Log Monitoring
Scalable, centralized log monitoring for hybrid cloud
As the recognized leader in log monitoring, with the broadest and most comprehensive set of log data sources in the industry, the Elastic Stack (also known as the ELK Stack) is the most popular free and open logging platform.
Learn how to ingest, view, and analyze custom logs from your applications using Elastic Cloud.
Get startedSee why Cerner depends on Elastic machine learning for a healthy infrastructure.
Learn moreMigrating from Splunk? Here's an easy way to get data into Elastic quickly.
Learn moreDeploy and manage logs at petabyte scale
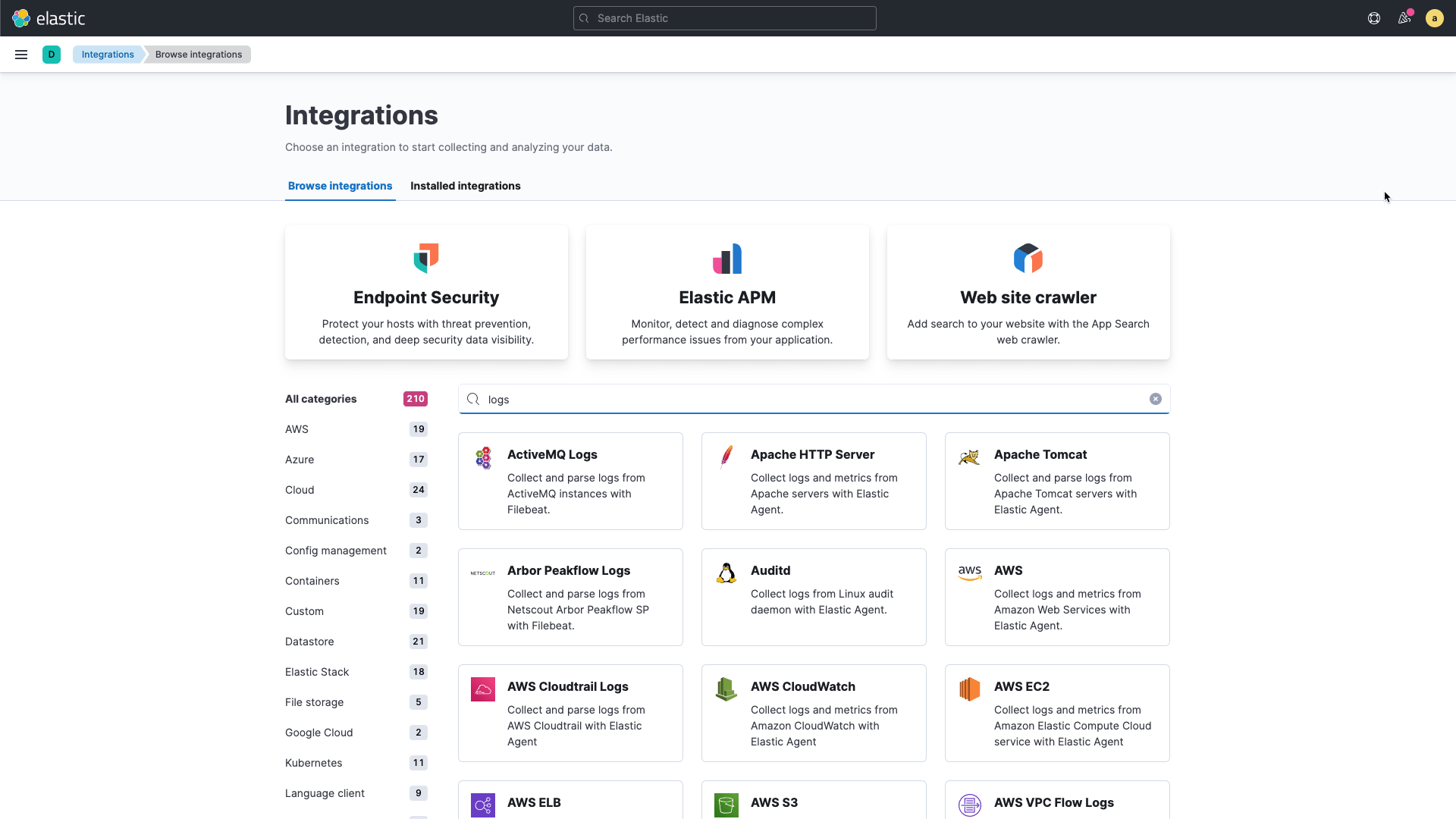
Elastic Agent makes it fast and easy to deploy log monitoring. Broad log data source support unifies application data with infrastructure data for context. Out-of-the-box support for common data sources helps you ship and visualize cloud services logs from Amazon, Microsoft Azure, and Google Cloud Platform and cloud-native technologies in minutes.
Get insights for structured and unstructured logs in minutes
Turn unstructured data into a valuable asset by parsing, transforming, and enriching logs for use cases for all teams and every technology stack irrespective of source. Improve query performance of your structured log data with schema on write, or take advantage of the benefits of schema on read with runtime fields to extract, calculate, and transform fields at query time.

Search across everything with search that scales with you
Eliminate all blind spots by ingesting all telemetry data without missing critical data needed to solve problems. Uniform data modeling with the Elastic Common Schema (ECS) means you can normalize all data and centrally analyze all your data from diverse sources. Search all your data across your data centers and cloud from a single console with powerful cross-cluster search.

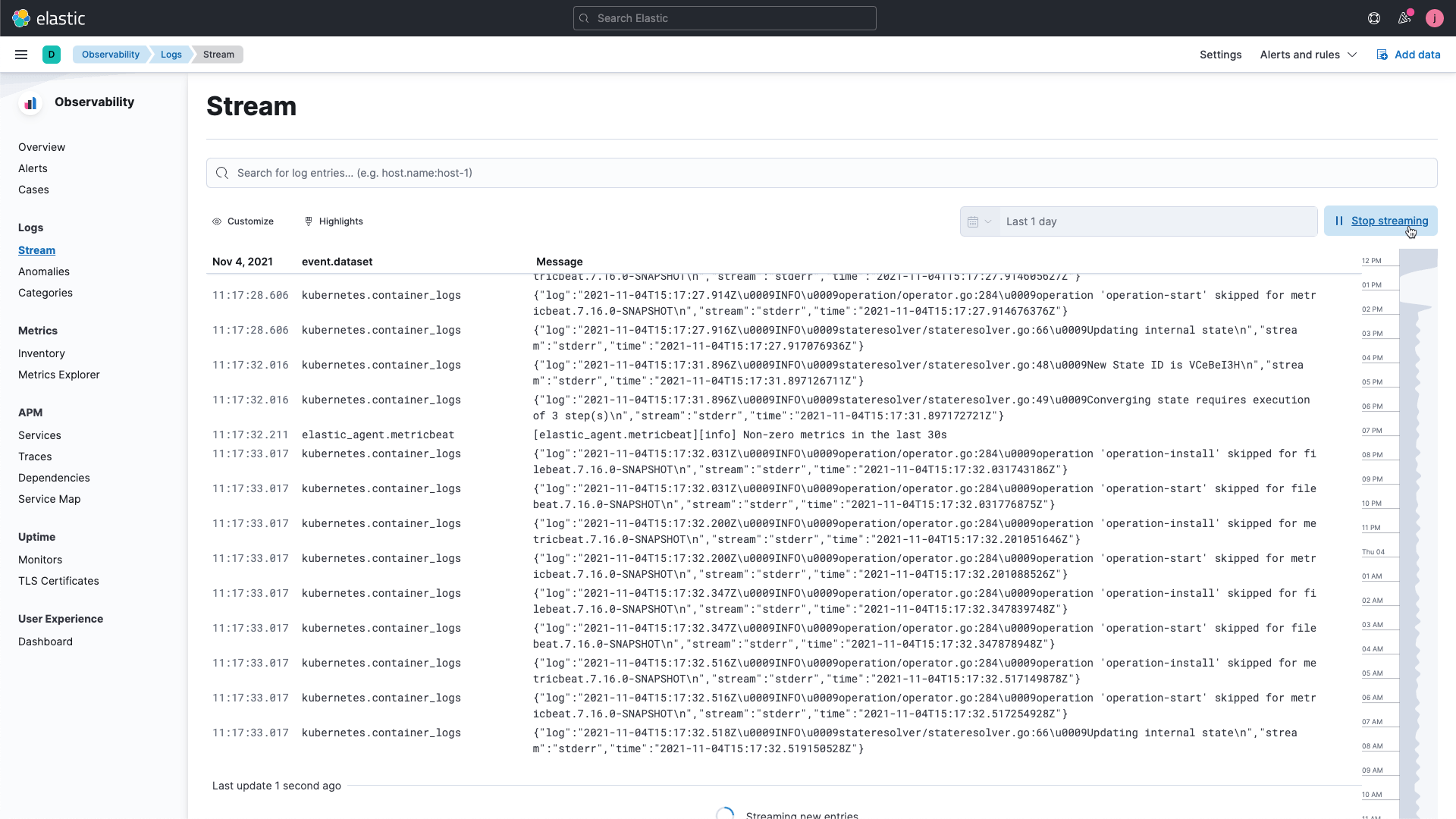
Real-time troubleshooting with live tail
Keep a pulse of all log files flowing in from your servers, virtual machines, and containers in a purpose-built and intuitive interface for viewing logs. Pin structured fields and explore related logs without leaving your current screen. Dive into your real-time streaming logs in Kibana for a console-like experience.
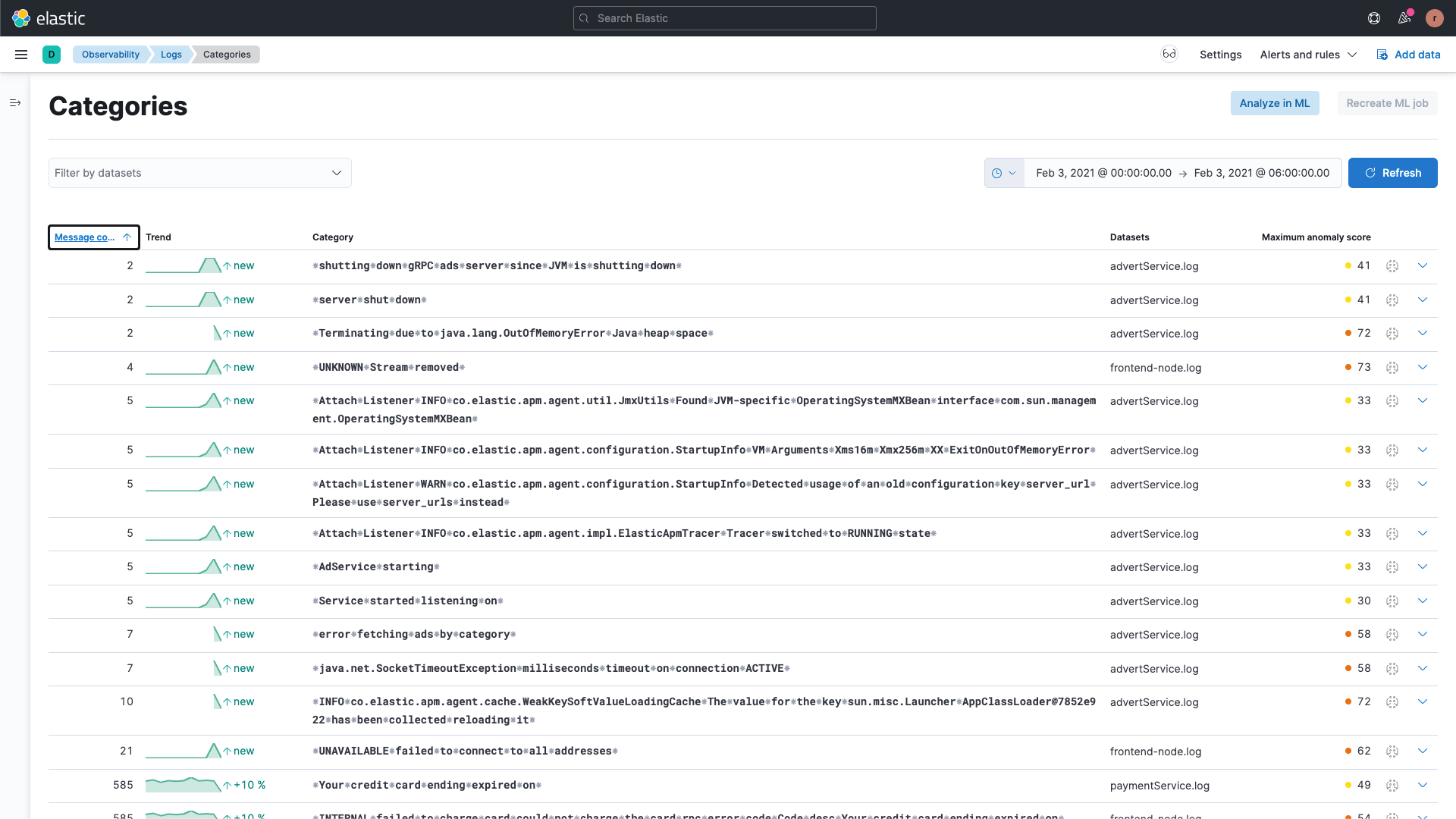
Detect patterns and outliers with log categorization and anomaly detection
Identify common patterns, trends, and outliers to help isolate performance and availability problems. Automatic out-of-the-box machine learning is applied to every log message for quick detection and correlation. Resolve your application problems faster than ever.