Run Osquery from investigation guides
Detection rule investigation guides suggest steps for triaging, analyzing, and responding to potential security issues. When you build a custom rule, you can also set up an investigation guide that incorporates Osquery. This allows you to run live queries from a rule’s investigation guide as you analyze alerts produced by the rule.
- The Osquery manager integration must be installed.
- Elastic Agent's status must be
Healthy. Refer to Common problems with Fleet and Elastic Agent if it isn’t. - In Elastic Stack, your role must have Osquery feature privileges.
- In Serverless, you must have the appropriate user role to use this feature.
You can only add Osquery to investigation guides for custom rules because prebuilt rules cannot be edited.
Go to the Rules page. To access it, find Detection rules (SIEM) in the main menu or by using the global search field.
Select a rule to open the its details, then click Edit rule settings.
Select the About tab, then expand the rule’s advanced settings.
Scroll down to the Investigation guide section. In the toolbar, click the Osquery button (
 ).
).Add a descriptive label for the query; for example,
Search for executables.Select a saved query or enter a new one.
TipUse placeholder fields to dynamically add existing alert data to your query.
Expand the Advanced section to set a timeout period for the query, and view or set mapped ECS fields included in the results from the live query (optional).
NoteOverwriting the query’s default timeout period allows you to support queries that take longer to run. The default and minimum supported value for the Timeout field is
60. The maximum supported value is900.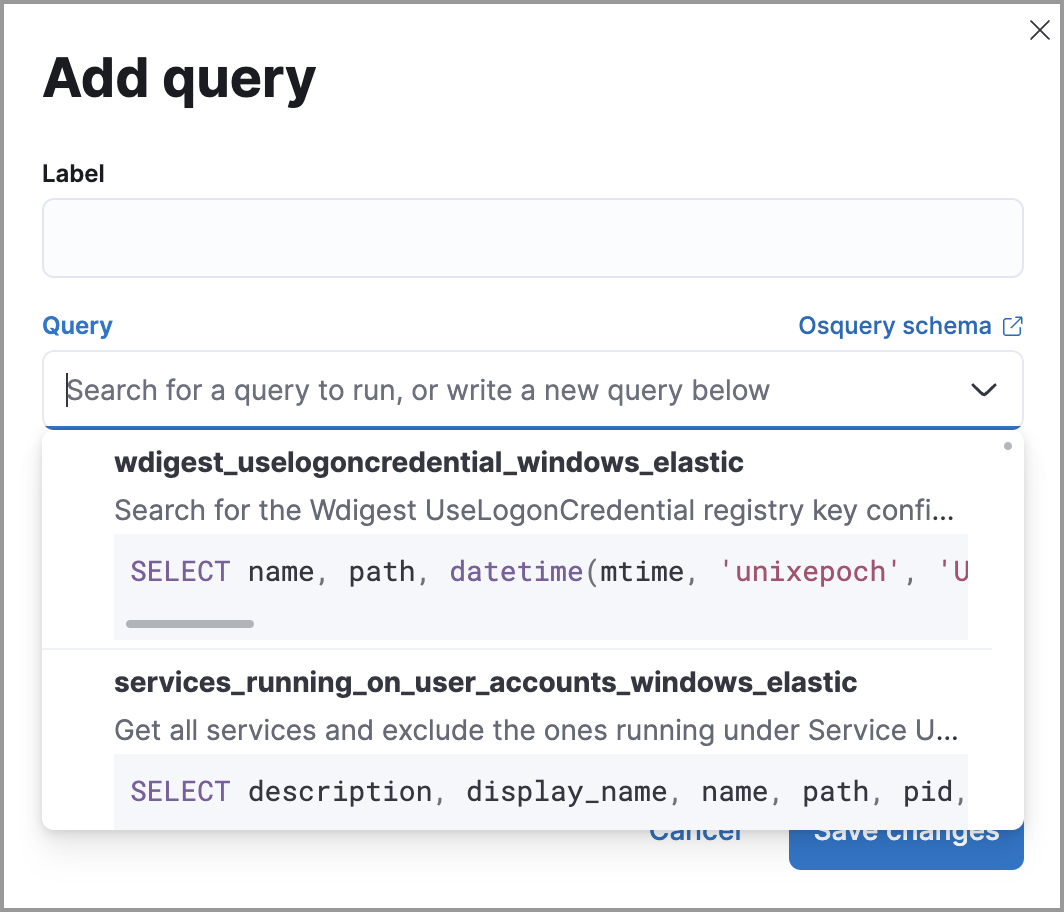
Click Save changes to add the query to the rule’s investigation guide.
Go to the Rules page. To access it, find Detection rules (SIEM) in the main menu or by using the global search field.
Select a rule to open the its details.
Go to Rules → Detection rules (SIEM), then select a rule to open its details.
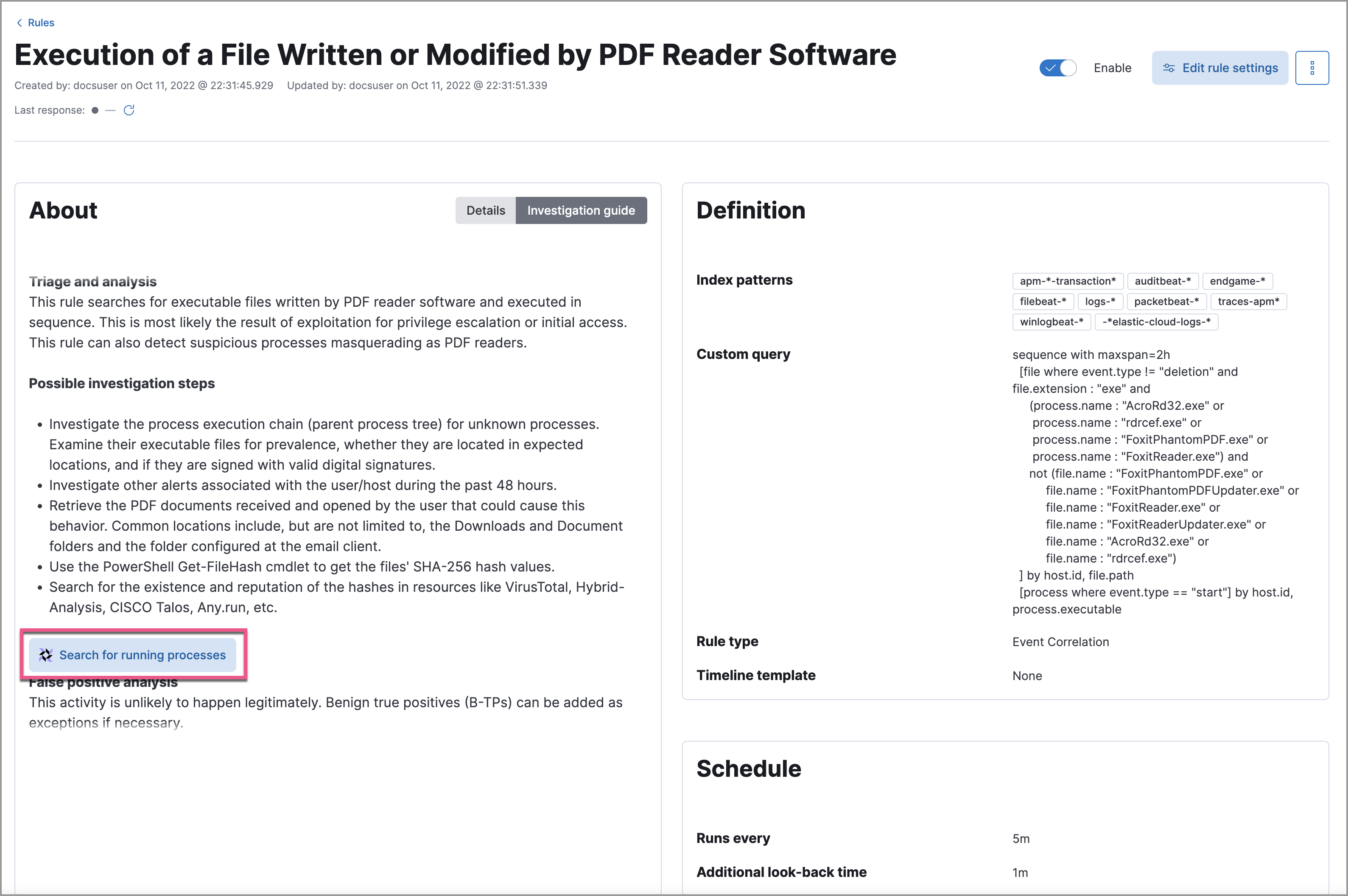
Go to the About section of the rule details page and click Investigation guide.
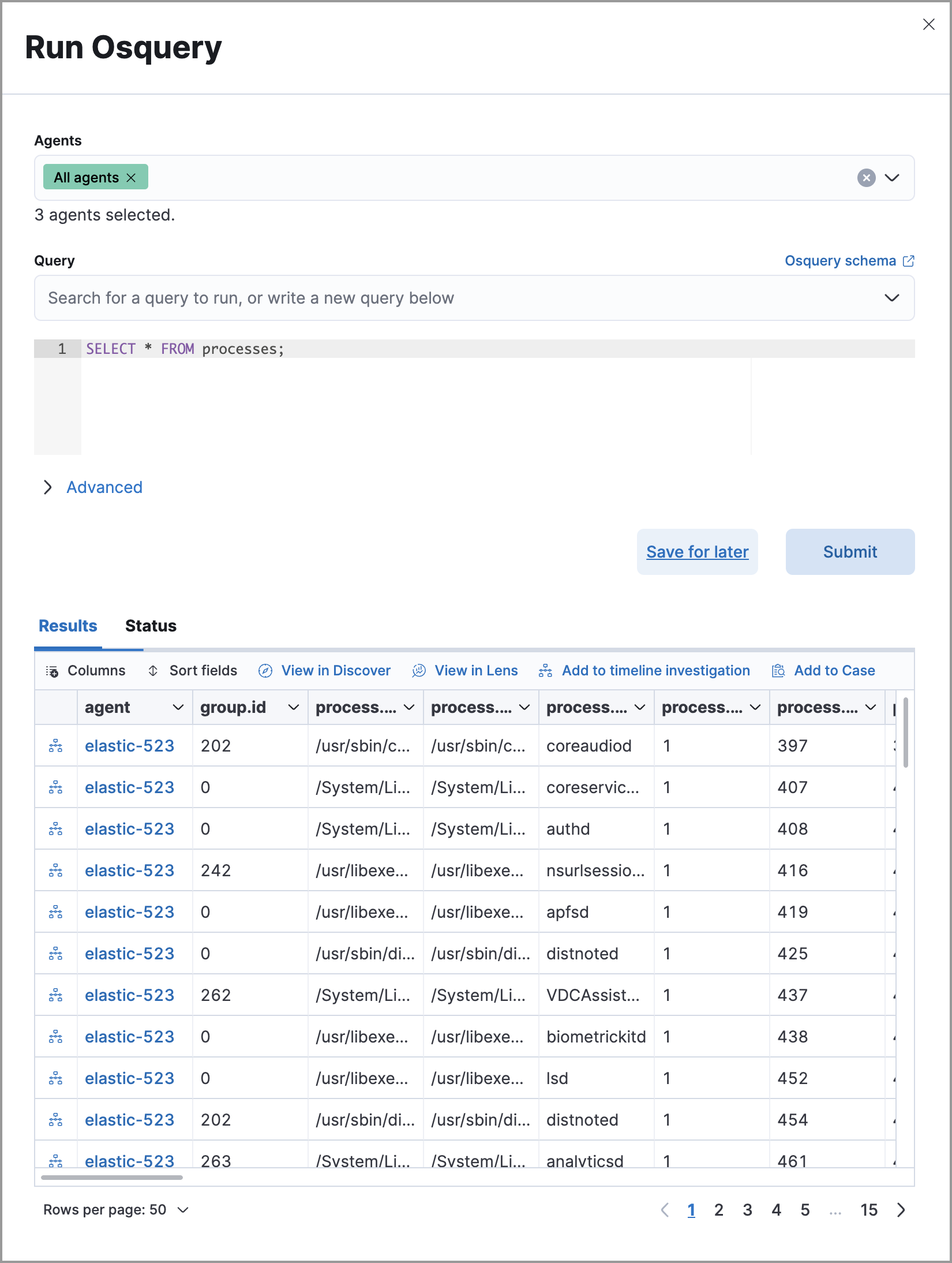
Click the query. The Run Osquery pane displays with the Query field autofilled. Do the following:
Select one or more Elastic Agents or groups to query. Start typing in the search field to get suggestions for Elastic Agents by name, ID, platform, and policy.
Expand the Advanced section to set a timeout period for the query, and view or set mapped ECS fields included in the results from the live query (optional).
NoteOverwriting the query’s default timeout period allows you to support queries that take longer to run. The default and minimum supported value for the Timeout field is
60. The maximum supported value is900.
Click Submit to run the query. Query results display in the flyout.
NoteRefer to Examine Osquery results for more information about query results.
Click Save for later to save the query for future use (optional).