Collect Logstash monitoring data for stack monitoring
Elastic Agent collects monitoring data from your Logstash instance and sends it directly to your monitoring cluster. With Elastic Agent collection the monitoring agent remains active even if the Logstash instance does not.
You can enroll Elastic Agent in Fleet for management from a central location, or you can run Elastic Agent standalone.
Prerequisites
Complete these steps as you prepare to collect and ship monitoring data for stack monitoring:
Set up Elasticsearch monitoring
To bind Logstash metrics to an Elasticsearch cluster, set up Elasticsearch monitoring. If you would like to create a dedicated monitoring cluster (optional), check out Elasticsearch monitoring documentation.
Disable default collection of Logstash monitoring metrics
Set monitoring.enabled to false in logstash.yml to disable default collection:
monitoring.enabled: false
Specify the target cluster_uuid (optional)
To bind the metrics of Logstash to a specific cluster, optionally define the monitoring.cluster_uuid in the configuration file (logstash.yml):
monitoring.cluster_uuid: PRODUCTION_ES_CLUSTER_UUID
Grant agent access to Elasticsearch (standalone agent only)
Minimal permissions required to send Logstash monitoring data to Elasticsearch:
monitorcluster privilegeauto_configureandcreate_docindex privileges onlogs-*andmetrics-*indices.
When you have completed the prerequisites, install and configure Elastic Agent to monitor host logs and metrics. We’ll walk you through the process in these steps:
- Add the Elastic Agent Logstash integration
- Install and run an Elastic Agent on your machine
- View assets
- Monitor Logstash logs and metrics (Stack Monitoring)
Check out Installing Elastic Agent in the Fleet and Elastic Agent Guide for more info.
Go to the Kibana home page, and click Add integrations.
In the query bar, search for Logstash and select the integration to see more details about it.
Click Add Logstash.
Configure the integration name and optionally add a description.
Configure the integration to collect logs.
- Make sure that Logs is turned on if you want to collect logs from your Logstash instance, ensuring that the required settings are correctly configured:
- Under Logs, modify the log paths to match your Logstash environment.
Configure the integration to collect metrics
TipFor the best experience with Stack Monitoring, we recommend collecting both
nodeandnode_stats. Turning off either of these will result in incomplete or missing visualizations.- Make sure that Metrics (Stack Monitoring) is turned on, and Metrics (Elastic Agent) is turned off, if you want to collect metrics from your Logstash instance.
- Under Metrics (Stack Monitoring), make sure the hosts setting points to your Logstash host URLs. By default, the integration collects Logstash monitoring metrics from
localhost:9600. If that host and port number are not correct, update thehostssetting. If you configured Logstash to use encrypted communications, you must access it via HTTPS. For example, use ahostssetting likehttps://localhost:9600.
Choose where to add the integration policy.
Click New hosts to add it to new agent policy or Existing hosts to add it to an existing agent policy.In the popup, click Add Elastic Agent to your hosts to open the Add agent flyout.
TipIf you accidentally close the popup, go to Fleet > Agents, then click Add agent to access the flyout.
The Add agent flyout has two options: Enroll in Fleet and Run standalone. Enrolling agents in Fleet (default) provides a centralized management tool in Kibana, reducing management overhead.
When the Add Agent flyout appears, stay on the Enroll in fleet tab.
Skip the Select enrollment token step. The enrollment token you need is already selected.
NoteThe enrollment token is specific to the Elastic Agent policy that you just created. When you run the command to enroll the agent in Fleet, you will pass in the enrollment token.
Download, install, and enroll the Elastic Agent on your host by selecting your host operating system and following the Install Elastic Agent on your host step.
It takes about a minute for Elastic Agent to enroll in Fleet, download the configuration specified in the policy you just created, and start collecting data.
- When the Add Agent flyout appears, navigate to the Run standalone tab.
- Configure the agent. Follow the instructions in Install Elastic Agent on your host.
- After unpacking the binary, replace the
elastic-agent.ymlfile with that supplied in the Add Agent flyout on the "Run standalone" tab, replacing the values ofES_USERNAMEandES_PASSWORDappropriately. - Run
sudo ./elastic-agent install
After you have confirmed enrollment and data is coming in, click View assets to access dashboards related to the Logstash integration.
For traditional Stack Monitoring UI, the dashboards marked [Logs Logstash] are used to visualize the logs produced by your Logstash instances, with those marked [Metrics Logstash] for metrics dashboards. These are populated with data only if you selected the Metrics (Elastic Agent) checkbox.
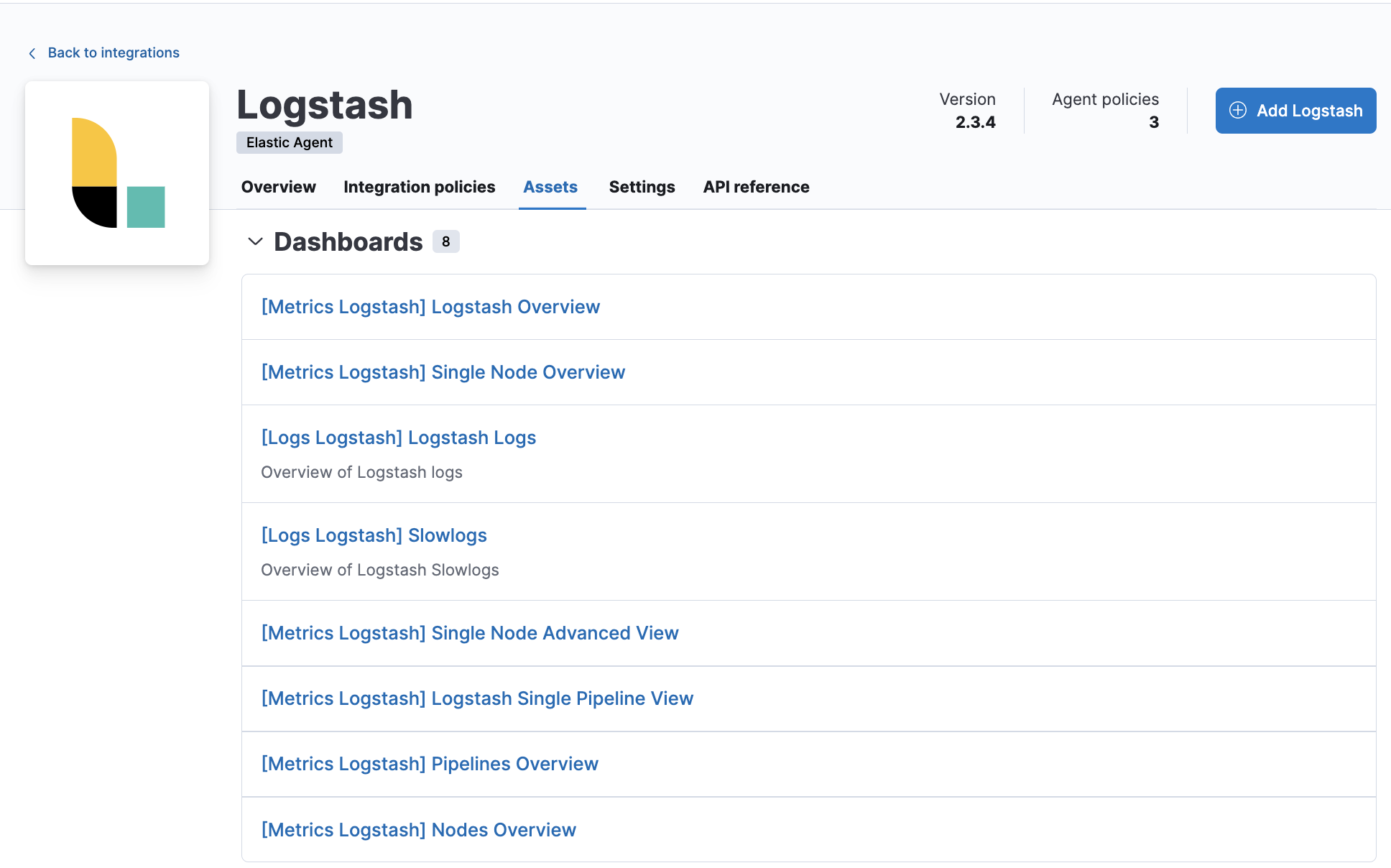
A number of dashboards are included to view Logstash as a whole, and dashboards that allow you to drill-down into how Logstash is performing on a node, pipeline and plugin basis.
View the monitoring data in Kibana, and navigate to the monitoring UI.