role mappings are stored in
CONFIGDIR/x-pack/role_mapping.yml. For example, the following snippet assigns thekibana_userrole to the group namedadminsand the user named Jack Nicholson:kibana_user: - "cn=admins,dc=example,dc=com" - "cn=Jack Nicholson,dc=example,dc=com"
-
-
Configure Kibana to encrypt communications between the browser and the Kibana server:
-
Generate a server certificate for Kibana. You must either set the certificate’s
subjectAltNameto the hostname, fully-qualified domain name (FQDN), or IP address of the Kibana server, or set the CN to the Kibana server’s hostname or FQDN. Using the server’s IP address as the CN does not work. -
Set the
server.ssl.keyandserver.ssl.certificateproperties inkibana.yml:server.ssl.key: /path/to/your/server.key server.ssl.certificate: /path/to/your/server.crt
Once you enable SSL encryption between the browser and the Kibana server, access Kibana via HTTPS. For example,
https://localhost:5601.You must enable SSL encryption between the browser and the Kibana server to use Kibana with X-Pack security enabled. If X-Pack security is configured to encrypt connections to Elasticsearch, you must also configure Kibana to connect to Elasticsearch via HTTPS.
-
Generate a server certificate for Kibana. You must either set the certificate’s
-
If you have enabled SSL encryption in X-Pack security, configure Kibana to connect to Elasticsearch via HTTPS:
-
Specify the HTTPS protocol in the
elasticsearch.urlsetting in the Kibana configuration file,kibana.yml:elasticsearch.url: "https://<your_elasticsearch_host>.com:9200"
-
If you are using your own CA to sign certificates for Elasticsearch, set the
elasticsearch.ssl.certificateAuthoritiessetting inkibana.ymlto specify the location of the PEM file.elasticsearch.ssl.certificateAuthorities: /path/to/your/cacert.pem
-
-
Install X-Pack into Kibana to secure user sessions and enable users to log in and out of Kibana:
-
Run the following command in your Kibana installation directory.
bin/kibana-plugin install x-pack
To perform an offline install, download the X-Pack zip file from
https://artifacts.elastic.co/downloads/packs/x-pack/x-pack-5.4.3.zip(sha1) and run:bin/kibana-plugin install file:///path/to/file/x-pack-5.4.3.zip
-
Set the
xpack.security.encryptionKeyproperty in thekibana.ymlconfiguration file. You can use any text string that is 32 characters or longer as the encryption key.xpack.security.encryptionKey: "something_at_least_32_characters"
-
To change the default session duration, set the
xpack.security.sessionTimeoutproperty in thekibana.ymlconfiguration file. By default, sessions will stay active until the browser is closed. The timeout is specified in milliseconds. For example, set the timeout to 600000 to expire sessions after 10 minutes:xpack.security.sessionTimeout: 600000
-
-
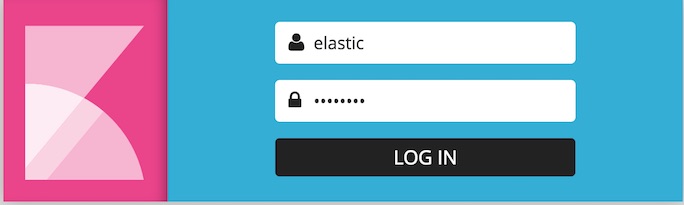
Restart Kibana and verify that you can log in as a user. If you are running Kibana locally, go to
https://localhost:5601and enter the credentials for a user you’ve assigned a Kibana user role. For example, you could log in as thejacknichuser created above.This must be a user who has been assigned the
kibana_userrole. Kibana server credentials should only be used internally by the Kibana server.
Kibana X-Pack security UI Settings
edit| Name | Default | Description |
|---|---|---|
|
- |
An arbitrary string of 32 characters or more used to encrypt credentials in a cookie. It is crucial that this key is not exposed to users of Kibana. Required. |
|
|
Sets the session duration (in milliseconds). |
|
|
Sets the name of the cookie used for the session. |
|
|
Sets the |