API keys
editAPI keysedit
API keys are sent as plain-text, so they only provide security when used in combination with TLS.
Enable API key authorization in the APM integration configuration panel. When enabled, API keys are used to authorize requests to the APM Server.
You can assign one or more unique privileges to each API key:
-
Agent configuration (
config_agent:read): Required for agents to read Agent configuration remotely. -
Ingest (
event:write): Required for ingesting agent events.
To secure the communication between APM Agents and the APM Server with API keys, make sure TLS is enabled, then complete these steps:
Enable API keysedit
Enable API key authorization in the APM integration configuration panel. You should also set a limit on the number of unique API keys that APM Server allows per minute; this value should be the number of unique API keys configured in your monitored services.
Create an API key user in Kibanaedit
API keys can only have the same or lower access rights than the user that creates them. Instead of using a superuser account to create API keys, you can create a role with the minimum required privileges.
The user creating an APM agent API key must have at least the manage_own_api_key cluster privilege
and the APM application-level privileges that it wishes to grant.
The example below uses the Kibana role management API
to create a role named apm_agent_key_role.
POST /_security/role/apm_agent_key_role
{
"cluster": ["manage_own_api_key"],
"applications": [{
"application": "apm",
"privileges": ["event:write", "config_agent:read"],
"resources": ["*"]
}]
}
Assign the newly created apm_agent_key_role role to any user that wishes to create APM agent API keys.
Create an API key in Kibanaedit
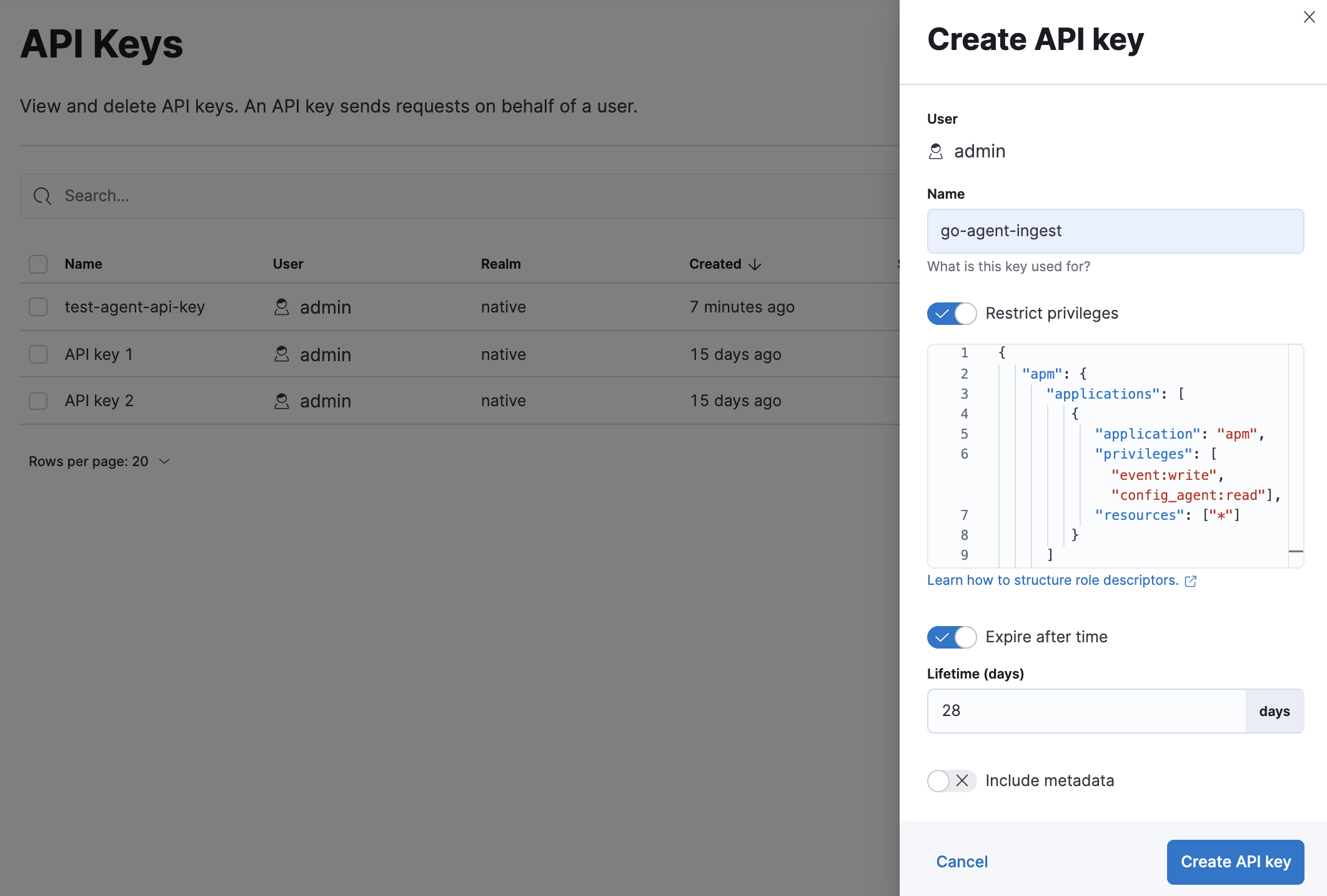
Using a superuser account, or a user with the role created in the previous step, open Kibana and navigate to Stack Management > API keys and click Create API key.
Enter a name for your API key and select Restrict privileges. In the role descriptors box, copy and paste the following JSON. This example creates an API key with privileges for ingesting APM events and reading agent central configuration:
{
"apm": {
"applications": [
{
"application": "apm",
"privileges": ["event:write", "config_agent:read"],
"resources": ["*"]
}
]
}
}
|
This example adds both API privileges to the new API key. Privileges are described above. Remove any privileges that you do not need. |
To set an expiration date for the API key, select Expire after time and input the lifetime of the API key in days.
Click Create API key and then copy the Base64 encoded API key. You will need this for the next step, and you will not be able to view it again.
Set the API key in your APM agentsedit
You can now apply your newly created API keys in the configuration of each of your APM agents. See the relevant agent documentation for additional information: