Elastic Security UI
editElastic Security UI
editThe Elastic Security app is a highly interactive workspace designed for security analysts. It provides a clear overview of events and alerts from your environment, and you can use the interactive UI to drill down into areas of interest.
Search
editFilter for alerts, events, processes, and other important security data with the benefit of Kibana Query Language (KQL) in the Search bar, which appears at the top of each page throughout the app. A date/time filter set to Last 24 hours is enabled by default, but can be changed to any time range. If you want to filter your search results with other fields, select Add Filter, followed by the field from which to filter and the operator (such is not or is between) for your query.
To save specific filters and queries, click the Save button, then Save current query.
Page navigation
editThe Elastic Security app contains the following pages that enable analysts to view, analyze, and manage security data:
- Overview
- Alerts
- Rules
- Exceptions
- Hosts
- Network
- Timelines
- Cases
- Endpoints
- Trusted applications
- Event filters
- Host isolation exceptions
Pages are grouped into four main sections within the navigation pane — Detect, Explore, Investigate, and Manage. Each section supports a different part of your workflow and describes actions you can perform in the Elastic Security app.
From the Detect section, you can access pages that allow you to view, create, and manage alerts, rules, and rule exceptions.
Under Explore, you access pages that provide key metrics about your hosts and networks.
The Investigate section gives you access to timelines and cases.
Pages under the Manage section allow to view and manage hosts that are running Endpoint Security. You can also view and manage trusted applications and event filters from pages in this section.
Click the Collapse side navigation button to collapse and expand the main navigation menu.
Overview page
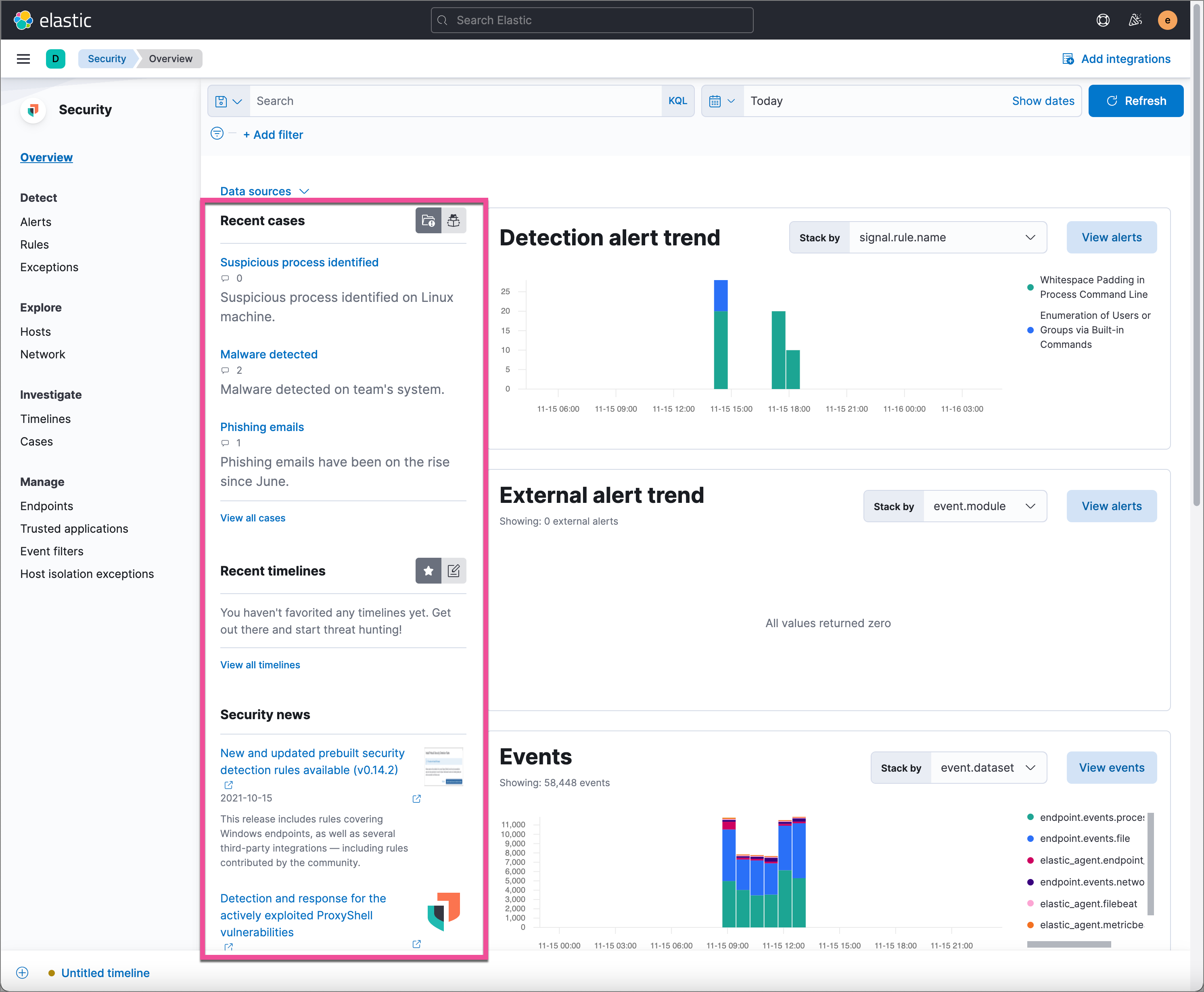
editThe Overview page provides a high-level snapshot view of detections, external alerts, and event trends. These trends are useful to assess overall system health and find anomalies that may require further investigation.
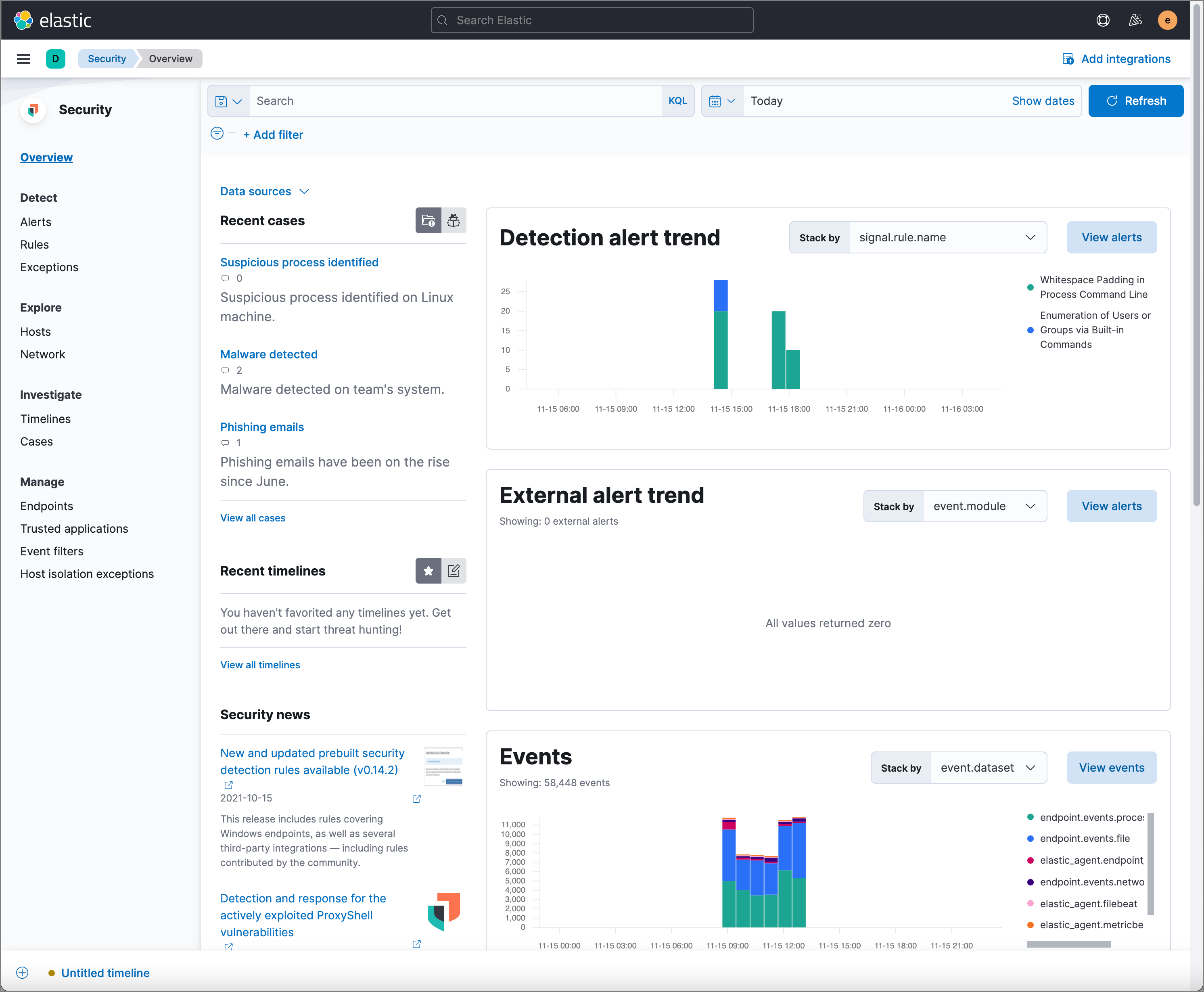
From the live feed on the Overview page, you can quickly access recently created cases, favorited timelines, and the latest Elastic Security news.
The Security news section provides you with the latest Elastic Security news so you can stay informed on new developments, learn about Elastic Security features, and more.
Histograms
Time-based histograms show you the number of detections, alerts, and events that have occurred within the selected time range. You can select areas of interest in time-based histograms by selecting a region to reflect a date range, or by selecting a preset value in the timepicker. In the Stack by dropdown, you can select specific parameters for which to visualize the individual counts. For example, in the Detection alert trend histogram, stack by signal.rule.name to display the total counts by alert name within the specified time frame.
All Elastic Security histograms, graphs, and tables contain an Inspect button so you can examine the Elasticsearch queries used to retrieve data throughout the app.
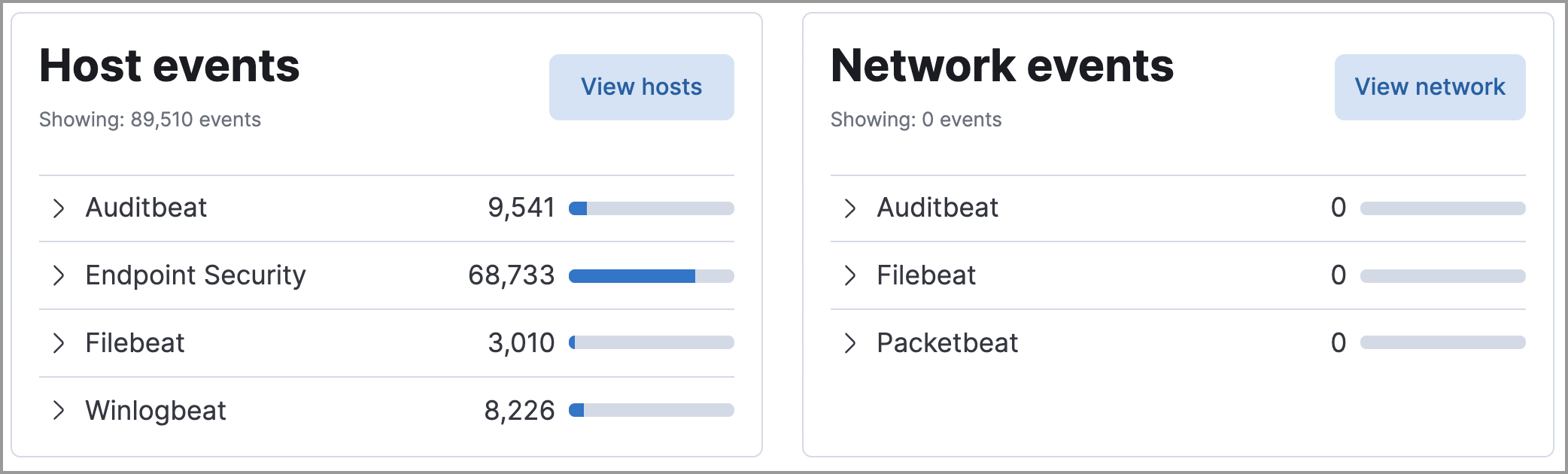
Host and network events
View event and host counts specific to Elastic data shippers and apps, such as Auditbeats or Elastic Endpoint Security. Expand each category to view specific counts of hosts or network events related to the selected category.
Threat Intelligence
The Threat Intelligence view shows the total number of threat indicator events collected by the Threat Intel Filebeat module. This module ingests, parses, and visualizes data from several open source threat feeds to provide you with relevant and timely threat intelligence. As a security analyst, you can use this data in a variety of ways. For example, you can reference this data while building new threat indicator match rules or triaging alerts. Or, you use it to assess the robustness of your organization’s security controls and make suggestions for improvements. Regardless of your goal, the Threat Intel Filebeat module offers you timely and actionable threat intelligence that you can leverage for your, or your organization’s, detection and prevention needs.
The Threat intelligence view queries indices specified in the securitySolution:defaultThreatIndex advanced setting. For more information, see Update default Elastic Security threat intelligence indices.
To open a full view of the Threat Intel Filebeat module, click View dashboard. To further inspect data from the ingested threat intelligence sources, click Source for the appropriate source.
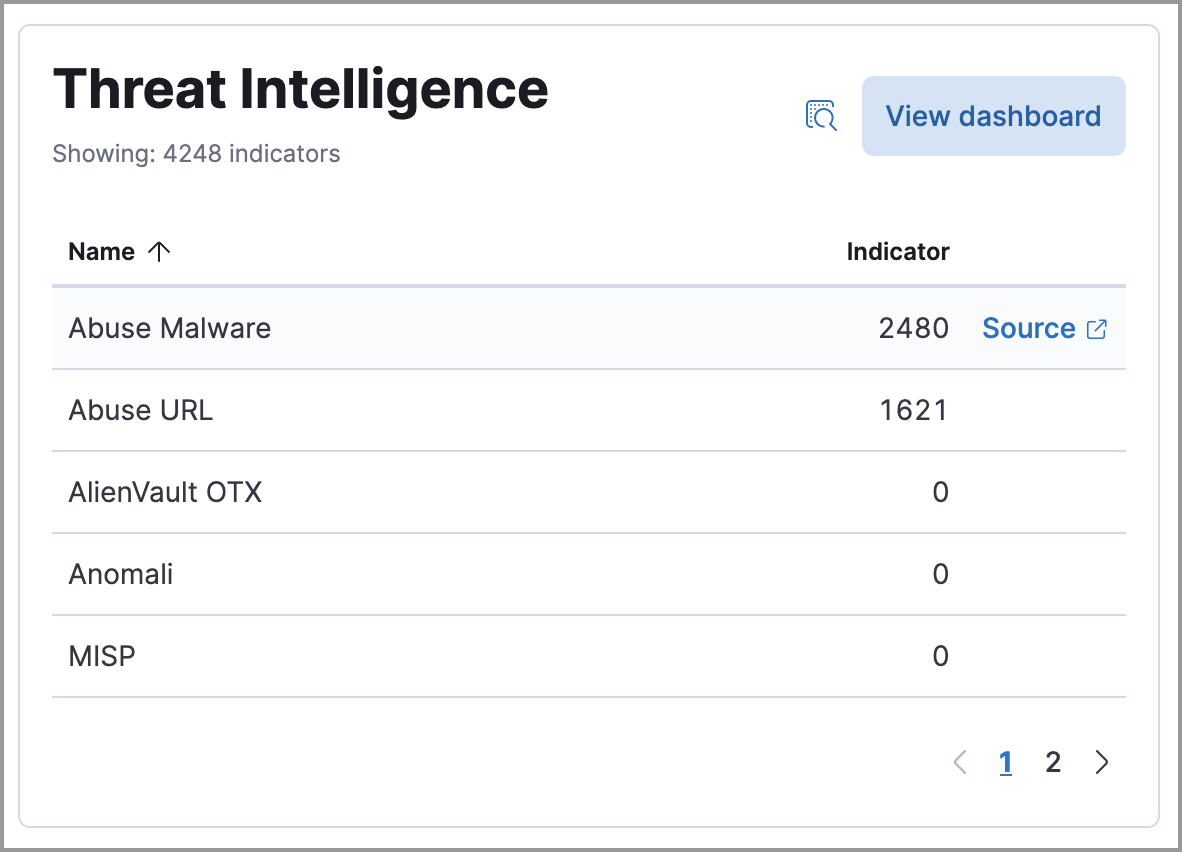
There are a few scenarios when data won’t display in the Threat Intelligence view:
- If you’ve chosen a time range that doesn’t contain threat indicator event data, you’ll be prompted to choose a different range. Use the the date and time picker in the Elastic Security app or Kibana to select a new range to analyze.
- If the Filebeat agent hasn’t ingested Threat Intel Filebeat module data yet, the View dashboard button greys out and threat indicator event counts won’t load. You can wait for data to generate or reach out to your administrator for help resolving this.
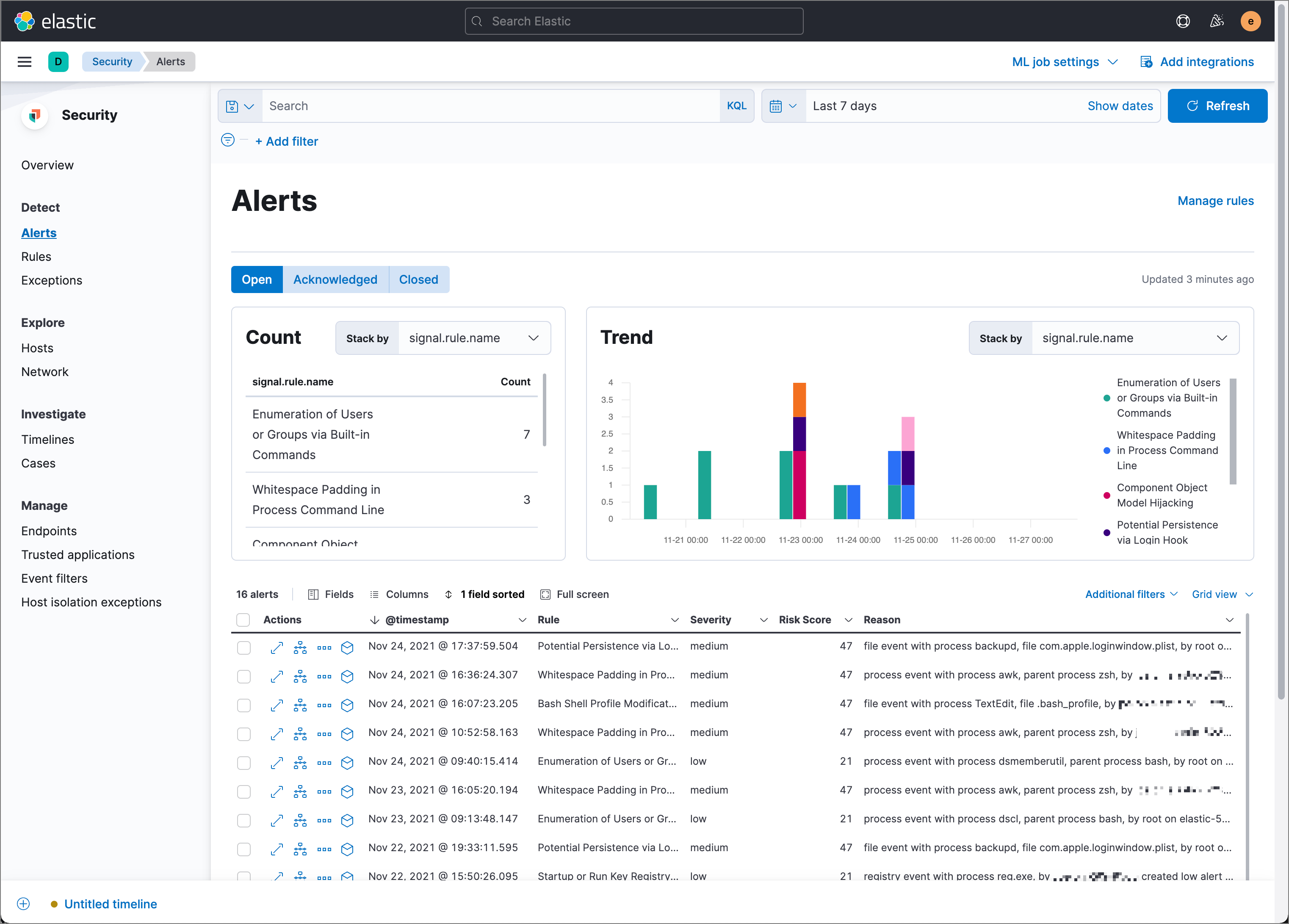
Alerts page
editThe Alerts page allows you to view and manage all alerts to monitor activity within your network. See Detections and Alerts for more information.
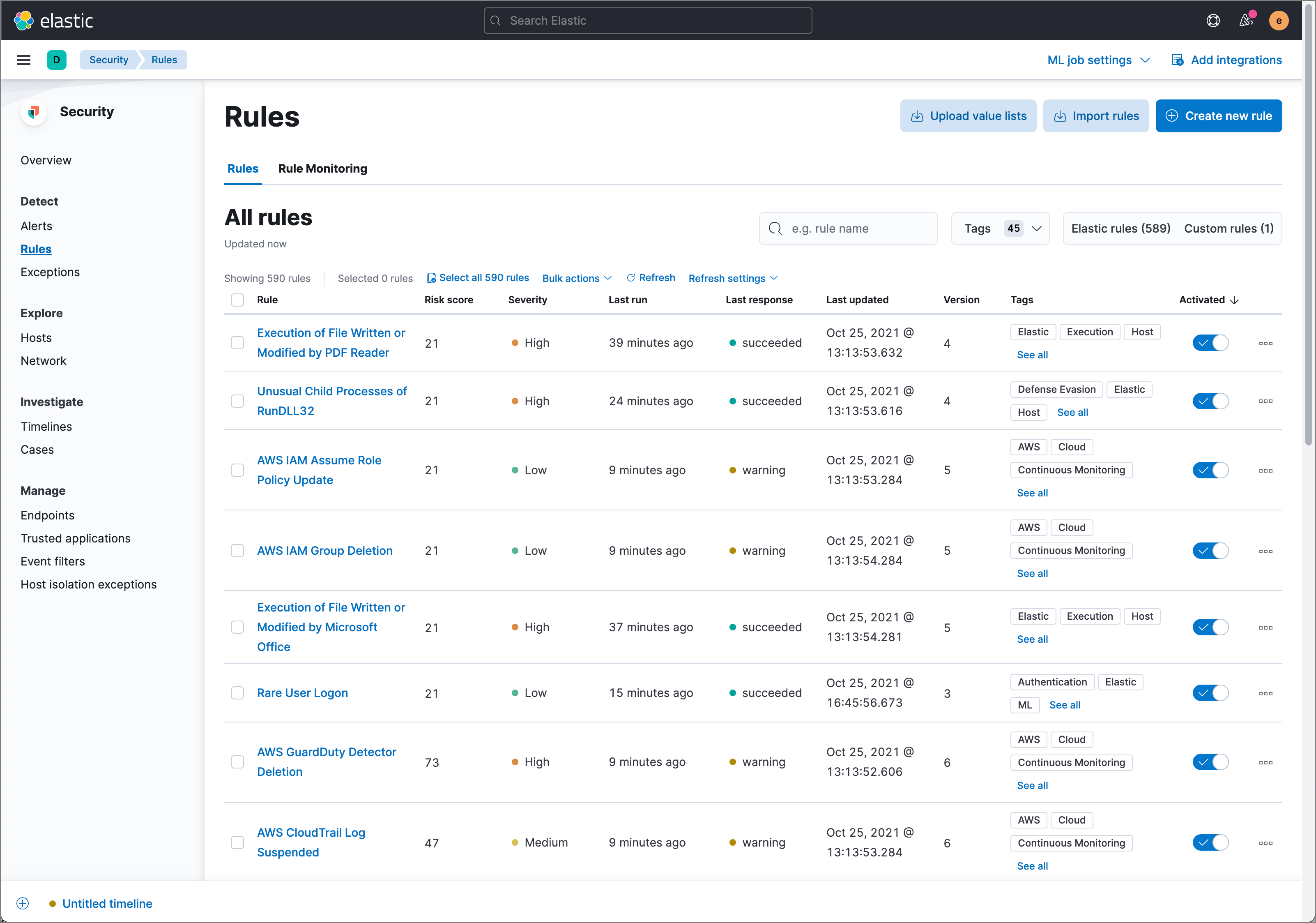
Rules page
editThe Rules page allows you to view and manage all detection rules. See Manage detection rules for more information about prebuilt and custom rules.
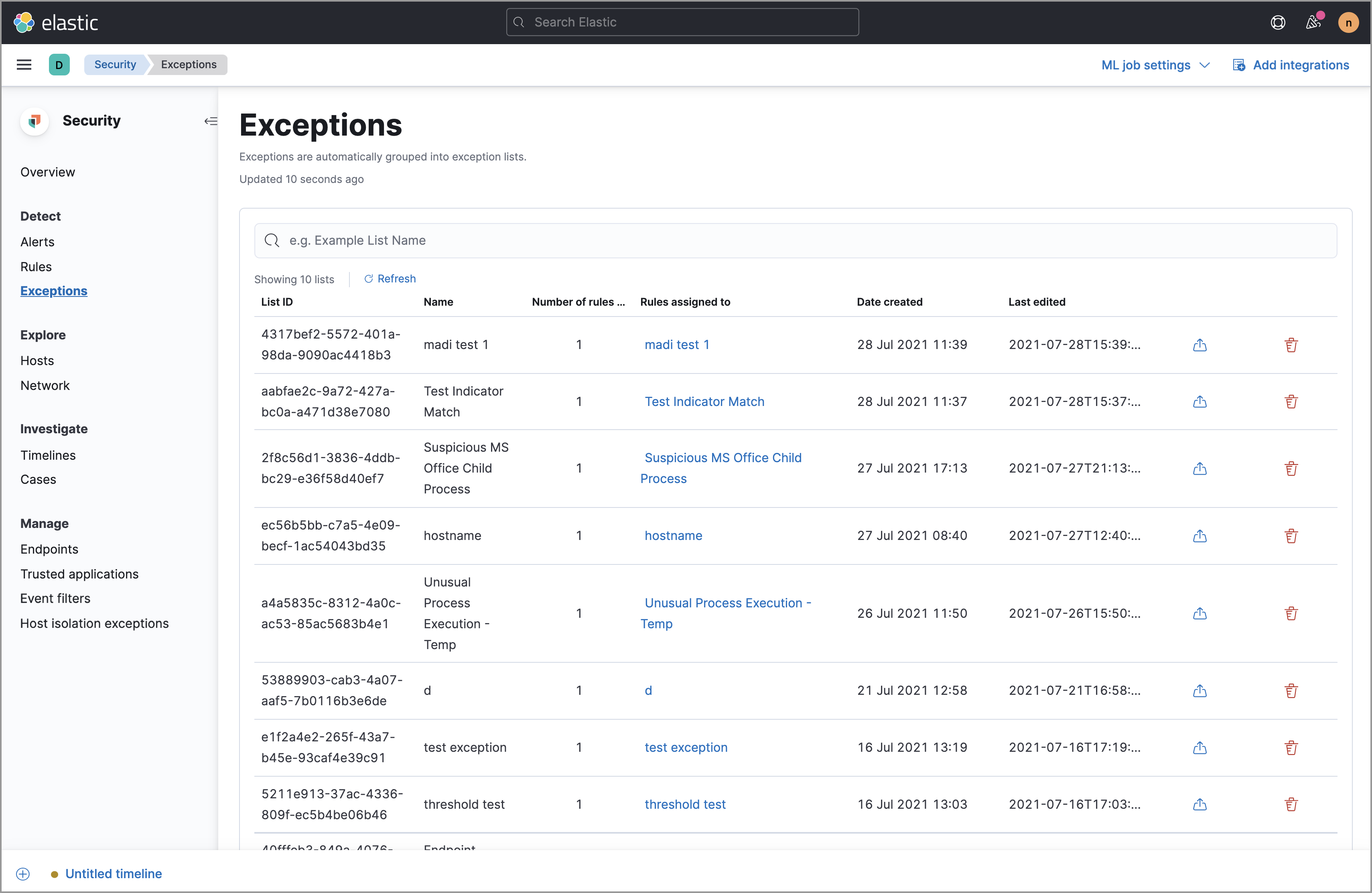
Exceptions page
editThe Exceptions page allows you to view and manage all rule exceptions. See Rule exceptions and value lists for more information about rule exceptions.
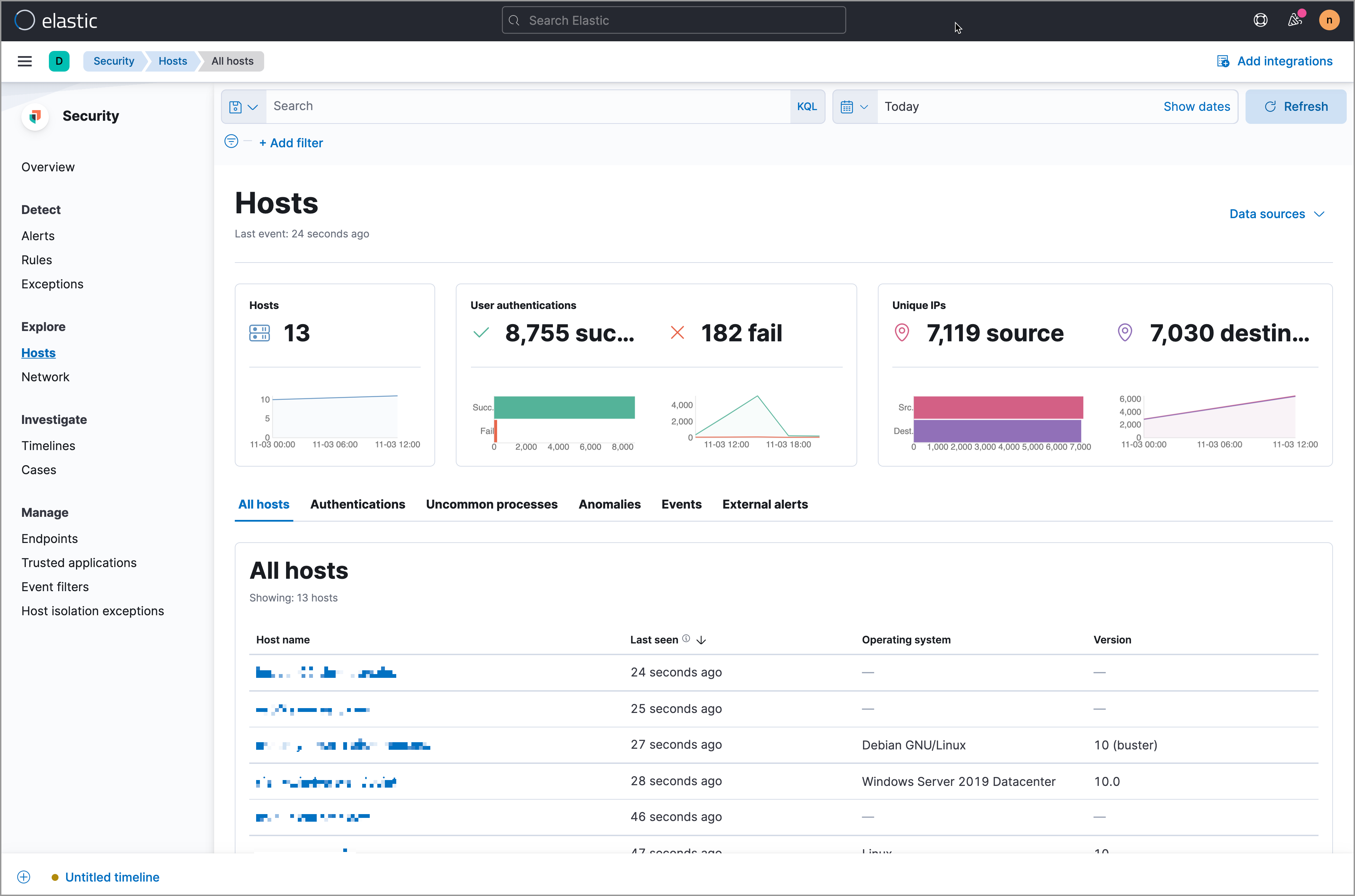
Hosts page
editThe Hosts view provides key metrics regarding host-related security events, and a set of data tables that let you interact with Timeline. See Hosts page overview for more information.
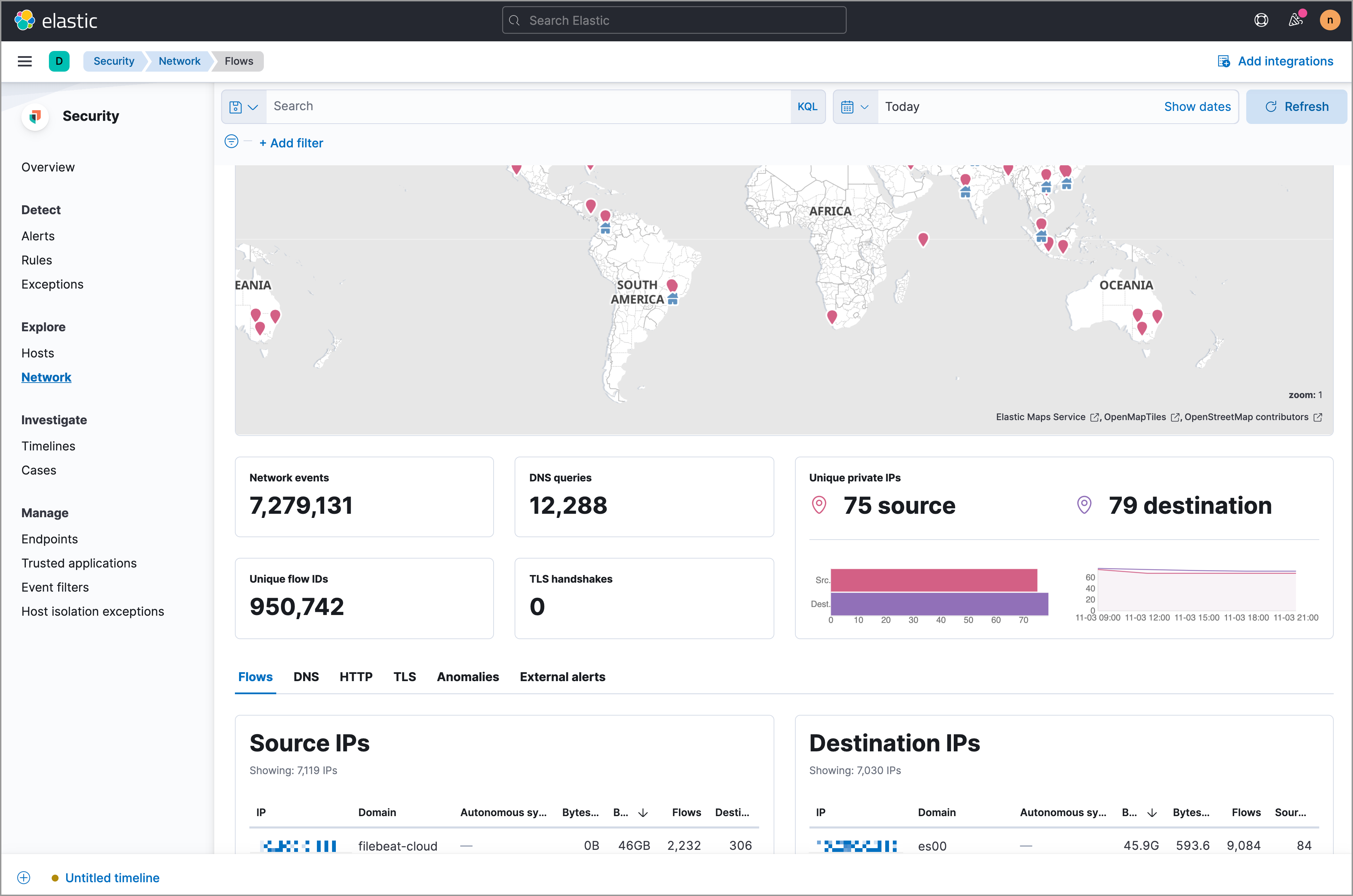
Network page
editThe Network page provides key network activity metrics via an interactive map and network event tables that enable interaction with Timeline. See Network page overview for more information.
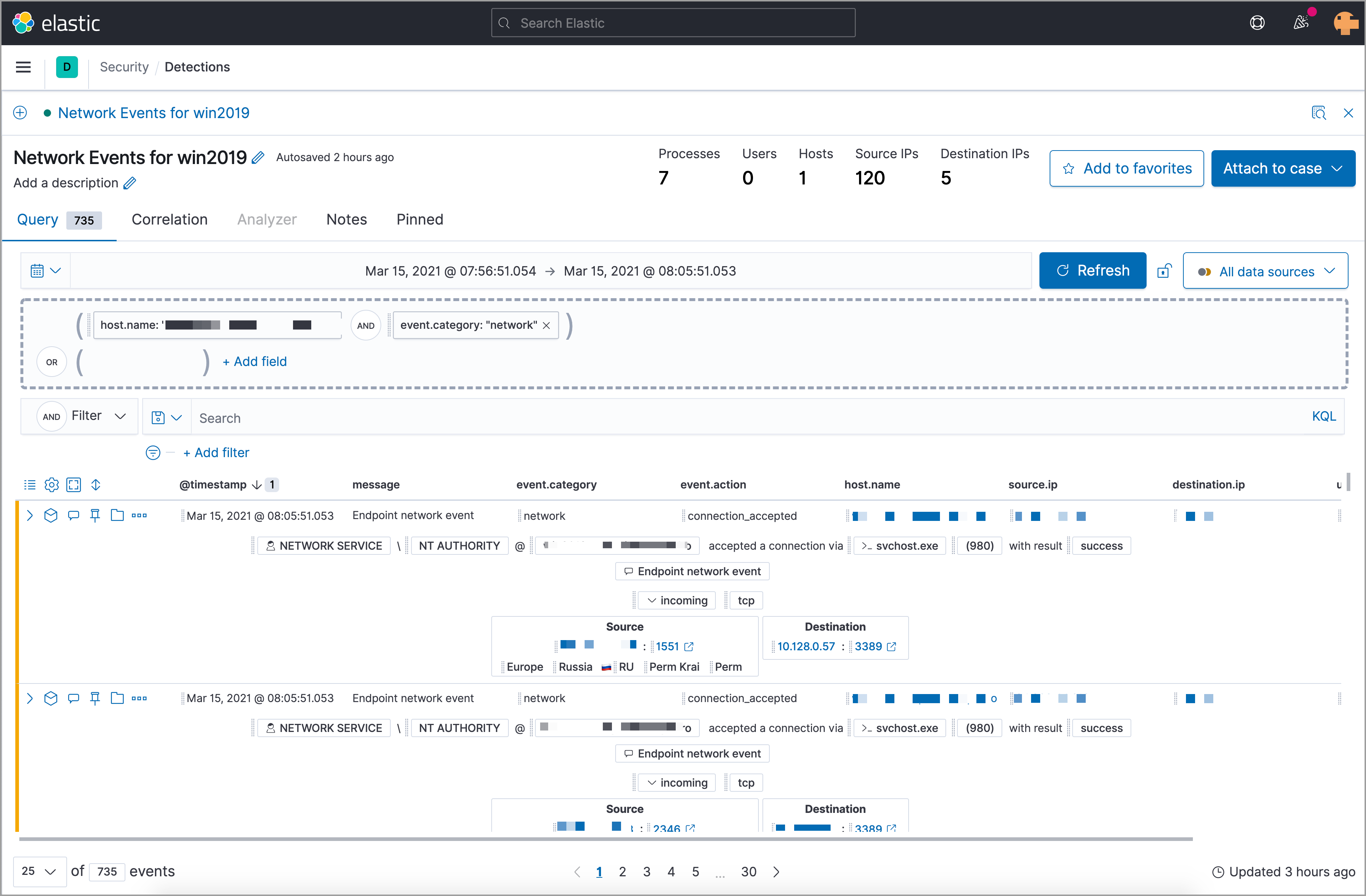
Timelines page
editUse the Timelines page to investigate alerts and complex threats, such as lateral movement of malware across hosts in your network. Timelines are responsive and allow you to share your findings among other team members. See Investigate events in Timeline for information about getting started with Timelines.
Select the collapsable Timeline button at the bottom of the Elastic Security app to start an investigation.
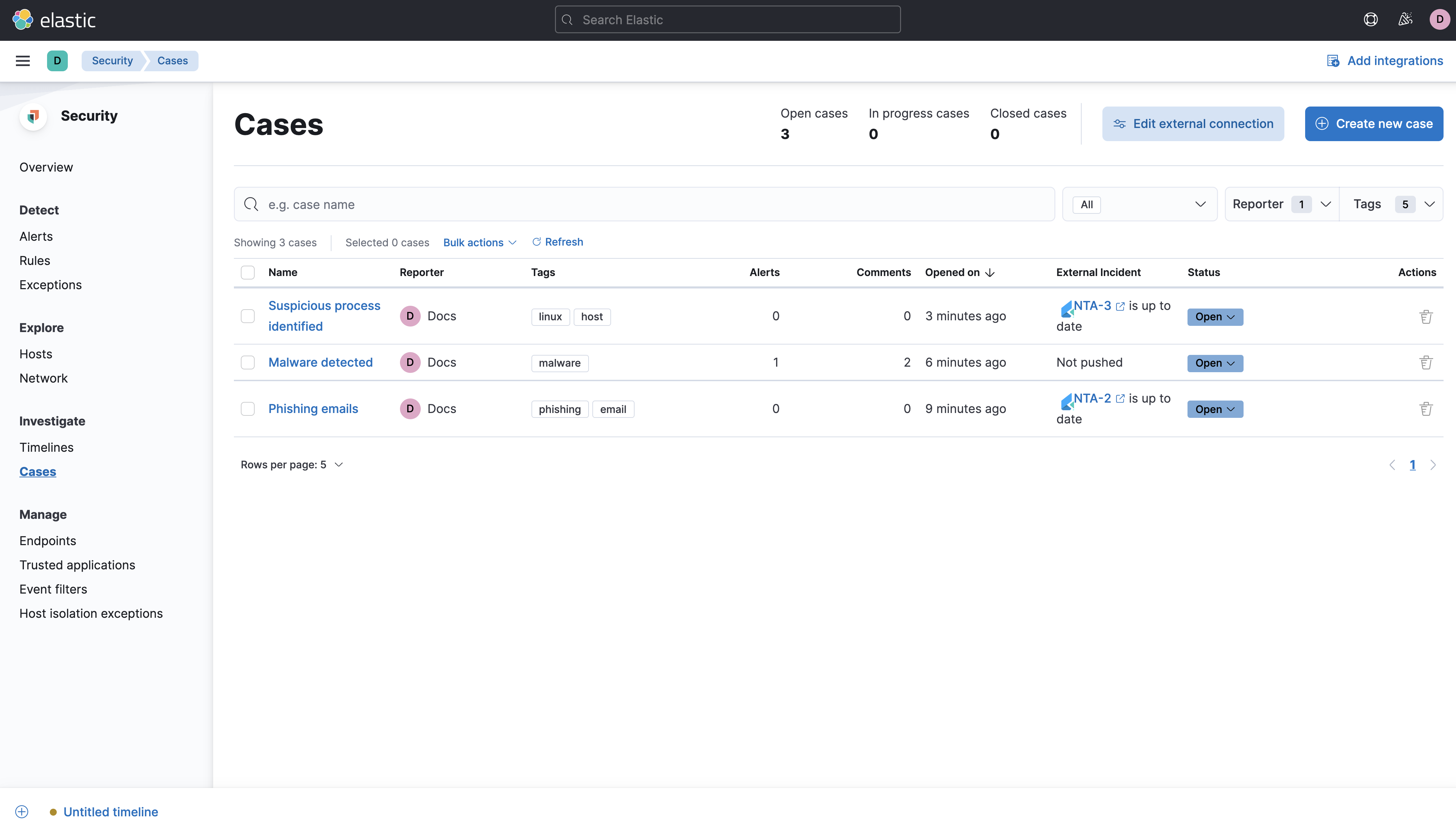
Cases page
editThe Cases page is used to open and track security issues directly in the Elastic Security app. See Cases for more information.
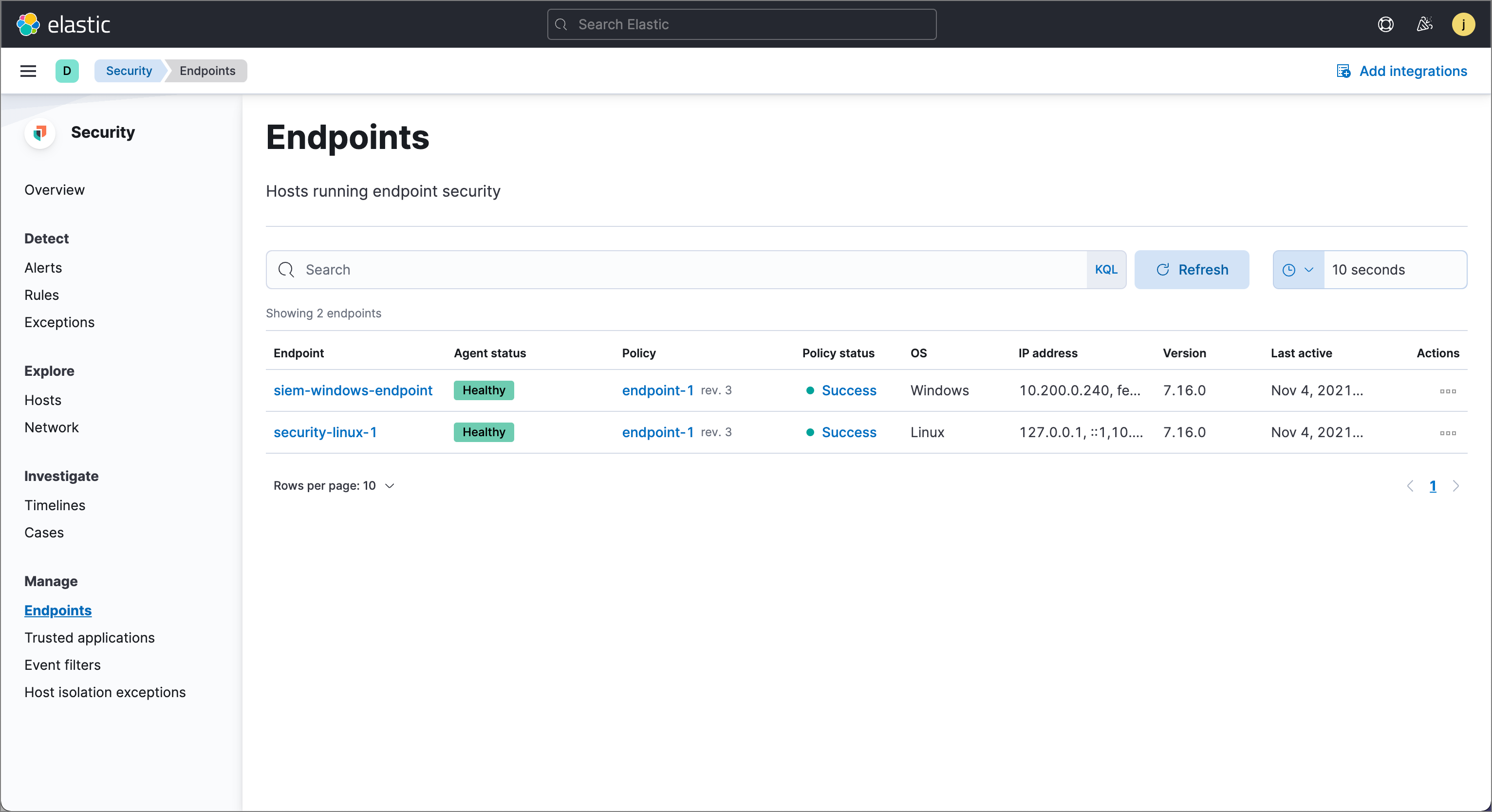
Endpoints page
editThe Endpoints page allows you to view and manage hosts that are running Endpoint Security. See Endpoints for more information.
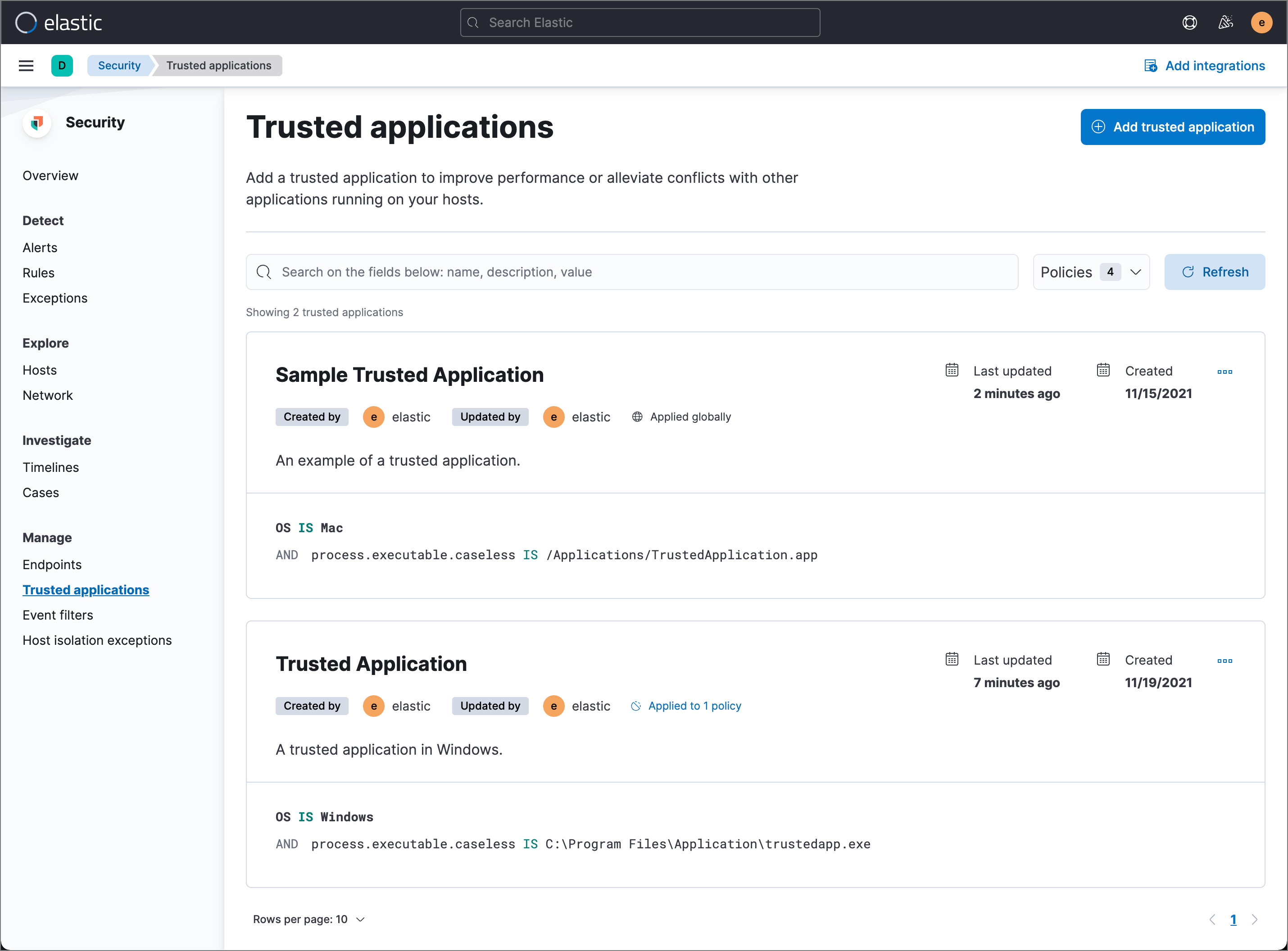
Trusted applications page
editThe Trusted applications page allows you to add Windows, macOS, and Linux applications that should be trusted. See Trusted applications for more information.
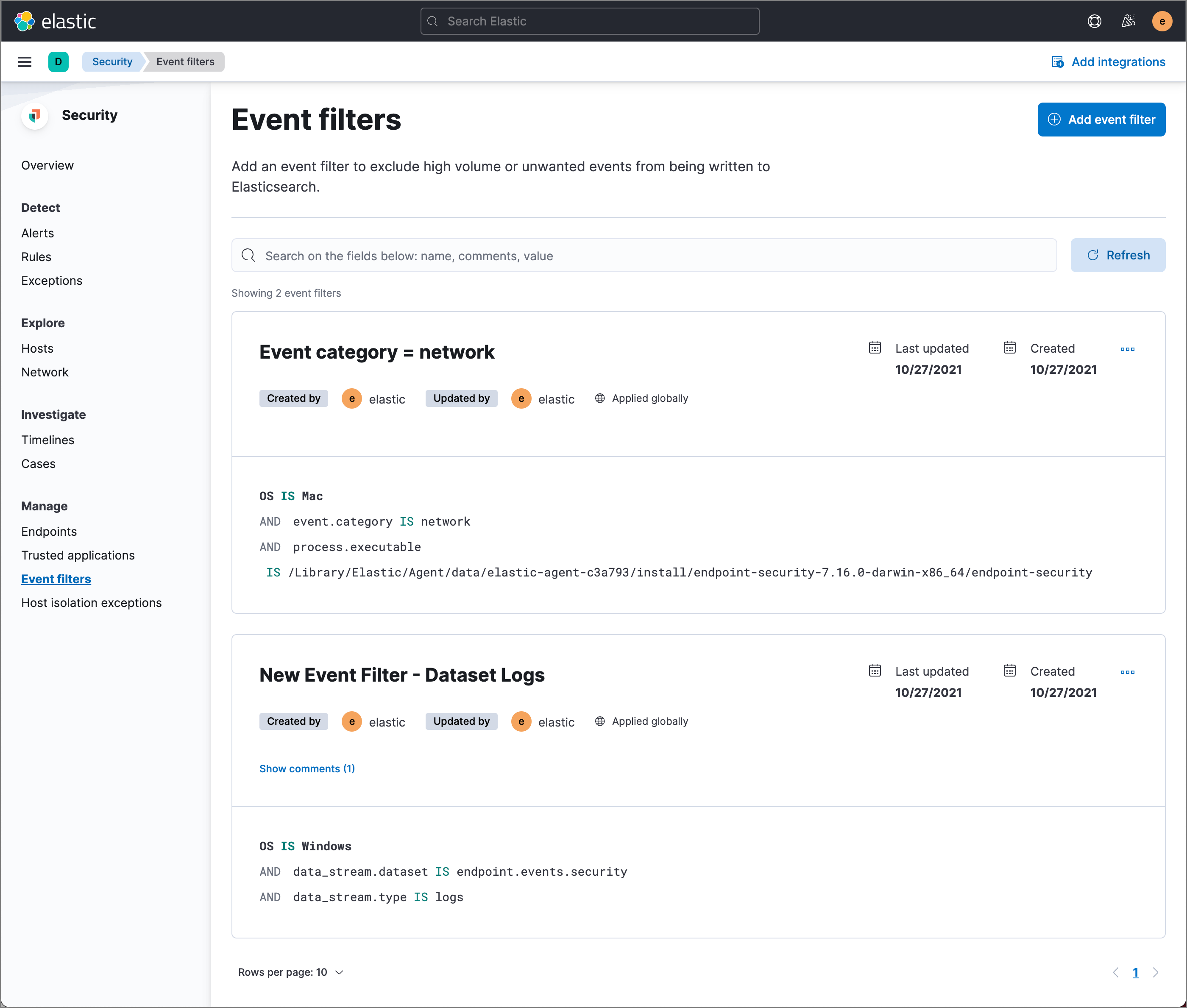
Event filters page
editThe Event filters page allows you to filter endpoint events that you do not need or want stored in Elasticsearch. See Event filters for more information.
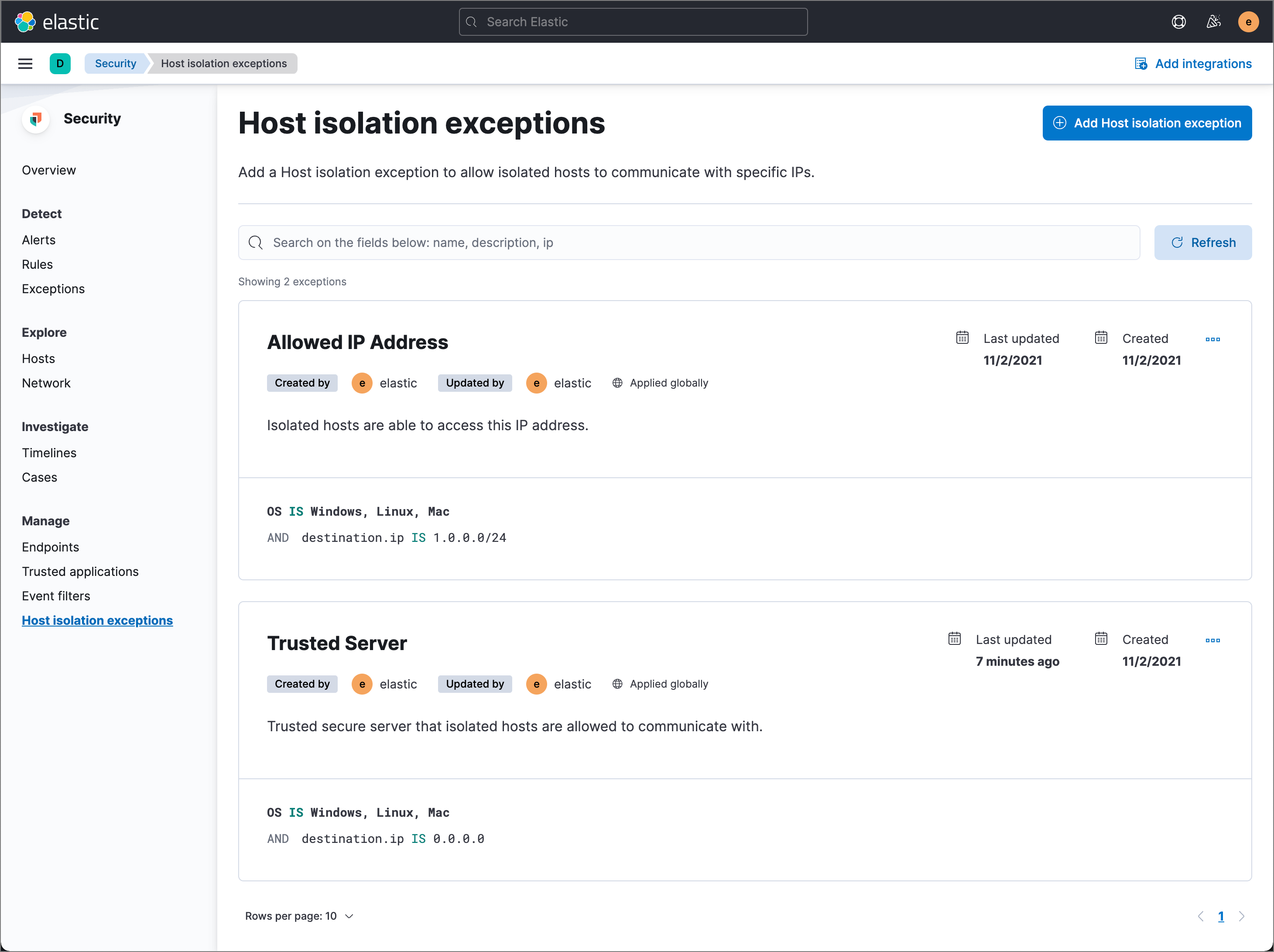
Host isolation exceptions page
editThe Host isolation exceptions page allows you to specify IP addresses that allow communication with isolated hosts, even when blocked from the rest of your network. See Host isolation exceptions for more information.
Accessibility features
editAccessibility features, such as keyboard focus and screen reader support, are built into the Elastic Security UI. These features offer additional ways for you to navigate the UI and interact with the application.
Interact with draggable elements
editUse your keyboard to interact with draggable elements in the Elastic Security UI:
-
Press the
Tabkey to apply keyboard focus to an element within a table. Or, use your mouse to click on an element and apply keyboard focus to it.
-
Press
Enteron an element with keyboard focus to display its menu and pressTabto apply focus sequentially to menu options. Thef,o,a,t,chotkeys are automatically enabled during this process and offer an alternative way to interact with menu options.
- Press the spacebar once to begin dragging an element to a different location and press it a second time to drop it. Use the directional arrows to move the element around the UI.
-
If an event has an event renderer, press the
Shiftkey and the down directional arrow to apply keyboard focus to the event renderer andTaborShift+Tabto navigate between fields. To return to the cells in the current row, press the up directional arrow. To move to the next row, press the down directional arrow.
Navigate the Elastic Security UI
editUse your keyboard to navigate through rows, columns, and menu options in the Elastic Security UI:
- Use the directional arrows to move keyboard focus right, left, up, and down in a table.
-
Press the
Tabkey to navigate through a table cell with multiple elements, such as buttons, field names, and menus. Pressing theTabkey will apply keyboard focus in a sequential manner to each element in the table cell.
-
Use
CTRL + Hometo shift keyboard focus to the first cell in a row. Likewise, useCTRL + Endto move keyboard focus to the last cell in the row.
-
Use the
Page UpandPage Downkeys to scroll through the page.