SIEM & Security Analytics
Elastic Security for SIEM & security analytics
Detect, investigate, and respond to evolving threats. Harness data at cloud speed and scale. Heighten host visibility and control. Modernize security with a unified, open SIEM solution.
SIEM & security analytics capabilities
Experience end-to-end security information and event management (SIEM).
Establish a holistic view
Centralize environmental activity and internal and external context. Enable uniform analysis with Elastic Common Schema (ECS). Add new data with one-click integrations, community-built plug-ins, and simple custom connectors.
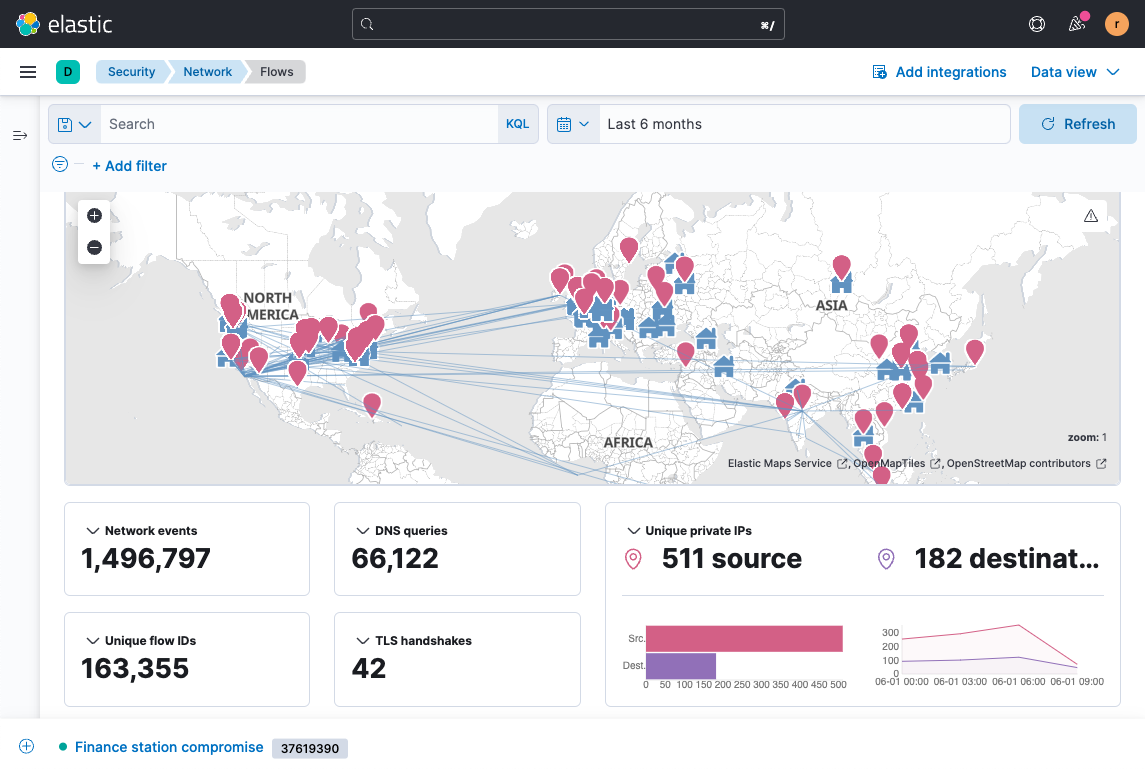
Analyze your environment at will
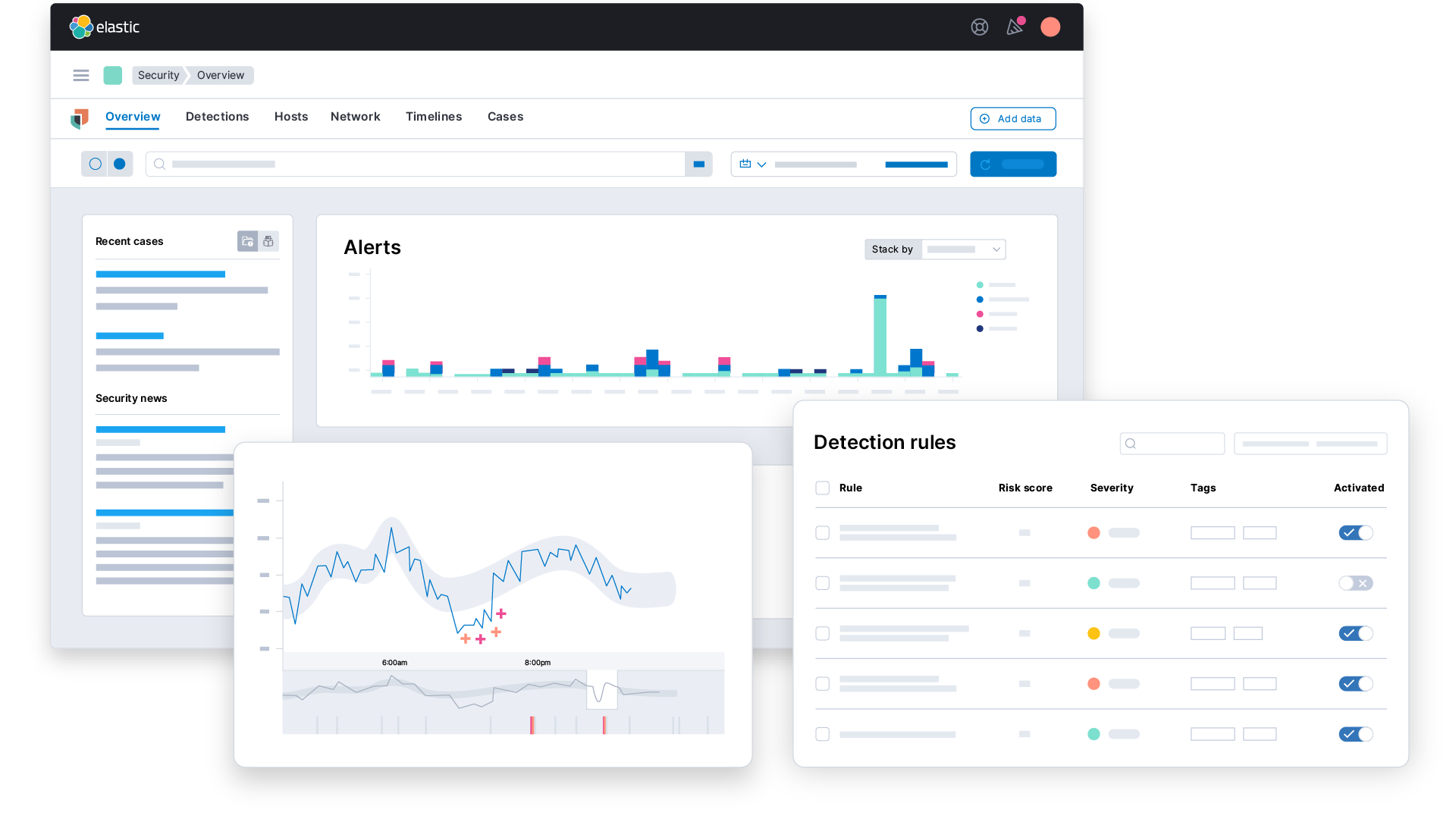
Interactively monitor years of historical data — without breaking your budget. Quickly grasp unfolding attacks by correlating all relevant data. Throughout the UI, access built-in trend charts for key data fields. And do it all with the only SIEM fast enough for the quickest analysts.
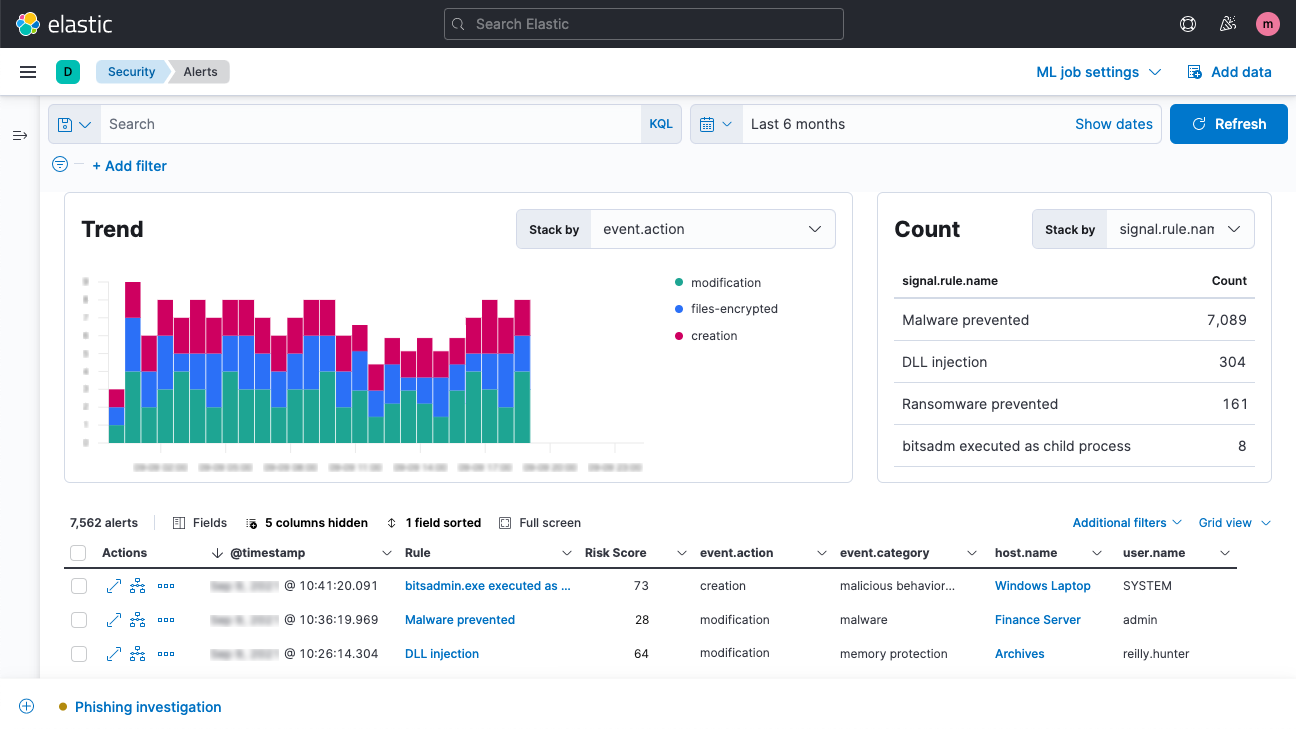
Automate detection with high-fidelity rules
Automate detection of suspicious activity and tools with behavior-based rules powered by research from Elastic Security Labs. Analyze adversary behavior and prioritize potential threats accordingly. Cut to what matters with risk and severity scores. Detections are aligned with MITRE ATT&CK® and shared openly for review and activation.
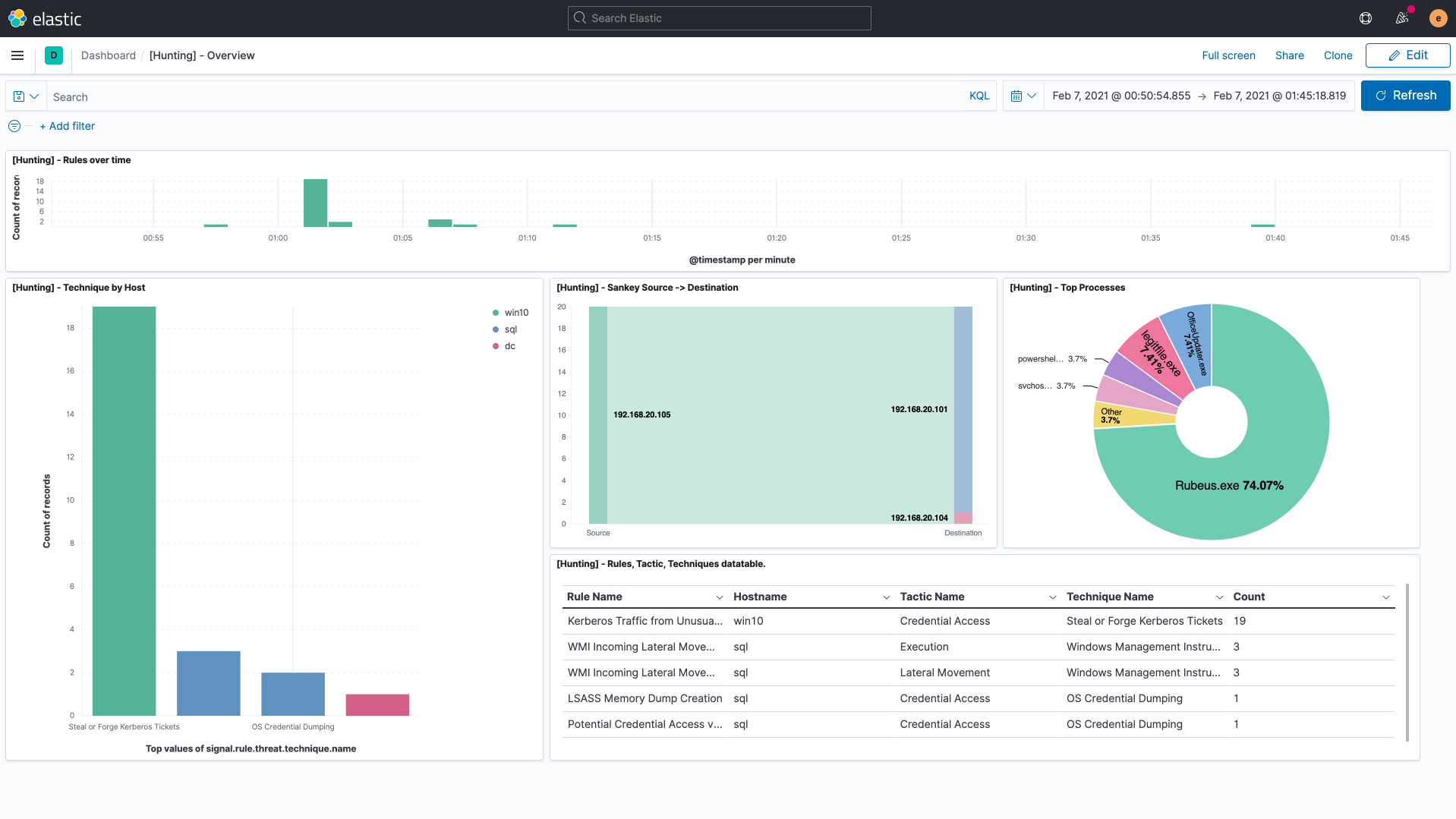
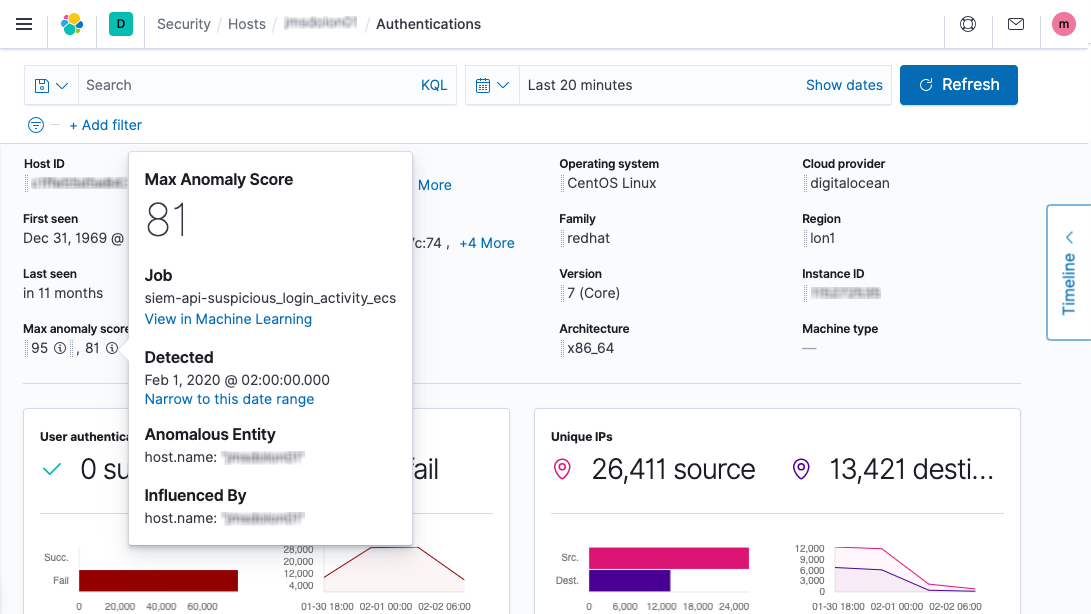
Assess risk with ML and entity analytics
Expose unknown threats with anomaly detection powered by prebuilt ML jobs. Arm threat hunters with evidence-based hypotheses. Uncover threats you expected — and others you didn’t. Gain insight into the entities at highest risk with security analytics.
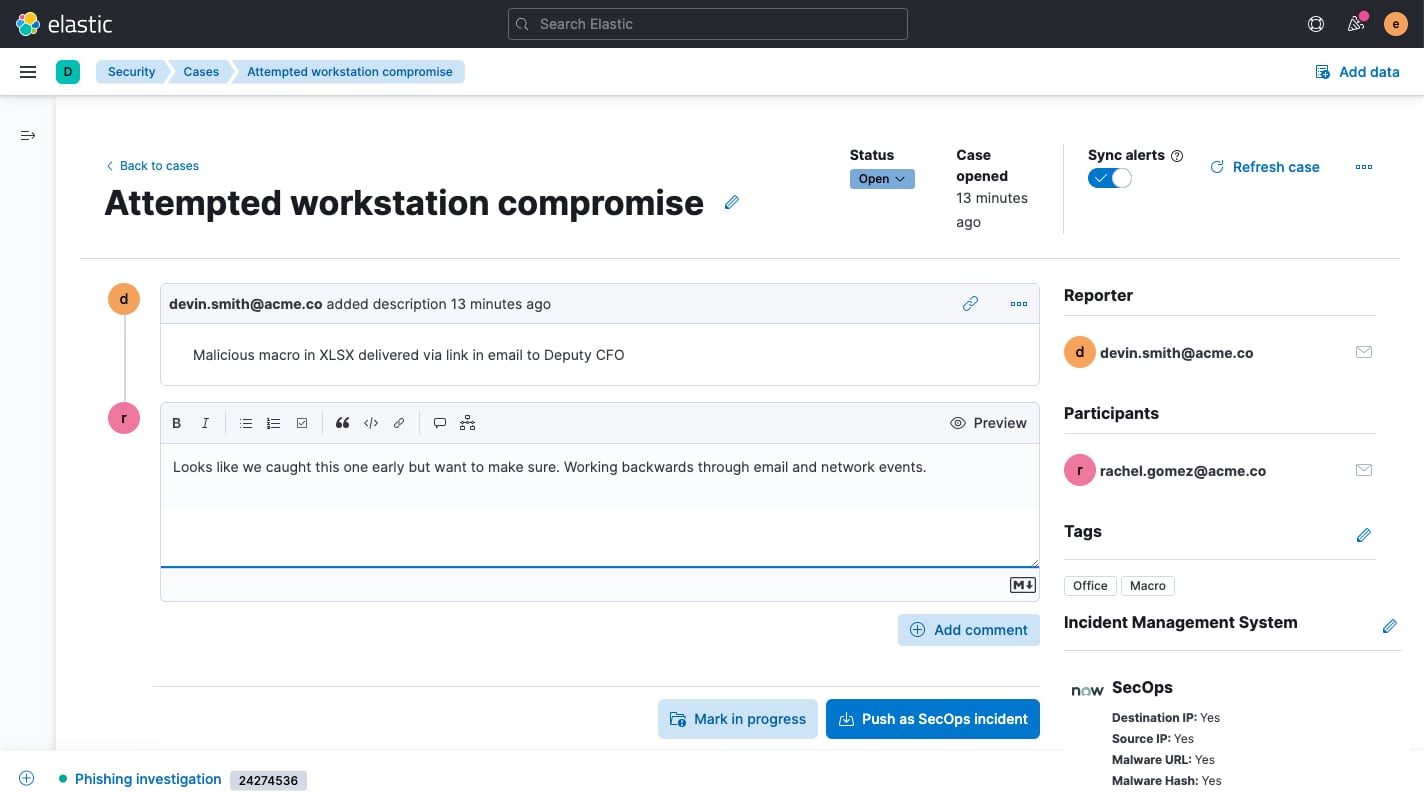
Streamline investigation, automate response
Enrich alerts and glean insights with threat intelligence. Accelerate workflows with native security orchestration, automation, and response (SOAR). Quickly and iteratively hunt with piped queries. Gather findings on an interactive timeline. Remotely inspect and invoke actions on distributed endpoints. Maintain momentum with generative AI and bidirectional workflow integrations.