Overviewedit
This functionality is in beta and is subject to change. The design and code is less mature than official GA features and is being provided as-is with no warranties. Beta features are not subject to the support SLA of official GA features.
SIEM enables analysis of host-related and network-related security events as part of alert investigations or interactive threat hunting.
The SIEM app in Kibana provides an interactive workspace for security teams to triage events and perform initial investigations.
SIEM componentsedit
SIEM requires the following Elastic Stack components.
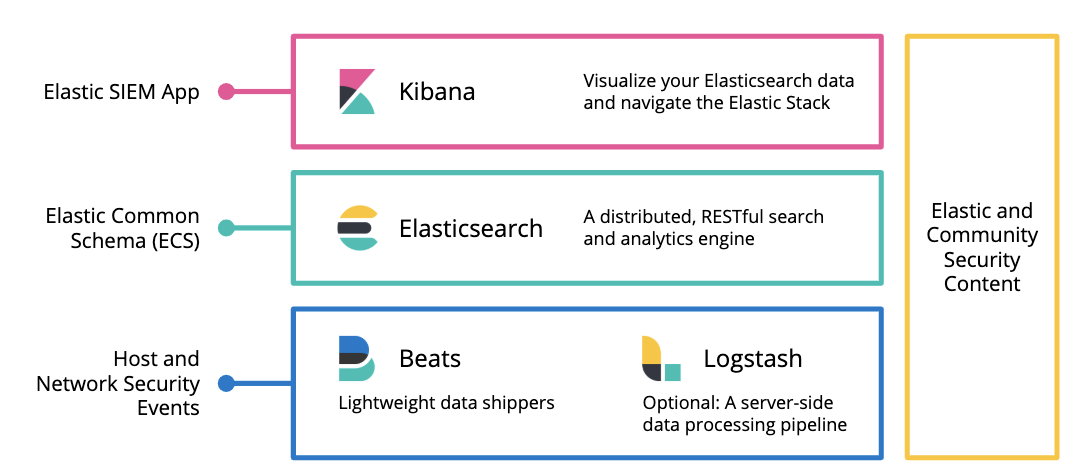
Beats are open source data shippers that you install as agents on your systems. Beats send security events and other data to Elasticsearch.
Elasticsearch is a real-time, distributed storage, search, and analytics engine. Elasticsearch excels at indexing streams of semi-structured data, such as logs or metrics.
Kibana is an open source analytics and visualization platform designed to work with Elasticsearch. You use Kibana to search, view, and interact with data stored in Elasticsearch indices. You can easily perform advanced data analysis and visualize your data in a variety of charts, tables, and maps.
The SIEM app in Kibana provides a dedicated user interface for analyzing and investigating host and network security events.
Additional Elastic componentsedit
You can use SIEM with other Elastic products and features to help you identify and investigate suspicious activity:
Data sourcesedit
SIEM can ingest and analyze data from a variety of sources, including Beats and Beats modules, and third-party collectors mapped to the Elastic Common Schema (ECS).
Hosts data sourcesedit
-
-
System module - Linux, macOS, Win
- packages
- processes
- logins
- sockets
- users and groups
- Auditd module (Linux Kernel Audit info)
- File integrity module (FIM) - Linux, macOS, Win
-
-
- system logs (auth logs) - Linux
- Santa - macOS
-
- Windows event logs - Windows
Network data sourcesedit
-
- Flows
- DNS
- other protocols
Elastic Common Schema (ECS) for normalizing dataedit
The Elastic Common Schema (ECS) defines a common set of fields to be used for storing event data in Elasticsearch. ECS helps users normalize their event data to better analyze, visualize, and correlate the data represented in their events.
SIEM can ingest and normalize events from ECS-compatible data sources.
Host identificationedit
All Beats use the add_host_metadata processor to add the host.name field to
events. The default value is host.name, but you can change it in Beats
processor settings.